Utiliser Pare-feu Azure pour gérer et sécuriser les environnements de Windows 365
Cet article explique comment simplifier et protéger votre environnement Windows 365 à l’aide de Pare-feu Azure. L’exemple d’architecture expliqué ici fournit une maintenance faible et un accès automatisé aux points de terminaison requis via un chemin de connexion direct et optimisé. Vous pouvez utiliser des règles de réseau Pare-feu Azure et des balises de nom de domaine complet (FQDN) pour répliquer cet exemple d’architecture dans votre environnement.
Remarque
Cet article s’applique aux clients qui déploient Windows 365 avec des connexions réseau Azure (ANC). Cet article ne s’applique pas aux environnements qui utilisent des réseaux hébergés par Microsoft. Pour plus d’informations sur chacun d’eux, consultez Windows 365 options de déploiement réseau.
Le service Windows 365 nécessite une connectivité optimisée et non proxiée aux points de terminaison de service critiques, dont la plupart résident dans l’infrastructure de Microsoft. La connexion à ces ressources à l’aide de réseaux locaux via Internet est inefficace et n’est pas recommandée. Ces connexions peuvent également être complexes à configurer et à gérer.
Par exemple, certains clients Windows 365 qui utilisent le modèle de déploiement ANC peuvent disposer d’une connexion directe à un environnement local qui utilise ExpressRoute ou VPN de site à site. Le trafic sortant peut être routé à l’aide d’un serveur proxy existant de la même façon que le trafic local. Cette stratégie de connexion n’est pas optimisée pour les environnements Windows 365 et risque d’avoir un impact significatif sur les performances.
Au lieu de cela, vous pouvez utiliser Pare-feu Azure avec vos environnements de Windows 365 ANC pour fournir un accès optimisé, sécurisé, à faible maintenance et automatisé.
Points de terminaison requis pour Windows 365
Windows 365 nécessite l’accès aux points de terminaison suivants :
Vous pouvez également envisager d’accéder à d’autres services Microsoft (comme Office 365) lors de la configuration d’une connectivité optimisée à partir de l’environnement.
Les étiquettes de nom de domaine complet de certains services sont disponibles pour Pare-feu Azure pour faciliter la configuration et la maintenance de ces règles de manière simple. Elles sont décrites plus loin dans ce document.
Exemple d’architecture utilisant des balises Pare-feu Azure et FQDN
Il existe de nombreuses façons de configurer la mise en réseau dans Azure. Ici, nous utilisons :
- Un réseau virtuel unique avec Pare-feu Azure la gestion de l’accès sortant.
- Un circuit ExpressRoute pour reconnecter le réseau virtuel à l’environnement local.
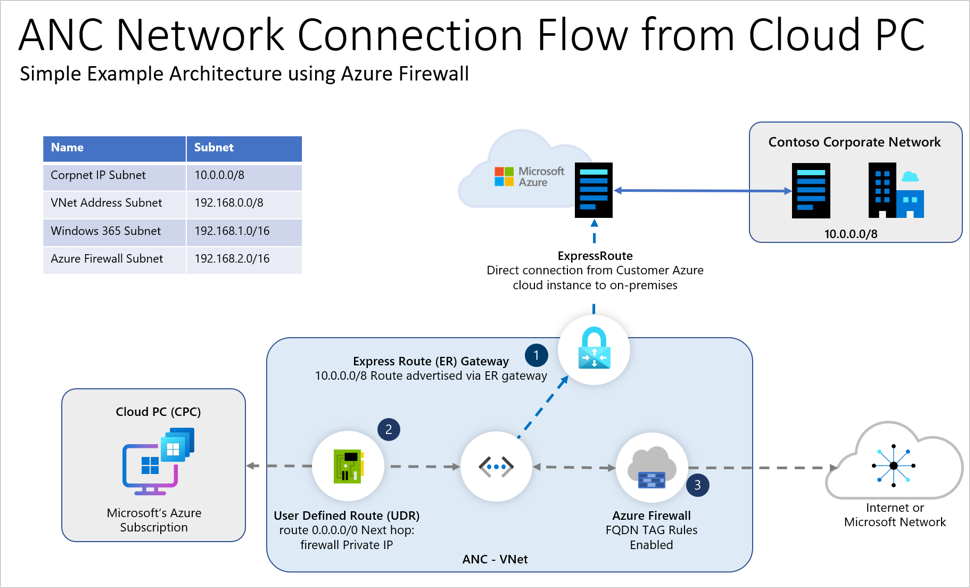
Flux de trafic dans ce diagramme :
- Réseau d’entreprise Contoso : ce sous-réseau IP local est publié dans le réseau virtuel via la passerelle ExpressRoute. Tout le trafic vers cette plage (10.0.0.0/8) est envoyé via le circuit ExpressRoute.
- Tout le trafic provenant du sous-réseau Windows 365 est envoyé au pare-feu Azure via un itinéraire défini par l’utilisateur (UDR) de 0.0.0.0/0. L’adresse IP du tronçon suivant est définie sur l’adresse IP privée de l’Pare-feu Azure.
- Le pare-feu a des règles d’application (et des balises FQDN) et des règles réseau configurées pour les points de terminaison Windows 365 requis. Le trafic conforme aux règles est autorisé. Tout autre trafic non explicitement autorisé est bloqué.
Pare-feu Azure règles d’application
L’environnement dans le diagramme a été configuré à l’aide des règles d’application Pare-feu Azure suivantes (appliquées dans la légende 3). Tout le trafic non destiné au sous-réseau local de Contoso est dirigé vers le pare-feu. Ces règles permettent au trafic défini de revenir à sa destination. Pour plus d’informations sur le déploiement de Pare-feu Azure, consultez Déployer et configurer Pare-feu Azure à l’aide du Portail Azure.
| Description de la règle | Type de destination | Nom de la balise FQDN | Protocole | Inspection TLS | Requis/Facultatif |
|---|---|---|---|---|---|
| noms de domaine complets Windows 365 | Balise FQDN | Windows365 | HTTP : 80, HTTPS : 443 | Non recommandé | Obligatoire |
| noms de domaine complets Intune | Balise FQDN | MicrosoftIntune | HTTP : 80, HTTPS : 443 | Non recommandé | Obligatoire |
| noms de domaine complets Office 365 | Balise FQDN | Office365 | HTTP : 80, HTTPS : 443 | Non recommandé pour optimiser & autoriser les catégories | Facultatif, mais recommandé |
| Windows Update | Balise FQDN | WindowsUpdate | HTTP : 80, HTTPS : 443 | Non recommandé | Facultatif |
| Citrix HDX Plus | Balise FQDN | CitrixHDXPlusForWindows365 | HTTP : 80, HTTPS : 443 | Non recommandé | Facultatif (obligatoire uniquement lors de l’utilisation de Citrix HDX Plus) |
Pare-feu Azure peuvent être associés à des adresses IP publiques pour fournir une connectivité sortante vers Internet. La première adresse IP publique est sélectionnée au hasard pour fournir un SNAT sortant. L’adresse IP publique disponible suivante sera utilisée une fois que tous les ports SNAT de la première adresse IP seront épuisés. Dans les scénarios nécessitant un débit élevé, il est recommandé de tirer parti d’une passerelle Azure NAT. La passerelle NAT met à l’échelle dynamiquement la connectivité sortante et peut être intégrée à un Pare-feu Azure. Pour obtenir de l’aide, consultez le tutoriel Intégrer la passerelle NAT à Pare-feu Azure.
Balise Windows365
La balise Windows365 inclut les points de terminaison Azure Virtual Desktop (AVD) requis, à l’exception des points de terminaison avec des ports non standard qui doivent être entrés manuellement (voir la section Règles réseau).
La balise Windows365 n’inclut pas Intune. La balise MicrosoftIntune peut être utilisée séparément.
La balise FQDN Windows365 inclut tous les points de terminaison requis, à l’exception des points de terminaison répertoriés comme Obligatoires dans des lignes distinctes de ce document, qui doivent être configurés séparément. Les étiquettes FQDN sont différentes d’une étiquette de service. Par exemple, l’étiquette de service WindowsVirtualDesktop inclut uniquement les adresses IP que *.wvd.microsoft.com résout.
Règles de réseau
Pare-feu Azure ne gère actuellement pas les ports non standard dans une balise FQDN. Windows 365 a quelques exigences de port non standard. Les règles suivantes doivent donc être ajoutées manuellement en tant que règles réseau en plus des balises FQDN.
| Description de la règle | Type de destination | Nom de domaine complet/adresse IP | Protocole | Port/s | Inspection TLS | Requis/Facultatif |
|---|---|---|---|---|---|---|
| Windows Activation | FQDN | azkms.core.windows.net | TCP | 1688 | Non recommandé | Obligatoire |
| Inscription | FQDN | global.azure-devices-provisioning.net | TCP | 443, 5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-prod-preu01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-prod-prap01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-prod-prna01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-prod-prau01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-prod-prna02.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-2-prod-prna01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-3-prod-prna01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-2-prod-preu01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-3-prod-preu01.azure-devices.net | TCP | 443,5671 | Non recommandé | Obligatoire |
| Connectivité UDP via TURN | IP | 20.202.0.0/16 | UDP | 3478 | Non recommandé | Obligatoire |
| Connectivité TURN | IP | 20.202.0.0/16 | TCP | 443 | Non recommandé | Obligatoire |
| Inscription | FQDN | hm-iot-in-4-prod-prna01.azure-devices.net | TCP | 443, 5671 | Non recommandé | Obligatoire |
Options de solution de sécurité partenaire
D’autres moyens de protéger votre environnement Windows 365 sont les options de solution de sécurité des partenaires qui fournissent des ensembles de règles automatisés pour accéder aux points de terminaison requis pour le service Windows 365. Ces options sont les suivantes :
- objets Check Point Software Technologies pouvant être mis à jour
Étapes suivantes
En savoir plus sur l’architecture Windows 365.
Pour en savoir plus sur les noms de domaine complets, consultez Vue d’ensemble des balises FQDN.
Pour en savoir plus sur les étiquettes de service, consultez Balises de service de réseau virtuel.