Investigate Microsoft Sentinel incidents in depth in the Azure portal
Microsoft Sentinel incidents are files that contain an aggregation of all the relevant evidence for specific investigations. Each incident is created (or added to) based on pieces of evidence (alerts) that were either generated by analytics rules or imported from third-party security products that produce their own alerts. Incidents inherit the entities contained in the alerts, as well as the alerts' properties, such as severity, status, and MITRE ATT&CK tactics and techniques.
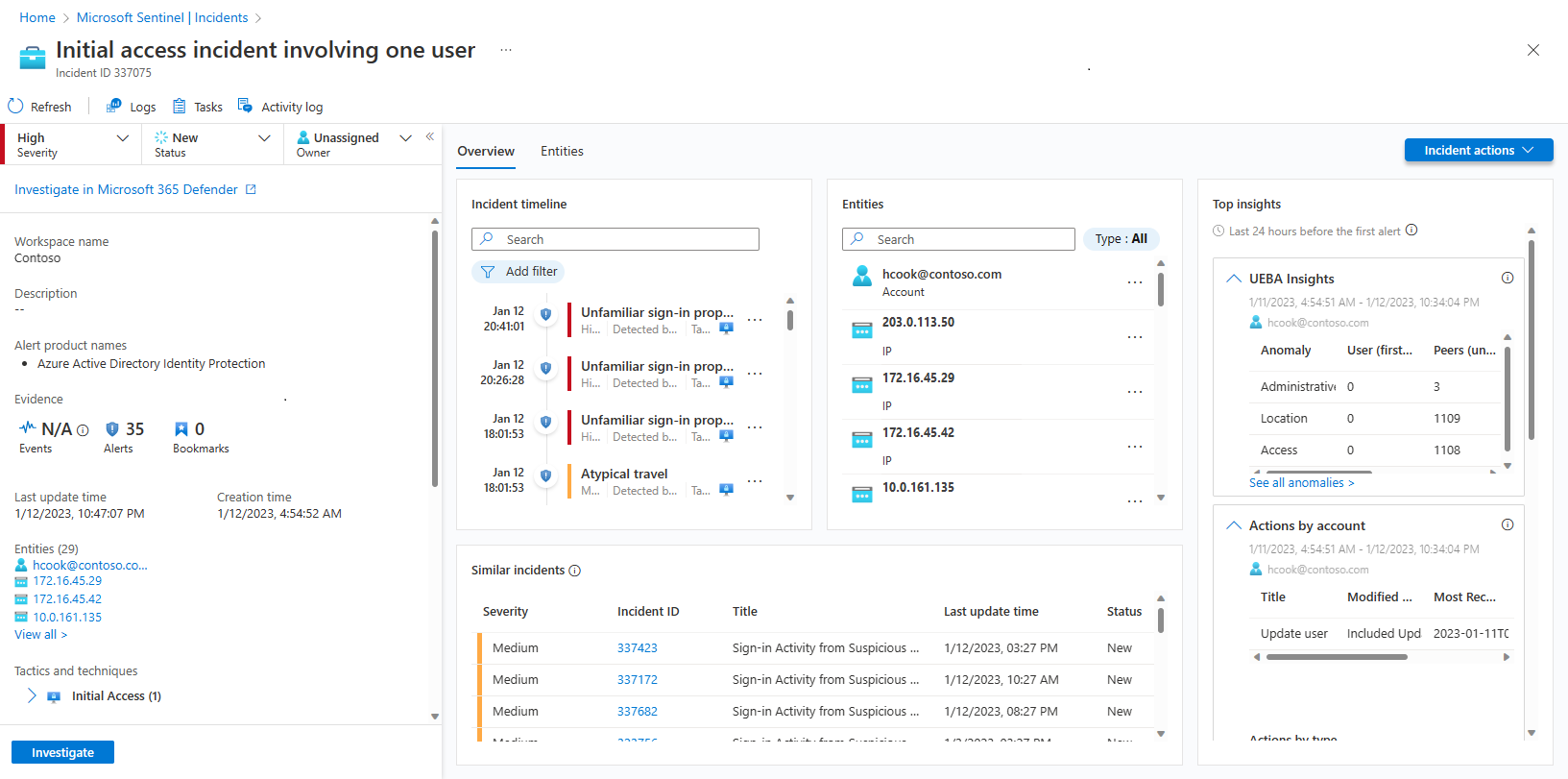
Microsoft Sentinel gives you a complete, full-featured case management platform in the Azure portal for investigating security incidents. The Incident details page is your central location from which to run your investigation, collecting all the relevant information and all the applicable tools and tasks in one screen.
This article describes how to investigate an incident in depth, helping you navigate and investigate your incidents more quickly, effectively, and efficiently, and reducing your mean time to resolve (MTTR).
Prerequisites
The Microsoft Sentinel Responder role assignment is required to investigate incidents.
Learn more about roles in Microsoft Sentinel.
If you have a guest user that needs to assign incidents, the user must be assigned the Directory Reader role in your Microsoft Entra tenant. Regular (nonguest) users have this role assigned by default.
If you're currently viewing the legacy experience of the incident details page, toggle on the new experience at the top-right of the page to continue with the procedures in this article for the new experience.
Prepare the ground properly
As you're setting up to investigate an incident, assemble the things you need to direct your workflow. You find the following tools on a button bar at the top of the incident page, right below the title.
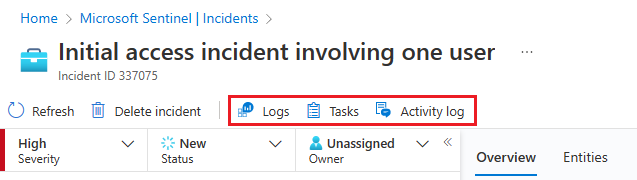
Select Tasks to see the tasks assigned for this incident, or to add your own tasks. Tasks can improve process standardization in your SOC. For more information, see Use tasks to manage incidents in Microsoft Sentinel.
Select Activity log to see if any actions have already been taken on this incident—by automation rules, for example—and any comments that have been made. You can add your own comments here as well. For more information, see Audit incident events and add comments.
Select Logs at any time to open a full, blank Log analytics query window inside the incident page. Compose and run a query, related or not, without leaving the incident. So, whenever you're struck with sudden inspiration to go chasing a thought, don't worry about interrupting your flow--the logs are there for you. For more information, see Dive deeper into your data in Logs.
The Incident actions button is also located opposite the Overview and Entities tabs. Here, you have the same actions described earlier as available from the Actions button on the details pane on the Incidents grid page. The only one missing is Investigate, which is available on the left-hand details panel instead.
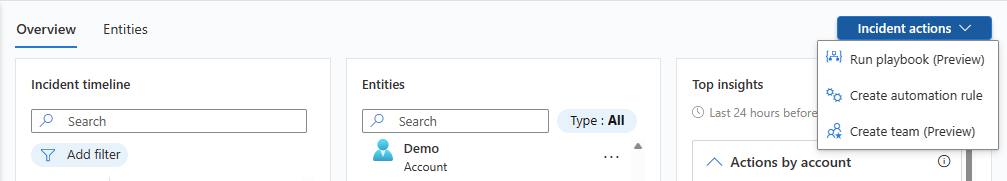
The available actions under the Incident actions button include:
| Action | Description |
|---|---|
| Run playbook | Run a playbook on this incident to take particular enrichment, collaboration, or response actions. |
| Create automation rule | Create an automation rule that runs only on incidents like this one (generated by the same analytics rule) in the future. |
| Create team (Preview) | Create a team in Microsoft Teams to collaborate with other individuals or teams across departments on handling the incident. If a team has already been created for this incident, this menu item displays as Open Teams. |
Get the whole picture on the incident details page
The left-hand panel of the incident details page contains the same incident detail information that you saw on the Incidents page to the right of the grid. This panel is always on display, no matter which tab is shown on the rest of the page. From there, you can see the incident's basic information, and drill down in the following ways:
Under Evidence, select Events, Alerts, or Bookmarks to open a Logs panel within the incident page. The Logs panel displays with the query of whichever of the three you selected, and you can go through the query results in depth, without pivoting away from the incident. Select Done to close the pane and return to your incident. For more information, see Dive deeper into your data in Logs.
Select any of the entries under Entities to display it in the Entities tab. Only the first four entities in the incident are shown here. See the rest of them by selecting View all, or in the Entities widget on the Overview tab, or in the Entities tab. For more information, see Entities tab.
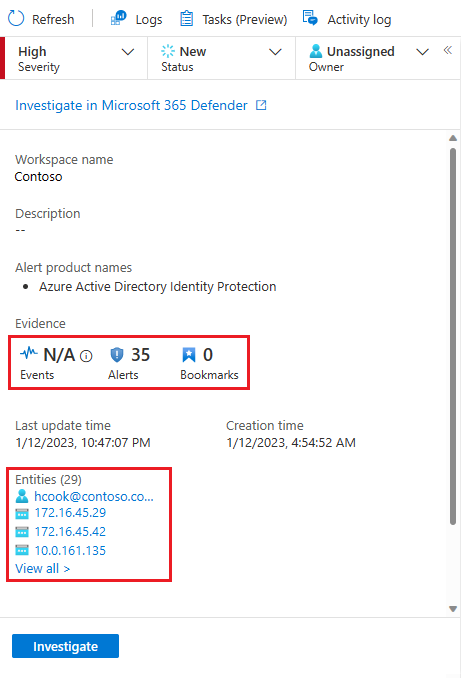
Select Investigate to open the incident in the graphical investigation tool that diagrams relationships between all the elements of the incident.
This panel can also be collapsed into the left margin of the screen by selecting the small, left-pointing double arrow next to the Owner drop-down. Even in this minimized state, however, you'll still be able to change the owner, status, and severity.
The rest of the incident details page is divided into two tabs, Overview and Entities.
The Overview tab contains the following widgets, each of which represents an essential objective of your investigation.
| Widget | Description |
|---|---|
| Incident timeline | The Incident timeline widget shows you the timeline of alerts and bookmarks in the incident, which can help you reconstruct the timeline of attacker activity. Select an individual item to see all of its details, enabling you to drill down further. For more information, see Reconstruct the timeline of the attack story. |
| Similar incidents | In the Similar incidents widget, you see a collection of up to 20 other incidents that most closely resemble the current incident. This allows you to view the incident in a larger context and helps direct your investigation. For more information, see Check for similar incidents in your environment. |
| Entities | The Entities widget shows you all the entities that have been identified in the alerts. These are the objects that played a role in the incident, whether they be users, devices, addresses, files, or any other types. Select an entity to see its full details, which are displayed in the Entities tab. For more information, see Explore the incident's entities. |
| Top insights | In the Top insights widget, you see a collection of results of queries defined by Microsoft security researchers that provide valuable and contextual security information on all the entities in the incident, based on data from a collection of sources. For more information, see Get the top insights into your incident. |
The Entities tab shows you the complete list of entities in the incident, which are also shown in the Entities widget on the Overview page. When you select an entity in the widget, you're directed here to see the entity's full dossier—its identifying information, a timeline of its activity (both within and outside the incident), and the full set of insights about the entity, just as you would see in its full entity page, but limited to the time frame appropriate to the incident.
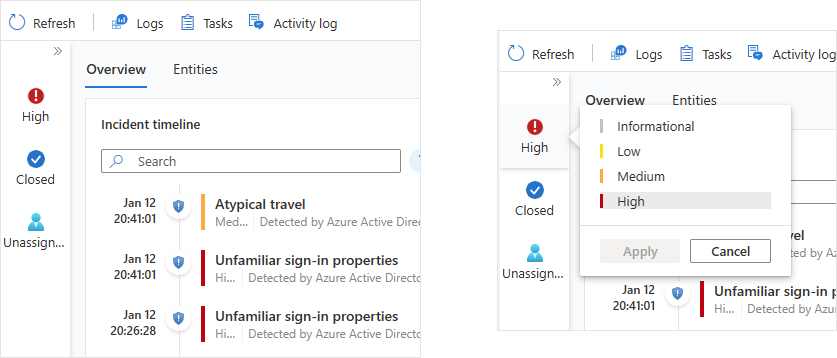
Reconstruct the timeline of the attack story
The Incident timeline widget shows you the timeline of alerts and bookmarks in the incident, which can help you reconstruct the timeline of attacker activity.
Hover over any icon or incomplete text element to see a ToolTip with the full text of that icon or text element. These ToolTips come in handy when the displayed text is truncated due to the limited width of the widget. See the example in this screenshot:
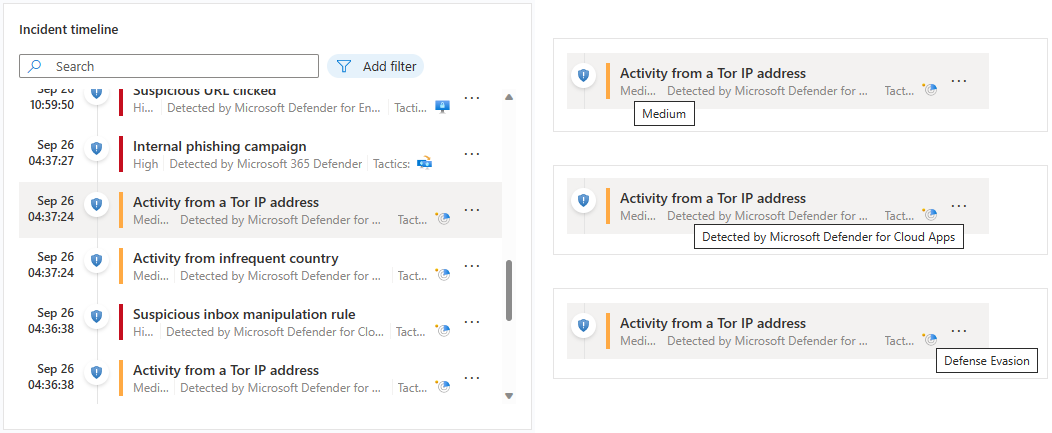
Select an individual alert or bookmark to see its full details.
Alert details include the alert's severity and status, the analytics rules that generated it, the product that produced the alert, the entities mentioned in the alert, the associated MITRE ATT&CK tactics and techniques, and the internal System alert ID.
Select the System alert ID link to drill down even further into the alert, opening the Logs panel and displaying the query that generated the results and the events that triggered the alert.
Bookmark details aren't exactly the same as alert details; while they also include entities, MITRE ATT&CK tactics and techniques, and the bookmark ID, they also include the raw result and the bookmark creator information.
Select the View bookmark logs link to open the Logs panel and display the query that generated the results that were saved as the bookmark.
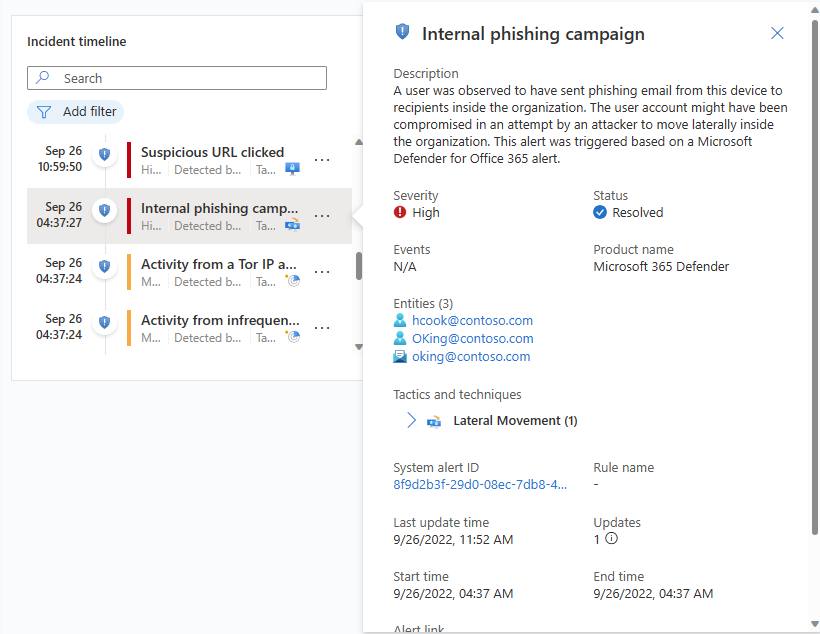
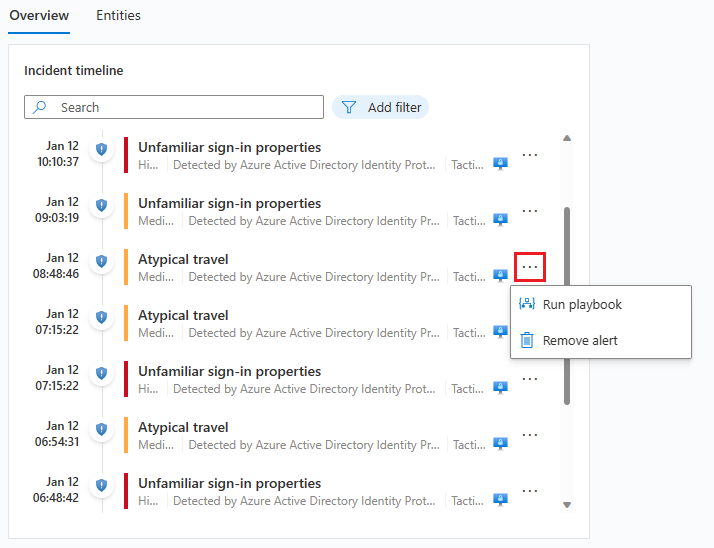
From the incident timeline widget, you can also take the following actions on alerts and bookmarks:
Run a playbook on the alert to take immediate action to mitigate a threat. Sometimes you need to block or isolate a threat before you continue investigating. Learn more about running playbooks on alerts.
Remove an alert from an incident. You can remove alerts that were added to incidents after their creation if you judge them to not be relevant. Learn more about removing alerts from incidents.
Remove a bookmark from an incident, or edit those fields in the bookmark that can be edited (not shown).
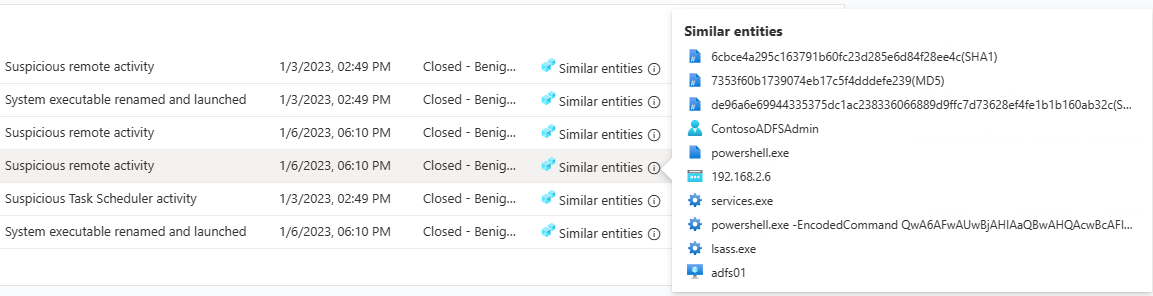
Check for similar incidents in your environment
As a security operations analyst, when investigating an incident you want to pay attention to its larger context.
As with the incident timeline widget, you can hover over any text that's incompletely displayed due to column width to reveal the full text.
The reasons an incident appears in the similar incidents list are displayed in the Similarity reason column. Hover over the info icon to show the common items (entities, rule name, or details).
Get the top insights into your incident
Microsoft Sentinel's security experts have built-in queries that automatically ask the significant questions about the entities in your incident. You can see the top answers in the Top insights widget, visible on the right side of the incident details page. This widget shows a collection of insights based on both machine-learning analysis and the curation of top teams of security experts.
These are some of the same insights that appear on entity pages, specially selected for helping you triage quickly and understand the scope of the threat. For the same reason, insights for all the entities in the incident are presented together to give you a more complete picture of what's happening.
Top insights are subject to change, and might include:
- Actions by account.
- Actions on account.
- UEBA insights.
- Threat indicators related to user.
- Watchlist insights (Preview).
- Anomalously high number of a security event.
- Windows sign-in activity.
- IP address remote connections.
- IP address remote connections with TI match.
Each of these insights (except for the ones relating to watchlists, for now) has a link you can select to open the underlying query in the Logs panel that opens in the incident page. You can then drill down into the query's results.
The time frame for the Top insights widget is from 24 hours before the earliest alert in the incident until the time of the latest alert.
Explore the incident's entities
The Entities widget shows you all the entities that have been identified in the alerts in the incident. These are the objects that played a role in the incident, whether they be users, devices, addresses, files, or any other types.
You can search the list of entities in the entities widget, or filter the list by entity type, to help you find an entity.
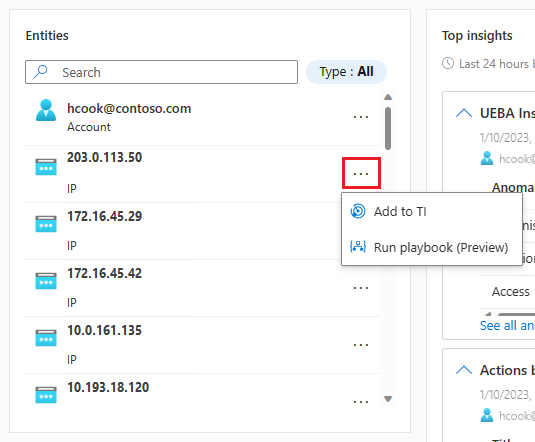
If you already know that a particular entity is a known indicator of compromise, select the three dots on the entity's row and choose Add to TI to add the entity to your threat intelligence. (This option is available for supported entity types.)
If you want to trigger an automatic response sequence for a particular entity, select the three dots and choose Run playbook (Preview). (This option is available for supported entity types.)
Select an entity to see its full details. When you select an entity, you move from the Overview tab to the Entities tab, another part of the incident details page.
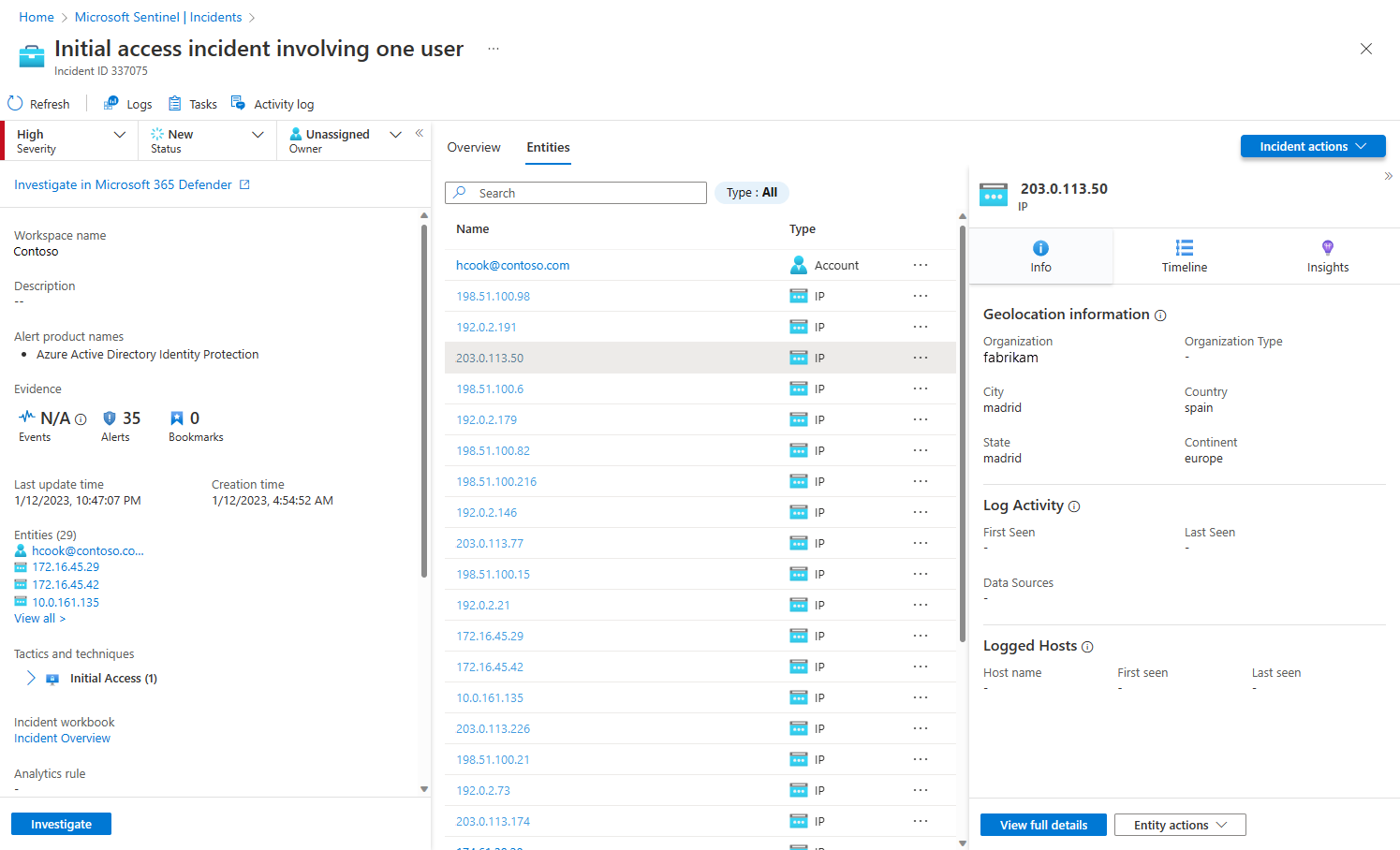
Entities tab
The Entities tab shows a list of all the entities in the incident.
Like the entities widget, this list can also be searched and filtered by entity type. Searches and filters applied in one list won't apply to the other.
Select a row in the list for that entity's information to be displayed in a side panel to the right.
If the entity name appears as a link, selecting the entity's name redirects you to the full entity page, outside the incident investigation page. To display just the side panel without leaving the incident, select the row in the list where the entity appears, but don't select its name.
You can take the same actions here that you can take from the widget on the overview page. Select the three dots in the row of the entity to either run a playbook or add the entity to your threat intelligence.
You can also take these actions by selecting the button next to View full details at the bottom of the side panel. The button reads either Add to TI, Run playbook (Preview), or Entity actions—in which case a menu appears with the other two choices.
The View full details button itself redirects you to the entity's full entity page.
Entities tab side pane
Select an entity on the Entities tab to show a side pane, with the following cards:
Info contains identifying information about the entity. For example, for a user account entity this might be things like the username, domain name, security identifier (SID), organizational information, security information, and more, and for an IP address it would include, for example, geolocation.
Timeline contains a list of the alerts, bookmarks, and anomalies that feature this entity, and also activities the entity has performed, as collected from logs in which the entity appears. All alerts featuring this entity are in this list, whether or not the alerts belong to this incident.
Alerts that aren't part of the incident are displayed differently: the shield icon is grayed out, the severity color band is dotted line instead of a solid line, and there's a button with a plus sign on the right side of the alert's row.
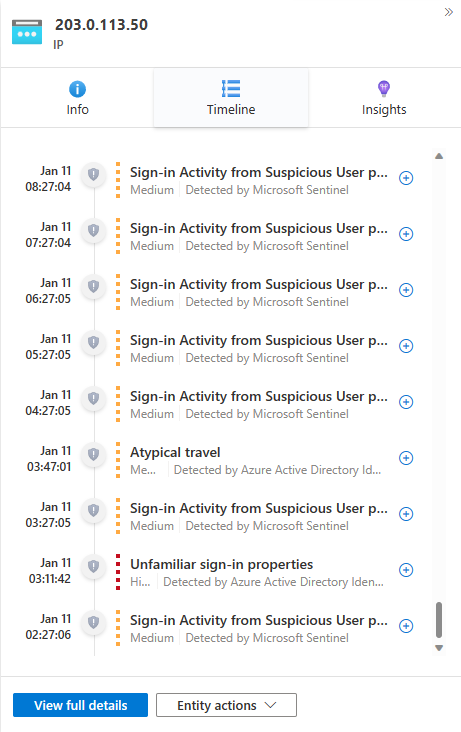
Select the plus sign to add the alert to this incident. When the alert is added to the incident, all the alert's other entities (that weren't already part of the incident) are also added to it. Now you can further expand your investigation by looking at those entities' timelines for related alerts.
This timeline is limited to alerts and activities over the prior seven days. To go further back, pivot to the timeline in the full entity page, whose time frame is customizable.
Insights contains results of queries defined by Microsoft security researchers that provide valuable and contextual security information on entities, based on data from a collection of sources. These insights include the ones from the Top insights widget and many more; they're the same ones that appear on the full entity page, but over a limited time frame: starting from 24 hours before the earliest alert in the incident, and ending with the time of the latest alert.
Most insights contain links which, when selected, open the Logs panel displaying the query that generated the insight along with its results.
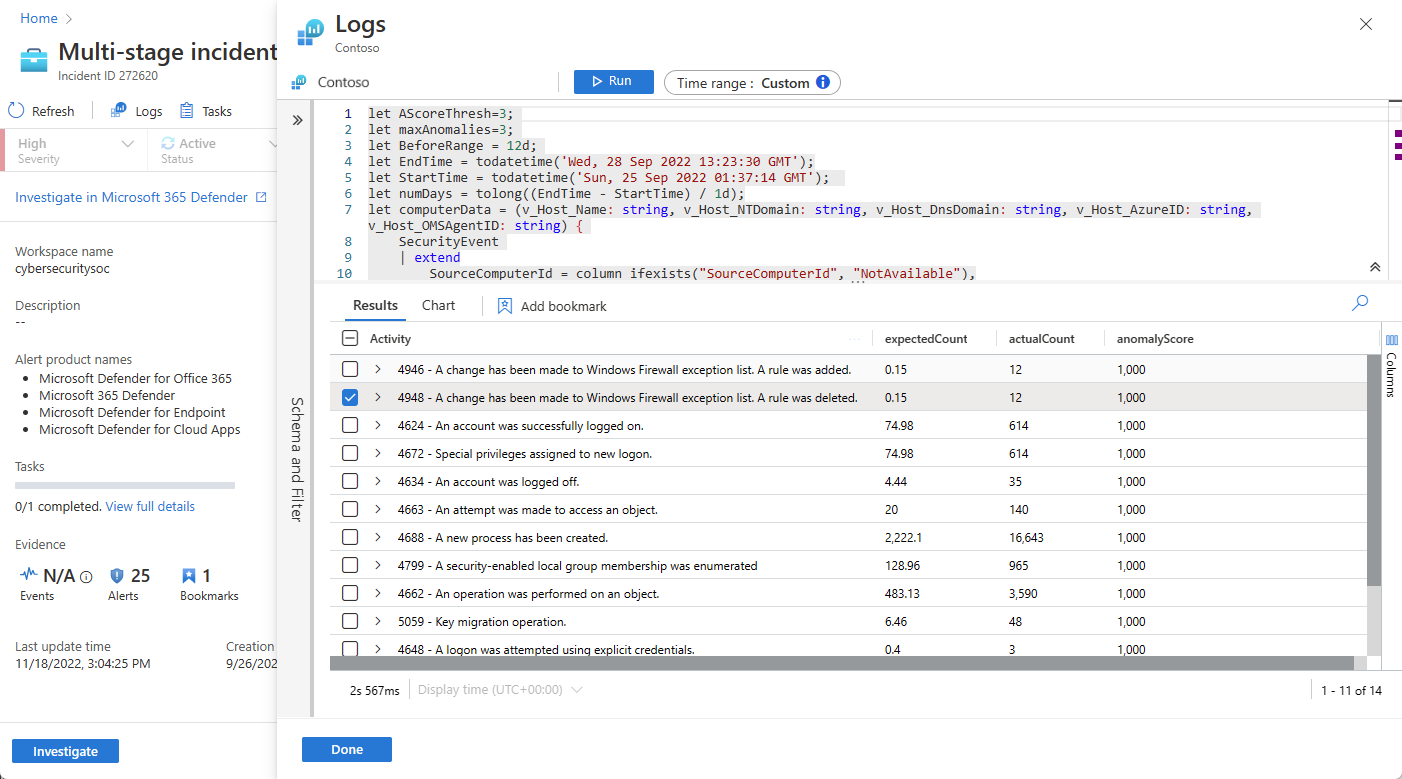
Dive deeper into your data in Logs
From almost anywhere in the investigation experience, you're able to select a link that opens an underlying query in the Logs panel, in the context of the investigation. If you got to the Logs panel from one of these links, the corresponding query appears in the query window, and the query runs automatically and generate the appropriate results for you to explore.
You can also call an empty Logs panel inside the incident details page anytime, if you think of a query you want to try while investigating, while remaining in context. To do this, select Logs at the top of the page.
However you end up on the Logs panel, if you've run a query whose results you want to save, use the following procedure:
Mark the check box next to the row you want to save from among the results. To save all the results, mark the check box at the top of the column.
Save the marked results as a bookmark. You have two options to do this:
Select Add bookmark to the current incident to create a bookmark and add it to the open incident. Follow the bookmark instructions to complete the process. Once completed, the bookmark appears in the incident timeline.
Select Add bookmark to create a bookmark without adding it to any incident. Follow the bookmark instructions to complete the process. You're able to find this bookmark along with any others you've created on the Hunting page, under the Bookmarks tab. From there you can add it to this or any other incident.
After creating the bookmark (or if you choose not to), select Done to close the Logs panel.
For example:
Expand or focus your investigation
Add alerts to your incidents to expand, or broaden the scope of your investigation. Alternatively, remove alerts from your incidents to narrow, or focus the scope of your investigation.
For more information, see Relate alerts to incidents in Microsoft Sentinel in the Azure portal.
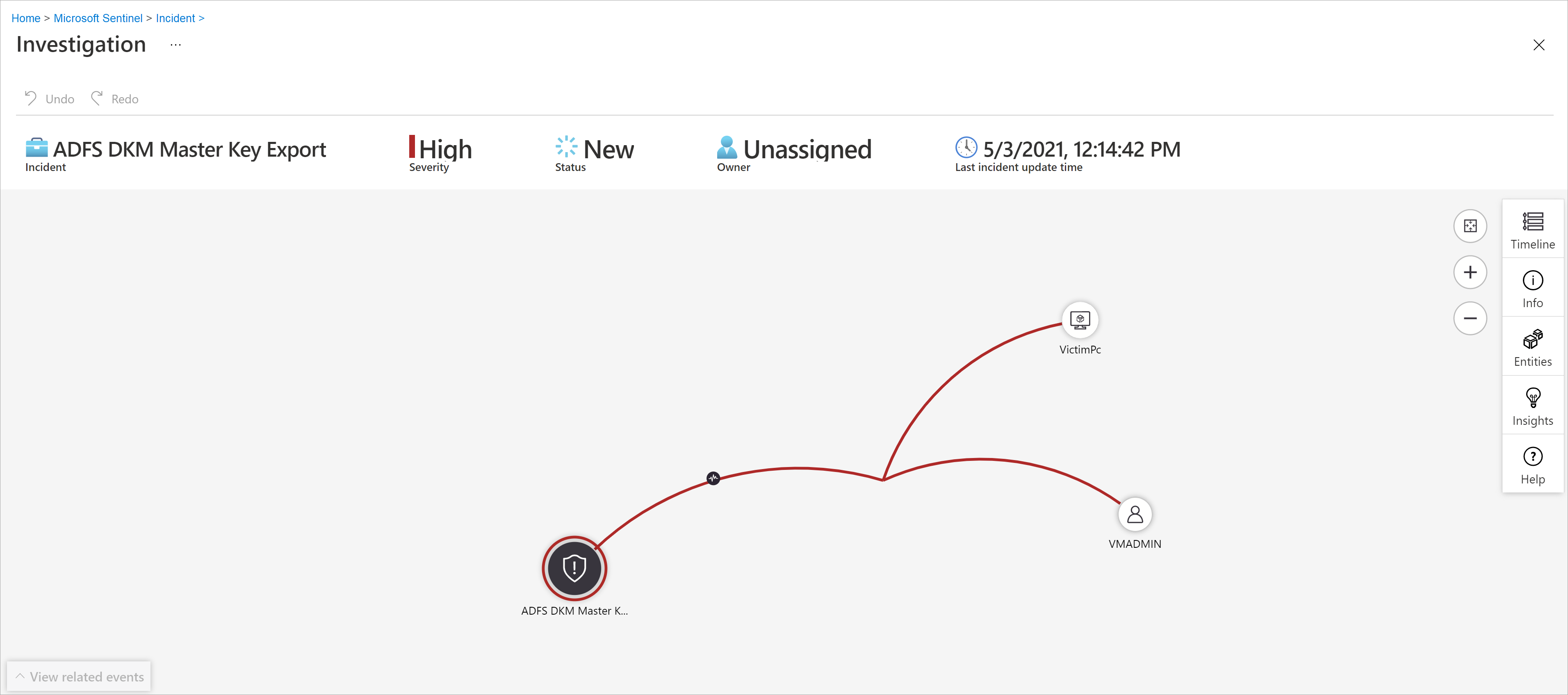
Investigate incidents visually using the investigation graph
If you prefer a visual, graphical representation of alerts, entities, and the connections between them in your investigation, you can accomplish many of the things discussed earlier with the classic investigation graph as well. The downside of the graph is that you end up having to switch contexts a great deal more.
The investigation graph provides you with:
| Investigation content | Description |
|---|---|
| Visual context from raw data | The live, visual graph displays entity relationships extracted automatically from the raw data. This enables you to easily see connections across different data sources. |
| Full investigation scope discovery | Expand your investigation scope using built-in exploration queries to surface the full scope of a breach. |
| Built-in investigation steps | Use predefined exploration options to make sure you're asking the right questions in the face of a threat. |
To use the investigation graph:
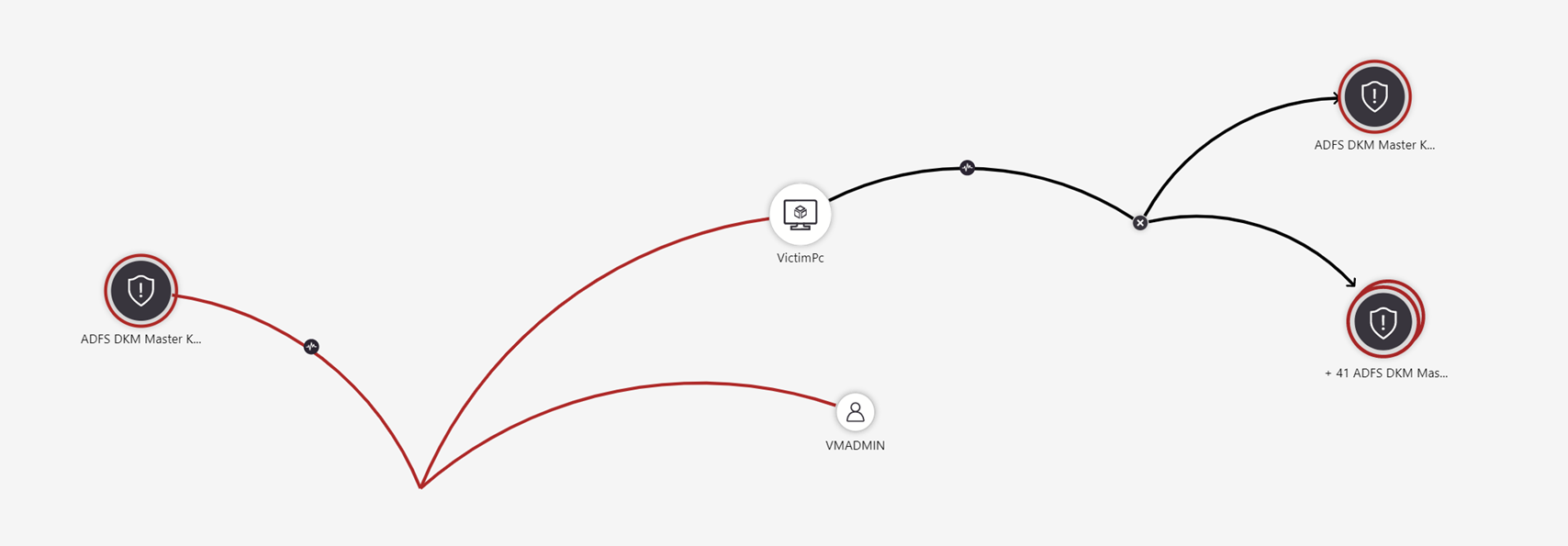
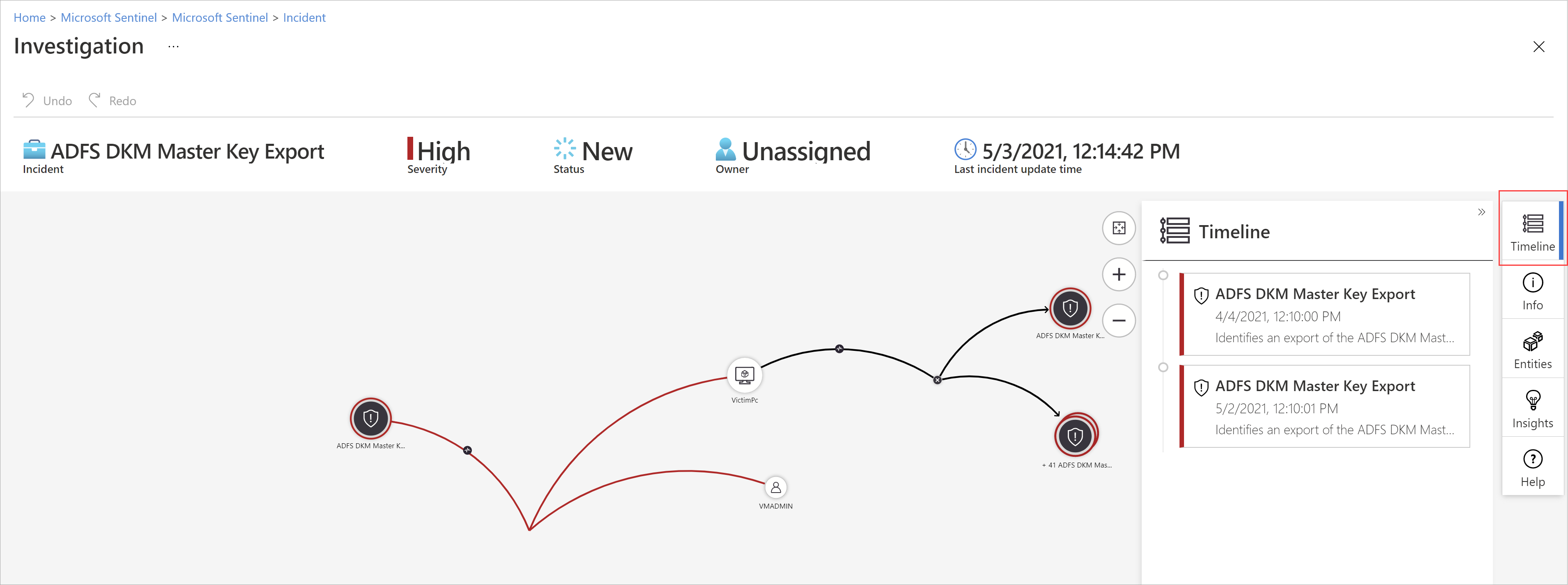
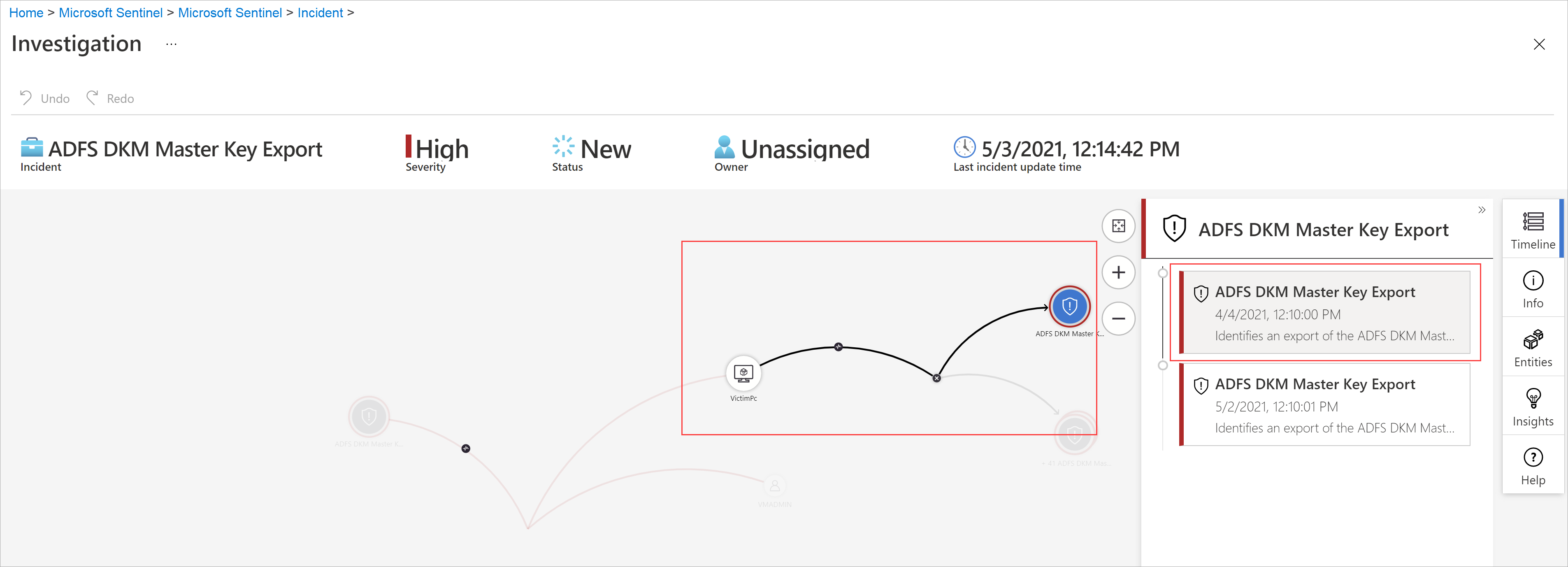
Select an incident, then select Investigate. This takes you to the investigation graph. The graph provides an illustrative map of the entities directly connected to the alert and each resource connected further.
Important
You'll only be able to investigate the incident if the analytics rule or bookmark that generated it contains entity mappings. The investigation graph requires that your original incident includes entities.
The investigation graph currently supports investigation of incidents up to 30 days old.
Select an entity to open the Entities pane so you can review information on that entity.
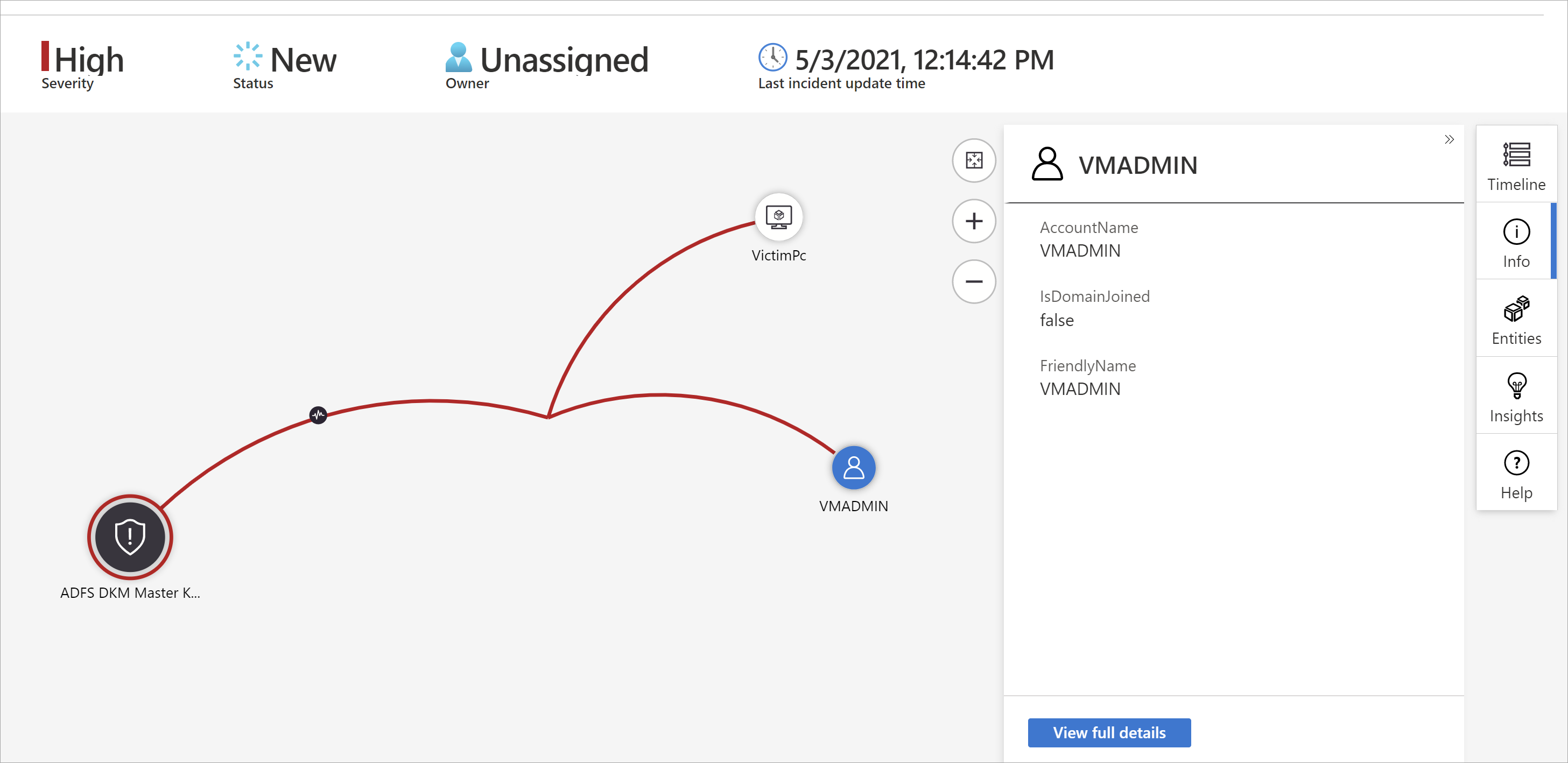
Expand your investigation by hovering over each entity to reveal a list of questions that are designed by our security experts and analysts per entity type to deepen your investigation. We call these options exploration queries.
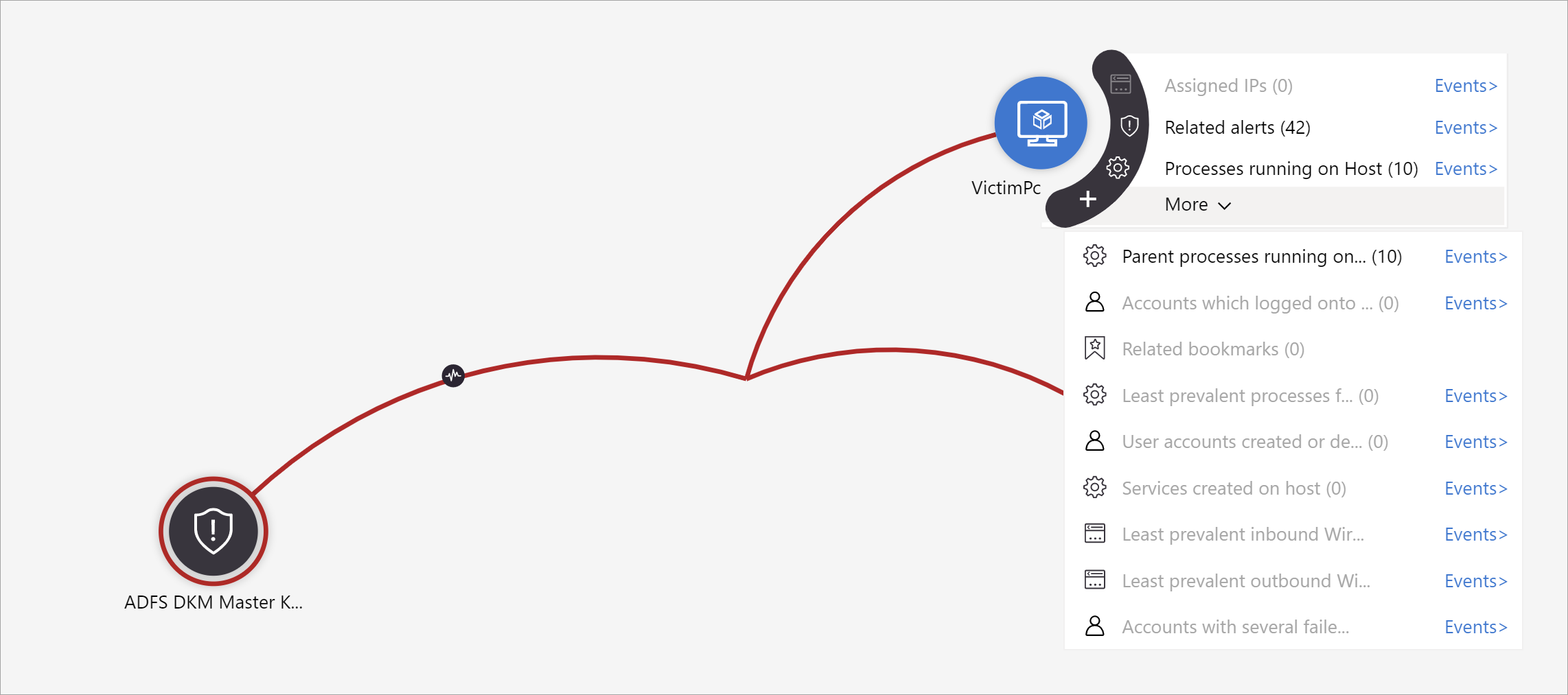
For example, you can request related alerts. If you select an exploration query, the resulting entitles are added back to the graph. In this example, selecting Related alerts returned the following alerts into the graph:
See that the related alerts appear connected to the entity by dotted lines.
For each exploration query, you can select the option to open the raw event results and the query used in Log Analytics, by selecting Events>.
In order to understand the incident, the graph gives you a parallel timeline.
Hover over the timeline to see which things on the graph occurred at what point in time.
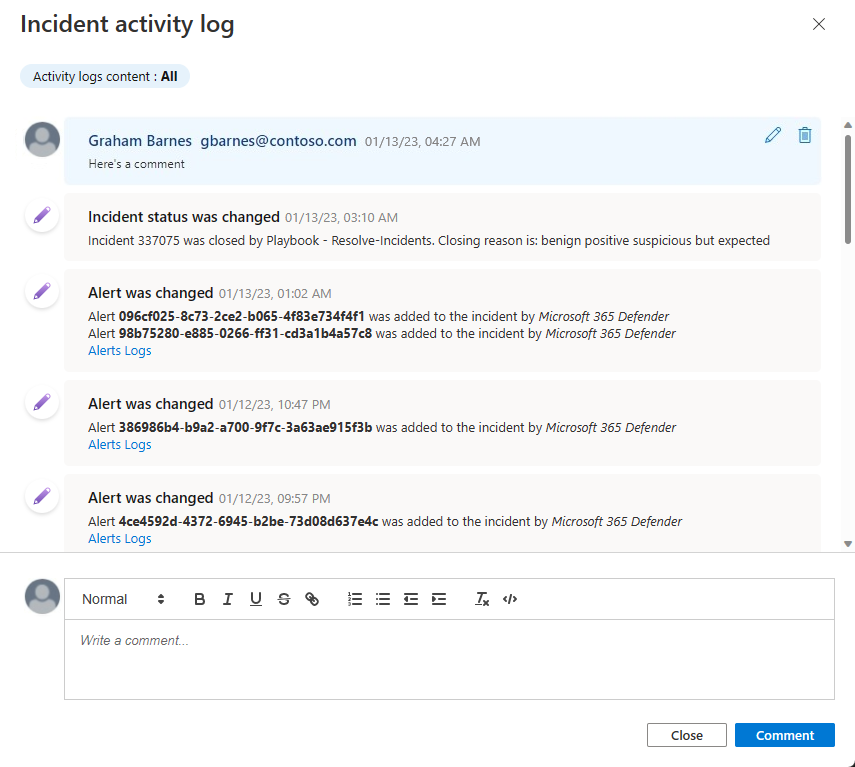
Audit incident events and add comments
When investigating an incident, you want to thoroughly document the steps you take, both to ensure accurate reporting to management and to enable seamless cooperation and collaboration among coworkers. You also want to clearly see records of any actions taken on the incident by others, including by automated processes. Microsoft Sentinel gives you the Activity log, a rich audit and commenting environment, to help you accomplish this.
You can also enrich your incidents automatically with comments. For example, when you run a playbook on an incident that fetches relevant information from external sources (say, checking a file for malware at VirusTotal), you can have the playbook place the external source's response—along with any other information you define—in the incident's comments.
The activity log autorefreshes, even while open, so that you can always see changes in real time. You're also notified of any changes made to the activity log while you have it open.
Prerequisites
Editing: Only the author of a comment has permission to edit it.
Deleting: Only users with the Microsoft Sentinel Contributor role have permission to delete comments. Even the comment's author must have this role in order to delete it.
To view the log of activities and comments, or to add your own comments:
- Select Activity log at the top of the incident details page.
- To filter the log to show either only activities or only comments, select the filter control at the top of the log.
- If you want to add a comment, enter it in the rich text editor at the bottom of the Incident activity log panel.
- Select Comment to submit the comment. Your comment is added at the top of the log.
Supported input for comments
The following table lists limits for supported inputs in comments:
| Type | Description |
|---|---|
| Text | Comments in Microsoft Sentinel support text inputs in plain text, basic HTML, and Markdown. You can also paste copied text, HTML, and Markdown into the comment window. |
| Links | Links must be in the form of HTML anchor tags, and they must have the parameter target="_blank". For example::html<br><a href="https://www.url.com" target="_blank">link text</a><br>If you have playbooks that create comments in incidents, links in those comments must conform to this template as well. |
| Images | Images can't be uploaded directly to comments. Instead, insert links to images in comments to display images inline. Linked images must already be hosted in a publicly accessible location such as Dropbox, OneDrive, Google Drive and so on. |
| Size limit | Per comment: A single comment can contain up to 30,000 characters. Per incident: A single incident can contain up to 100 comments. The size limit of a single incident record in the SecurityIncident table in Log Analytics is 64 KB. If this limit is exceeded, comments (starting with the earliest) are truncated, which may affect the comments that appear in advanced search results. The actual incident records in the incidents database aren't affected. |
Next step
Investigate incidents with UEBA data
Related content
In this article, you learned how to get started investigating incidents using Microsoft Sentinel. For more information, see: