Novidades do Microsoft Defender para Identidade
Este artigo é atualizado frequentemente para lhe dar a conhecer as novidades nas versões mais recentes do Microsoft Defender para Identidade.
Novidades no âmbito e nas referências
As versões do Defender para Identidade são implementadas gradualmente nos inquilinos dos clientes. Se existir uma funcionalidade documentada aqui que ainda não vê no seu inquilino, marcar novamente mais tarde para a atualização.
Para obter mais informações, consulte também:
- Novidades no Microsoft Defender XDR
- Novidades no Microsoft Defender para Ponto de Extremidade
- Novidades no Microsoft Defender para Aplicativos em Nuvem
Para obter atualizações sobre versões e funcionalidades lançadas há seis meses ou anteriores, consulte o artigo Novidades do arquivo para Microsoft Defender para Identidade.
Março de 2025
Novos eventos de consulta LDAP adicionados à tabela IdentityQueryEvents na Investigação Avançada
Foram adicionados novos eventos de consulta LDAP à IdentityQueryEvents tabela em Investigação Avançada para fornecer mais visibilidade sobre consultas de pesquisa LDAP adicionais em execução no ambiente do cliente.
Fevereiro de 2025
Atualizações do módulo defenderForIdentity do PowerShell (versão 1.0.0.3)
Novas Funcionalidades e Melhoramentos:
- Suporte para obter, testar e definir a Reciclagem do Active Directory em Get/Set/Test MDIConfiguration.
- Suporte para obter, testar e definir a configuração do proxy no novo sensor MDI.
- O valor de registo dos Serviços de Certificados do Active Directory para filtragem de auditoria define agora corretamente o tipo.
- New-MDIConfigurationReport agora mostra o nome do GPO testado e suporta os argumentos Servidor e Identidade.
Correções de Erros:
- Maior fiabilidade para permissões de contentor DeletedObjects em sistemas operativos não ingleses.
- Foi corrigida uma saída desnecessária para a criação da chave de raiz do KDS.
- Outras correções de fiabilidade.
Novo separador caminhos de ataque na página Perfil de identidade
Este separador fornece visibilidade sobre potenciais caminhos de ataque que conduzem a uma identidade crítica ou que a envolvem no caminho, ajudando a avaliar os riscos de segurança. Para obter mais informações, veja Descrição geral do caminho de ataque na Gestão de Exposição.
Melhorias adicionais na página de identidade:
Novo painel lateral com mais informações para cada entrada no linha do tempo do utilizador.
Capacidades de filtragem no separador Dispositivos em Observados na organização.
Atualizar a recomendação de postura "Proteger e gerir palavras-passe de administrador local com a Microsoft LAPS"
Esta atualização alinha a avaliação da postura de segurança na Classificação de Segurança com a versão mais recente do Windows LAPS, garantindo que reflete as melhores práticas de segurança atuais para gerir palavras-passe de administrador local.
Eventos novos e atualizados na tabela Advanced hunting IdentityDirectoryEvents
Adicionámos e atualizámos os seguintes eventos na IdentityDirectoryEvents tabela em Investigação Avançada:
O sinalizador de controlo conta de utilizador foi alterado
Criação de grupos de segurança no Active Directory
Falha ao tentar alterar uma palavra-passe de conta
Alteração da palavra-passe da conta com êxito
O ID do grupo primário da conta foi alterado
Além disso, a referência de esquema incorporada para Investigação Avançada no Microsoft Defender XDR foi atualizada para incluir informações detalhadas sobre todos os tipos de eventos suportados (ActionTypevalores) em tabelas relacionadas com identidades, garantindo uma visibilidade total dos eventos disponíveis. Para obter mais informações, veja Advanced hunting schema details (Detalhes do esquema de investigação avançada).
Janeiro de 2025
Nova apresentação do Guia de identidade
Explore as principais funcionalidades do MDI com a nova Apresentação de Identidades no portal do M365. Navegue em Incidentes, Investigação e Definições para melhorar a segurança de identidade e a investigação de ameaças.
Dezembro de 2024
Nova avaliação da postura de segurança: Impedir a Inscrição de Certificados com Políticas de Aplicação arbitrárias (ESC15)
O Defender para Identidade adicionou a nova recomendação Impedir Inscrição de Certificados com Políticas de Aplicação arbitrárias (ESC15) na Classificação de Segurança da Microsoft.
Esta recomendação aborda diretamente o CVE-2024-49019 recentemente publicado, que destaca os riscos de segurança associados a configurações vulneráveis do AD CS. Esta avaliação da postura de segurança lista todos os modelos de certificado vulneráveis encontrados em ambientes de cliente devido a servidores do AD CS não recortados.
A nova recomendação é adicionada a outras recomendações relacionadas com o AD CS. Em conjunto, estas avaliações oferecem relatórios de postura de segurança que superam problemas de segurança e configurações incorretas graves que publicam riscos para toda a organização, juntamente com deteções relacionadas.
Para saber mais, confira:
Outubro de 2024
O MDI está a expandir a cobertura com as novas 10 recomendações de postura de identidade (pré-visualização)
As novas avaliações da postura de segurança de identidade (ISPMs) podem ajudar os clientes a monitorizar a configuração incorreta ao observar pontos fracos e reduzir o risco de ataques potenciais à infraestrutura no local.
Estas novas recomendações de identidade, como parte da Classificação de Segurança da Microsoft, são novos relatórios de postura de segurança relacionados com a infraestrutura do Active Directory e objetos de política de grupo:
Alterar a palavra-passe antiga da conta de computador do Controlador de Domínio
GPO atribui identidades sem privilégios a grupos locais com privilégios elevados
A conta de Convidado do Active Directory incorporada está ativada
Alterar a palavra-passe da conta de Administrador de domínio incorporada
Além disso, atualizámos a recomendação existente de "Modificar delegações kerberos não seguras para impedir a representação" para incluir a indicação da Delegação Restrita de Kerberos com Transição de Protocolo para um serviço privilegiado.
Agosto de 2024
Novo sensor Microsoft Entra Connect:
Como parte do nosso esforço contínuo para melhorar Microsoft Defender para Identidade cobertura em ambientes de identidade híbrida, introduzimos um novo sensor para servidores do Microsoft Entra Connect. Além disso, lançámos novas deteções de segurança híbridas e novas recomendações de postura de identidade especificamente para o Microsoft Entra Connect, ajudando os clientes a manterem-se protegidos e a mitigar potenciais riscos.
Novas recomendações de postura de identidade do Microsoft Entra Connect:
-
Rodar a palavra-passe para a conta do conector do Microsoft Entra Connect
- Uma conta de conector Microsoft Entra Connect comprometida (conta do conector do AD DS, normalmente apresentada como MSOL_XXXXXXXX) pode conceder acesso a funções de privilégios elevados, como replicação e reposições de palavras-passe, permitindo aos atacantes modificar as definições de sincronização e comprometer a segurança em ambientes na cloud e no local, bem como oferecer vários caminhos para comprometer todo o domínio. Nesta avaliação, recomendamos que os clientes alterem a palavra-passe das contas MSOL com a palavra-passe definida pela última vez há mais de 90 dias. Para obter mais informações, clique aqui.
-
Remover permissões de replicação desnecessárias para a Conta do Microsoft Entra Connect
- Por predefinição, a conta do conector do Microsoft Entra Connect tem permissões extensas para garantir uma sincronização adequada (mesmo que não sejam realmente necessárias). Se a Sincronização hash de palavras-passe não estiver configurada, é importante remover permissões desnecessárias para reduzir a potencial superfície de ataque. Para obter mais informações, clique aqui
-
Alterar a palavra-passe para Microsoft Entra configuração de conta SSO totalmente integrada
- Este relatório lista todas as Microsoft Entra contas de computador SSO totalmente integradas com a palavra-passe definida pela última vez há mais de 90 dias. A palavra-passe da conta de computador SSO do Azure não é alterada automaticamente a cada 30 dias. Se um atacante comprometer esta conta, pode gerar pedidos de assistência para a conta AZUREADSSOACC em nome de qualquer utilizador e representar qualquer utilizador no inquilino Microsoft Entra sincronizado a partir do Active Directory. Um atacante pode utilizá-lo para mover lateralmente do Active Directory para o Microsoft Entra ID. Para obter mais informações, clique aqui.
Novas deteções do Microsoft Entra Connect:
-
Início de Sessão Interativo Suspeito no Servidor do Microsoft Entra Connect
- Os inícios de sessão diretos nos servidores do Microsoft Entra Connect são altamente invulgares e potencialmente maliciosos. Os atacantes direcionam frequentemente estes servidores para roubar credenciais para um acesso de rede mais amplo. Microsoft Defender para Identidade agora pode detetar inícios de sessão anormais nos servidores do Microsoft Entra Connect, ajudando-o a identificar e responder a estas potenciais ameaças mais rapidamente. É especificamente aplicável quando o servidor Microsoft Entra Connect é um servidor autónomo e não funciona como controlador de domínio.
-
Reposição de Palavra-passe de Utilizador por conta do Microsoft Entra Connect
- A conta do conector do Microsoft Entra Connect tem frequentemente privilégios elevados, incluindo a capacidade de repor as palavras-passe do utilizador. Microsoft Defender para Identidade agora tem visibilidade sobre essas ações e detetará qualquer utilização dessas permissões identificadas como maliciosas e não legítimas. Este alerta só será acionado se a funcionalidade de repetição de escrita de palavras-passe estiver desativada.
-
Repetição de escrita suspeita por Microsoft Entra Ligar a um utilizador confidencial
- Embora o Microsoft Entra Connect já impeça a repetição de escrita para utilizadores em grupos com privilégios, Microsoft Defender para Identidade expande esta proteção ao identificar tipos adicionais de contas confidenciais. Esta deteção melhorada ajuda a impedir reposições de palavras-passe não autorizadas em contas críticas, o que pode ser um passo crucial em ataques avançados direcionados para ambientes na cloud e no local.
Melhorias e capacidades adicionais:
- Nova atividade de qualquer reposição de palavra-passe falhada numa conta confidencial disponível na tabela "IdentityDirectoryEvents" em Investigação Avançada. Isto pode ajudar os clientes a controlar eventos de reposição de palavras-passe falhados e a criar deteção personalizada com base nesses dados.
- Precisão melhorada para a deteção de ataques de sincronização de DC .
- Novo problema de estado de funcionamento para casos em que o sensor não consegue obter a configuração do serviço Microsoft Entra Connect.
- Monitorização alargada para alertas de segurança, como o Detetor de Execução Remota do PowerShell, ao ativar o novo sensor nos servidores do Microsoft Entra Connect.
Saiba mais sobre o novo sensor
Módulo do PowerShell DefenderForIdentity atualizado
O módulo DefenderForIdentity do PowerShell foi atualizado, incorporando novas funcionalidades e resolvendo várias correções de erros. As principais melhorias incluem:
-
Novo
New-MDIDSACmdlet: simplifica a criação de contas de serviço, com uma predefinição para Contas de Serviço Geridas de Grupo (gMSA) e uma opção para criar contas padrão. - Deteção Automática de PDCe: melhora a fiabilidade de criação do Objeto Política de Grupo (GPO) ao direcionar automaticamente o Emulador do Controlador de Domínio Primário (PDCe) para a maioria das operações do Active Directory.
-
Filtragem manual do Controlador de Domínio: novo parâmetro do Servidor para
Get/Set/Test-MDIConfigurationcmdlets, permitindo-lhe especificar um controlador de domínio para filtragem em vez do PDCe.
Para saber mais, confira:
- Módulo DefenderForIdentity do PowerShell (Galeria do PowerShell)
- Documentação de referência do PowerShell defenderForIdentity
Julho de 2024
6 As novas deteções são novas na pré-visualização pública:
-
Possível ataque NetSync
- O NetSync é um módulo no Mimikatz, uma ferramenta de pós-exploração, que pede o hash de palavra-passe de uma palavra-passe de um dispositivo de destino fingindo ser um controlador de domínio. Um atacante pode estar a realizar atividades maliciosas dentro da rede através desta funcionalidade para obter acesso aos recursos da organização.
-
Possível obtenção de uma conta SSO Microsoft Entra totalmente integrada
- Um Microsoft Entra objeto de conta SSO (início de sessão único) totalmente integrado, AZUREADSSOACC, foi modificado de forma suspeita. Um atacante pode estar a mover-se lateralmente do ambiente no local para a cloud.
-
Consulta LDAP suspeita
- Foi detetada uma consulta LDAP (Lightweight Directory Access Protocol) suspeita associada a uma ferramenta de ataque conhecida. Um atacante pode estar a realizar o reconhecimento para passos posteriores.
-
SPN suspeito foi adicionado a um utilizador
- Foi adicionado um nome de principal de serviço (SPN) suspeito a um utilizador confidencial. Um atacante pode estar a tentar obter acesso elevado para movimento lateral dentro da organização
-
Criação suspeita do grupo ESXi
- Foi criado um grupo VMWare ESXi suspeito no domínio. Isto pode indicar que um atacante está a tentar obter mais permissões para passos posteriores num ataque.
-
Autenticação suspeita do ADFS
- Uma conta associada a um domínio com sessão iniciada com Serviços de Federação do Active Directory (AD FS) (ADFS) a partir de um endereço IP suspeito. Um atacante pode ter roubado as credenciais de um utilizador e está a utilizá-lo para se mover lateralmente na organização.
Versão 2.238 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Junho de 2024
Procurar facilmente informações do utilizador a partir do dashboard do ITDR
O Widget Shield fornece uma descrição geral rápida do número de utilizadores em ambientes híbridos, na cloud e no local. Esta funcionalidade inclui agora ligações diretas para a plataforma Investigação Avançada, oferecendo informações detalhadas do utilizador ao seu alcance.
O Widget de Estado de Funcionamento da Implementação itDR agora inclui Microsoft Entra Acesso Condicional e Acesso privado do Microsoft Entra
Agora, pode ver a disponibilidade da licença para Microsoft Entra Acesso Condicional à Carga de Trabalho, acesso condicional Microsoft Entra utilizador e Acesso privado do Microsoft Entra.
Versão 2.237 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Maio de 2024
Versão 2.236 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.235 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Abril de 2024
Detetar facilmente a Vulnerabilidade de Desativação da Funcionalidade de Segurança Kerberos do Windows CVE-2024-21427
Para ajudar os clientes a identificar e detetar melhor as tentativas de ignorar os protocolos de segurança de acordo com esta vulnerabilidade, adicionámos uma nova atividade na Investigação Avançada que monitoriza a autenticação Kerberos AS.
Com estes dados, os clientes podem agora criar facilmente as suas próprias regras de deteção personalizadas no Microsoft Defender XDR e acionar automaticamente alertas para este tipo de atividade
Access Defender XDR portal –> Investigação –> Investigação Avançada.
Agora, pode copiar a nossa consulta recomendada, conforme indicado abaixo, e clicar em "Criar regra de deteção". Tenha em atenção que a nossa consulta fornecida também monitoriza as tentativas de início de sessão falhadas, o que pode gerar informações não relacionadas com um possível ataque. Por conseguinte, não hesite em personalizar a consulta de acordo com os seus requisitos específicos.
IdentityLogonEvents
| where Application == "Active Directory"
| where Protocol == "Kerberos"
| where LogonType in("Resource access", "Failed logon")
| extend Error = AdditionalFields["Error"]
| extend KerberosType = AdditionalFields['KerberosType']
| where KerberosType == "KerberosAs"
| extend Spns = AdditionalFields["Spns"]
| extend DestinationDC = AdditionalFields["TO.DEVICE"]
| where Spns !contains "krbtgt" and Spns !contains "kadmin"
| project Timestamp, ActionType, LogonType, AccountUpn, AccountSid, IPAddress, DeviceName, KerberosType, Spns, Error, DestinationDC, DestinationIPAddress, ReportId
Versão 2.234 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.233 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Março de 2024
Novas permissões só de leitura para visualizar as definições do Defender para Identidade
Agora, pode configurar os utilizadores do Defender para Identidade com permissões só de leitura para ver as definições do Defender para Identidade.
Para obter mais informações, veja Permissões necessárias do Defender para Identidade no Microsoft Defender XDR.
Nova API baseada em Grafos para ver e gerir problemas de Estado de Funcionamento
Agora, pode ver e gerir problemas de estado de funcionamento Microsoft Defender para Identidade através do API do Graph
Para obter mais informações, veja Gerir problemas de Estado de Funcionamento através de API do Graph.
Versão 2.232 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.231 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Fevereiro de 2024
Versão 2.230 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Nova avaliação da postura de segurança para a configuração insegura do ponto final do IIS do AD CS
O Defender para Identidade adicionou a nova recomendação Editar pontos finais IIS (ESC8) de inscrição de certificados ADCS inseguros na Classificação de Segurança da Microsoft.
Os Serviços de Certificados do Active Directory (AD CS) suportam a inscrição de certificados através de vários métodos e protocolos, incluindo a inscrição através de HTTP através do Serviço de Inscrição de Certificados (CES) ou da interface de Inscrição Web (Certsrv). As configurações inseguras dos pontos finais CES ou Certsrv IIS podem criar vulnerabilidades para ataques de reencaminhamento (ESC8).
A nova recomendação Edit insecure ADCS certificate enrollment IIS endpoints (ESC8) é adicionada a outras recomendações relacionadas com o AD CS lançadas recentemente. Em conjunto, estas avaliações oferecem relatórios de postura de segurança que superam problemas de segurança e configurações incorretas graves que publicam riscos para toda a organização, juntamente com deteções relacionadas.
Para saber mais, confira:
- Avaliação de segurança: Editar pontos finais IIS de inscrição de certificados do ADCS inseguros (ESC8)
- Avaliações da postura de segurança para sensores do AD CS
- Avaliações da postura de segurança do Microsoft Defender para Identidade
Versão 2.229 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
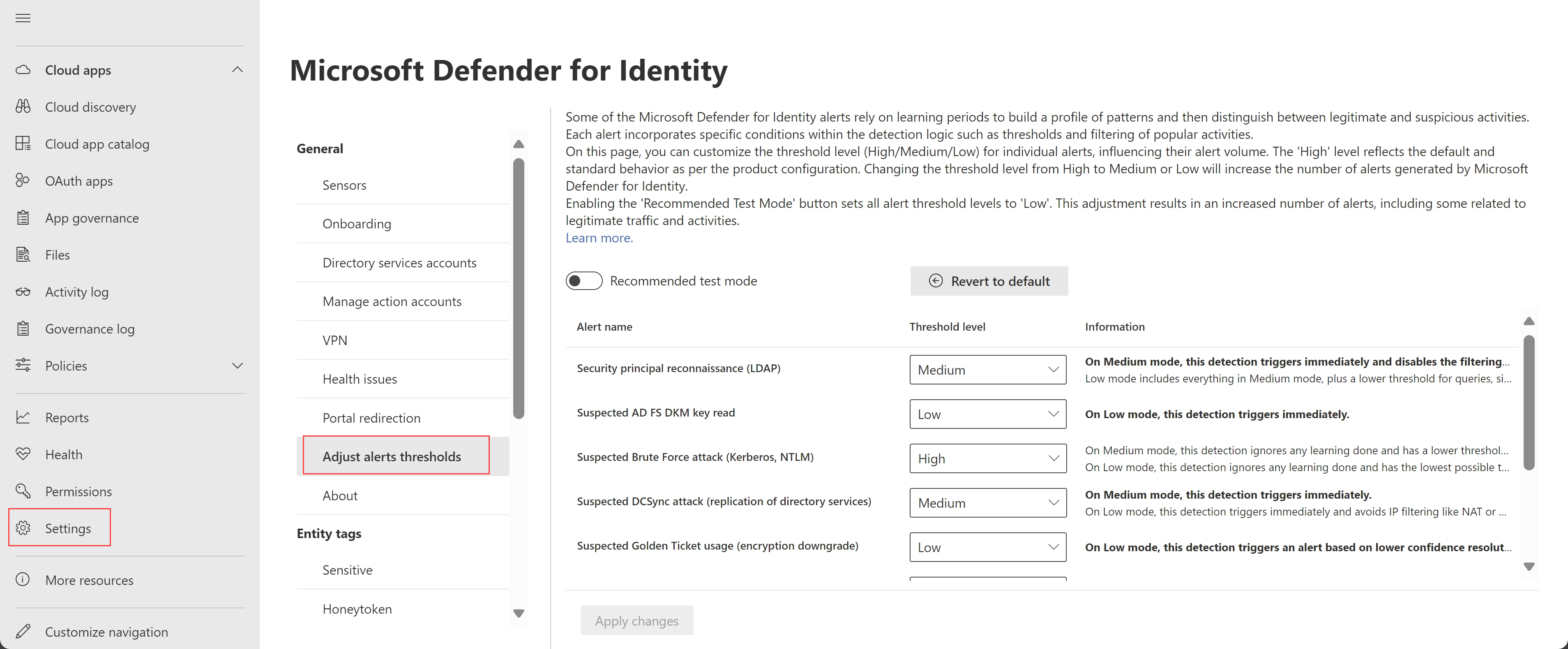
Experiência de utilizador melhorada para ajustar limiares de alertas (Pré-visualização)
A página Definições Avançadas do Defender para Identidade foi agora renomeada para Ajustar limiares de alerta e fornece uma experiência atualizada com maior flexibilidade para ajustar os limiares de alerta.
As alterações incluem:
Removemos a opção anterior Remover período de aprendizagem e adicionámos uma nova opção Modo de teste recomendado . Selecione Modo de teste recomendado para definir todos os níveis de limiar para Baixo, aumentar o número de alertas e definir todos os outros níveis de limiar como só de leitura.
A coluna de nível de Confidencialidade anterior foi agora renomeada como Nível de limiar, com valores recentemente definidos. Por predefinição, todos os alertas estão definidos para um Limiar elevado , que representa o comportamento predefinido e uma configuração de alerta padrão.
A tabela seguinte lista o mapeamento entre os valores anteriores do nível de Confidencialidade e os novos valores de nível de Limiar :
| Nível de confidencialidade (nome anterior) | Nível de limiar (novo nome) |
|---|---|
| Normal | High |
| Medium | Medium |
| High | Baixo |
Se tiver valores específicos definidos na página Definições Avançadas , transferimo-los para a nova página Ajustar limiares de alertas da seguinte forma:
| Configuração de página de definições avançadas | Nova configuração da página Ajustar limiares de alerta |
|---|---|
| Remover o período de aprendizagem ativado |
Modo de teste recomendado desativado. As definições de configuração do limiar de alerta permanecem as mesmas. |
| Remover período de aprendizagem desativado |
Modo de teste recomendado desativado. As definições de configuração do limiar de alerta são todas repostas para os valores predefinidos, com um nível de limiar Elevado . |
Os alertas são sempre acionados imediatamente se a opção Modo de teste recomendado estiver selecionada ou se um nível de limiar estiver definido como Médio ou Baixo, independentemente de o período de aprendizagem do alerta já ter sido concluído.
Para obter mais informações, veja Ajustar limiares de alerta.
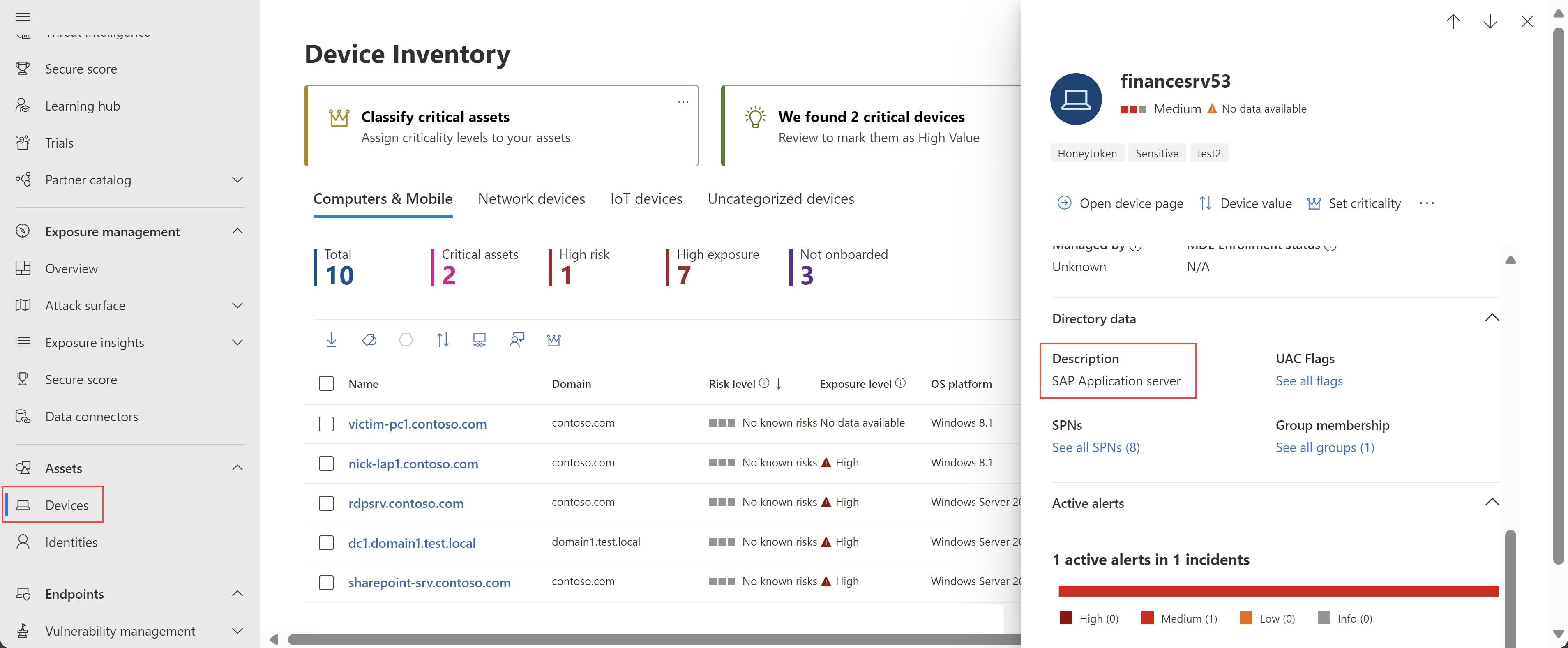
As páginas de detalhes do dispositivo incluem agora descrições do dispositivo (Pré-visualização)
Microsoft Defender XDR agora inclui descrições de dispositivos em painéis de detalhes do dispositivo e páginas de detalhes do dispositivo. As descrições são preenchidas a partir do atributo Descrição do Active Directory do dispositivo.
Por exemplo, no painel lateral de detalhes do dispositivo:
Para obter mais informações, veja Passos de investigação para dispositivos suspeitos.
Versão 2.228 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade e os seguintes novos alertas:
- Reconhecimento de Enumeração de Conta (LDAP) (ID externo 2437) (Pré-visualização)
- Alteração da Palavra-passe do Modo de Restauro dos Serviços de Diretório (ID externo 2438) (Pré-visualização)
Janeiro de 2024
Versão 2.227 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
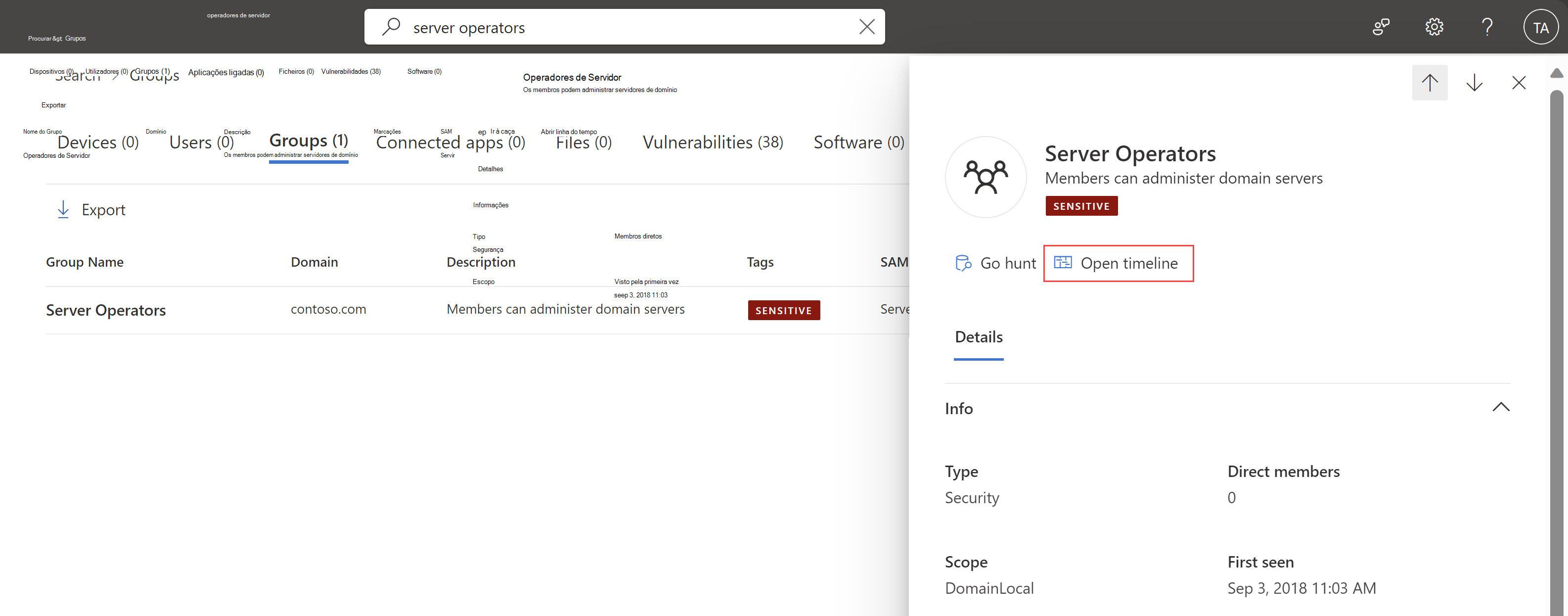
Separador Linha Cronológica adicionado para entidades de grupo
Agora, pode ver as atividades e os alertas relacionados com a entidade do grupo Active Directory dos últimos 180 dias no Microsoft Defender XDR, como alterações de associação a grupos, consultas LDAP, entre outros.
Para aceder ao grupo linha do tempo página, selecione Abrir linha do tempo no painel de detalhes do grupo.
Por exemplo:
Para obter mais informações, veja Passos de investigação para grupos suspeitos.
Configurar e validar o ambiente do Defender para Identidade através do PowerShell
Agora, o Defender para Identidade suporta o novo módulo defenderForIdentity do PowerShell, que foi concebido para o ajudar a configurar e validar o seu ambiente para trabalhar com Microsoft Defender para Identidade.
Utilize os comandos do PowerShell para evitar configurações incorretas, poupar tempo e evitar cargas desnecessárias no seu sistema.
Adicionámos os seguintes procedimentos à documentação do Defender para Identidade para o ajudar a utilizar os novos comandos do PowerShell:
- Alterar a configuração do proxy com o PowerShell
- Configurar, obter e testar políticas de auditoria com o PowerShell
- Gerar um relatório com configurações atuais através do PowerShell
- Testar as permissões e delegações de DSA através do PowerShell
- Testar a conectividade do serviço com o PowerShell
Para saber mais, confira:
- Módulo DefenderForIdentity do PowerShell (Galeria do PowerShell)
- Documentação de referência do PowerShell defenderForIdentity
Versão 2.226 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.225 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Dezembro de 2023
Observação
Se estiver a ver um número reduzido de alertas de tentativas de execução de código remoto , veja os nossos anúncios de setembro atualizados, que incluem uma atualização da lógica de deteção do Defender para Identidade. O Defender para Identidade continua a registar as atividades de execução remota de código como anteriormente.
Nova área de Identidades e dashboard no Microsoft 365 Defender (Pré-visualização)
Os clientes do Defender para Identidade têm agora uma nova área Identidades no Microsoft 365 Defender para obter informações sobre a segurança de identidade com o Defender para Identidade.
No Microsoft 365 Defender, selecione Identidades para ver qualquer uma das seguintes novas páginas:
Dashboard: esta página mostra gráficos e widgets para o ajudar a monitorizar as atividades de deteção e resposta de ameaças de identidade. Por exemplo:
Para obter mais informações, veja Work with Defender for Identity's ITDR dashboard (Trabalhar com o ITDR do Defender para Identidade) dashboard.
Problemas de estado de funcionamento: esta página é movida da área Identidades das Definições > e lista quaisquer problemas de estado de funcionamento atuais para a implementação geral do Defender para Identidade e sensores específicos. Para obter mais informações, veja Microsoft Defender para Identidade problemas de estado de funcionamento do sensor.
Ferramentas: esta página contém ligações para informações e recursos úteis ao trabalhar com o Defender para Identidade. Nesta página, encontre ligações para documentação, especificamente sobre a ferramenta de planeamento de capacidade e o script Test-MdiReadiness.ps1 .
Versão 2.224 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Avaliações da postura de segurança para sensores do AD CS (Pré-visualização)
As avaliações da postura de segurança do Defender para Identidade detetam e recomendam proativamente ações nas suas configurações de Active Directory local.
As ações recomendadas incluem agora as seguintes novas avaliações de postura de segurança, especificamente para modelos de certificado e autoridades de certificação.
Ações recomendadas de modelos de certificado:
- Impedir que os utilizadores peçam um certificado válido para utilizadores arbitrários com base no modelo de certificado (ESC1)
- Editar modelo de certificado excessivamente permissivo com EKU privilegiado (EKU para qualquer finalidade ou Sem EKU) (ESC2)
- Modelo de certificado do agente de inscrição configurado incorretamente (ESC3)
- Editar modelos de certificado configurados incorretamente ACL (ESC4)
- Editar proprietário de modelos de certificado configurado incorretamente (ESC4)
Ações recomendadas da autoridade de certificação:
As novas avaliações estão disponíveis na Classificação de Segurança da Microsoft, apresentando problemas de segurança e configurações incorretas graves que representam riscos para toda a organização, juntamente com as deteções. A sua classificação é atualizada em conformidade.
Por exemplo:
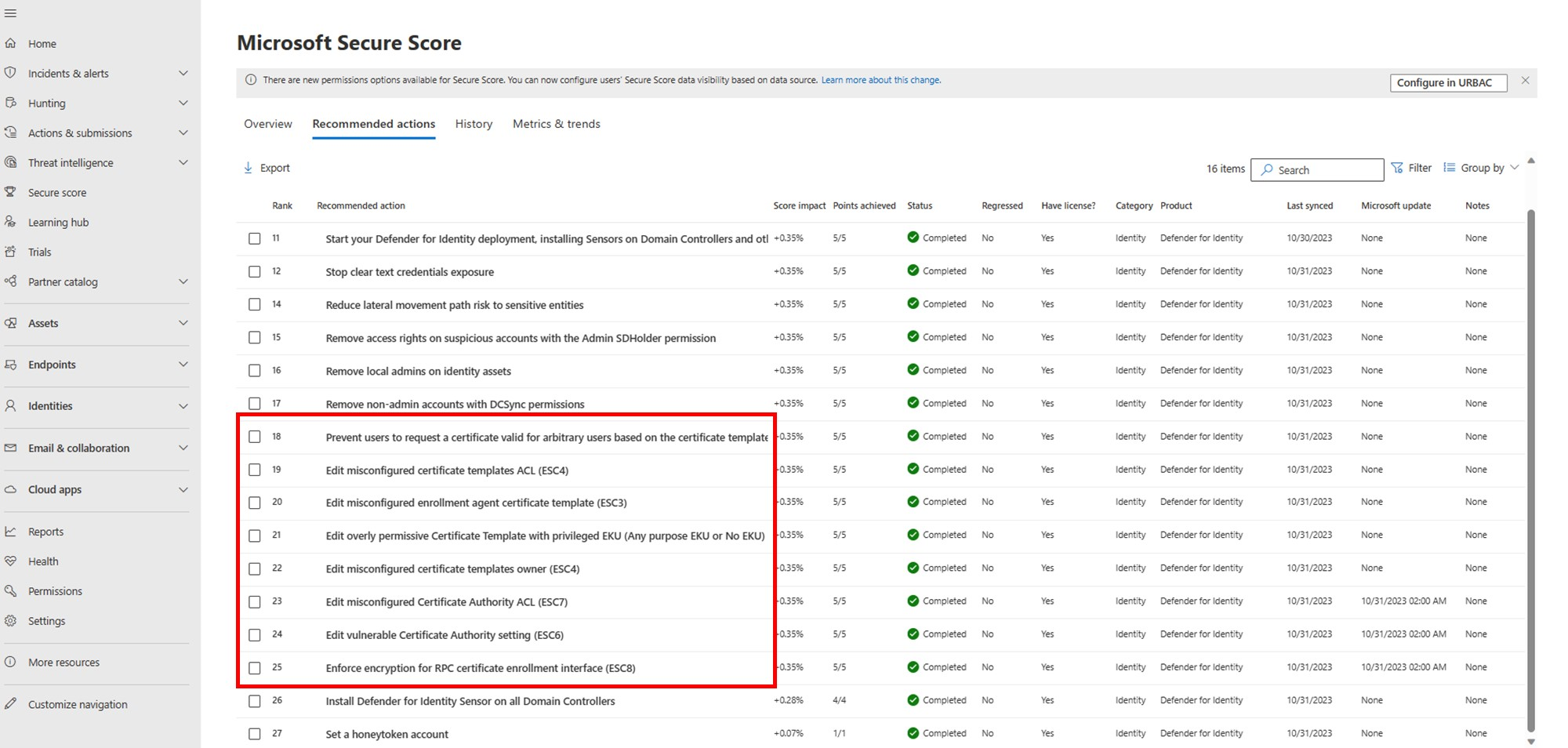
Para obter mais informações, veja avaliações da postura de segurança do Microsoft Defender para Identidade.
Observação
Embora as avaliações de modelos de certificado estejam disponíveis para todos os clientes que tenham o AD CS instalado no respetivo ambiente, as avaliações da autoridade de certificação só estão disponíveis para clientes que tenham instalado um sensor num servidor do AD CS. Para obter mais informações, veja Novo tipo de sensor para os Serviços de Certificados do Active Directory (AD CS).
Versão 2.223 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.222 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.221 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Novembro de 2023
Versão 2.220 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.219 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
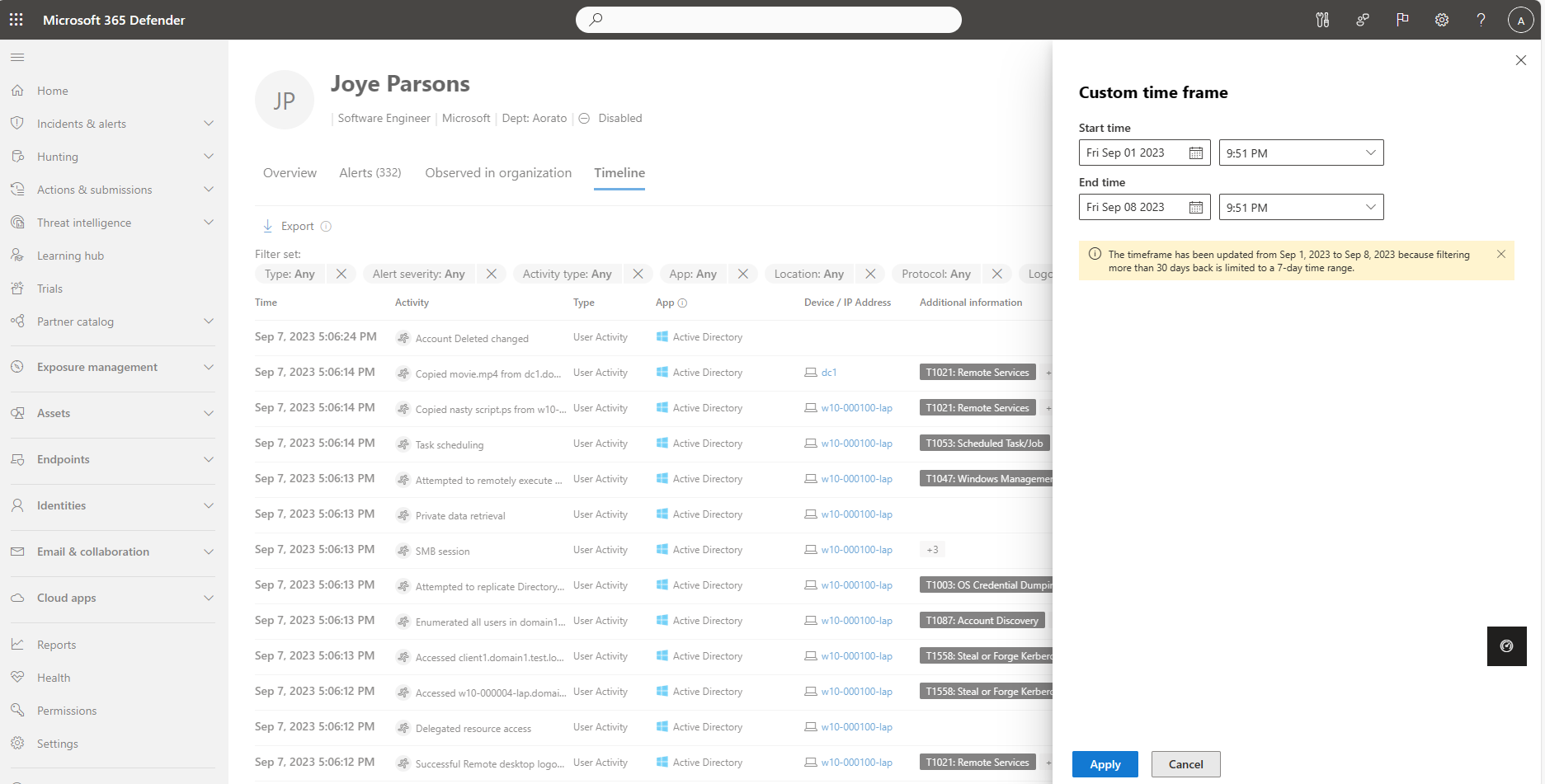
O linha do tempo de identidade inclui mais de 30 dias de dados (Pré-visualização)
O Defender para Identidade está a implementar gradualmente retenção de dados alargados em detalhes de identidade para mais de 30 dias.
O separador Linha Cronológica da página de detalhes de identidade, que inclui atividades do Defender para Identidade, Microsoft Defender para Aplicativos de Nuvem e Microsoft Defender para Ponto de Extremidade, inclui atualmente um mínimo de 150 dias e está a crescer. Poderá haver alguma variação nas taxas de retenção de dados nas próximas semanas.
Para ver atividades e alertas sobre a identidade linha do tempo dentro de um período de tempo específico, selecione os 30 Dias predefinidos e, em seguida, selecione Intervalo personalizado. Os dados filtrados de há mais de 30 dias são apresentados durante um máximo de sete dias de cada vez.
Por exemplo:
Para obter mais informações, veja Investigar recursos e Investigar utilizadores no Microsoft Defender XDR.
Versão 2.218 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Outubro de 2023
Versão 2.217 do Defender para Identidade
Esta versão inclui os seguintes melhoramentos:
Relatório de resumo: o relatório de resumo é atualizado para incluir duas novas colunas no separador Problemas de estado de funcionamento:
- Detalhes: informações adicionais sobre o problema, como uma lista de objetos afetados ou sensores específicos nos quais o problema ocorre.
- Recomendações: uma lista de ações recomendadas que podem ser tomadas para resolve o problema ou como investigar melhor o problema.
Para obter mais informações, consulte Transferir e agendar relatórios do Defender para Identidade no Microsoft Defender XDR (Pré-visualização).
Problemas de estado de funcionamento: o botão de alternar "Remover período de aprendizagem" foi desativado automaticamente para este problema de estado de funcionamento do inquilino*.
Esta versão também inclui correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.216 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Setembro de 2023
Número reduzido de alertas para Tentativas de Execução de Código Remoto
Para alinhar melhor o Defender para Identidade e Microsoft Defender para Ponto de Extremidade alertas, atualizámos a lógica de deteção para as deteções de tentativas de execução remota de código do Defender para Identidade.
Embora esta alteração resulte num número reduzido de alertas de tentativas de execução de código remoto , o Defender para Identidade continua a registar as atividades de execução remota do código. Os clientes podem continuar a criar as suas próprias consultas de investigação avançadas e criar políticas de deteção personalizadas.
Definições de confidencialidade de alertas e melhoramentos do período de aprendizagem
Alguns alertas do Defender para Identidade aguardam um período de aprendizagem antes de os alertas serem acionados, ao mesmo tempo que criam um perfil de padrões a utilizar ao distinguir entre atividades legítimas e suspeitas.
O Defender para Identidade fornece agora as seguintes melhorias para a experiência do período de aprendizagem:
Os administradores podem agora utilizar a definição Remover período de aprendizagem para configurar a confidencialidade utilizada para alertas específicos. Defina a confidencialidade como Normal para configurar a definição Remover período de aprendizagem como Desativado para o tipo de alerta selecionado.
Depois de implementar um novo sensor numa nova área de trabalho do Defender para Identidade, a definição Remover período de aprendizagem é ativada automaticamente durante 30 dias. Quando 30 dias estiverem concluídos, a definição Remover período de aprendizagem é desativada automaticamente e os níveis de confidencialidade dos alertas são devolvidos à respetiva funcionalidade predefinida.
Para que o Defender para Identidade utilize a funcionalidade do período de aprendizagem padrão, em que os alertas não são gerados até que o período de aprendizagem seja concluído, configure a definição Remover períodos de aprendizagem como Desativado.
Se tiver atualizado anteriormente a definição Remover período de aprendizagem , a definição permanece como a configurou.
Para obter mais informações, veja Definições avançadas.
Observação
A página Definições Avançadas listou originalmente o alerta de reconhecimento de enumeração de conta nas opções Remover período de aprendizagem como configuráveis para as definições de confidencialidade. Este alerta foi removido da lista e é substituído pelo alerta de Reconhecimento do principal de segurança (LDAP). Este erro na interface de utilizador foi corrigido em novembro de 2023.
Versão 2.215 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Relatórios do Defender para Identidade movidos para a área relatórios do main
Agora, pode aceder aos relatórios do Defender para Identidade a partir da área main Reports de Microsoft Defender XDR em vez da área Definições. Por exemplo:
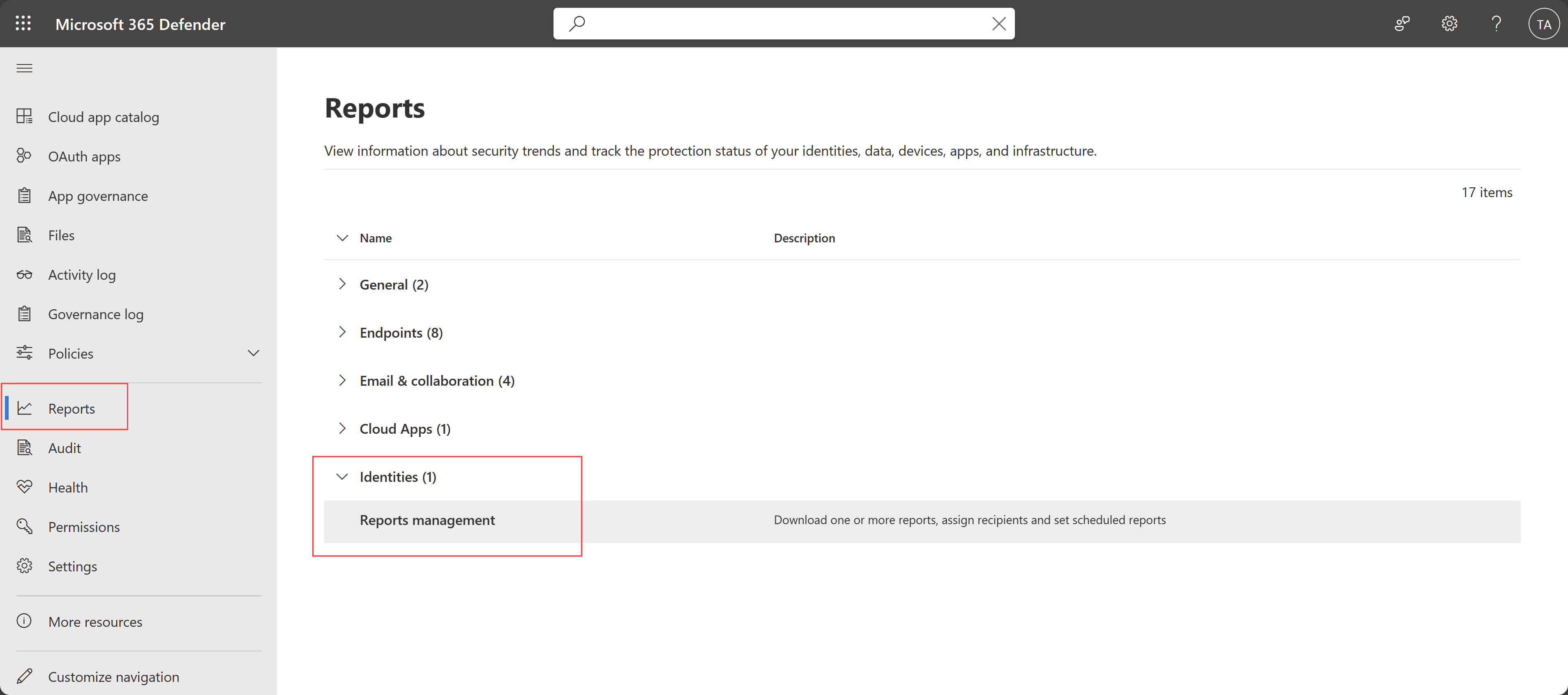
Para obter mais informações, consulte Transferir e agendar relatórios do Defender para Identidade no Microsoft Defender XDR (Pré-visualização).
Botão Go hunt para grupos no Microsoft Defender XDR
O Defender para Identidade adicionou o botão Go hunt para grupos no Microsoft Defender XDR. Os utilizadores podem utilizar o botão Go hunt para consultar atividades e alertas relacionados com grupos durante uma investigação.
Por exemplo:
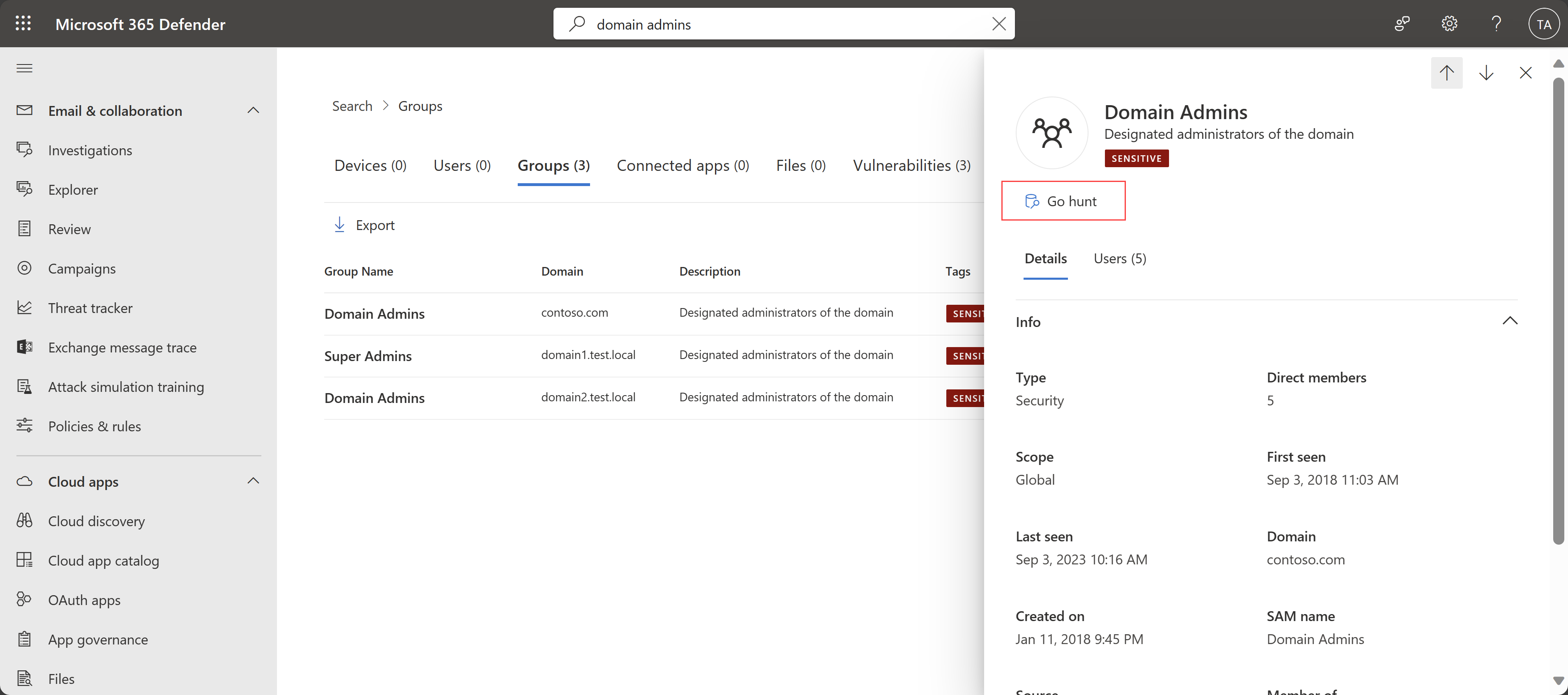
Para obter mais informações, veja Procurar rapidamente informações de entidades ou eventos com go hunt.
Versão 2.214 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Melhoramentos de desempenho
O Defender para Identidade melhorou internamente a latência, a estabilidade e o desempenho ao transferir eventos em tempo real dos serviços do Defender para Identidade para Microsoft Defender XDR. Os clientes não devem esperar atrasos nos dados do Defender para Identidade apresentados no Microsoft Defender XDR, como alertas ou atividades para investigação avançada.
Para saber mais, confira:
- Alertas de segurança no Microsoft Defender para Identidade
- Avaliações da postura de segurança do Microsoft Defender para Identidade
- Proativamente, procure ameaças com investigação avançada em Microsoft Defender XDR
Agosto de 2023
Versão 2.213 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.212 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Versão 2.211 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.
Novo tipo de sensor para os Serviços de Certificados do Active Directory (AD CS)
O Defender para Identidade suporta agora o novo tipo de sensor ADCS para um servidor dedicado com os Serviços de Certificados do Active Directory (AD CS) configurados.
Verá o novo tipo de sensor identificado na página Sensores de Identidades > de Definições > no Microsoft Defender XDR. Para obter mais informações, veja Gerir e atualizar sensores de Microsoft Defender para Identidade.
Juntamente com o novo tipo de sensor, o Defender para Identidade também fornece agora alertas do AD CS relacionados e relatórios de Classificação de Segurança. Para ver os novos alertas e relatórios de Classificação de Segurança, certifique-se de que os eventos necessários estão a ser recolhidos e registados no servidor. Para obter mais informações, veja Configurar a auditoria para eventos dos Serviços de Certificados do Active Directory (AD CS).
O AD CS é uma função Windows Server que emite e gere certificados de infraestrutura de chaves públicas (PKI) em protocolos de comunicação e autenticação seguros. Para obter mais informações, veja O que são os Serviços de Certificados do Active Directory?
Versão 2.210 do Defender para Identidade
Esta versão inclui melhoramentos e correções de erros para serviços cloud e o sensor do Defender para Identidade.