Active Directory Certificate Services (AD CS): Network Device Enrollment Service (NDES)
The Network Device Enrollment Service (NDES) is one of the role services of the Active Directory Certificate Services (AD CS) role. It implements the Simple Certificate Enrollment Protocol (SCEP). SCEP defines the communication between network devices and a Registration Authority (RA) for certificate enrollment and is defined in detail in https://tools.ietf.org/html/draft-nourse-scep-18
"The goal of SCEP is to support the secure issuance of certificates to network devices in a scalable manner, using existing technology whenever possible ."
 Warning Warning |
|---|
| SCEP was designed to be used in a closed network where all end-points are trusted. The warnings from CERT in the article " Simple Certificate Enrollment Protocol (SCEP) does not strongly authenticate certificate requests " should be considered when implementing the NDES service. If an application utilizes SCEP, it should provide its own strong authentication. |
This article was updated to cover the Windows Server 2012 release with the following exceptions:
- Some functionality was modified in the Windows Server 2008 R2 release, Windows Server 2008 Service Pack 2, and software updates for the Windows Server 2008. Whenever applicable, the document will explicitly state the differences between the different operating system versions.
- SCEP implementation is available in the Resource Kit for Windows 2000 Server and Windows Server 2003. It is also known as the Microsoft Simple Certificate Enrollment Protocol (MSCEP). Appendix 1 highlights the delta between the SCEP implementation in the Windows Server 2003 release and the Windows Server 2008 release.
Note
One major difference between Windows Server 2008 R2 and Windows Server 2012 is that starting with Windows Server 2012, the NDES role service is available in all Windows Server 2012 versions. See the AD CS Overview article for the table that shows the AD CS roles that are not available in some Windows Server 2008 R2 versions. The important point for this article is that Windows Server 2008 R2 Standard, Web Server, and Foundation editions do not support the NDES role service. Further, installations of Windows Server 2008 R2 using Server Core do not support NDES. Since Small Business Server (SBS) 2011 is based on Windows Server 2008 R2 standard, the NDES role service is not available on that platform either.
Prerequisites
This article is intended for those with a basic understanding of PKI concepts and x509 certificates.
Understanding the Network Device Enrollment Service
The need to secure networks has grown substantially over the last few years. One of the security challenges organizations face is authentication. There are few protocols that can be used for authentication-one of which, Internet Protocol Security (IPSec), uses X509 version 3 certificates as a means to identify the entities involved in a secure session. However, the challenge has moved from authentication to issuance certificate to these end entities. Moreover, our network includes devices that do not run with established credentials (domain known), for example, routers. SCEP enables network devices that do not run with domain credentials to enroll for x509 version 3 certificates from a Certification Authority (CA).
At the end of the transactions defined in this protocol, the network device will have a private key and associated certificate that is issued by a CA. Applications on the device may use the key and its associated certificate to interact with other entities on the network. The most common usage of this certificate on a network device is to authenticate the device in an IPSec session.
The Entities
The following entities are involved in SCEP.
- Device (client) This is the actual client for this protocol. It can be a router or any other device including software components such as a virtual private network (VPN) clients that do not run with domain credentials; hence, they cannot authenticate over the network.
- Device Administrator This entity is responsible for the administration of the device or client.
- Network Device Enrollment Service (Service) This is the service that corresponds to the server in the SCEP. This service might be referred to as the RA.
- CA server This is the server that runs Certificate Services. The CA issues client certificates.
- CA administrator This user has administrator rights on the CA server and can modify its policy settings.
- Domain Controller (DC) This is the server that runs Microsoft Active Directory Domain Services. It is used as a central repository for certificate templates to enforce certificate issuance policies across the domain.
Terminology Used in this Article
- Password challenge As defined in the SCEP, the password challenge is a sequence of bytes the service may supply to the device administrator and can later be used to authenticate the device.
- Password cache The service maintains a list of passwords it has supplied to the device administrators to enable device authentication. The service uses an in-memory cache for these passwords. Once a password has been used, it will be removed from the password cache.
- Administration site This is the Web site that should be used by a device administrator to obtain password challenges for device enrollment.
- Service certificates These are the two certificates the service will use during the device enrollment session. The encryption certificate will be used by the device to encrypt the password challenge it sends with the enrollment request. The signing certificate will be used by the service to send the device request to the CA.
- Configured CA The Network Device Enrollment Service has one CA that is used for sending certificate requests and retrieving CA information. This CA is configured during the service setup and cannot be modified later. It can be either an Enterprise CA or a Stand-alone CA.
- Configured Certificate Templates If the configured CA is an enterprise CA, the Network Device Enrollment Service will use the configured templates when sending an enrollment request to the CA. Three configured templates are defined in the registry. For more information, see Configuring the Network Device Enrollment Service.
The Enrollment Process
Figure 1 illustrates the various steps for enrolling certificates through the Network Device Enrollment Service.
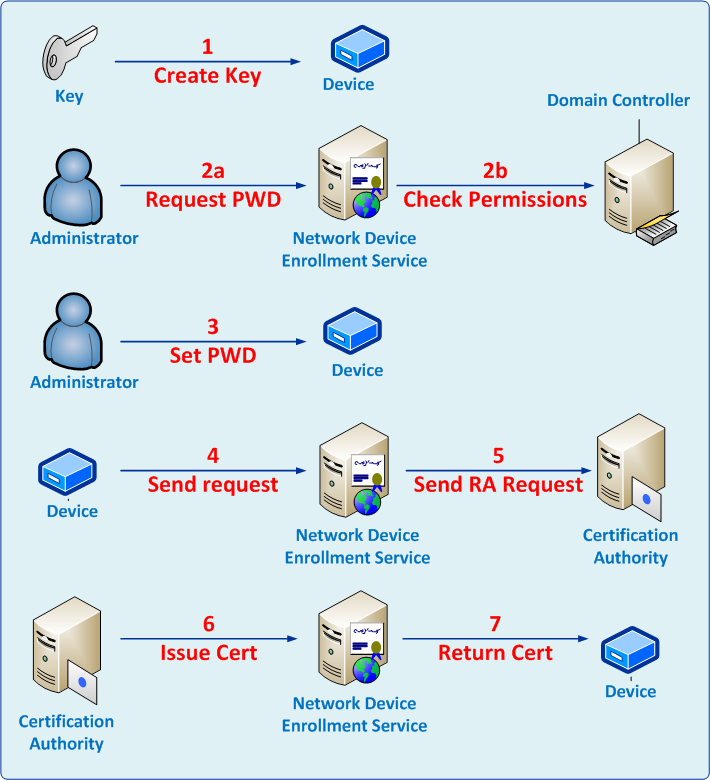
Figure 1: Enrollment Process
The enrollment process includes the following steps.
- The device generates an RSA public-private key pair on the device.
- The administrator obtains a password from the Network Device Enrollment Service.
- The administrator browses to the administration Web page.
- The service verifies that the administrator holds the required permissions for the configured certificate templates.
- The administrator sets the device with the password and sets it to trust the enterprise PKI.
- The administrator configures the device to send the enrollment request to the Network Device Enrollment Service.
- The Network Device Enrollment Service signs the enrollment request with its Enrollment Agent certificate and sends it to the CA.
- The CA issues the certificate and returns to the service.
- The device retrieves the issued certificate from the service.
Step 1: Generates a public-private key pair
In this step, the device must create a private and public key pair. The device must define the cryptography actions enabled for this key from the following list.
- Signing and signature verifications, OR
- Decryption and encryption, OR
- Both
At the end of the step, the device must have a public-private key pair for cryptography operations.
Step 2: Obtains a password from the Network Device Enrollment Service
In this step, the device administrator obtains a password from the Network Device Enrollment Service at https://<ServerName>/certsrv/mscep_admin (Figure 2).
 Notes Notes |
|---|
|
The service gets the requestor credentials and verifies that it possesses the following permissions.
- If the Service-configured CA is an Enterprise CA, the requestor must have Enroll permission for all three configured certificate templates. These templates are set through the EncryptionTemplate, SignatureTemplate, and GeneralPurposeTemplate registry keys. For more information about configuring templates, see Configuring Templates for Device Enrollment.
- If the Service-configured CA is a Stand-alone CA, the requestor must be a member of the CA Administrators group.
Next, the service will check that the password table is not full. If it is not full, the service will create a random password and embed it in the HTML page returned to the caller. For more information about the service password table, see Password and Password Cache.
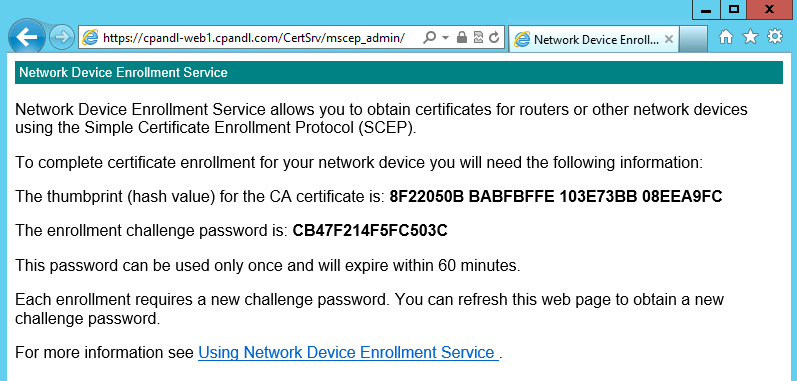
Figure 2: Administration Web Page
Step 3: Sets the device to trust the Enterprise PKI
This step is specific for each device. By the end of this step, the device should be configured to trust the enterprise PKI. It is usually achieved when the device is invoking the GetCACert operation implemented by the service, and trusting the returned CA certificate. The following is an example of a call to get the CA certificate.
https://myregistrationauthority/certsrv/mscep?operation=GetCACert&message=MyDeviceID
Step 4: Submits a certificate enrollment request to the service
In this step, the device administrator performs the required steps to submit a request from the device to the service. If the service requires a password, the administrator needs to configure the device with the password that was received from the service in Step 2.
This step is device-specific. Once it is completed, the service must receive a PKCS #7 request containing the required information for the device enrollment. The KeyUsage extension of the enrollment request should be one of the following:
- Key Encipherment (0x20)
- Digital Signature (0x80)
- Both (0xa0)
Note
The KeyUsage extension value usually defaults to 0xa0 for most devices.
If the request does not contain a KeyUsage extension, the service will treat the request as it was sent for both cryptographic operations (0xa0).
The request syntax is specified in
https://tools.ietf.org/html/draft-nourse-scep-18
Step 5: Sends an enrollment request to the CA
After receiving the enrollment request from the device, the service does the following:
- It verifies that the enrollment request contains a valid password.
- If it is configured to use an Enterprise CA, the service looks for the template to use when sending a certificate request to that CA. The template will be based on the KeyUsage extension.
- 0x80: Uses the template name identified in the "SignatureTemplate" registry key
- 0x20: Uses the template name identified in the "EncryptionTemplate" registry key.
- 0xa0: Uses the template name identified in the "GeneralPurposeTemplate" registry key.
Note
If the registry key is not set, the service will default to the "IPSec (Offline Request)" certificate template.
- It constructs the certificate request based on the request received from the device and the certificate template identified in the previous bullet. (Certificate templates apply to enterprise CAs only.)
- It signs the request using the service enrollment agent signing certificate.
- It sends the request to the CA by calling ICertRequest:: Submit.
Step 6a: CA issues the device certificate immediately
If the CA issues the certificate immediately, the service will get the certificate and return it to the device.
Note
For an enterprise CA, the issuance policies for a certificate request are based on the certificate template the certificate is constructed with. In the default installation and configuration, the service will send a certificate request based on the "IPSec (Offline Request)" template. The administrator can change the template by configuring the registry key as specified in Configuring Templates for Device Enrollment.
For a stand-alone CA, the default issuance policy is to hold all certificate requests for approval by a CA manager.
Step 6b: Asynchronous issuance
If the certificate request is not issued immediately, the service will return the status to the device.
The device administrator will have to send another request to receive status for the pending certificate request. The service will receive the updated status from the CA; if the certificate has already been issued, it will return the issued certificate to the device.
Certificate Renewal
The NDES supports certificate renewal where a device uses a previously issued certificate to validate the new certificate request. This feature is supported on Windows Server 2012, Windows Server 2008 R2, Windows Server 2008 Service Pack 2, or on Windows Server 2008 with the KB959193 hotfix installed ( https://support.microsoft.com/kb/959193 ).
 Warning Warning |
|---|
| The certificate Subject information must remain the same in order for renewal to succeed. If you modify the certificate subject information after certificates are issued, you will be unable to renew them. |
The certificate subject name is configured in the following registry key:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\CertSvc\Configuration\CA Name>
Multi String value=SubjectTemplate
Deploying the Network Device Enrollment Service
The Network Device Enrollment Service does not require a complex deployment plan. It can be installed on any machine that runs Internet Information Services (IIS) as long as it can communicate with the CA through the Distributed Component Object Model (DCOM).
Note that the screenshots provided in this section are based on the user interface as it implemented in Windows Server 2008 R2. The difference in user interface between Windows Server 2008 and Windows Server 2008 R2 is not significant so it should be easy for the reader to follow instructions in Windows Server 2008 as well.
Deployments Scenarios
There are two deployment scenarios for the Network Device Enrollment Service.
- Enterprise scenario
- Stand-alone scenario
Enterprise Scenario Deployment
In an enterprise scenario deployment, the service will use an existing Enterprise CA.
Since the CA computer has access to the CA key, it is recommended to reduce the attack surface of the computer hosting the CA by not enabling additional services. Therefore, the recommended setting is to install the Network Device Enrollment Service on a different computer than the one hosting the CA service. Figure 3 illustrates a network diagram of this deployment model.
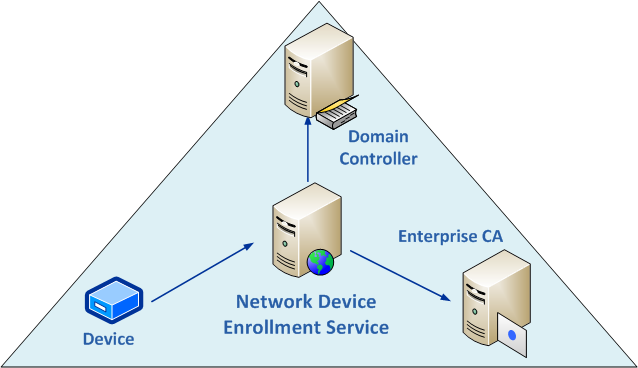
Figure 3: Enterprise Scenario Deployment
In this deployment scenario, all permissions will be based on permissions set on certificate templates published in DC. In addition, the certificate requests sent to the CA will be based on certificate templates.
Stand-Alone Scenario Deployment
In this deployment scenario, the service will not use an existing Enterprise CA. Instead, it will use a stand-alone CA. It is recommended that the stand-alone CA will be deployed on the same computer as the Network Device Enrollment Service and will be used to issue device certificates only.
Figure 4 illustrates a network diagram of this deployment model.
** **
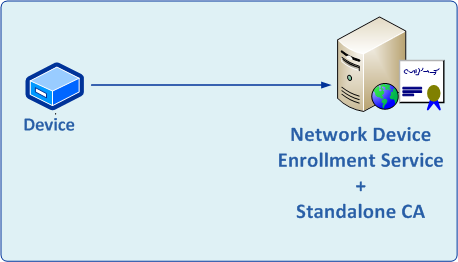
Figure 4 : Stand-alone Scenario Deployment
Permissions Required for the Network Device Enrollment Service
There are three roles related to setting up and running the service.
- Service Administrator The user who must be logged on to the service machine when installing the Network Device Enrollment Service. In this article, this user is referred to as SCEPAdmin.
- Service Account The credentials that will be used to run the service. This user is referred to as SCEPSvc
- Device Administrator The user who manages the devices and should request a one-time password from the service to enable security enrollment. This user is referred to as DeviceAdmin.
The following are the required permissions for each of the entities.
SCEPAdmin
- Must be part of the local administrators' group.
- Must be logged on locally when the installation of the Network Device Enrollment Service role is triggered.
- For setting up the service with an Enterprise CA, this user should have the following permissions as well.
-
- Must have Enroll permission on the "Exchange Enrollment Agent (Offline request)" and "CEP Encryption" templates.
- Must have permissions to add templates to the selected CA.
- Must be a member of the Enterprise Admins group (this is just required for installation and not for ongoing administration).
SCEPSvc
- Must be a member of the local IIS Server's IIS_IUSRS group (this is an installer prerequisite).
- Must have Request permission on the configured CA.
- Must be a domain user account and have Read and Enroll permissions on the configured templates. For more information about the configured template, see Configuring Templates for Device Enrollment.
- May require an SPN to be set in Active Directory.
- If using a single NDES server and its actual hostname (a most common scenario), the account does not need an SPN registered.
- The computer account's default SPNs for HOST/computerfqdn cover this case.
- If using all other defaults (particularly around IIS kernel-mode authentication)
- Skip to the next section.
- If using a custom A record as a hostname, or load balancing with a Virtual IP, an SPN needs to be registered against the NDES service account (SCEPSvc)
- To do so, use the Setspn command syntax of: Setspn -s HTTP/computerfqdn domainname**\**accountname. For example, given the following:
- Domain: Fabrikam.com
- NDES VIP name (or single-computer host record): NDESFARM
- NDES service account name: SCEPSvc
- Commands to enter:
- Setspn -s HTTP/NDESFARM.fabrikam.com fabrikam\SCEPSvc
- Setspn -s HTTP/NDESFARM fabrikam\SCEPSvc
- Then disable IIS Kernel-mode Authentication for the site.
- If using a single NDES server and its actual hostname (a most common scenario), the account does not need an SPN registered.
DeviceAdmin :
- If the service is configured with an Enterprise CA, the user must have Enroll permissions on all templates configured in the registry.
- If the service is configured with a Stand-alone CA, the user must be a member of the CA administrators group.
Setup
Installing and configuring the Network Device Enrollment Service are done through the Add Roles Wizard. This wizard collects the required information for installing Windows Server Roles.
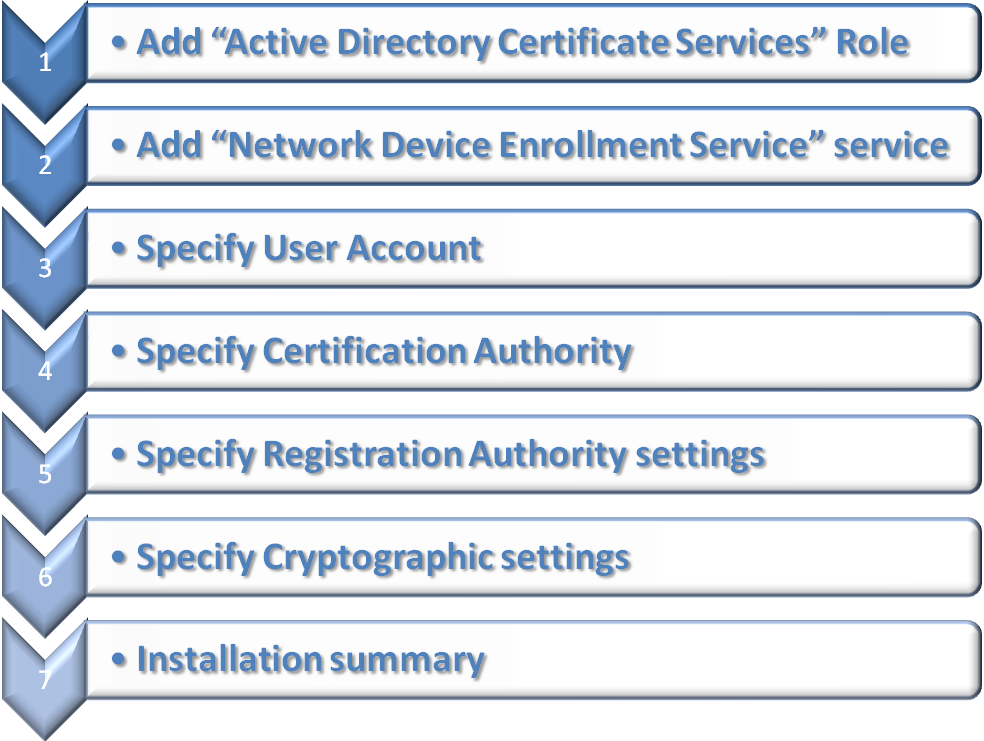
Figure 5 illustrates a summary of the steps for setting up the Network Device Enrollment Service.
Figure 5: Setup Steps Summary
The following sections provide the wizard steps for setting up the service.
Before you set up the service, you will need to
- Identify the CA that the service will work with.
- Make sure that you are logged on as the SCEPAdmin user. If you are logged on as the SCEPSvc user, you will be prompted to enter credentials for the SCEPAdmin user, but installation will fail with an "Access Denied" error.
- Ensure that you created a user account for the service credentials and provided the permissions specified in the previous section for the SCEPSvc user.
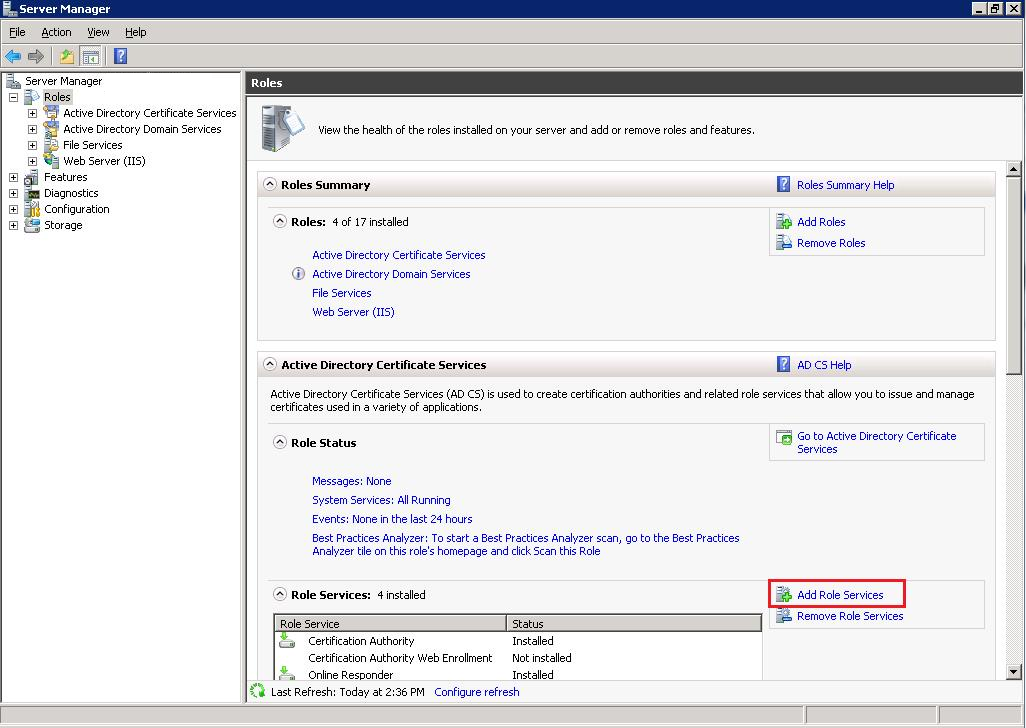
Step 1: Add the Active Directory Certificate Services Role
There are two scenarios for installing the Network Device Enrollment Service.
ADCS role is installed. You already have one of the ADCS services installed on the server, for example, a CA is already installed.
Launch the Server Manager Microsoft Management Console (MMC), click Manage Roles in the left panel, and then click Add role services in the Active Directory Certificate Services section (red rectangle in Figure 6). Go to Step 2: Add the Network Device Enrollment Service role service
Figure 6: Server Manager
ADCS role is not installed.
Launch the Server Manager MMC, and then click Add Roles. The Add Roles Wizard will appear. On the Select Server Role page, select the Active Directory Certificate Services" role, then and click Next. The default service selected is the Certification Authority, clear the check box, and then go to Step 2: Add the Network Device Enrollment Service role service.
Note
If you would like to set up the service and its CA is on the same computer, you must set up the CA first; after installation is completed, run the setup wizard again and add the Network Device Enrollment Service.
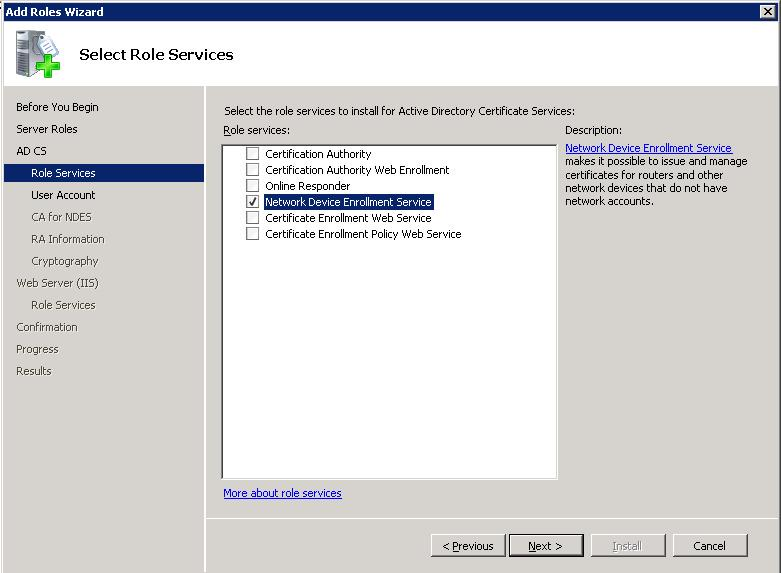
Step 2: Add the Network Device Enrollment Service role service
In the Add Roles Wizard (Figure 7 ), on the Select Role Services page, select the Network Device Enrollment Service check box. The wizard will detect whether all the required dependencies are installed. If any dependencies are missing, you will be prompted with a dialog box explaining what is missing and requesting your permission to install the dependencies. Click Yes to continue the installation.
Figure 7: Setup - Select Role Services
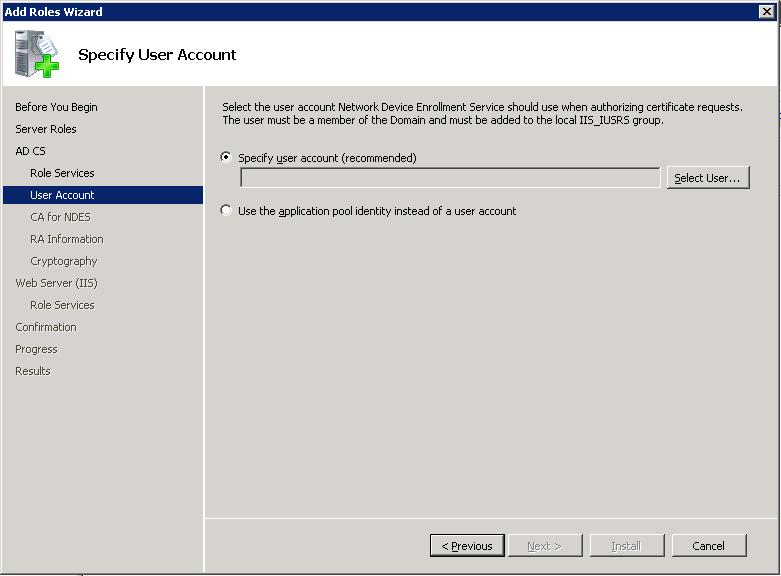
Step 3: Specify User Account
In the Add Roles Wizard (Figure 8), on the Specify User Account page, set the credentials for the Network Device Enrollment Service. If you are using a local CA for this service, you cannot select the Network Service Account option. If you are using a remote CA, it is highly recommended that you create a dedicated account for this service. Setting the service to run as a network service may have security implications.
Note that in Windows Server 2008 R2, the network service option has been replaced with application pool identity (UI is not shown here). The application pool identity is a more secure option than network service as it doesn't possess impersonate privilege and is not shared with other services on the machine.
Figure 8 : Setup - Specify User Account
The selected account should have the permissions specified for the SCEPSvc in the PERMISSIONS REQUIRED FOR THE NETWORK DEVICE ENROLLMENT SERVICE section.
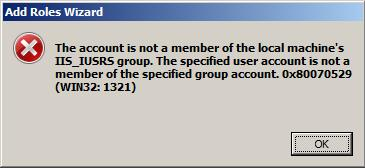
If the user is not a member of the local IIS_IUSRS account, the following error will appear (Figure 9).
Figure 9: Setup - Permissions Error
Open another instance of Server Manager and add the selected account to the IIS_IUSRS group before proceeding.
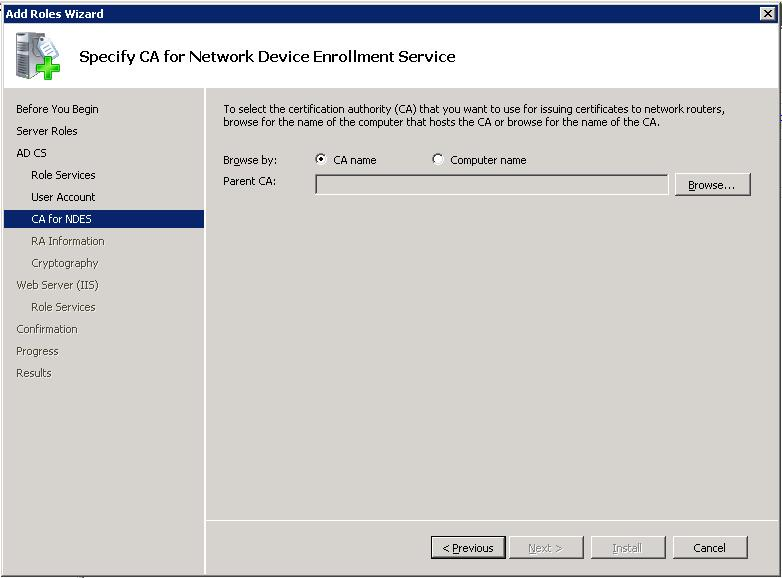
Step 4: Specify the Certification Authority
The service needs to be configured with a CA. This CA will be used for two purposes.
- Enrolling for the service certificates-one certificate for encryption and one certificate for signing.
- Enrolling for the device certificates.
This step will set up the CA (Figure 10). You can browse to the CA by looking for the CA's name stored on the domain controller (upper browse button) or by typing the machine name (lower browse button). The CA must be online during the service setup. Some devices have restrictions on your enterprise PKI, for example, not supporting special characters in the CA name. Check your manufacturer's specification restrictions.
Note
If a CA is running on the same machine, setup will not show Figure 10 and will use the local CA for this service.
Figure 10 : Setup - Specify CA
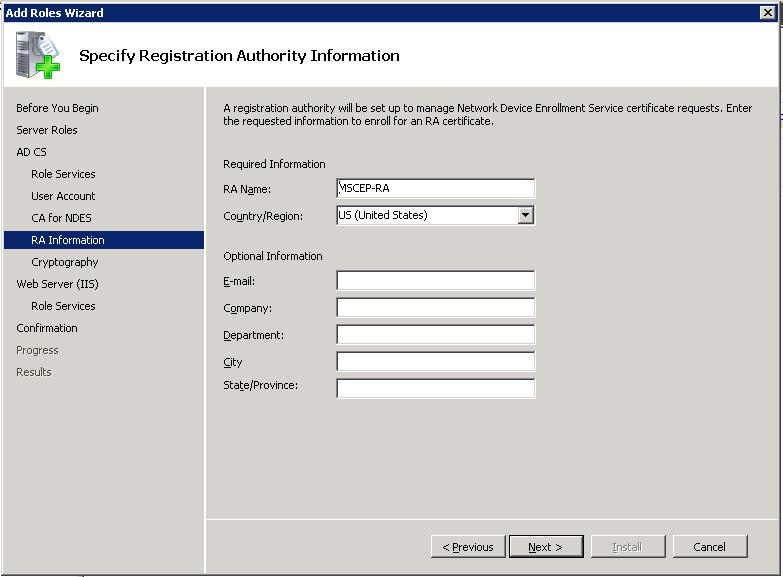
Step 5: Specify Service Information
On the Specify Registration Authority Information page (Figure 11), all the required and optional fields for setting up the service as the RA are collected. The information you provide here will be used to construct the signing certificate issued to the service.
Figure 11 : Setup - Specify Registration Authority Information
Step 6: Specify Cryptographic Settings
The Network Device Enrollment Service uses two certificates and their keys to enable device enrollment. Organizations might want to use different Cryptographic Service Providers (CSPs) to store these keys, or they may want to change the length of the keys used by the service.
The Configure Cryptography for Registration Authority (Figure 12) page enables you to change these key properties.
If you do not have a specific requirement to change the settings, it is recommended to keep the default settings.
Note
Only Cryptographic Application Programming Interface (CryptoAPI) Service Providers are supported for the RA keys; Cryptography API: Next Generation (CNG) providers are not supported.
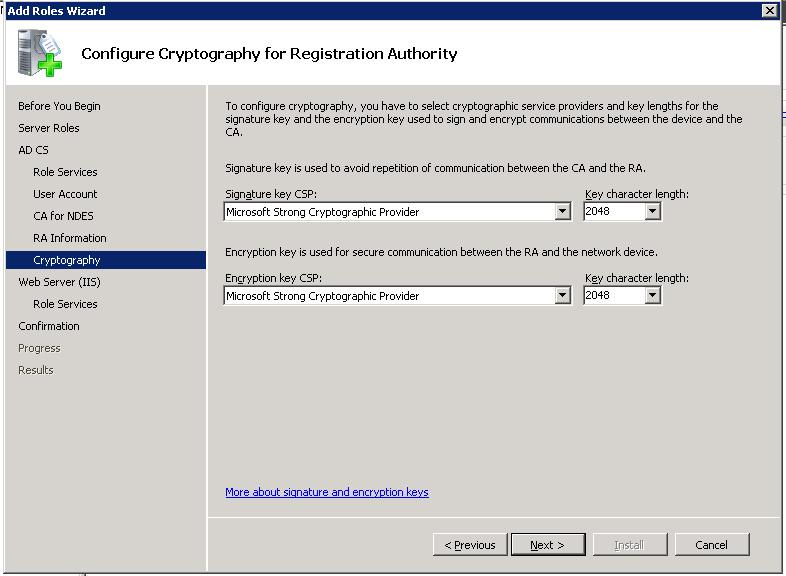
Figure 12: Setup - Configure Cryptography
Step 7: Installation Summary
On the Confirm Installation Selections page (Figure 12, review all the settings for the service and then click Install.
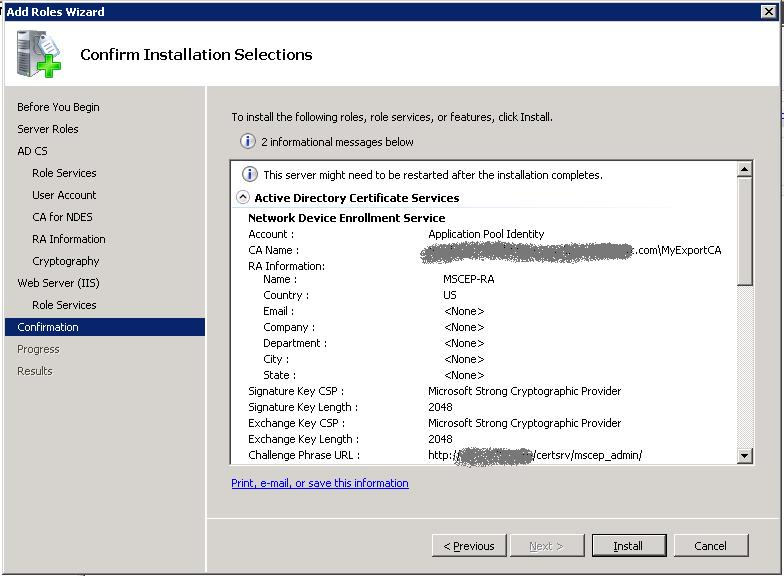
Figure 13: Setup - Confirmation Page
Upgrade
Windows Server 2008 is the first Windows release that includes a service which implements SCEP natively. The service is available only on Enterprise and Datacenter SKUs; it is not available on other Windows Server 2008 SKUs.
Since a previous implementation of the protocol was distributed previously with the Windows Server Resource Kit - MSCEP, there are some unique upgrade scenarios.
- Upgrade to Enterprise or DataCenter SKU
- Upgrade from: Any SKU
- Upgrade to: Windows Server 2008, Advanced or Datacenter SKUs
- Windows upgrade code will detect the presence of MSCEP and replace it with the Network Device Enrollment Protocol.
Note
MSCEP used a dedicated certificate store to hold its certificate-CEP. New installations of the Network Device Enrollment Service will store certificates in the default machine store. However, after upgrading from MSCEP to the Network Device Enrollment Service, the CEP store will still be the location for the certificates. This can be changed by changing the CertInMyStore registry key. For more information, see Configuring the Network Device Enrollment Service.
- Upgrade to Standard or WebServer SKUs
- Upgrade from: Any SKU
- Upgrade to: Windows Server 2008, not Advanced or Datacenter SKUs
- Since the Network Device Enrollment Service is disabled in Windows Server 2008 SKUs, Windows upgrade code will ignore the presence of MSCEP.
Note
Previous MSCEP implementations (that were released with the Windows Server Resource Kit) are not supported on any Windows Server 2008 SKU.
Understanding Network Device Enrollment Service Components
The Implementation
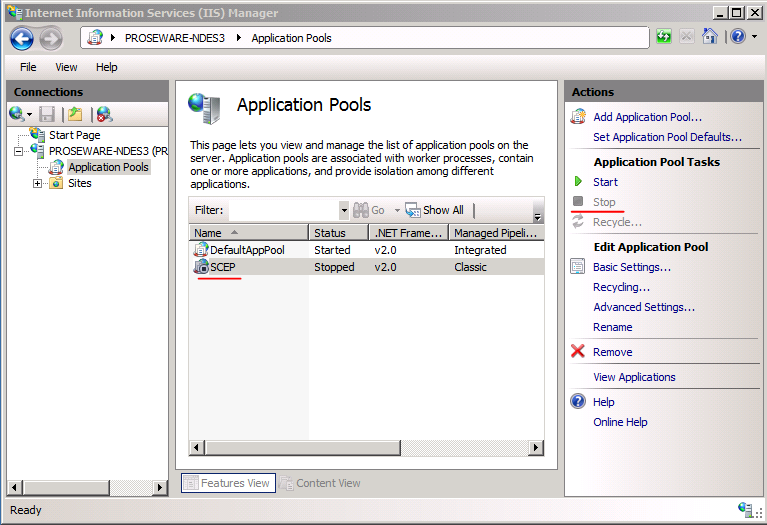
The service is implemented as an ISAPI extension. It requires IIS to be installed on the same computer. It does not require the CA to be installed on the same computer.
The Internet Server API (ISAPI) extension runs in its own application pool: SCEP. This application pool is created during setup and is configured to run with the credentials that were provided during setup.
Virtual Applications
The SCEP specification does not require devices to support Secure Socket Layer (SSL). However, the process of retrieving a one-time password from the service should be protected using SSL. Therefore, setup will create two virtual applications - one for the device and one for the administrator.
- https://localhost/certsrv/mscep Devices use this location for all communication.
- https://localhost/certsrv/mscep_admin Administrators use this location to retrieve enrollment passwords.
Note
Windows Setup cannot enable SSL on the administration virtual application since enabling SSL requires a certificate and a key that might not exist. It is highly recommended to enable SSL on the administration virtual application. Not setting SSL allows an un-authenticated user to hijack the password as it is returned to the administrator.
Password and Password Cache
Passwords are used by the service to authenticate the device before forwarding its enrollment request to the CA. This password should be obtained through a call to the administration virtual application https://localhost/certsrv/mscep_admin.
Every password can be used for the following:
- One certificate request that contains 0xa0 value in the KeyUsage extension (both encryption and signature).
- Two certificate requests, one for 0x20 value in the KeyUsage extension (encryption) and the other for 0x80 value in the KeyUsage extension (signature).
Password restrictions
- Passwords are valid for 60 minutes. This configuration can be changed by modifying the PasswordValidity registry key.
- The password cache can contain five passwords. This configuration can be changed by modifying the PasswordMax registry key.
- Password length is set to eight Unicode bytes. This configuration can be changed by modifying the PasswordLength registry key.
Reusing a password for multiple devices
In some environments, such as manufacturing, it may be desirable to reuse the same challenge for more than one device.
Warning: Although you can configure NDES to use a single password (UseSinglePassword mode), it should only be used in tightly controlled network environments where all devices requesting certificates as well as the people/software in possession of that password can be trusted. When NDES is configured to use a single password, any device on the network can be used to request a password using the same password. In contrast, when you are deploying certificates to mobile devices, we do not recommend using a single password as any one of your employees or their devices may leak the password. For additional information, see Can I use a single password or passphrase for device enrollment?
To enable this feature, follow these steps:
- Configure service to function in a single-password mode by creating a REG_DWORD value UseSinglePassword and setting it to 0x1.
- Give Full Control permission to the account used to run NDES for the HKEY_LOCAL_MACHINE\Microsoft\Cryptography\MSCEP registry key. This step only required if you have installed KB959193 hotfix.
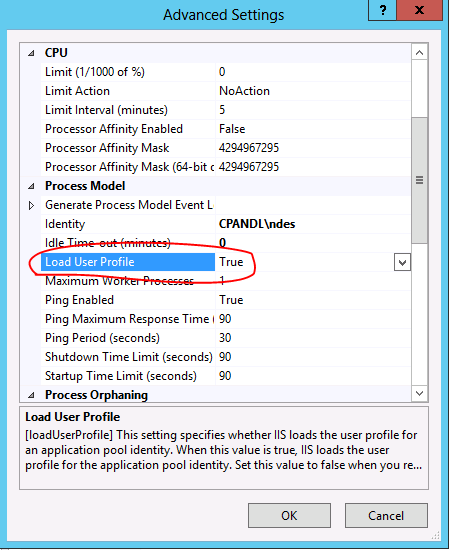
- In the IIS Manager snap-in, navigate to the SCEP application pool and in Advanced Settings set Load User Profile to true.
- If you've configured NDES to run under some user account, logon interactively with that user account onto the machine where NDES is installed to force the creation of a user profile for that account. This is a one-time operation, the user doesn't need to stay interactively logged on while NDES is running. To prepare the NDES service account profile:
- On the NDES server, open Internet Information Services (IIS) Manager.
- In the Connections pane, expand the Web server running the NDES service.
- In the Connections pane, click Application Pools.
- In the Application Pools pane, click SCEP.
- In the Actions pane, click Advanced Settings.
- In the Advanced Settings dialog box, under Process Model, configure Load User Profile to True. Click OK.
- In Application Pools, right-click SCEP and then click Stop.
- Sign off the NDES server.
- Sign on using the NDES user account. The NDES service account user profile is created.
- Sign off the NDES server.
- Sign on the NDES server using an account that is a member of local Administrators.
- Open Internet Information Services (IIS) Manager, expand the Web server object, and then select Application Pools.
- In the Application Pools pane, right-click SCEP and then click Start.
After the above steps are complete, the NDES will use only one password for all certificate requests. This password can be obtained in the same way as a one-time password by going to the admin page of the NDES. Administrators can deploy that password to their devices in an automated way.
Note that this functionality is supported on Windows Server 2008 R2, Windows Server 2008 Service Pack 2, or on Windows Server 2008 with the KB959193 hotfix installed ( https://support.microsoft.com/kb/959193 ).
Service Certificates
The service uses two certificates for two different scenarios.
- Enrollment agent certificate This certificate will be used to send the enrollment request to the CA.
- Key Exchange certificate This certificate will be used by the device to encrypt all the communication with the service (essential for transmitting the password).
Service Setup
During setup, the service enrolls for the two service certificates based on two preconfigured certificate templates.
- Exchange Enrollment Agent (Offline request) This certificate template is used for enrolling for the enrollment agent certificate.
- CEP Encryption This certificate template is used for enrolling for the key exchange certificate.
Note These certificate templates are hard-coded to the Network Device Enrollment Service setup and cannot be modified.
In addition, setup will set the required permissions on the Certificate Template object and the CA that the service is configured with, for example, adding the required Certificate Templates to the list of templates supported by the CA.
For more information about Windows PKI Certificate Template, see https://technet2.microsoft.com/WindowsServer/en/library/c25f57b0-5459-4c17-bb3f-2f657bd23f781033.mspx?mfr=true
Service Startup
When the service starts, it searches for two certificates that can be used for the previous two scenarios. These certificates do not have to be the same certificate the service enrolled for during setup. The following logic is used by the service for finding the certificate for the two scenarios at startup.
- The service searches in the machine MY store AND
- The certificate must have the following extensions AND
- For the Key Exchange certificate:
- ExtendedKeyUsage: "Certificate Request Agent"
- KeyUsage: Encryption (0x20)
- For the enrollment agent certificate:
- ExtendedKeyUsage: "Certificate Request Agent"
- KeyUsage: Signature (0x80)
- For the Key Exchange certificate:
- The certificate must not be archived AND
- The computer must have the private key for the certificate AND
- The certificate must be issued by the same CA that the service is configured for AND
- The certificate must have a valid chain AND
- If there is more than one certificate for either of the certificates that meet the previous criteria, the service will select the most recent one (the latest that was issued)
CA Configuration
The Network Device Enrollment Service is configured during its setup to use a CA. It supports a Microsoft CA running on any of the following operating system (OS) versions.
- Windows 2000 Server
- Windows Server 2003: Standard SKU, Advanced SKU, Datacenter SKU
- Windows Server 2008 Standard SKU, Advanced SKU, Datacenter SKU
- Windows Server 2008 R2 Standard SKU, Advanced SKU, Datacenter SKU
Once the CA is selected, the service will call the CA and retrieve its type-Enterprise or Stand-alone CA.
Configuring IIS
Two virtual applications are created for the service during setup.
- A virtual application for requesting passwords.
- A virtual application for sending the certificate request.
The first virtual application will authenticate the caller and verify that the caller has the required permissions to obtain a new password. If the validation succeeds, the service will generate a password and return it in clear text.
Since the password should be secured, it is highly recommended that SSL be enabled only on this virtual application.
Configuring the Network Device Enrollment Service
The service uses the registry to store configuration settings. All settings are stored under one Registry key.
HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP
If the key is not present, the service will use the hard-coded default value from the following table.
This table defines the registry keys and their associated values.
| Key\Value Value | Type | Default | Usage |
| EnforcePassword\EnforcePassword | DWORD | 1 | 1 = MSCEP requires a password for enrollment requests.
0 = Passwords are not enforced. |
| SignatureTemplate | String | IPSECIntermediateOffline | If this key is set, the service will use the value as the certificate template name when the device sends an enrollment request with 0x80 value for the KeyUsage extension. If it is not set, the service will use the IPSECIntermediate
Offline template. |
| EncryptionTemplate | String | IPSECIntermediateOffline | If this key is set, the service will use the value as the certificate template name when the device sends an enrollment request with 0x20 value for the KeyUsage extension. If it is not set, the service will use the IPSECIntermediate
Offline template. |
| GeneralPurposeTemplate | String | IPSECIntermediateOffline | If this key is set, the service will use the value as the certificate template name when the device sends an enrollment request with empty or 0xa0 value for the KeyUsage extension. If it is not set, the service will use the IPSECIntermediate
Offline template. |
| CAType\CAType | DWORD | Based on setup | 1 = Enterprise
0 = Stand-alone |
| CAInfo\Configuration | String | Based on setup | If the CA is not installed on the same computer as the service, this registry key must be set with the CA information in the format of CAMachineName\CAName. |
| RefreshPeriod\RefreshPeriod | Binary | 7 | The number of days that pending requests will be kept in the service cache. Note: This value is located under HKEY_LOCAL_ROOT\Software\Microsoft\Cryptography\MSCEP\Refresh. |
| CacheRequest\CacheRequest | DWORD | 20 | The number of minutes that an issued certificate will be kept in the service cache. |
| CertsInMYStore\CertsInMyStore | DWORD | 1 | 1 = The service will look for its certificates in the computer "My" store.
0 = The service will look for its certificates in the computer "CEP" store. Note: If the key does not exist, the service will look for its certificates in the computer "CEP" store. |
| PasswordMax\PasswordMax | DWORD | 5 | The maximum number of available passwords. |
| PasswordVDir\PasswordVDir | String | MSCEP_Admin | This is the name of the virtual application that can be used for password requests. If set, MSCEP will accept password requests only from the defined virtual application. If the value is empty or not set, MSCEP will accept password requests retrieved from any virtual application. |
| PasswordValidity\PasswordValidity | DWORD | 60 | The number of minutes a password is valid. |
| PasswordLength\PasswordLength | DWORD | 8 | The Unicode character length of a password. |
| HashAlgorithm\HashAlgorithm | String | SHA1 | Specifies the hash algorithm the service will use when constructing the request to the CA. |
| DisableRenewalSubjectNameMatch\
DisableRenewalSubjectNameMatch |
DWORD | N/A | When set to 0x1, disables subject and subject alternative names match during certificate renewal. |
| UseSinglePassword\UseSinglePassword | DWORD | 0x0 | When set to 0x1, enables single-password mode. |
| EncryptedPassword\EncryptedPassword | Binary | N/A | When in single-password mode, the NDES will store encrypted password in this registry key protection by DPAPI. Do not modify this registry value directly. |
Note
Any changes to the previous keys should be followed by restarting IIS to ensure that the changes are loaded by the service.
Best Practices for Deploying and Using the Network Device Enrollment Service
Like any other service, the Network Device Enrollment Service can be deployed and configured in multiple ways. The following sections present the tradeoffs for various configurations and recommendations based mainly on prioritizing security above other considerations.
Setting SSL for the Administrator Site
Recommendation: Always set up the administrator site with SSL-only configuration. (Disable http access to this site.)
Pros: The password is returned encrypted.
Cons: An additional step is required to enroll for a server certificate and to configure the IIS for SSL.
Extend the Validity Period for the Device Certificates
This is a tradeoff between manageability and security. The longer the certificates are valid, the less frequent the enrollment process needs to occur. However, a longer validity period for keys might provide an attacker enough time to compute the private key information.
The service default setting validity period is one year.
Recommendation: For deployments of more than 100 devices, if the security risk is acceptable, you may consider extending the validity period of the device certificates to two years.
Pros: Management is easier the longer the device certificates are valid.
Cons: The security of the keys might be compromised if the certificate is valid for a longer period of time.
Stop the Service When It Is Not Used
Recommendation: After completing enrollment for all your devices, it is recommended to stop IIS. Before renewal, you will need to start IIS.
Note
Stopping IIS will clear all data stored in the service cache, for example, all passwords that are not used will be deleted from the password cache.
If IIS is used by other applications on the same machine, you may stop the SCEP application pool instead.
Pros: The attack surface of the service and its associated keys is reduced.
Cons: IIS must be restarted before the enrollment process.
Locking Down the Machine
Recommendation: Before setting up the service, it is recommended that you install IIS and lock it down using the Security Configuration Wizard. In addition, it is recommended that no other services will run on the same computer.
Pros: The attack surface of the computer hosting the service is reduced.
Cons: An additional configuration task is required.
Role Separation
Recommendation: For all deployments, it is recommended that you create a separate non-interactive account for the service credentials.
Based on existing PKI policies, CA administrators should consider setting up a separate account for the service administrators and an additional account as the device administrator. (This account should have the permissions to request a password.)
Pros: Different accounts for managing enterprise PKI, running the services, setting up the service, and requesting a password increase the security of an Enterprise PKI deployment.
Cons: Additional setup tasks are required to configure accounts and permissions.
Operational Guide for the Network Device Enrollment Service
The procedures in this section provide the operational tasks related to the ongoing maintenance and usage of the Network Device Enrollment Service.
Setting Up New Templates for the Service Certificates
The service uses two certificates. The encryption certificate is based on the "CEPEncryption" template, and the signature certificate is based on the "Exchange Enrollment Agent (Offline Request)" template. Since these are version 1 templates, they cannot be modified.
If the PKI administrator wants to change any of the service certificate templates, new ones will need to be created and enrolled. It is recommended that the default template is duplicated and the duplicated templates are used for enrollment.
To duplicate the CEP Encryption template
Log on to a domain joined computer as an Enterprise Administrator.
Run certtmpl.msc to start the Certificate Template snap-in. If the snap-in does not load, install the Remote Administration feature using the Role Management Tool.
In the Certificate Template snap-in, select the CEP Encryption template.
Note
Click the template and select Duplicate Template. A dialog box will appear where you enter the template type.
For template type, select strong>Windows Server 2003, Server Edition, and then click OK.
Name the new template, for example, CEP Encryption V2.
Modify the template as required, for example, extend the validity period to two years.
Click OK.
Next step is to enable the CA to issue certificates based on this template.
To enable the CA to issue certificates based on this template
- Run certsrv.msc.
- Select the root node.
- Right-click and select Retarget Certification Authority.
- Select the CA that is configured for the Network Device Enrollment Service.
- Expand the root node.
- Select the Certificate Templates node.
- Right-click, select New, and then click Certificate Template to Issue. A dialog box will appear.
- Select CEP Encryption V2.
Now, the CA is ready to receive enrollment requests based on the CEP Encryption V2 certificate template.
The following section explains how to use the template you just created.
Renewing Service Certificates
The service needs two valid certificates. If the service certificates have expired, or are about to expire, the service administrator needs to enroll for new certificates.
To enroll for new certificates
Log on to the computer hosting the Network Device Enrollment Service as a local administrator.
Start the MMC.
Click File, and then click Add Remove Snap-ins to open the snap-in selection dialog box.
Select the Certificates snap-in, and then click Add.
In the Certificate snap-in dialog box, select Computer Account, and then click Next.
On the next page, click Finish.
Click OK.
In the MMC, expand the root node.
Select the Personal node.
Right-click, select All Tasks, and then click Select New Certificates.
In the Certificate Enrollment dialog box, click Next.
On the next page, select the certificate template you would like to enroll. The default is CEP Encryption.
Click Details, and then click Properties.
In the Certificate Properties dialog box, click the Certification Authority tab.
Ensure that the CA that is configured for the Network Device Enrollment Service is the only CA that is enabled (checked) for this certificate enrollment.
Note
Depending on your certificate template settings, you might need to provide additional information to complete the enrollment based on your template settings.
Click OK.
In the Certificate Enrollment dialog box, click Enroll.
Once the enrollment is complete, expand Personal and its Certificate folders.
In the Result pane, identify the certificate you enrolled for in the previous steps.
Select the new certificate.
Right-click the certificate, select All Tasks, and then click Manage Private Keys. In the dialog box that appears, you can control the permissions on the keys that are associated with the new certificate.
Add Read permission to the account the service is running as, for example, SCEPSvc.
If you upgraded from previous releases of MSCEP and the service certificates are stored in the CEP store, set the registry key CertsInMyStore value to 1.
To force the service to implement the configuration changes, restart IIS.
Configuring Templates for Device Enrollment
By default, the service is configured to submit enrollment requests based on the IPSec (Offline Request) certificate template.
To change the default by modifying registry keys
- Log on to the computer hosting the Network Device Enrollment Service.
- Run regedit.
- Go to HKLM\Software\Microsoft\Cryptography\MSCEP.
- If your device sends a request with encryption and signing KeyUsage extensions, you will need to modify the GeneralPurposeTemplate registry value with the name of your new certificate template.
- If your device sends a request with encryption KeyUsage extension only, you will need to modify the EncryptionTemplate registry value with the name of your new certificate template.
- If your device sends a request with signing KeyUsage extension only, you will need to modify the SignatureTemplate registry value with the name of your new certificate template.
- To force the service to implement the configuration changes, restart IIS.
Enable Logging
The service can be configured to log additional information for troubleshooting purposes in a special log file. This log file can only be consumed by Microsoft's support personnel. The information will be logged in the profile of the account the service is running as. Therefore, you have to log on as this account to create its profile first.
To create the profile
- Log on to the NDES server with the appropriate permissions to manage Internet Information Services. Stop the NDES Service.
- Log on as the service account on the computer hosting NDES. This will create a user profile for the account.
- Once you see the user is completely logged on, the profile is created. Log off.
- Log on as an administrator on the computer hosting the NDES service.
- Open a Command Prompt as an Administrator (Run as administrator) and then run certutil -f -setreg debug 0xffffffe3.
- Configure the SCEP Application pool to "Load User Profile"
- Open the Internet Information Service (IIS) Management Console
- In the Connections pane, expand the IIS server hosting NDES and then click Application Pools.
- In the Application Pools pane, click the SCEP application pool.
- In the Actions pane, click Advanced Settings.
- In the Advanced Settings dialog box, set Load User Profile to True.
- Start the NDES service.
- Open Internet Information Service (IIS) Management Console.
- In the Connections pane, expand the IIS server hosting NDES and then click Application Pools.
- In the Application Pools pane, click SCEP.
- In the Actions Pane, click Start.
- Restart IIS (for example, run iisreset)
- Reproduce a failure.
- Look under the service account profile ( for example c:\Users\SCEPSvc) for the mscep.log file.
Backing Up
You may want to back up NDES if you have implemented a non-default configuration. By default, NDES obtains its service certificates based on the CEP Encryption and Enrollment Agent (Offline) certificate templates. These templates do not allow the export of private keys by default, so you will be unable to back up the certificate with its private key by default. If you have a need to recover NDES, you can reinstall the service or install NDES on another computer.
If you have made customizations to the NDES configuration, they should be located in the Windows registry key:
HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP
You can export that registry key and import it after reinstalling the NDES service to retain the customizations.
Note
- For information about exporting and importing Windows registry keys, see Reg export, Reg import, and Export all or part of the registry to a text file.
- If NDES is configured to run in single password mode (UseSinglePassword), the EncryptedPassword registry key stores the password. If the EncryptedPassword registry key is not present and the NDES service is started in single password mode, NDES will recreate the registry key and password. This new password will likely be different than the previous password. If this happens, then you will have to update any existing NDES clients to utilize the new password.
Troubleshooting
This section contains some resolutions for common issues.
Ensure your Certificate Revocation List (CRL) is current
NDES will fail to function properly if the registration authority certificate cannot validate the CRL. You can refresh your CRL by running certutil -crl on your CA from an administrative command prompt.
Server Manager Does Not Load
You do not see the link to the server manager console.
Resolution: Ensure that you are a member of the local administrator group.
Network Service Option Disabled
During setup, the option to select a Network Service account is disabled.
Resolution: If an Enterprise CA is installed on the same computer, the service cannot use Network Service for its credentials.
Setup Failed
The Network Device Enrollment Setup failed.
Resolution: The following must be verified.
- The issuing CA must be online.
- The following templates must exist on the domain controller.
- Exchange Enrollment Agent (Offline requests)
- CEP Encryption
- The logged on user must be a member of the Enterprise Administrator group.
The Password Cache is Full
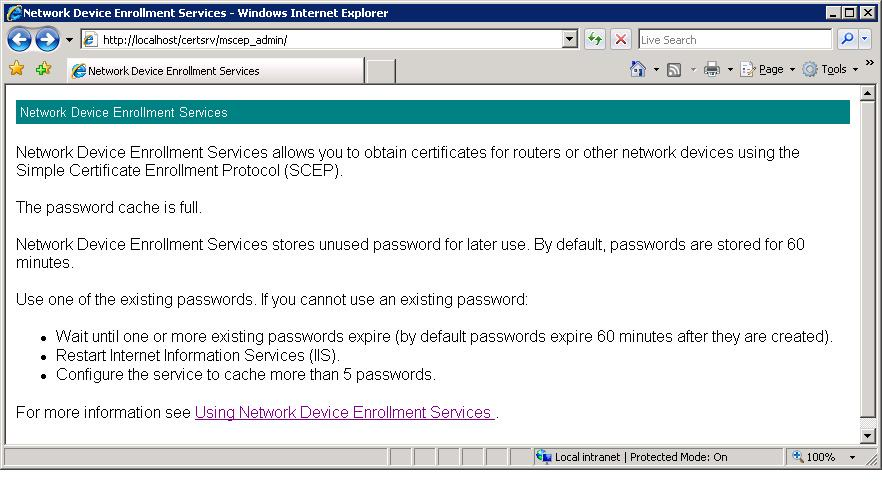
When opening the administration page, Figure 14 will appear.
Figure 14 : Cache is full error
Resolution: Try the following suggestions.
- Use one of the issued passwords.
- Wait until one of the passwords expires.
- Restart IIS.
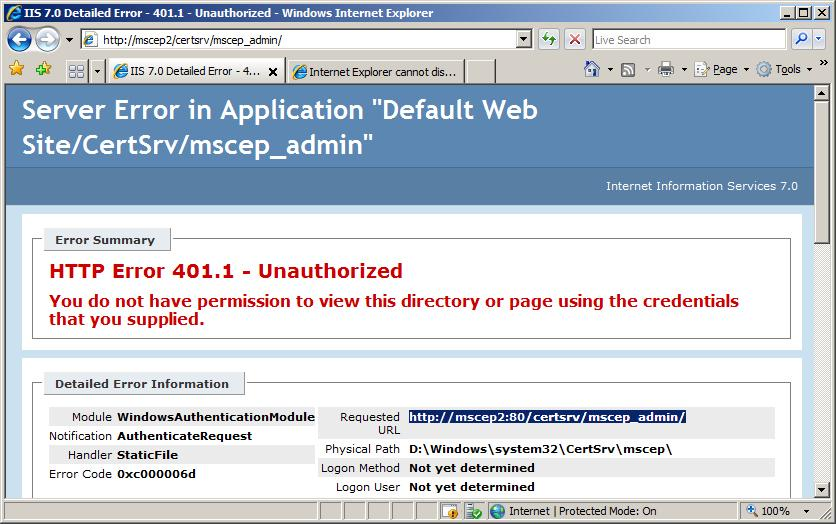
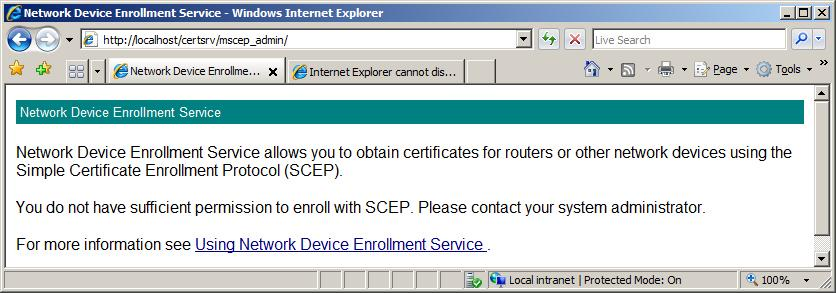
Administrator Cannot Obtain Password from the Local Machine
When an administrator tries to retrieve a password while logging on to the same computer that hosts the Network Device Enrollment Service, the retrieval will fail. This is due to the User Access Control (UAC) feature in Windows Vista and Windows Server 2008.
The error message displayed for the administrator will be either Figure 15 or Figure 16 .
Figure 15 : Unauthorized error
Figure 16 : Insufficient Permission error
Resolution: Ensure that the logged on user is not a member of the local administrator group, or retrieve the password from a remote computer (any other computer on the network).
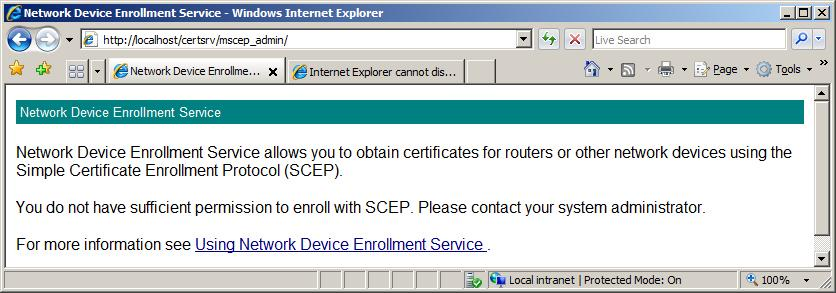
Administrator Cannot Obtain Password from a Remote Machine
When opening the administrator page, Figure 17 will appear.
Figure 17 : No Sufficient Permissions error
Resolution: The administrator who browsed to this page MUST have the following permissions.
- If the service configured CA is an Enterprise CA, the requestor must have Enroll permission to all three configured certificate templates. These templates are set through the EncryptionTemplate, SignatureTemplate, and GeneralPurposeTemplate registry keys. For more information about configuring templates, see Configuring Templates for Device Enrollment.
- If the service configured CA is a Stand-alone CA, the requestor must be a member of the CA administrators group.
Device Does not Trust Your Enterprise PKI
The device does not accept your PKI certificate (CA certificate and chain, certificate revocation list (CRL), device encryption certificates).
Resolution: The following are possible reasons.
- Your PKI certificates are using algorithms that are not supported by the device.
- Your PKI certificates are using key lengths that are not supported by the device, for example, RSA4096.
- Your PKI certificate includes a subject name with characters that are not supported by your device. Many old routers do not support the characters &,*, :, ;, ', ".
- Some devices do not support subordinate CAs, or a three-tier PKI chain.
Check your device specifications for certificate restrictions.
Device Cannot Enroll Anymore
Everything used to work, but now the device can no longer enroll.
Resolution: The following are possible reasons.
- Your service certificate expired or was revoked.
- Your CA certificate was renewed, since you configured the trust between the device and the CA.
For more information, check your computer event logs.
Error Events
| <- | Scroll right -> |
| ID | Internal Name | Source | Description | Diagnostics | Resolution |
| Event ID: 2 - The Network Device Enrollment Service cannot be started (%ErrorCode). %ErrorMessage | EVENT_MSCEP_FAILED_TO_LOAD | Microsoft-Windows-NetworkDeviceEnrollmentService | This generic error message indicates the enrollment service did not start successfully. The error code and error message included in the event description should contain more specific information about the problem encountered. | Check the error code in the event description for the specific reason the Network Device Enrollment Service failed to start. Check resources on the computer running the enrollment service to ensure that there is sufficient memory. Also, check the IIS logs for errors and warnings that may provide more information. An error 0x80004005 or 0x800700ea could mean that we have failed to connect to the CA, it might have been down when the first request was serviced by IIS and even if it is fully operational now, we might still get an error on every request we try to service. If the CA was down (due to a server reboot or service restart), confirm that it is operational at this time and re-start the IIS application pool for NDES. From an administrative command prompt: c:\windows\system32\inetsrv\appcmd stop apppool /apppool.name:SCEP c:\windows\system32\inetsrv\appcmd start apppool /apppool.name:SCEP For Windows Server 2012, also check: |
|
Event ID: 4 The Network Device Enrollment Service cannot be stopped (%ErrorCode) %ErrorMessage |
EVENT_MSCEP_FAILED_TO_UNLOAD | Microsoft-Windows-NetworkDeviceEnrollmentService | This generic error message indicates the enrollment service did not stop successfully. The error code and error message included in the event description should contain more specific information about the problem encountered. | Check the error code in the event description for the specific reason the Network Device Enrollment Service was unable to shut down. Also, check the IIS logs for errors and warnings that may provide more information. |
|
Event ID: 6 The Network Device Enrollment Service cannot provide its password because the user does not have Enroll permissions on the configured certificate template, or the certification authority is not enabled to issue certificates based on the configured certificate template.
|
EVENT_MSCEP_NO_PASSWORD_TEMPLATE | Microsoft-Windows-NetworkDeviceEnrollmentService | When requesting a password to set up a new device for device enrollment, the requesting user must have Read and Enroll permissions on the template(s) configured for device enrollment. By default, this template is IPSec (Offline Request). | On the Network Device Enrollment Service computer, check for the registry entries SignatureTemplate, EncryptionTemplate, and GeneralPurposeTemplate under the key "HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP\". Use the Certificate Templates MMC to check the permissions on the IPSec (Offline Request) template or any templates identified in the previous registry entries. Note You must be able to connect to Active Directory, where Certificate Templates are stored, to perform this step. |
Open the Certificate Templates MMC and grant the requesting user Read and Enroll permissions on the IPSec (Offline Request) template or any templates identified in the previous registry entries. Note You must be able to connect to Active Directory, where Certificate Templates are stored, to perform this step. |
Event ID: 7 The Network Device Enrollment Service failed to return the certification authority certificate to the caller (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_GET_CA_CERT_FAILED | Microsoft-Windows-NetworkDeviceEnrollmentService | This event occurs upon device request. The Network Device Enrollment Service failed to retrieve the certification authority certificate and return it to the caller. | Note the error code and error message included in the event description. Ensure that the CA is available and Certificate Services is running on the CA (certutil -ping on CA). Ensure that the Network Device Enrollment Service can connect to the CA and to Active Directory. Otherwise, your computer may be low on physical memory. |
Resolve any errors identified in the event description and try to resubmit the request. |
Event ID: 8 The Network Device Enrollment Service cannot retrieve information about the Certification Authority (%ErrorCode). %ErrorMessage
|
EVENT_MSCEP_FAILED_CA_INFO | Microsoft-Windows-NetworkDeviceEnrollmentService | This event occurs on Network Device Enrollment Service startup. | Note the error code and error message included in the event description. Ensure that the CA is available and Certificate Services is running on the CA (certutil -ping on CA). Ensure that the Network Device Enrollment Service can connect to the CA and to Active Directory. |
Resolve any errors identified in the event description. |
Event ID: 9 The Network Device Enrollment Service cannot retrieve the certification authority certificate (%ErrorCode). %ErrorMessage
|
EVENT_MSCEP_FAILED_CA_CERT | Microsoft-Windows-NetworkDeviceEnrollmentService | This event occurs on Network Device Enrollment Service startup. | Note the error code and error message included in the event description. Ensure that the CA is available and Certificate Services is running on CA (certutil -ping on CA). Ensure that the Network Device Enrollment service can connect to the CA and to Active Directory. |
Resolve any errors identified in the event description. |
Event ID: 10 The Network Device Enrollment Service cannot retrieve one of its required certificates (%ErrorCode). %ErrorMessage
|
EVENT_MSCEP_FAILED_RA_CERT | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service has two certificates: a key exchange certificate used for encryption and a Network Device Enrollment Service certificate used for signing. At least one of the certificates is not available or not valid. | Note the error code and error message included in the event description. The Network Device Enrollment Service certificates are stored in either the default machine certificate store (if the value of the registry entry "CertsInMyStore" is 1) or in the "CEP" store (if the registry entry does not exist or if its value is 0). Use the Certificates MMC on the enrollment service machine to check the validity of any enrollment service certificates. Verify that all of the requirements documented in Service Startup section have been met. To validate certificate chain, certutil.exe -verify command can be used. |
Resolve any errors identified in the event description. If necessary, re-enroll for a signing certificate from the Certificates MMC. See Renewing Service Certificates. |
Event ID: 11 The Network Device Enrollment Service received an http message without the "Operation" tag or with an invalid "Operation" tag. |
EVENT_MSCEP_NO_OPERATION | Microsoft-Windows-NetworkDeviceEnrollmentService | The service has received an invalid request from a client device. The "Operation" tag in the http request from the client was either invalid or not present. | Check IIS log to find out what query string was submitted. Note the query string's <operation>. Use certutil to check whether the Public Key Cryptography Standard 7 (PKCS7) package from the client is valid. (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured.) Otherwise, enable CAPI2 diagnostics and reproduce the error. |
If necessary, contact the vendor of the SCEP client and make sure that all the required fields are present. |
Event ID: 12 The Network Device Enrollment Service received an http message without the "Message" tag. |
EVENT_MSCEP_NO_MESSAGE | Microsoft-Windows-NetworkDeviceEnrollmentService | The service has received an invalid request from a client device. The "Message" tag in the http request from the client was either invalid or not present. | Check IIS log to find out what query string was submitted. Note the query string's <message>. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and reproduce the error. |
If necessary, contact the vendor of the SCEP client and ensure that all the required fields are present. |
Event ID: 13 The Network Device Enrollment Service cannot encrypt the response to a client request (%ErrorCode). %ErrorMessage
|
EVENT_MSCEP_FAIL_TO_ENCRYPT | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a device request because it was unable to complete an encryption operation. | Note the error code and error message included in the event description. The computer running the Network Device Enrollment Service may be low on physical memory, or the event description may contain a more specific error code to help diagnose the issue. Check resources on the enrollment service computer. Also, check the IIS logs for errors and warnings that may provide more information. Otherwise, enable Microsoft-Windows-CAPI2/Diagnostics in the Windows Event Viewer. Re-run the operation and examine the logged CAPI2 diagnostics entries. |
Resolve any errors identified in the event description. Try re-starting the service or the computer to free system resources. If the error persists, call Microsoft Customer Support Services. |
Event ID: 14 The Network Device Enrollment Service cannot sign the response to a client request (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_TO_SIGN | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a device request because it was unable to complete a signing operation. | Note the error code and error message included in the event description. The computer running the Network Device Enrollment Service may be low on physical memory, or the event description may contain a more specific error code to help diagnose the issue. Check resources on the enrollment service computer. Also, check the IIS logs for errors and warnings that may provide more information. Otherwise, enable Microsoft-Windows-CAPI2/Diagnostics in the Windows Event Viewer. Re-run the operation and examine the logged CAPI2 diagnostics entries.
|
Resolve any errors identified in the event description. Try re-starting the service or the computer to free system resources. If the error persists, call Microsoft Customer Support Services. |
Event ID: 15 The Network Device Enrollment Service cannot convert encoded portions of the client's http message, or the converted message is larger than 64K (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_TO_CONVERT | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem converting the http message, or that message was too long. | Note the error code and error message included in the event description. Check the IIS log to find out what query string was submitted. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. If necessary, contact the vendor of the SCEP client and make sure that the request is being submitted correctly. |
Event ID: 16 The Network Device Enrollment Service cannot decode the http message from the client (%ErrorCode). %ErrorMessage
|
EVENT_MSCEP_FAIL_TO_DECODE | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem decoding the http message. | Note the error code and error message included in the event description. Check the IIS log to find out what query string was submitted. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error.
|
Resolve any errors identified in the event description. If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 17 The Network Device Enrollment Service cannot retrieve required information, such as the transaction ID, message type, or signing certificate, from the client's PKCS7 message (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_TO_RETRIEVE_INFO | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem parsing the http message. | Note the error code and error message included in the event description. Check the IIS log to find out what query string was submitted. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 18 The Network Device Enrollment Service cannot decrypt the client's PKCS7 message (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_TO_DECRYPT_INNER | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem decrypting the PKCS7 message. | Note the error code and error message included in the event description. Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 19 The Network Device Enrollment Service failed trying to retrieve a certificate from the CA. Verify that the CA service is running. Use the Certification Authority MMC to verify that the Network Device Enrollment Service account has Read permissions on the CA service. Verify that the serial number specified in the GETCERT request is correct, and that the CA service has successfully created a certificate with the specified serial number (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_TO_GET_CERT_FROM_NUMBER | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request for a certificate. | Note the error code and error message included in the event description. Check the IIS log to find out what query string was submitted. Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
|
Event ID: 23 The Network Device Enrollment Service cannot complete the PKCS7 request. (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_CERT_REQ | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed while executing a client device request. | Note the error code and error message included in the event description. Ensure that the CA is available and Certificate Services is running on the CA (certutil -ping on CA). Ensure that the Network Device Enrollment Service can connect to the CA. Ensure that the enrollment service has Read and Enroll permissions on the certificate template(s) configured for device enrollment. [These will be the templates identified in the registry entries "SignatureTemplate", "EncryptionTemplate", and "GeneralPurposeTemplate" under the key "HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP\" on the enrollment service computer; otherwise, the default is the "IPSec (Offline Request)" template.] Otherwise, your computer may be low on physical memory.
|
Resolve any specific errors identified in the event description, as well as any connectivity or permissions problems identified previously, and try to resubmit the request.
|
Event ID: 24 The Network Device Enrollment Service cannot find the issuer name or serial number in the client's PKCS7 message. (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_NAME_NUMBER_FROM_MESSAGE | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request. In this case, it could not find the certificate serial number within the client's PKCS7 request. | Note the error code and error message included in the event description. Check the IIS log to find out what query string was submitted. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. If necessary, contact the vendor of the SCEP client and make sure that the request is being submitted correctly. |
Event ID: 25 The Network Device Enrollment Service cannot locate a valid certificate request ID that matches the transaction ID in the client's PKCS7 message. (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_TO_GET_ID | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request. | Note the error code and error message included in the event description. Check the IIS log to find out what query string was submitted. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error.
|
Resolve any errors identified in the event description. If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 26 The Network Device Enrollment Service was not able to query the Certification Authority (CA) for a previously submitted device certificate request. Verify that the CA service is running and that the Network Device Enrollment Service account has Read permissions on the CA service. Use the Certification Authority MMC to verify the permissions on the CA service. The error returned was (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_QUERY_CA | Microsoft-Windows-NetworkDeviceEnrollmentService | Network Device Enrollment Service cannot contact the CA and, therefore, cannot retrieve a pending certificate. | Note the error code and error message included in the event description. Otherwise, your computer may be low on physical memory. |
Follow the troubleshooting steps identified in the error message. Ensure that the CA is available and Certificate Services is running on the CA, for example, by executing the command "certutil -ping" at the command line on the CA. Ensure that the Network Device Enrollment Service can connect to the CA. Use the Certification Authority MMC to verify the Network Device Enrollment Service account has Read permissions on the CA service. Otherwise, resolve any specific errors identified in the event description and try to resubmit the request. |
Event ID: 28 Windows 2008 text: The Network Device Enrollment Service cannot locate a required password in the certificate request. Windows 2008 R2 text: The Network Device Enrollment Service cannot locate a required password in the certificate request. Either a password must be present in the certificate request or the certificate request should be signed with a valid signing certificate. The signing certificate must chain up to a trusted root in the Enterprise store. The signing certificate and the certificate request must have the same subject name or subject alternate name.
|
EVENT_MSCEP_NO_PASSWORD | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it could not locate the required password in the request. | Check the IIS log to find out what query string was submitted. Check the device configuration to ensure that the password is being submitted as part of the request. Use certutil to check whether the Public PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 29 The password in the certificate request cannot be verified. It may have been used already. Obtain a new password to submit with this request. |
EVENT_MSCEP_INVALID_PASSWORD | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because the submitted password is invalid. | Check the IIS log to find out what query string was submitted. Check the device configuration to ensure that the correct password is being submitted as part of the request. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error.
|
If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 30 The Network Device Enrollment Service cannot add an alternative subject name extension to the certificate request (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_ADD_ALT | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem adding a subject alternative name extension to the certificate request. | Note the error code and error message included in the event description. The computer running the Network Device Enrollment Service may be low on physical memory, or the event description may contain a more specific error code to help diagnose the issue. Check resources on the enrollment service computer. Also, check the IIS logs for errors and warnings that may provide more information. Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. Try re-starting the service or the computer to free system resources. If the error persists, call Microsoft Customer Support Services. |
Event ID: 31 The Network Device Enrollment Service cannot submit the certificate request (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAIL_SUBMIT | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed while submitting a certificate request on behalf of a client device. | Note the error code and error message included in the event description. Ensure that the CA is available and Certificate Services is running on the CA (certutil -ping on CA). Ensure that the Network Device Enrollment Service can connect to the CA. Ensure that the enrollment service has Read and Enroll permissions on the certificate template(s) configured for device enrollment. (These will be the templates identified in the registry entries "SignatureTemplate", "EncryptionTemplate", and "GeneralPurposeTemplate" under the key "HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP\" on the enrollment service computer; otherwise, the default "IPSec (Offline Request)" template will be used). Otherwise, your computer may be low on physical memory. |
Resolve any specific errors identified in the event description, as well as any connectivity or permissions problems identified previously, and try to resubmit the request. |
Event ID: 32 The Network Device Enrollment Service cannot retrieve the certificate identified by this request ID (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_GET_REQUEST_ID | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem retrieving the certificate's request ID. This event is logged when the service is unable to submit the "Request ID" of the certificate request earlier. | Note the error code and error message included in the event description. The computer running the Network Device Enrollment Service may be low on physical memory, or the event description may contain a more specific error code to help diagnose the issue. Check resources on the enrollment service computer. Also, check the IIS logs for errors and warnings that may provide more information. Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. Try re-starting the service or the computer to free system resources. If the error persists, call Microsoft Customer Support Services. |
Event ID: 33 The Network Device Enrollment Service failed to cache this certificate ID and transaction ID (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_ADD_ID | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because of a server problem. It cannot locate the certificate identified in the request. | Note the error code and error message included in the event description. The computer running the Network Device Enrollment Service may be low on physical memory, or the event description may contain a more specific error code to help diagnose the issue. Check resources on the enrollment service computer. Also, check the IIS logs for errors and warnings that may provide more information. Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. Try re-starting the service or the computer to free system resources. If the error persists, call Microsoft Customer Support Services. |
Event ID: 34 At least one of the certificates for the Network Device Enrollment Service has expired. Verify that both the encryption and signing certificates are valid and restart the service. |
EVENT_SCEP_RA_EXPIRE | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service requires two certificates: a key exchange certificate and a Network Device Enrollment Service certificate used for signing. As indicated in the event description, the Network Device Enrollment Service's key exchange (encryption) and/or enrollment agent (signing) certificates have expired. | The Network Device Enrollment Service certificates are stored in either the default machine certificate store (if the value of the registry entry "CertsInMyStore" is 1) or in the "CEP" store (if the registry entry does not exist or if its value is 0). | Using the Certificates MMC, locate and renew all Network Device Enrollment Service certificates to ensure continued service availability. For detailed steps, see Renewing Service Certificates. |
Event ID: 35 At least one of the certificates for the Network Device Enrollment Service will expire soon. Check the validity period for both the encryption and signing certificates. Renew any certificates that are nearing the end of their validity period and restart the service. |
EVENT_SCEP_RA_CLOSE_TO_EXPIRE | Microsoft-Windows-NetworkDeviceEnrollmentService | This event is of type "error", but it can be treated as a warning. As indicated in the event description, the Network Device Enrollment Service's key exchange (encryption) and/or enrollment agent (signing) certificates are near the end of their validity period and are at risk of expiring.
|
The Network Device Enrollment Service certificates are stored in either the default machine certificate store (if the value of the registry entry "CertsInMyStore" is 1) or in the "CEP" store (if the registry entry does not exist or if its value is 0). | Using the Certificates MMC, locate and renew all Network Device Enrollment Service certificates to ensure continued service availability. For detailed steps, see Renewing Service Certificates. |
Event ID: 36 The Network Device Enrollment Service failed while attempting to write the header portion of an http response (%ErrorCode). %ErrorMessage |
EVENT_SCEP_SERVER_SUPPORT
|
Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem writing the header portion of the http response. | Note the error code and error message included in the event description. The computer running the Network Device Enrollment Service may be low on physical memory, or the event description may contain a more specific error code to help diagnose the issue. Check resources on the enrollment service computer. Also, check the IIS logs for errors and warnings that may provide more information. Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error.
|
Resolve any errors identified in the event description. Try re-starting the service or the computer to free system resources. If the error persists, call Microsoft Customer Support Services. |
Event ID: 37 The Network Device Enrollment Service failed while attempting to write the data portion of an http response (%ErrorCode). %ErrorMessage
|
EVENT_SCEP_WRITE_DATA | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it had a problem writing the data portion of the http response. | Note the error code and error message included in the event description. The computer running the Network Device Enrollment Service may be low on physical memory, or the event description may contain a more specific error code to help diagnose the issue. Check resources on the enrollment service computer. Also, check the IIS logs for errors and warnings that may provide more information. Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
Resolve any errors identified in the event description. Try re-starting the service or the computer to free system resources. If the error persists, call Microsoft Customer Support Services. |
Event ID: 38 The Network Device Enrollment Service detected an invalid message type in the client's PKCS7 message. |
EVENT_MSCEP_BAD_MESSAGE_TYPE | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because the message type is invalid. | Check the IIS log to find out what query string was submitted. Check the device configuration to ensure that the correct message type is being submitted as part of the request. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 39 The Network Device Enrollment Service cannot find key usage information in the certificate request and will use both the Signature and Exchange key usages. |
EVENT_MSCEP_NO_KEY_USAGE | Source: Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to find a key usage extension in the client's request and hence used both the Signature and Exchange key usages. | Check the IIS log to find out what query string was submitted.
Check the device configuration to ensure that the correct key usage information is being submitted as part of the request. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 41 The Network Device Enrollment Service cannot issue a password because the requester is not an administrator on the Certification Authority. |
EVENT_MSCEP_NO_PASSWORD_STANDALONE | Microsoft-Windows-NetworkDeviceEnrollmentService | When requesting a password to set up a new device for device enrollment, if the enrollment service is configured for a stand-alone (not enterprise) CA, the requesting user must have administrative privileges on the CA. | NA | Ensure that the user is a member of the local Administrators group on the stand-alone CA. |
Event ID: 42 The Network Device Enrollment Service cannot decode an X509 certificate request. |
EVENT_MSCEP_FAIL_DECODE_X509_REQUEST | Microsoft-Windows-NetworkDeviceEnrollmentService | The Network Device Enrollment Service failed to process a client device's request because it could not decode the certificate request. | Check the IIS log to find out what query string was submitted. Check the device configuration to ensure that the password is being submitted as part of the request. Use certutil to check whether the PKCS7 package from the client is valid (certutil -v p7request.txt, where p7request.txt is a file in which the query string is captured). Otherwise, enable CAPI2 diagnostics and, if possible, reproduce the error. |
If necessary, contact the vendor of the SCEP client and ensure that the request is being submitted correctly. |
Event ID: 43 This password has already been used to request a (%KeyUsage) certificate. Only one signing certificate and one exchange certificate can be issued per password. Obtain a new password to use with this request, or create a new request with a different key usage and the same password, and then try again. |
EVENT_MSCEP_INVALID_USAGE_FOR_PASSWORD | Microsoft-Windows-NetworkDeviceEnrollmentService | As the event describes, a password can only be used one time per device per key usage (signing and encryption). | NA | Go to the Enrollment Service Administration site and obtain a new password to configure on the device. |
Event ID: 44 The Network Device Enrollment Service cannot obtain the CRL for key (%KeyID) from the Certification Authority. Verify that the CA service is running, the Network Device Enrollment Service account has Read permissions on the CA service, and the CA service has successfully created the latest CRL. Use the Certification Authority MMC to verify the permissions on the CA service. Use the command Certutil -config "%ConfigString" -cainfo crl %KeyID to verify that the CA service has created the latest CRL. The error returned was (%ErrorCode). %ErrorString. |
EVENT_MSCEP_GETCRL_FAILED | Microsoft-Windows-NetworkDeviceEnrollmentService | This error occurs when the service attempts to obtain the CRL from the CA directly and fails. | NA | Follow the troubleshooting steps identified in the error message. |
Event ID: 45 The Network Device Enrollment Service cannot match the issuer name and serial number in the device request to any CA certificate. Verify that the device request contains the correct CA certificate information, and then resubmit the request. |
EVENT_MSCEP_NOMATCH_ISSUERNAME_SERIALNUMBER | Microsoft-Windows-NetworkDeviceEnrollmentService | This event occurs in the scenario in which the device certificate was pended by the CA and subsequently issued interactively by a CA manager. In this scenario, the device administrator must submit another request to the service to obtain the device certificate. In this case, the service was unable to match the "issuer" information in the request to the CA certificate. | NA | Follow the troubleshooting steps identified in the error message. |
Event ID: 46 The Network Device Enrollment Service failed to load the hash algorithm specified at location %RegistryLocation. Use the command "certutil -v -csplist" to verify that the computer on which the Network Device Enrollment Service is installed supports the hash algorithm specified. Near the end of the command output, look for the section labeled "Hash Algorithms". If the algorithm specified in the registry is not listed, configure a different hash algorithm in the registry. The error returned was (%ErrorCode). %ErrorMessage |
EVENT_MSCEP_FAILED_HASH_ALGORITHM | Microsoft-Windows-NetworkDeviceEnrollmentService | This error can occur when the service administrator has configured a custom hash algorithm in the registry, and this algorithm is not supported on the computer on which the service is running. | NA | Follow the troubleshooting steps identified in the error message. |
Event ID: 49 The Network Device Enrollment Service has failed to decrypt the encrypted password or the decrypted password's length doesn't match the one configured in the registry. To fix this, delete the EncryptedPassword entry in the registry. |
EVENT_MSCEP_FAILED_DECRYPT_PASSWORD
|
Microsoft-Windows-NetworkDeviceEnrollmentService
|
This error can occur due to corruption in the registry or a password reset for the account used to run NDIS. | NA | Follow the troubleshooting steps identified in the error message. |
Event ID: 51 The Network Device Enrollment Service cannot create or modify the registry key "%1"; Grant Read and Write permissions on the registry key "%2"; to the account that the Network Device Enrollment Service is running as. |
EVENT_MSCEP_UNABLE_TO_CREATEORSET_REGKEY | Microsoft-Windows-NetworkDeviceEnrollmentService | This error can occur when NDIS was installed on the Windows 2008 Server SP1 with no KB959193 hotfix deployed. In this case, the setup doesn't set permission required for the single password mode. | NA | Follow the troubleshooting steps identified in the error message. |
Appendix 1: The Differences Between the Network Device Enrollment Service and Previous MSCEP Implementations
MSCEP is available for previous versions of Windows through the appropriate resource kit for that version. After installing the resource kit, start the cepsetup.exe application. This setup application will guide you through the required configuration for setting up MSCEP.
The following features are included in Windows Server 2008 and were not implemented in previous releases.
- Set up a remote CA The Network Device Enrollment Service can be configured with an enterprise CA on a remote computer. Previous releases forced it to use the local CA.
- Hash Algorithm The Network Device Enrollment Service uses SHA-1 as the default hash algorithm when constructing the request to the CA. In addition, the hash algorithm is configurable through the registry. Previous releases always used MD5 as the hash algorithm.
- Defaults The following configurations are set with a more secure default.
- A password is required by default.
- The maximum number of passwords is set to five. In previous releases, it was set to 1000.
- Single virtual application The Network Device Enrollment Service creates two virtual applications so SSL can be set on the virtual application that is created to the password requests. Previous releases created a single virtual application for password requests and enrollment requests. It did not allow administrators to enable SSL for password requests.
- Request size limit In Windows Server 2008, the request size is limited to 64Kb.
- Default credentials The Network Device Enrollment Service no longer defaults to run as Local System.
- Certificate renewal The Network Device Enrollment Service supports renewing the service certificates.
- Configure Templates The Network Device Enrollment Service supports configuring the certificate template for all request types.
Appendix 2: Set Registry Keys to Default Values
The following script can be used to set default values to all the registry keys that the service uses.
To run the script
- Copy the following content (in grey) to a file, and then save the file as mscep.reg.
- Run mscep.reg from the command line.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1]
"SignatureTemplate"="IPSECIntermediateOffline"
"EncryptionTemplate"="IPSECIntermediateOffline"
"GeneralPurposeTemplate"="IPSECIntermediateOffline"
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1\EnforcePassword]
"EnforcePassword"=dword:1
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1\Refresh]
"RefreshPeriod"=hex:07
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1\CacheRequest]
"CacheRequest"=dword:14
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1\PasswordMax]
"PasswordMax"=dword:5
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1\PasswordValidity]
"PasswordValidity"=dword:3c
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1\PasswordLength]
"PasswordLength"=dword:8
[HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\MSCEP1\HashAlgorithm]
"HashAlgorithm"="SHA1"
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\MSCEP\UseSinglePassword]
"UseSinglePassword"=dword:00000000
Note The script will override all changes made to the default settings. It will not override settings that can be set up only through setup (like the CA the service will use).
Related Resources
Connecting iPads to an Enterprise Wireless 802.1x Network Using Certificates and Network Device Enrollment Services (NDES) https://blogs.technet.com/b/pki/archive/2012/02/27/ndes-and-ipads.aspx