Azure AD Security – Protect Those Accounts, Services, and Audit Access!
Everyday I’m asked questions about Enterprise Mobility + Security as well as other Microsoft services. I’m also asked how we can provide single-sign on to SaaS and on-premises applications using Azure AD Premium. What surprises me though is how few organizations ask me about providing additional protection layers to protect accounts as well as the services themselves from credentials that have been compromised (unless I bring the topic up). However, not a day goes by where I’m not asked about second factor authentication (i.e. Multi-Factor Authentication). Although MFA is extremely important and I highly recommend turning it on and testing within your organization, there are other important security mechanisms that can be turned on as well.
As you may have heard, identity is the new control plane, meaning protection starts at the account.
Azure AD Identity Protection
Do you have cloud only accounts or are you synchronizing your Active Directory accounts to Azure AD (e.g. O365, Dynamics CRM, etc.)? If you’re using O365 then you are, regardless of what identity provider you’re using. Azure AD Identity Protection can help you secure those identity today.
In a previous post I walked through setting up and implementing Azure AD Identity Protection, however below is a video where in the first half I log in as a user using a Tor browser and I’m able to access the service without challenge. In the second half, I turn on identity protection and when I attempt to sign on using a Tor browser, I’m challenged with multi-factor. A simple sign-on policy can protect you and your users from irregular sign-on activity and stolen credentials.
Azure AD Privileged Identity Management (PIM)
Protecting the account itself is in my opinion non-negotiable and if you’re using Azure, O365, Dynamics CRM, Intune, or any other Microsoft services that leverage Azure AD, I highly recommend turning on Azure AD Identity Protection. However, what about protecting access to the service itself? You can by using Azure AD Privileged Identity Management.
What is Azure AD Privileged Identity Management?
Organizations want to minimize the number of people who have access to secure information or resources, because that reduces the chance of a malicious user getting that access. However, users still need to carry out privileged operations in Azure, Office 365, or SaaS apps. Organizations give users privileged access in Azure AD without monitoring what those users are doing with their admin privileges. Azure AD Privileged Identity Management helps to resolve this risk.
Azure AD Privileged Identity Management helps you:
- See which users are Azure AD administrators
- Enable on-demand, "just in time" administrative access to Microsoft Online Services like Office 365 and Intune
- Get reports about administrator access history and changes in administrator assignments
- Get alerts about access to a privileged role
Azure AD Privileged Identity Management can manage the built-in Azure AD organizational roles, including:
- Global Administrator
- Billing Administrator
- Service Administrator
- User Administrator
- Password Administrator
However, those are not the only roles available, did you know Exchange Online, Skype for Business, Intune, and many other roles are available as well? Which means global admins can protect access to elevated admin permissions and require admins to request access as well as provide additional info before their credentials are elevated.
More details about additional roles available in Azure AD PIM here: /en-us/azure/active-directory/active-directory-privileged-identity-management-roles
The following video steps through a user elevating permissions to access the admin console for Skype for Business using Azure AD Privileged Identity Management. The user is only allowed one hour to accomplish their task (global admin can adjust the policy to span 1 to 72 hours if needed per role), once the one hour is up, the user would need to go through the process again to elevate their account permissions.
Reporting
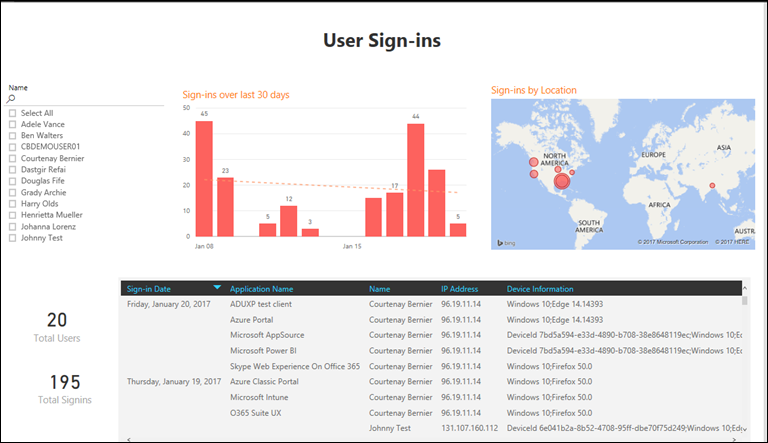
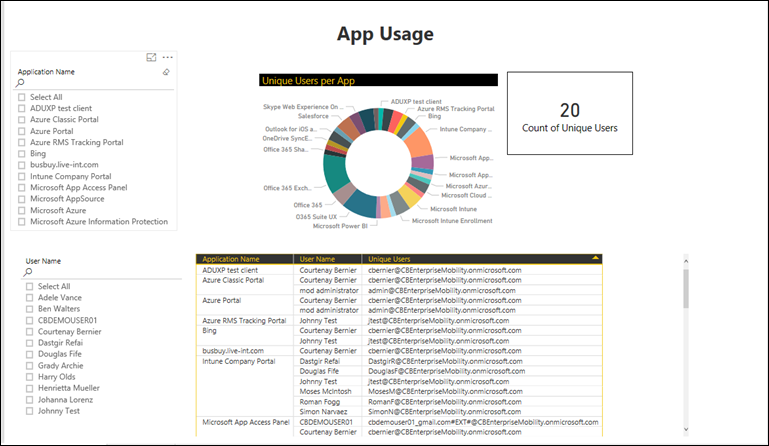
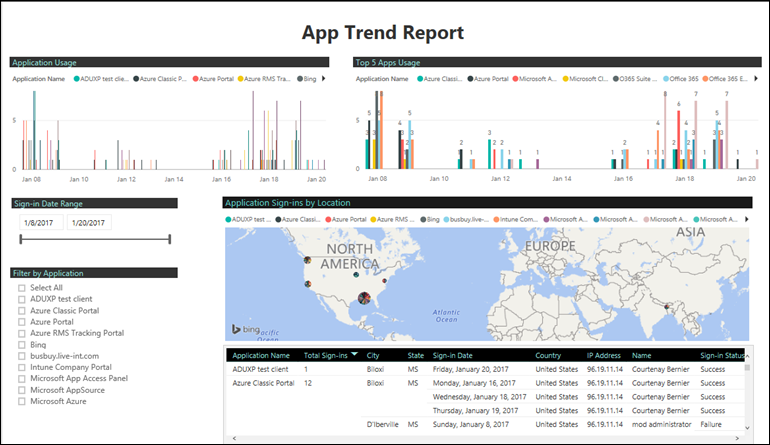
Reporting on identity and access is critical as well. It’s important to have systems in place to protect identities and services, however it’s equally important to have insight as to who’s accessing the services, from where, from what, how, and when. Last week the Azure AD team announced an Azure AD content pack for Power BI.
Here are a few reports from a fresh environment I’ve created:
For more details on how to get started with Azure AD and the Power BI content pack please visit: https://powerbi.microsoft.com/en-us/blog/azure-active-directory-meets-power-bi/preview/
I encourage everyone to start protecting your identities and services today. There’s always going to be risk, why not reduce the risk by implementing safeguards to prevent unchallenged access.