Personalizzare le impostazioni di riservatezza dei dati
Questo articolo descrive come personalizzare le impostazioni di riservatezza dei dati in Microsoft Defender per il cloud.
Le impostazioni di riservatezza dei dati vengono usate per identificare e concentrarsi sulla gestione dei dati sensibili critici nell'organizzazione.
- I tipi di informazioni sensibili e le etichette di riservatezza provenienti da Portale di conformità di Microsoft Purview e che è possibile selezionare in Defender per il cloud. Per impostazione predefinita, Defender per il cloud usa i tipi di informazioni sensibili predefiniti forniti da Portale di conformità di Microsoft Purview. Alcuni tipi di informazioni e etichette sono abilitati per impostazione predefinita, Di questi tipi di informazioni sensibili predefiniti è disponibile un subset supportato dall'individuazione dei dati sensibili. È possibile visualizzare un elenco di riferimenti di questo subset, che elenca anche i tipi di informazioni supportati per impostazione predefinita. La pagina delle impostazioni di riservatezza consente di modificare le impostazioni predefinite.
- Se si importano etichette, è possibile impostare le soglie di riservatezza che determinano il livello di riservatezza minimo per un'etichetta da contrassegnare come sensibile in Defender per il cloud.
Questa configurazione consente di concentrarsi sulle risorse sensibili critiche e migliorare l'accuratezza delle informazioni dettagliate sulla riservatezza.
Prima di iniziare
- Assicurarsi di esaminare i prerequisiti e i requisiti per personalizzare le impostazioni di riservatezza dei dati.
- In Defender per il cloud abilitare le funzionalità di individuazione dei dati sensibili nei piani di Defender CSPM e/o Defender per Archiviazione.
Le modifiche apportate alle impostazioni di riservatezza diventano effettive al successivo rilevamento delle risorse.
Importare tipi/etichette di informazioni di riservatezza personalizzate
I tipi di informazioni di riservatezza e le etichette di riservatezza personalizzati vengono importati automaticamente in Defender per il cloud. Se si ha la licenza Enterprise Mobility and Security E5/A5/G5, non è necessario fornire manualmente il consenso nel portale di Microsoft 365 Defender per importarli. Altre informazioni sulle licenze per l'etichettatura della riservatezza di Microsoft Purview.
Defender per il cloud importa solo etichette di riservatezza con regole di etichettatura automatica. Defender per il cloud ignora la sezione "location" nella regola di etichettatura automatica e applica l'etichetta a tutti i tipi di risorse e le posizioni.
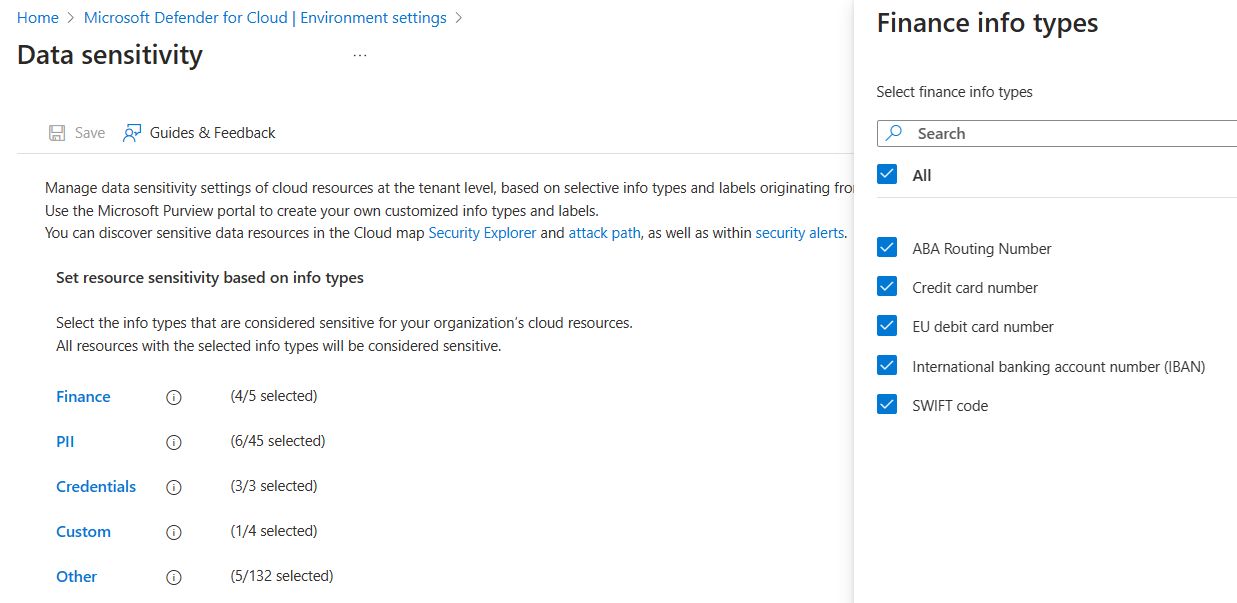
Personalizzare categorie/tipi di dati sensibili
Per personalizzare le impostazioni di riservatezza dei dati visualizzate in Defender per il cloud, esaminare i prerequisiti e quindi eseguire le operazioni seguenti.
Accedere al portale di Azure.
Andare alle impostazioni dell'ambiente Microsoft Defender per il cloud>.
Selezionare Riservatezza dei dati.
Selezionare la categoria del tipo di informazioni da personalizzare:
- Le categorie Finance, PII e Credentials contengono i dati predefiniti del tipo di informazioni ricercati dagli utenti malintenzionati.
- La categoria Custom contiene tipi di informazioni personalizzati dalla configurazione di Portale di conformità di Microsoft Purview.
- La categoria Other contiene tutti gli altri tipi di informazioni disponibili predefiniti.
Selezionare i tipi di informazioni da contrassegnare come sensibili.
Selezionare Applica e Salva.
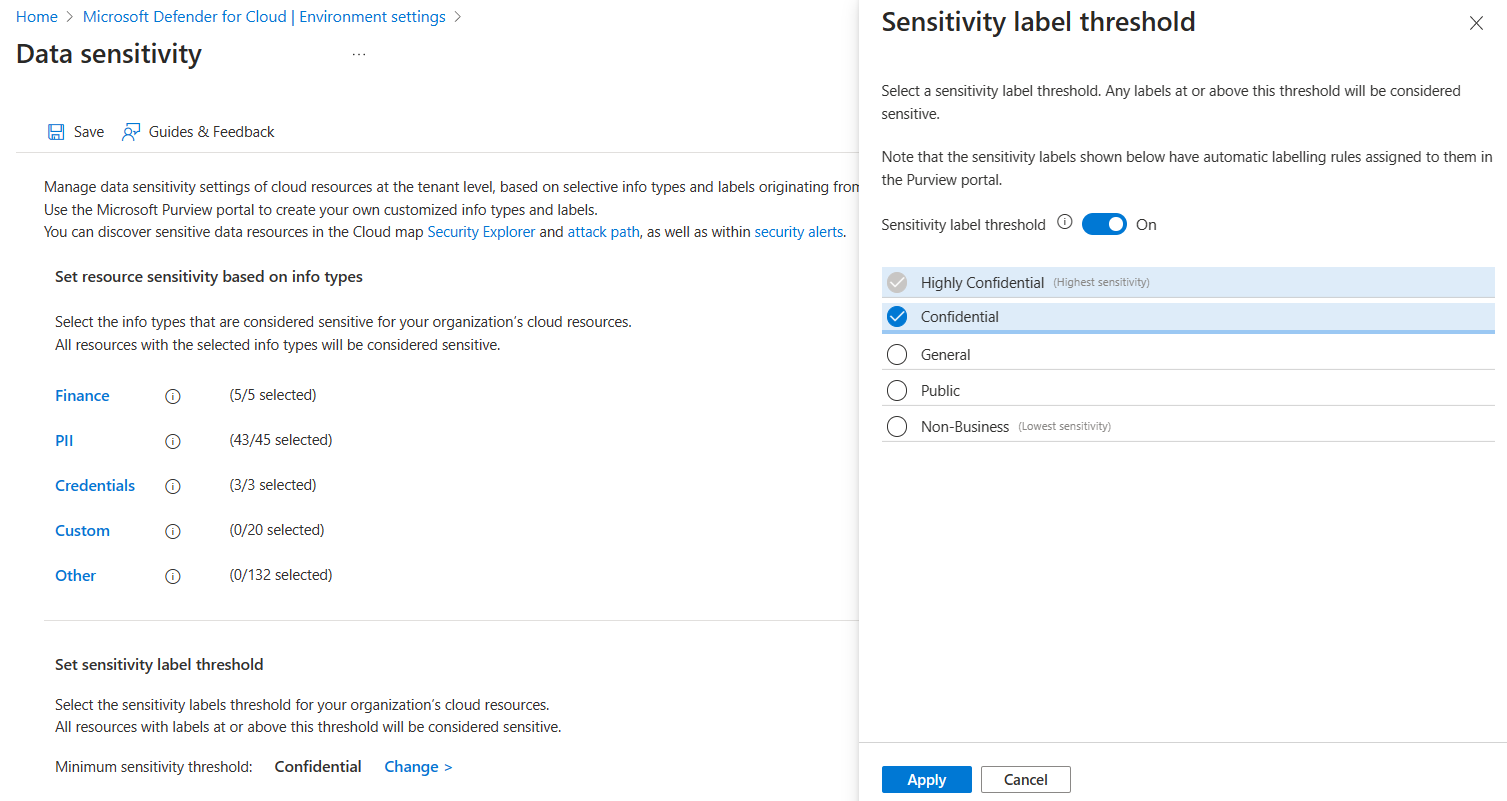
Impostare la soglia per le etichette dati sensibili
Se si usano le etichette di riservatezza di Microsoft Purview, assicurarsi che:
L'ambito dell'etichetta viene impostato su file e altri asset di dati, in cui è necessario configurare la regola di etichettatura automatica.
Le etichette vengono pubblicate con un criterio di etichetta attivo.
È possibile impostare una soglia per determinare il livello di riservatezza minimo per un'etichetta da contrassegnare come sensibile in Defender per il cloud.
Accedere al portale di Azure.
Andare alle impostazioni dell'ambiente Microsoft Defender per il cloud>.
Selezionare Riservatezza dei dati. Viene visualizzata la soglia di riservatezza minima corrente.
Selezionare Cambia per visualizzare l'elenco delle etichette di riservatezza e selezionare l'etichetta di riservatezza più bassa che si vuole contrassegnare come sensibile.
Selezionare Applica e Salva.
Nota
- Quando si attiva la soglia, si seleziona un'etichetta con l'impostazione più bassa che deve essere considerata sensibile nell'organizzazione.
- Qualsiasi risorsa con questa etichetta minima o superiore può contenere dati sensibili.
- Ad esempio, se si seleziona Riservato come minimo, anche Riservatezza elevata viene considerata sensibile. Generale, Pubblico e Non-Business non sono.
- Non è possibile selezionare un'etichetta secondaria nella soglia. Tuttavia, è possibile visualizzare l'etichetta secondaria come etichetta interessata sulle risorse nel percorso di attacco/Cloud Security Explorer, se l'etichetta padre fa parte della soglia (parte delle etichette riservate selezionate).
- Le stesse impostazioni verranno applicate a qualsiasi risorsa supportata (archiviazione oggetti e database).
Passaggio successivo
Esaminare i rischi per i dati sensibili