Implantar o Azure Local, versão 23H2 por meio do modelo de implantação do Azure Resource Manager
Aplica-se a: Azure Local 2311.2 e posterior
Este artigo detalha como usar um modelo do Azure Resource Manager no portal do Azure para implantar um Azure Local em seu ambiente. O artigo também contém os pré-requisitos e as etapas de preparação necessárias para iniciar a implantação.
Importante
A implantação do modelo do Azure Resource Manager de sistemas Azure Local, versão 23H2, é direcionada para implantações em escala. O público-alvo dessa implantação são os administradores de TI com experiência na implantação de instâncias locais do Azure. Recomendamos que você implante um sistema versão 23H2 por meio do portal do Azure primeiro e, em seguida, execute implantações subsequentes por meio do modelo do Resource Manager.
Pré-requisitos
- Conclusão de Registrar seus computadores no Azure Arc e atribuir permissões de implantação. Certifique-se de que:
- Todas as extensões obrigatórias são instaladas com sucesso. As extensões obrigatórias incluem: Azure Edge Lifecycle Manager, Azure Edge Device Management, Telemetria e Diagnóstico e Suporte Remoto do Azure Edge.
- Todas as máquinas estão executando a mesma versão do sistema operacional.
- Todas as máquinas têm a mesma configuração de adaptador de rede.
Etapa 1: Preparar recursos do Azure
Siga estas etapas para preparar os recursos do Azure necessários para a implantação:
Criar uma entidade de serviço e um segredo do cliente
Para autenticar seu sistema, você precisa criar uma entidade de serviço e um segredo do cliente correspondente para o Arc Resource Bridge (ARB).
Criar uma entidade de serviço para ARB
Siga as etapas em Criar um aplicativo e uma entidade de serviço do Microsoft Entra que possa acessar recursos por meio do portal do Azure para criar a entidade de serviço e atribuir as funções. Como alternativa, use o procedimento do PowerShell para criar uma entidade de serviço do Azure com o Azure PowerShell.
As etapas também estão resumidas aqui:
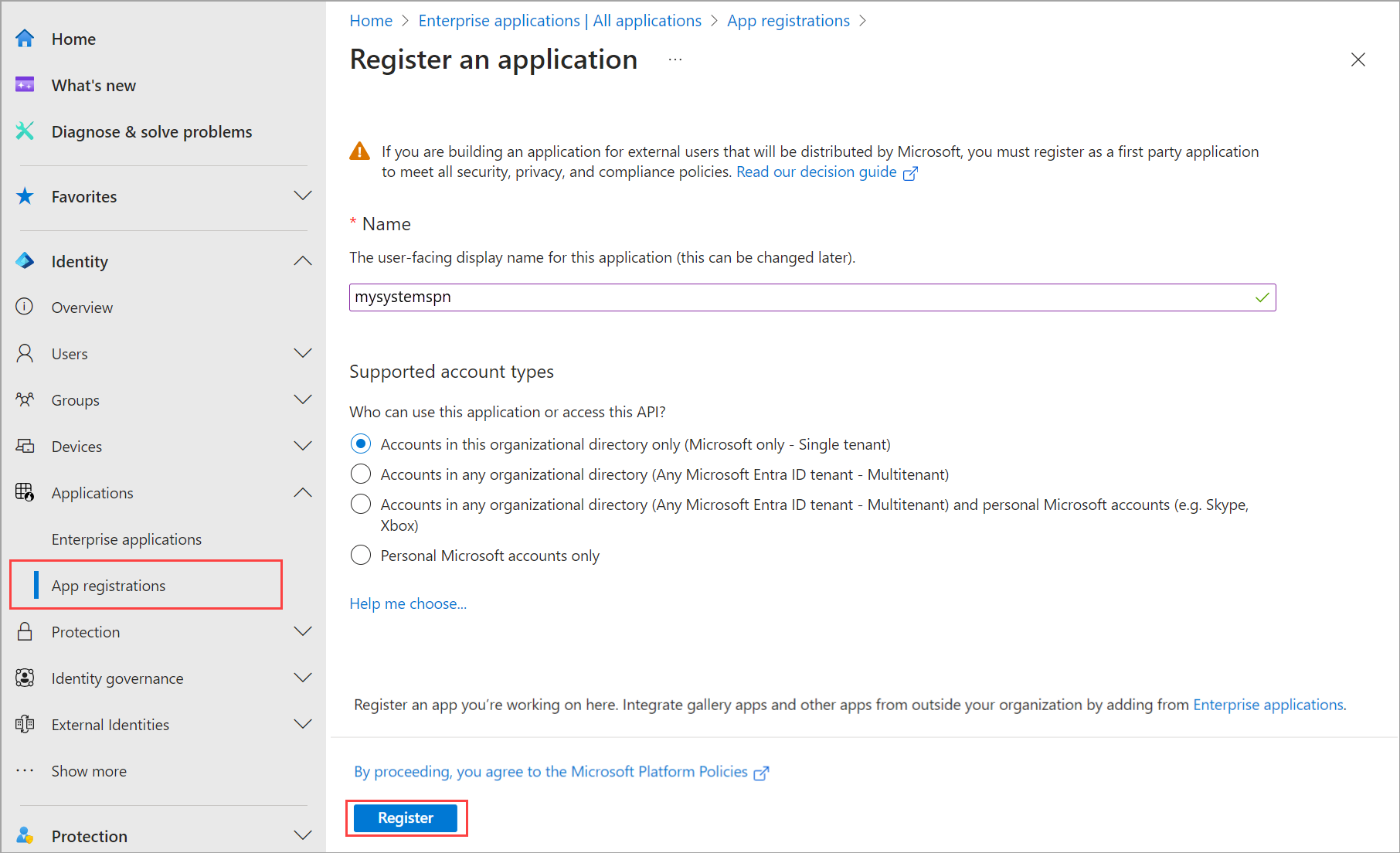
Entre no centro de administração do Microsoft Entra como pelo menos um Administrador de Aplicativos de Nuvem. Navegue até > identidade e selecione Novo registro.
Forneça um Nome para o aplicativo, selecione um Tipo de conta com suporte e, em seguida, selecione Registrar.
Depois que a entidade de serviço for criada, vá para a página Aplicativos empresariais . Pesquise e selecione o SPN que você criou.
Em propriedades, copie a ID do aplicativo (cliente) e a ID do objeto para essa entidade de serviço.
Você usa a ID do
arbDeploymentSPNObjectIDManager.
Criar um segredo do cliente para a entidade de serviço ARB
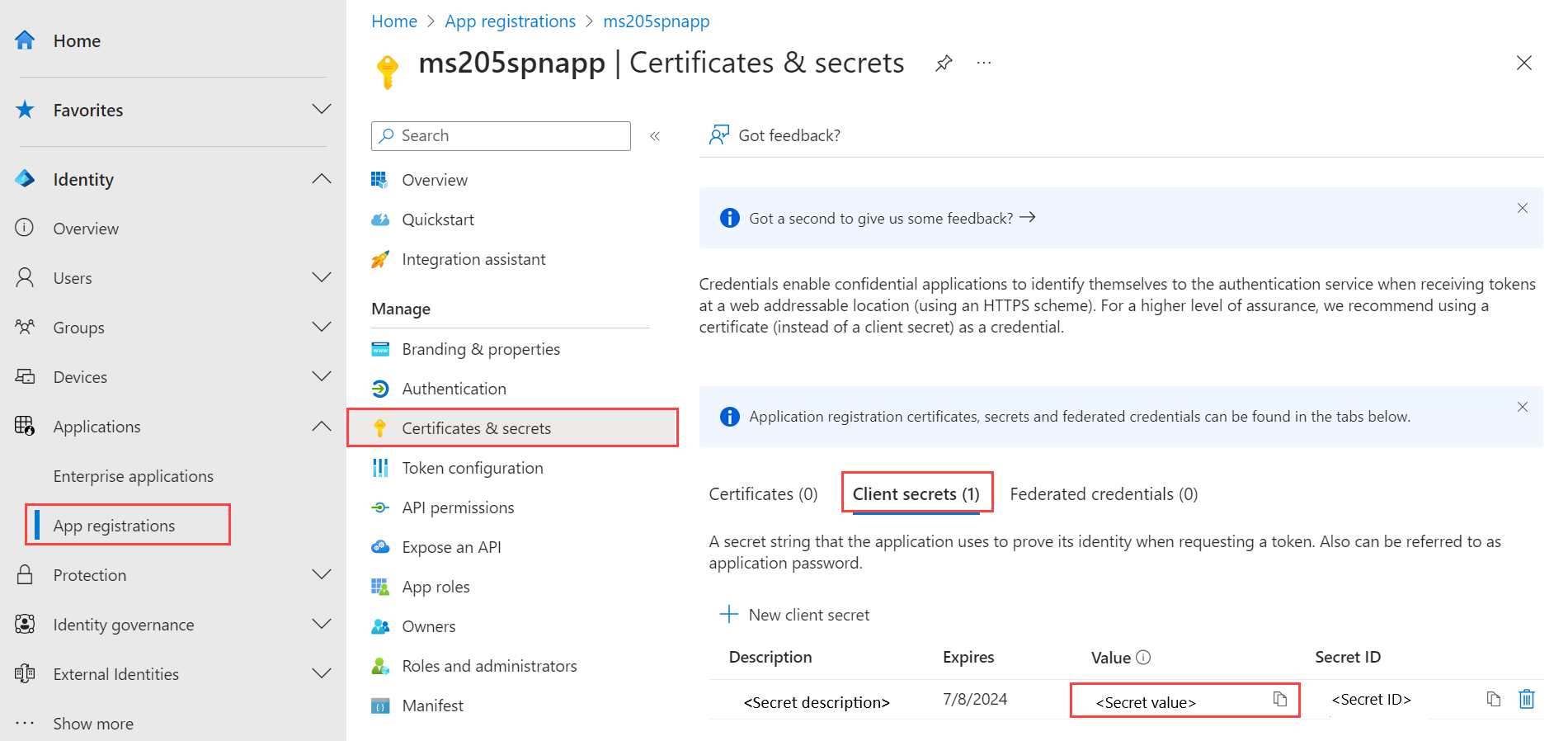
Vá para o registro do aplicativo que você criou e navegue até Certificados e segredos > Segredos do cliente.
Selecione + Novo segredo do cliente.
Adicione uma Descrição para o segredo do cliente e forneça um período de tempo quando ele expirar. Selecione Adicionar.
Copie o valor do segredo do cliente à medida que o usar mais tarde.
Observação
Para a ID do cliente do aplicativo, você precisará do valor secreto. Os valores secretos do cliente não podem ser exibidos, exceto imediatamente após a criação. Certifique-se de salvar esse valor quando criado antes de sair da página.
Use o valor do segredo do cliente em relação ao
arbDeploymentAppSecretparâmetro no modelo do Resource Manager.
Obter a ID do objeto para o Provedor de Recursos Local do Azure
Essa ID de objeto para o RP Local do Azure é exclusiva por locatário do Azure.
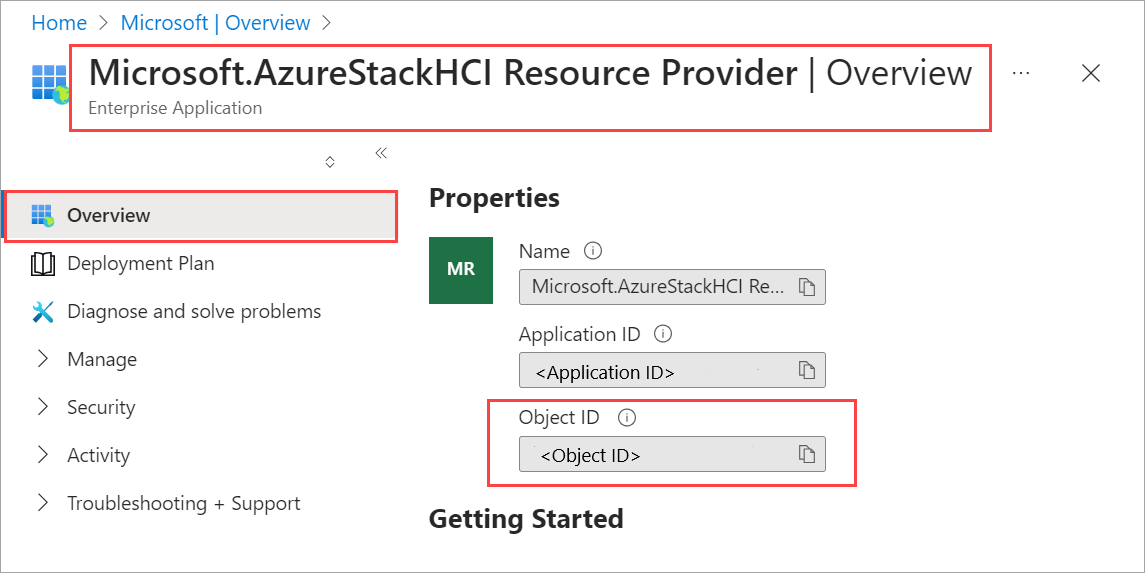
No portal do Azure, pesquise e acesse Microsoft Entra ID.
Vá para a guia Visão geral e pesquise Microsoft.AzureStackHCI Resource Provider.
Selecione o SPN listado e copie a ID do objeto.
Como alternativa, você pode usar o PowerShell para obter a ID do objeto da entidade de serviço do RP Local do Azure. Execute o seguinte comando no PowerShell:
Get-AzADServicePrincipal -DisplayName "Microsoft.AzureStackHCI Resource Provider"Use a ID do Objeto em relação ao
hciResourceProviderObjectIDparâmetro no modelo do Resource Manager.
Etapa 2: Implantar usando o modelo do Azure Resource Manager
Um modelo do Resource Manager cria e atribui todas as permissões de recursos necessárias para a implantação.
Com todas as etapas de pré-requisito e preparação concluídas, você está pronto para implantar usando um modelo de implantação do Resource Manager em boas condições e testado e o arquivo JSON de parâmetros correspondentes. Use os parâmetros contidos no arquivo JSON para preencher todos os valores, incluindo os valores gerados anteriormente.
Importante
Nesta versão, certifique-se de que todos os parâmetros contidos no valor JSON sejam preenchidos, incluindo aqueles que têm um valor nulo. Se houver valores nulos, eles precisarão ser preenchidos ou a validação falhará.
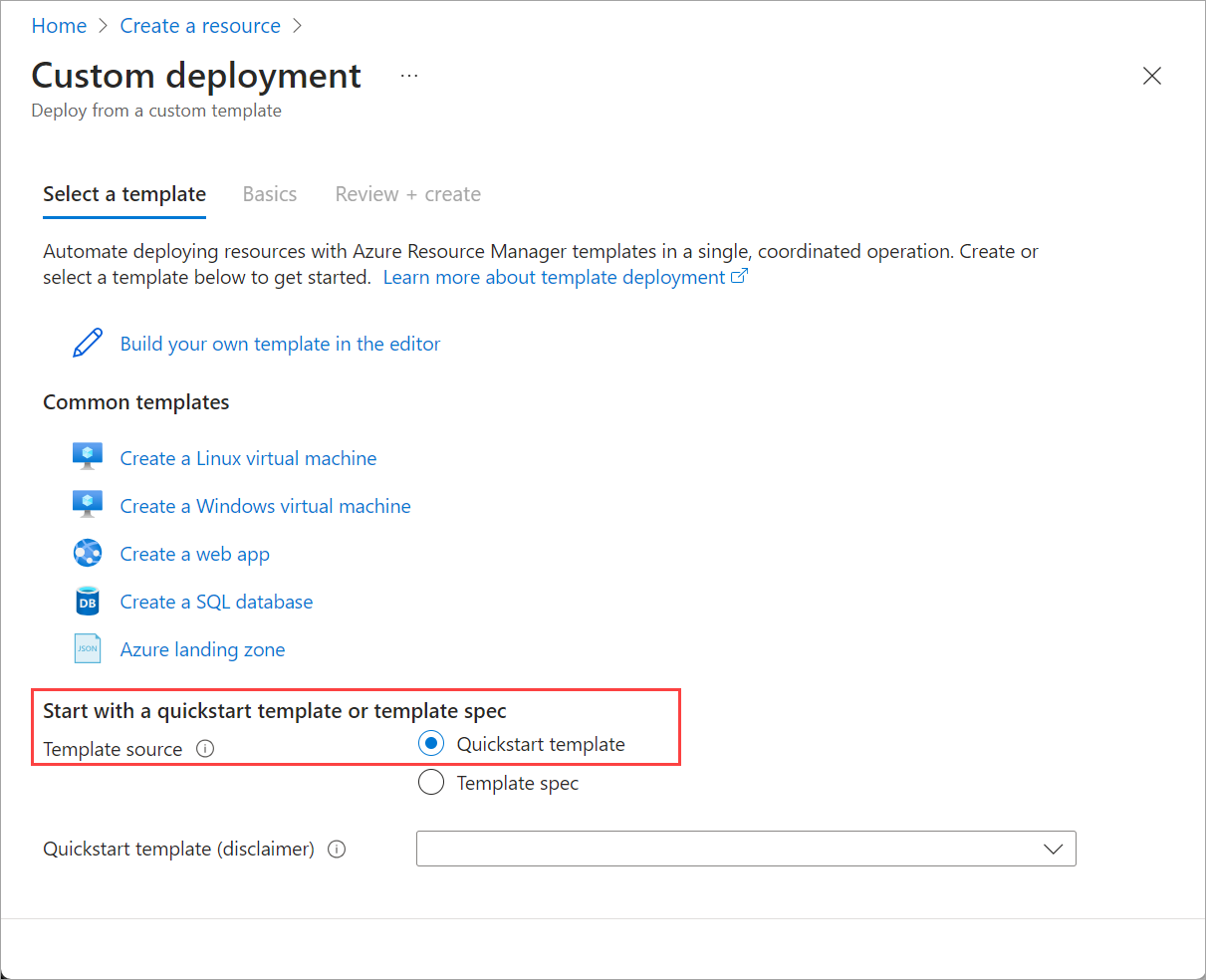
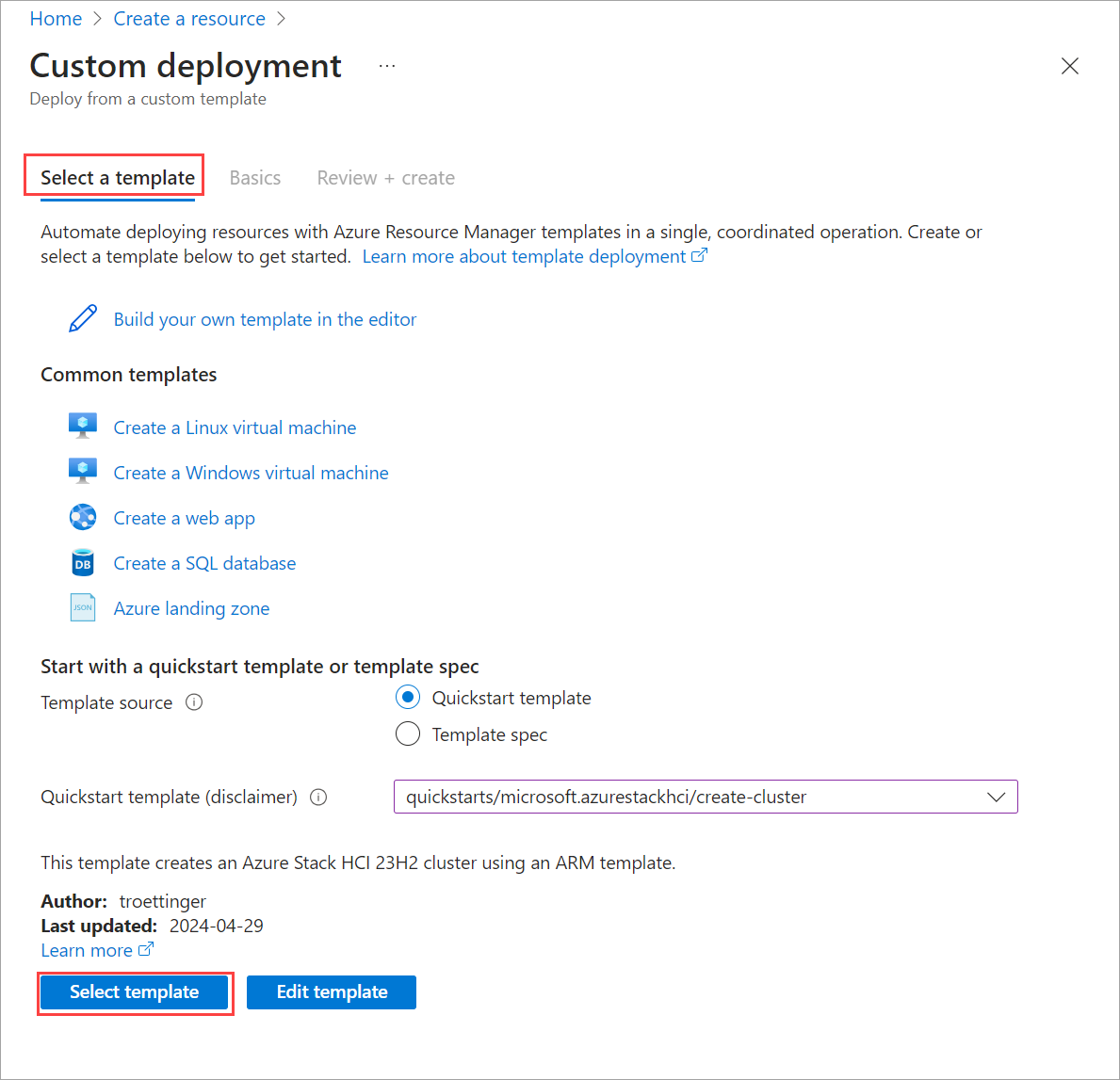
No portal do Azure, vá para Página Inicial e selecione + Criar um recurso.
Selecione Criar em Implantação de modelo (implantar usando modelos personalizados).
Perto da parte inferior da página, localize Iniciar com um modelo de início rápido ou seção de especificação de modelo. Selecione a opção de modelo de início rápido.
Use o campo Modelo de início rápido (aviso de isenção de responsabilidade) para filtrar o modelo apropriado. Digite azurestackhci/create-cluster para o filtro.
Quando terminar, selecione o modelo.
Na guia Noções básicas , você verá a página Implantação personalizada. Você pode selecionar os vários parâmetros por meio da lista suspensa ou selecionar Editar parâmetros.
Edite parâmetros como intenção de rede ou intenção de rede de armazenamento. Depois que todos os parâmetros estiverem preenchidos, salve o arquivo de parâmetros.
Selecione o grupo de recursos apropriado para seu ambiente.
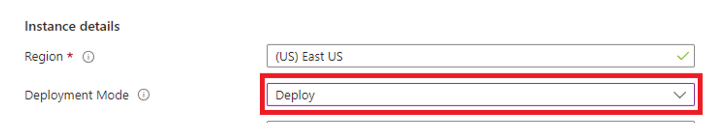
Role até a parte inferior e confirme se Modo de implantação = Validar.
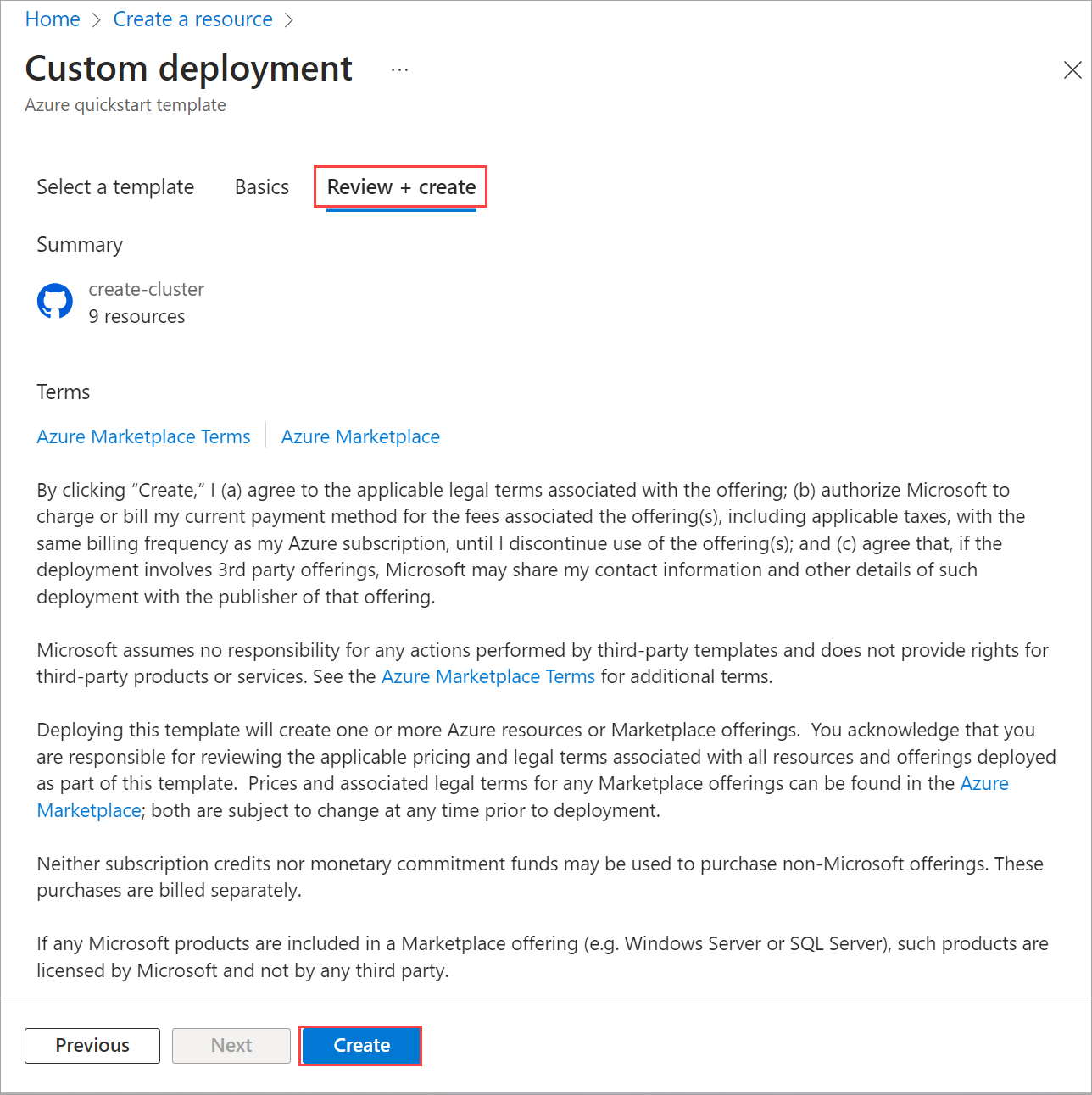
Selecione Examinar + criar.
Na guia Examinar + Criar, selecione Criar. Isso cria os recursos de pré-requisito restantes e valida a implantação. A validação leva cerca de 10 minutos para ser concluída.
Quando a validação for concluída, selecione Reimplantar.
Na tela Implantação personalizada, selecione Editar parâmetros. Carregue os parâmetros salvos anteriormente e selecione Salvar.
Na parte inferior do workspace, altere o valor final no JSON de Validate para Deploy, em que Deployment Mode = Deploy.
Verifique se todos os campos do modelo de implantação do Resource Manager estão preenchidos pelo JSON de Parâmetros.
Selecione o grupo de recursos apropriado para seu ambiente.
Role até a parte inferior e confirme se Modo de implantação = Implantar.
Selecione Examinar + criar.
Selecione Criar. A implantação é iniciada usando os recursos de pré-requisito existentes que foram criados durante a etapa Validar .
A tela Implantação alterna no recurso de cluster durante a implantação.
Depois que a implantação é iniciada, há uma execução limitada do Verificador de Ambiente, uma execução completa do Verificador de Ambiente e a implantação na nuvem é iniciada. Após alguns minutos, você pode monitorar a implantação no portal.
Em uma nova janela do navegador, navegue até o grupo de recursos do seu ambiente. Selecione o recurso de cluster.
Selecione Implantações.
Atualize e observe o progresso da implantação do primeiro computador (também conhecido como computador de propagação e é o primeiro computador em que você implantou o cluster). A implantação leva entre 2,5 e 3 horas. Várias etapas levam de 40 a 50 minutos ou mais.
A etapa da implantação que leva mais tempo é Implantar Moc e ARB Stack. Esta etapa leva de 40 a 45 minutos.
Depois de concluída, a tarefa na parte superior é atualizada com o status e a hora de término.
Você também pode conferir este modelo de origem da comunidade para Implantar uma instância do Azure Local, versão 23H2 usando o Bicep.
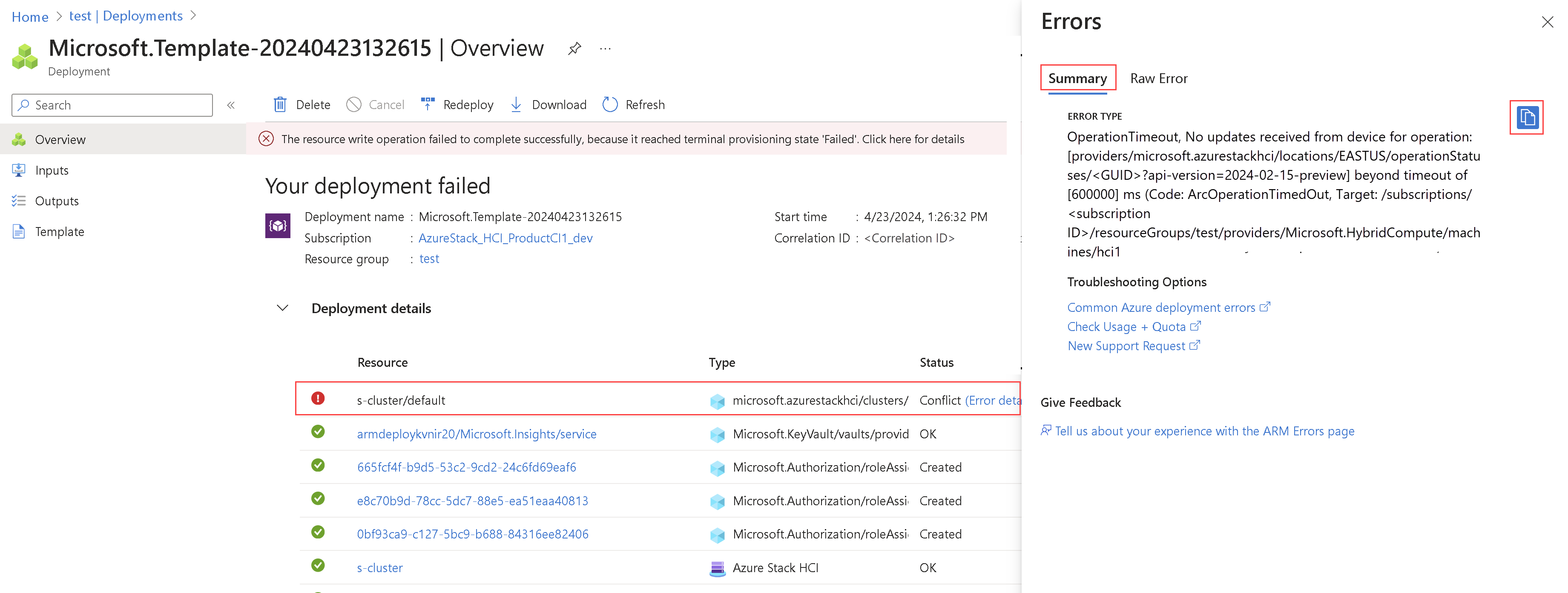
Solucionar problemas de implantação
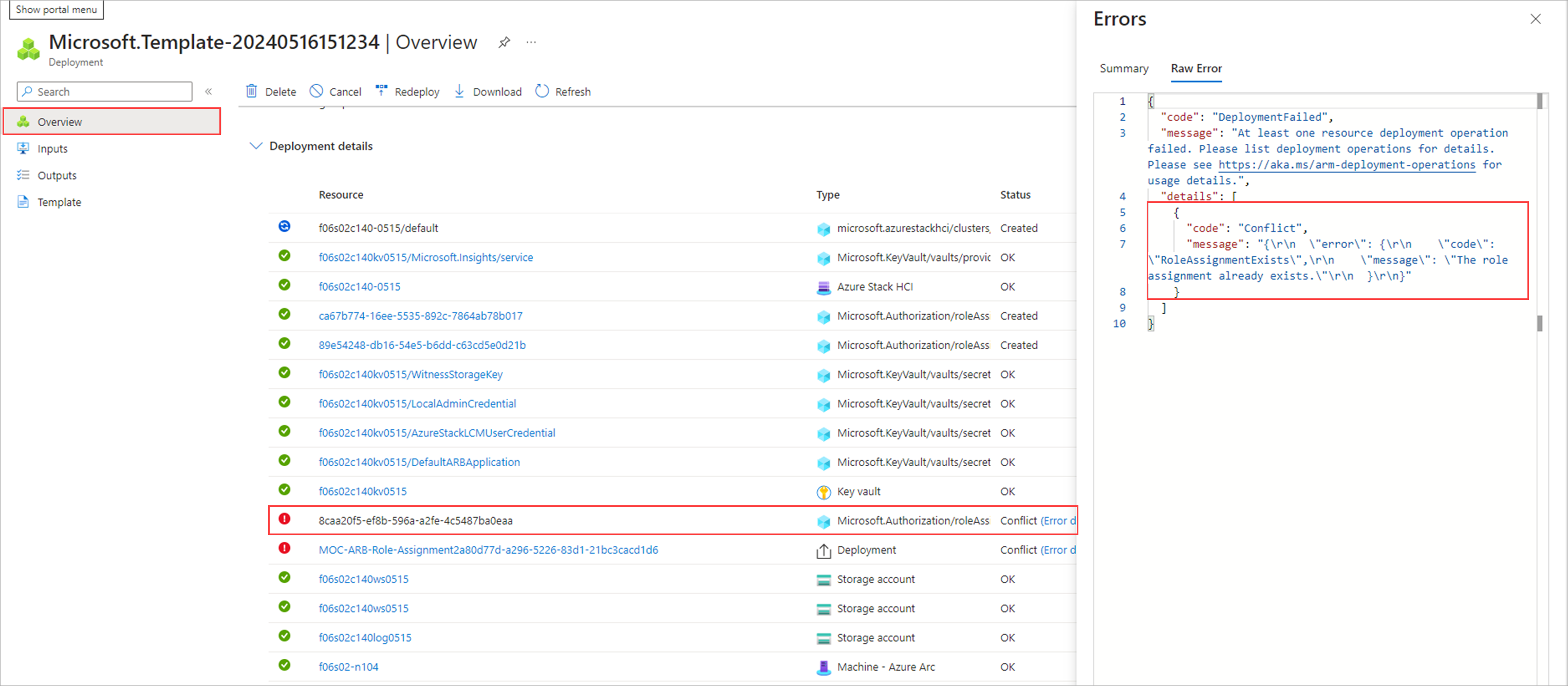
Se a implantação falhar, você verá uma mensagem de erro na página de implantações.
Nos detalhes da implantação, selecione os detalhes do erro.
Copie a mensagem de erro da folha Erros . Você pode fornecer essa mensagem de erro ao suporte da Microsoft para obter mais assistência.
Problemas conhecidos para implantação de modelo do ARM
Esta seção contém problemas conhecidos e soluções alternativas para a implantação do modelo do ARM.
A atribuição de função já existe
Problema: nesta versão, você pode ver o erro A atribuição de função já existe . Esse erro ocorrerá se a implantação da instância local do Azure tiver sido tentada no portal primeiro e o mesmo grupo de recursos tiver sido usado para a implantação do modelo do ARM. Você verá esse erro na página de detalhes>visão geral do recurso aplicável. Esse erro indica que uma atribuição de função equivalente já foi feita por outra identidade para o mesmo escopo de grupo de recursos e a implantação do modelo do ARM não pode executar a atribuição de função.
Solução alternativa: embora esses erros possam ser desconsiderados e a implantação possa continuar por meio do modelo do ARM, é altamente recomendável que você não troque os modos de implantação entre o portal e o modelo do ARM.
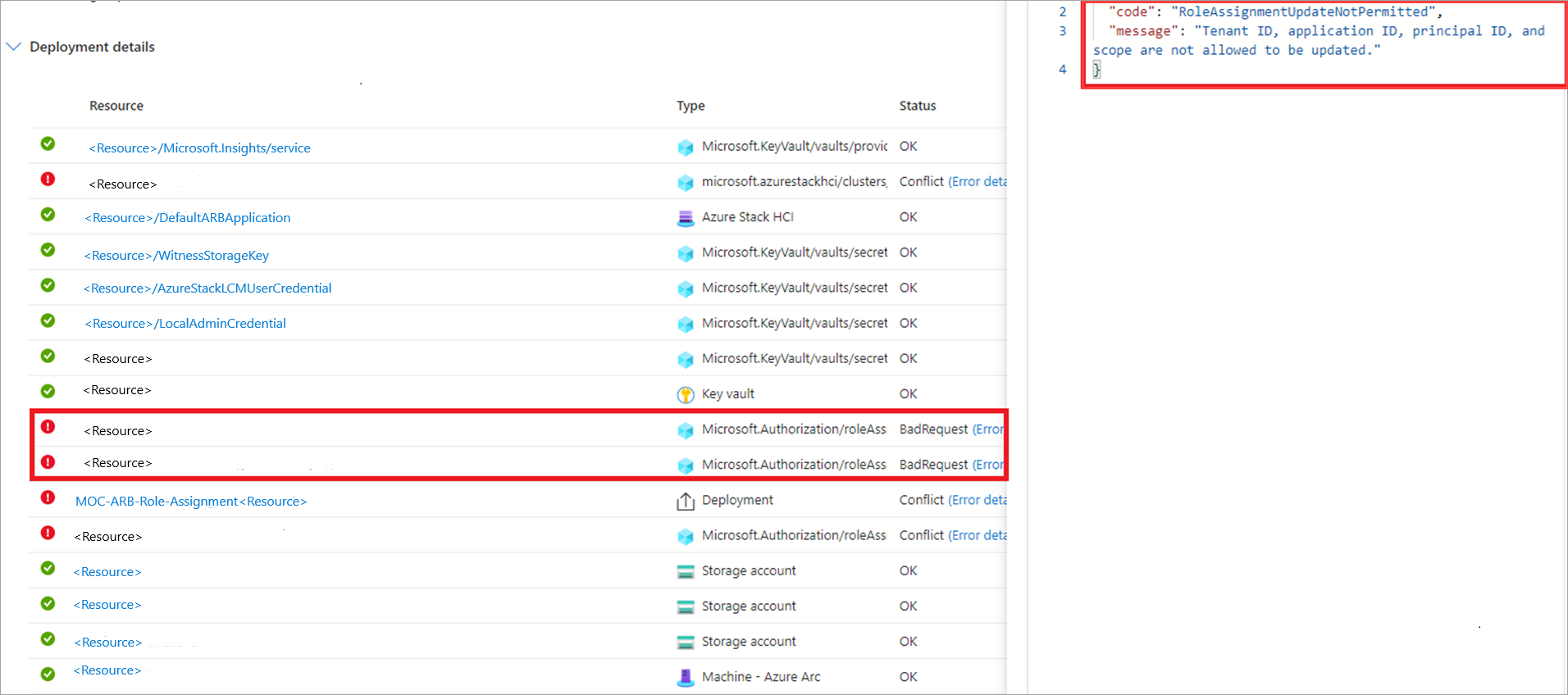
A ID do locatário, a ID do aplicativo, a ID da entidade de segurança e o escopo não podem ser atualizados
Problema: a atribuição de função falha com o erro ID do locatário, ID do aplicativo, ID da entidade de segurança e escopo não podem ser atualizados. Você verá esse erro na página de detalhes>visão geral do recurso aplicável. Esse erro pode aparecer quando há atribuições de função zumbi no mesmo grupo de recursos. Por exemplo, quando uma implantação anterior foi executada e os recursos correspondentes a essa implantação foram excluídos, mas os recursos de atribuição de função foram deixados por perto.
Solução alternativa: Para identificar as atribuições de função zumbi, acesse Controle de acesso (IAM) > Tipo de atribuições de > função: guia Desconhecido . Essas atribuições são listadas como *Identidade não encontrada. Incapaz de encontrar identidade. Exclua essas atribuições de função e repita a implantação do modelo do ARM.
Problema de sincronização de licença
Problema: nesta versão, você pode encontrar problemas de sincronização de licença ao usar a implantação do modelo do ARM.
Solução alternativa: depois que o sistema concluir o estágio de validação, recomendamos que você não inicie outra implantação de modelo do ARM no modo Validar se o sistema estiver no estado Falha na implantação. Iniciar outra implantação redefine as propriedades do sistema, o que pode resultar em problemas de sincronização de licença.