Learn about insider risk management policy templates
Important
Microsoft Purview Insider Risk Management correlates various signals to identify potential malicious or inadvertent insider risks, such as IP theft, data leakage, and security violations. Insider risk management enables customers to create policies to manage security and compliance. Built with privacy by design, users are pseudonymized by default, and role-based access controls and audit logs are in place to help ensure user-level privacy.
Policy templates
Insider risk management templates are pre-defined policy conditions that define the types of risk indicators and risk scoring model used by the policy. Each policy must have a template assigned in the policy creation workflow before the policy is created. Insider risk management supports up to twenty policies for each policy template. When you create a new insider risk policy with the policy workflow, choose from one of the following policy templates:
Tip
Get started with Microsoft Security Copilot to explore new ways to work smarter and faster using the power of AI. Learn more about Microsoft Security Copilot in Microsoft Purview.
Data theft by departing users
When users leave your organization, there are specific risk indicators typically associated with potential data theft by departing users. This policy template uses exfiltration indicators for risk scoring and focuses on detection and alerts in this risk area. Data theft for departing users might include downloading files from SharePoint Online, printing files, and copying data to personal cloud messaging and storage services near their employment resignation and end dates. When you use either the Microsoft HR connector or the option to automatically check for user account deletion in Microsoft Entra for your organization, this template starts scoring for risk indicators relating to these activities and how they correlate with user employment status. This can include cloud indicators for services such as Box, Dropbox, Google Drive, Amazon S3, and Azure.
Important
When using this template, you can configure a Microsoft 365 HR connector to periodically import resignation and termination date information for users in your organization. See the Import data with the HR connector article for step-by-step guidance to configure the Microsoft 365 HR connector. If you choose not to use the HR connector, you must select the User account deleted from Microsoft Entra option when configuring trigger events in the policy workflow.
Data leaks
Protecting data and preventing data leaks is a constant challenge for most organizations, particularly with the rapid growth of new data created by users, devices, and services. Users are empowered to create, store, and share information across services and devices that make managing data leaks increasingly more complex and difficult. Data leaks can include accidental oversharing of information outside your organization or data theft with malicious intent. This template scores real-time detections of suspicious SharePoint Online data downloads, file and folder sharing, printing files, and copying data to personal cloud messaging and storage services.
When using a Data leaks template, you can assign a DLP policy to trigger indicators in the insider risk policy for high severity alerts in your organization. Whenever a high severity alert is generated by a DLP policy rule is added to the Office 365 audit log, insider risk policies created with this template automatically examine the high severity DLP alert. If the alert contains an in-scope user defined in the insider risk policy, the alert is processed by the insider risk policy as a new alert and assigned an insider risk severity and risk score. You can also choose to assign selected indicators as triggering events for a policy. This flexibility and customization helps scope the policy to only the activities covered by the indicators. This policy allows you to evaluate this alert in context with other activities included in the case.
This template can also include cloud indicators for services such as Box, Dropbox, Google Drive, Amazon S3, and Azure.
Data leaks policy guidelines
When creating or modifying data loss prevention policies for use with insider risk management policies, consider the following guidelines:
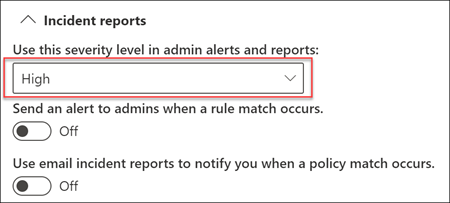
Prioritize data exfiltration events and be selective when assigning Incident reports settings to High when configuring rules in your DLP policies. For example, emailing sensitive documents to a known competitor should be a High alert level exfiltration event. Over-assigning the High level in the Incident reports settings in other DLP policy rules can increase the noise in the insider risk management alert workflow and make it more difficult for your data investigators and analysts to properly evaluate these alerts. For example, assigning High alert levels to access denial activities in DLP policies makes it more challenging to evaluate truly risky user behavior and activities.
When using a DLP policy as the triggering event, make sure you understand and properly configure the in-scope users in both the DLP and insider risk management policies. Only users defined as in-scope for insider risk management policies using the Data leaks template will have high severity DLP policy alerts processed. Additionally, only users defined as in-scope in a rule for a high severity DLP alert are analyzed by the insider risk management policy for consideration. It's important that you don't unknowingly configure in-scope users in both your DLP and insider risk policies in a conflicting manner.
For example, if your DLP policy rules are scoped to only users on the Sales Team and the insider risk policy created from the Data leaks template has defined all users as in-scope, the insider risk policy will only process high severity DLP alerts for the users on the Sales Team. The insider risk policy won't receive any high priority DLP alerts for users to process that aren't defined in the DLP rules in this example. Conversely, if your insider risk management policy created from Data leaks templates is scoped to only users on the Sales Team and the assigned DLP policy is scoped to all users, the insider risk policy will only process high severity DLP alerts for members of the Sales Team. The insider risk management policy will ignore high severity DLP alerts for all users not on the Sales Team.
Make sure the Incident reports rule setting in the DLP policy used for this insider risk management template is configured for High severity level alerts. The High severity level is the triggering events and insider risk management alerts won't be generated from rules in DLP policies with the Incident reports field set at Low or Medium.
Note
When creating a new DLP policy using the built-in templates, you'll need to select the Create or customize advanced DLP rules option to configure the Incident reports setting for the High severity level.
Each insider risk management policy created from the Data leaks template can only have one DLP policy assigned when using this triggering event option. Consider creating a dedicated DLP policy that combines the different activities you want to detect and act as triggering events for insider risk policies that use the Data leaks template.
See the Create and Deploy data loss prevention policies article for step-by-step guidance to configure DLP policies for your organization.
Data leaks by priority users
Protecting data and preventing data leaks for users in your organization might depend on their position, level of access to sensitive information, or risk history. Data leaks can include accidental oversharing of highly sensitive information outside your organization or data theft with malicious intent. With an assigned data loss prevention (DLP) policy as a triggering event option, this template starts scoring real-time detections of suspicious activity and result in an increased likelihood of insider risk alerts and alerts with higher severity levels. Priority users are defined in priority user groups configured in the insider risk management settings area.
As with the Data leaks template, you can choose a DLP policy to trigger indicators in the insider risk policy for high severity alerts in your organization. Follow the Data leaks policy guidelines for DLP policies when creating a policy with the DLP option when using this template. You can also choose to assign selected indicators as triggering events for a policy. This flexibility and customization help scope the policy to only the activities covered by the indicators. Additionally, you need to assign priority user groups created in Insider risk management > Settings > Priority user groups to the policy.
Data leaks by risky users
When users experience employment stressors, they might become risky users, which might increase the chances of insider risk activity. This template starts scoring user activity when an indicator associated with risky user is identified. Examples include performance improvement notifications, poor performance reviews, changes to job level status, or email and other messages that might signal risk activities. Data leaks for risky users might include downloading files from SharePoint Online and copying data to personal cloud messaging and storage services.
When using this template, you must either configure an HR connector, select the option to integrate communication compliance risk signals from user messages, or do both. The HR connector enables the periodic import of performance improvement notifications, poor performance review statuses, or job level change information for users in your organization. Communication compliance risk integration imports signals for user messages that might contain potentially threatening, harassing, or discriminatory text content. Associated alerts generated in Communication Compliance don't need to be triaged, remediated, or changed in status to be integrated with the insider risk management policy.
To configure an HR connector, see the Import data with the HR connector article. To configure integration with communication compliance, select this option in the workflow when you configure the policy.
Patient data misuse (preview)
Protecting healthcare record data and preventing the misuse of patient personal data is a significant concern for organizations in the healthcare industry. This misuse might include confidential data leaks to unauthorized persons, fraudulent modification of patient records, or the theft of patient healthcare records. Preventing this misuse of patient data is helps meet the regulatory requirements of the Health Insurance Portability and Accountability Act (HIPAA) and the Health Information Technology for Economic and Clinical Health (HITECH) Act. Both of these acts establish the requirements for safeguarding patient protected health information (PHI).
This policy template enables risk scoring for internal users that detects suspicious activities associated with records hosted on existing electronic medical record (EMR) systems. Detection focuses on unauthorized access, viewing, modification, and export of patient data. You need to configure a connector the Microsoft Healthcare connector to support detection of access, exfiltration, or obfuscation activities in your EMR system.
When using this template, you must also configure a Microsoft HR connector to periodically import organization profile data for users in your organization. See the Set up a connector to import HR data article for step-by-step guidance to configure the Microsoft 365 HR connector.
Risky AI usage (preview)
The use of AI tools and applications in many organizations presents new risk opportunities that might be difficult to identify and help mitigate. Users might inadvertently or purposefully created prompts in Microsoft AI tools that might contain sensitive information or risky intent. Additionally, AI tools might inappropriately use sensitive information to provide responses to user prompts that might expose your organization to increased risks.
To help protect against these risks, this policy can help detect and enable risk scoring for these types of prompts and responses across AI tools in your organization. Detection focuses on user browsing activities to generative AI websites, user prompts and AI responses containing sensitive information in Microsoft 365 Copilot and Microsoft Copilot. Detection of risky activity by this policy also contributes to the user risk scoring in Adaptive Protection.
When using this template, you must configure the Microsoft Insider risk extension (on Microsoft Edge browser) or Microsoft Purview extension (on Chrome browser) on the user devices. We also recommend optionally configuring a Microsoft HR connector to detect departing users and configuring a communication compliance policy to detect inappropriate content in messages for wider detection coverage. This policy can also be created as a quick policy in the AI hub.
Risky browser usage (preview)
Identifying user visitation to potentially inappropriate or unacceptable web sites on organization devices and networks is an important part of minimizing security, legal, and regulatory risks. Users that inadvertently or purposefully visit these types of websites might expose the organization to legal actions from other users, violate regulatory requirements, elevate network security risks, or jeopardize current and future business operations and opportunities. This misuse is often defined in an organization's acceptable use policy for user devices and organization network resources but is often difficult to quickly identify and act on.
To help protect against these risks, this policy can help detect and enable risk scoring for web browsing that might be in violation of your organization's acceptable use policy, such as visiting sites that pose a threat (phishing sites, for example) or that contain adult content. Several types of categories are available for automatic categorization of web browsing activities by in-scope users.
This policy template has several prerequisites. For more information, see Learn about and configure insider risk management browser signal detection.
Security policy violations (preview)
In many organizations, users have permission to install software on their devices or to modify device settings to help with their tasks. Either inadvertently or with malicious intent, users might install malware or disable important security features that help protect information on their device or on your network resources. This policy template uses security alerts from Microsoft Defender for Endpoint to start scoring these activities and focus detection and alerts to this risk area. Use this template to provide insights for security policy violations in scenarios when users might have a history of security policy violations that might be an indicator of insider risk.
You need to configure Microsoft Defender for Endpoint in your organization and enable Defender for Endpoint for insider risk management integration in the Defender Security Center to import security violation alerts. For more information on configuring Defender for Endpoint for insider risk management integration, see Configure advanced features in Defender for Endpoint.
Security policy violations by departing users (preview)
Departing users, whether they're leaving on positive or negative terms, might be higher risks for security policy violations. To help protect against inadvertent or malicious security violations for departing users, this policy template uses Defender for Endpoint alerts to provide insights into security-related activities. These activities include the user installing malware or other potentially harmful applications and disabling security features on their devices. When you use the Microsoft HR connector or the option to automatically check for user account deletion in Microsoft Entra for your organization, this template starts scoring for risk indicators relating to these security activities and how they correlate with user employment status.
You need to configure Microsoft Defender for Endpoint in your organization and enable Defender for Endpoint for insider risk management integration in the Defender Security Center to import security violation alerts. For more information on configuring Defender for Endpoint for insider risk management integration, see Configure advanced features in Defender for Endpoint.
Security policy violations by priority users (preview)
Protecting against security violations for users in your organization might depend on their position, level of access to sensitive information, or risk history. Because security violations by priority users might have a significant impact on your organization's critical areas, this policy template starts scoring on these indicators, and uses Microsoft Defender for Endpoint alerts to provide insights into security-related activities for these users. These activities might include the priority users installing malware or other potentially harmful applications and disabling security features on their devices. Priority users are defined in priority user groups configured in the insider risk management settings area.
You need to configure Microsoft Defender for Endpoint in your organization and enable Defender for Endpoint for insider risk management integration in the Defender Security Center to import security violation alerts. For more information on configuring Defender for Endpoint for insider risk management integration, see Configure advanced features in Defender for Endpoint. Additionally, you need to assign priority user groups created in Insider risk management > Settings > Priority user groups to the policy.
Security policy violations by risky users (preview)
Users that experience employment stressors might be at a higher risk for inadvertent or malicious security policy violations. These stressors could include a user being placed on a performance improvement plan, having a poor performance review, or experiencing a demotion. This policy template starts risk scoring based on these indicators and activities associated with these types of events.
When using this template, you must configure an HR connector, or select the option to integrate communication compliance risk signals from user messages, or both. The HR connector enables the periodic import of performance improvement notifications, poor performance review statuses, or job level change information for users in your organization. Communication compliance risk integration imports signals for user messages that might contain potentially threatening, harassing, or discriminatory text content. Associated alerts generated in communication compliance don't need to be triaged, remediated, or changed in status to be integrated with the insider risk management policy. To configure an HR connector, see the Import data with the HR connector article. To configure integration with communication compliance, select this option in the workflow when you configure the policy.
You also need to configure Microsoft Defender for Endpoint in your organization and enable Defender for Endpoint for insider risk management integration in the Defender Security Center to import security violation alerts. For more information on configuring Defender for Endpoint for insider risk management integration, see Configure advanced features in Defender for Endpoint.
Policy template prerequisites and triggering events
Depending on the template you choose for an insider risk management policy, the triggering events and policy prerequisites vary. Triggering events are prerequisites that determine if a user is active for an insider risk management policy. If a user is added to an insider risk management policy but doesn't have a triggering event, the user activity isn't evaluated by the policy unless they're manually added in the Users dashboard. Policy prerequisites are required items so that the policy receives the signals or activities necessary to evaluate risk.
The following table lists the triggering events and prerequisites for policies created from each insider risk management policy template:
| Policy template | Triggering events for policies | Prerequisites |
|---|---|---|
| Data theft by departing users | Resignation or termination date indicator from HR connector or Microsoft Entra account deletion | (optional) Microsoft 365 HR connector configured for termination and resignation date indicators |
| Data leaks | Data leak policy activity that creates a High severity alert or built-in exfiltration event triggers | DLP policy configured for High severity alerts OR Customized triggering indicators |
| Data leaks by priority users | Data leak policy activity that creates a High severity alert or built-in exfiltration event triggers | DLP policy configured for High severity alerts OR Customized triggering indicators Priority user groups configured in insider risk settings |
| Data leaks by risky users | - Performance improvement, poor performance, or job level change indicators from HR connector. - Messages containing potentially threatening, harassing, or discriminatory language |
Microsoft 365 HR connector configured for disgruntlement indicators AND/OR Communication Compliance integration and dedicated disgruntlement policy |
| Security policy violations | Defense evasion of security controls or unwanted software detected by Microsoft Defender for Endpoint | Active Microsoft Defender for Endpoint subscription Configuration of Microsoft Defender for Endpoint integration with Microsoft Purview compliance portal |
| Patient data misuse | Defense evasion of security controls from EMR systems User and patient address matching indicators from HR systems |
Healthcare access indicators selected in policy or insider risk settings Microsoft 365 HR connector configured for address matching Microsoft Healthcare connector configured |
| Risky AI usage | Microsoft Insider risk extension (on Microsoft Edge browser) or Microsoft Purview extension (on Chrome browser) must be installed on the user's devices At least one browsing indicator selected in the policy AND (optional) Microsoft 365 HR connector configured for termination and resignation date indicators (optional) A communication compliance policy detecting inappropriate content in messages |
|
| Risky browser usage | User browsing activity related to security that matches at least one selected Browsing indicator | See the complete list of prerequisites in the browser signal detection article |
| Security policy violations by departing users | Resignation or termination date indicators from HR connector or Microsoft Entra account deletion | (optional) Microsoft 365 HR connector configured for termination and resignation date indicators Active Microsoft Defender for Endpoint subscription Configuration of Microsoft Defender for Endpoint integration with Microsoft Purview compliance portal |
| Security policy violations by priority users | Defense evasion of security controls or unwanted software detected by Microsoft Defender for Endpoint | Active Microsoft Defender for Endpoint subscription Configuration of Microsoft Defender for Endpoint integration with Microsoft Purview compliance portal Priority user groups configured in insider risk settings |
| Security policy violations by risky users | - Performance improvement, poor performance, or job level change indicators from HR connector. - Messages containing potentially threatening, harassing, or discriminatory language |
Microsoft 365 HR connector configured for risk indicators AND/OR Communication Compliance integration and dedicated risky user policy AND Active Microsoft Defender for Endpoint subscription Configuration of Microsoft Defender for Endpoint integration with Microsoft Purview compliance portal |
Policy template limits
Insider risk management policy templates use limits to manage the volume and rate of processing for in-scope user risk activities and for integration with supporting Microsoft 365 services. Each policy template has a maximum number of users that can be actively assigned risk scores for the policy that it can support and effectively process and report potentially risky activities. In-scope users are users with triggering events for the policy.
The limit for each policy is calculated based on the total number of unique users receiving risk scores per policy template type. If the number of users for a policy template type is near or exceeds the user limit, the policy performance is reduced. To view the current number of users for a policy, navigate to the Policy tab and the Users in scope column. These maximum limits apply to users across all policies using a given policy template.
You can have up to 20 policies for any policy template.
Use the following table to determine the maximum number of in-scope users supported for each policy template. These maximum limits apply to users across all policies using a given policy template.
| Policy template | In-scope user maximum |
|---|---|
| General data leak | 15,000 |
| Data leak by risky users | 7,500 |
| Data leak by priority users | 1,000 |
| Data theft by departing users | 20,000 |
| Security policy violations | 1,000 |
| Patient data misuse | 5,000 |
| Risky AI usage | 10,000 |
| Risky browser usage | 7,000 |
| Security policy violation by priority users | 1,000 |
| Security policy violations by departing users | 15,000 |
| Security policy violations by risky users | 7,500 |
| Forensic evidence | Unlimited |
Note
The number of in-scope users for a policy is displayed in the Users in scope column on the Policies tab.