Access the Kubernetes Dashboard in Azure Stack Hub
Note
Only use the Kubernetes Azure Stack Marketplace item to deploy clusters as a proof-of-concept. For supported Kubernetes clusters on Azure Stack, use the AKS engine.
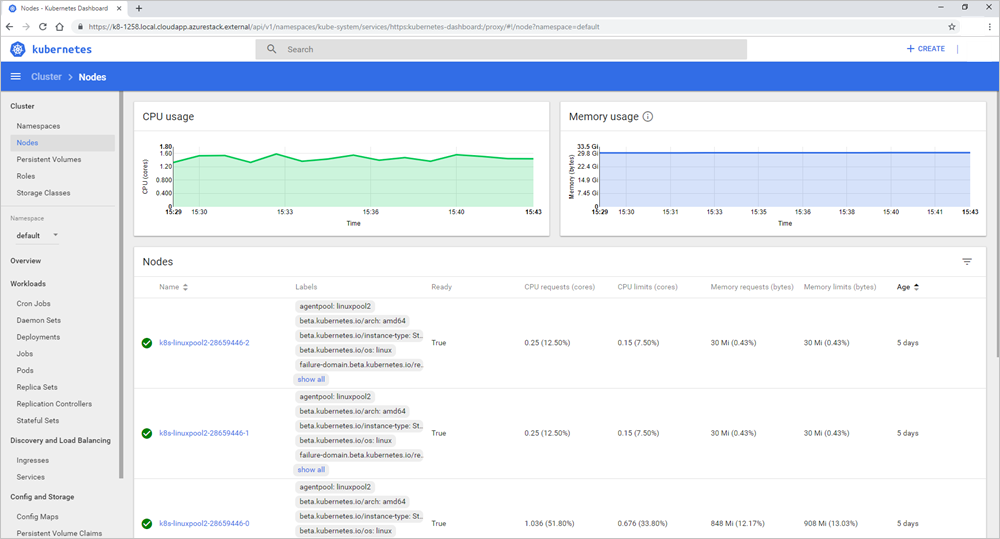
Kubernetes includes a web dashboard that you can use for basic management operations. This dashboard lets you view basic health status and metrics for your applications, create and deploy services, and edit existing applications. This article shows you how to set up the Kubernetes dashboard on Azure Stack Hub.
Prerequisites for Kubernetes Dashboard
- Azure Stack Hub Kubernetes cluster: a Kubernetes cluster deployed to Azure Stack Hub. For more information, see Deploy Kubernetes.
- SSH client: an SSH client to security connect to your control plane node in the cluster. If you use Windows, you can use Putty. You need the private key that you used when you deployed your Kubernetes cluster.
- FTP (PSCP): an FTP client that supports SSH and the SSH File Transfer Protocol to transfer the certificates from the control plane node to your Azure Stack Hub management machine. You can use FileZilla. You need the private key that you used when you deployed your Kubernetes cluster.
Overview of steps to enable dashboard
- Export the Kubernetes certificates from the control plane node in the cluster.
- Import the certificates to your Azure Stack Hub management machine.
- Open the Kubernetes web dashboard.
Export certificate from the master
You can retrieve the URL for the dashboard from the control plane node in your cluster.
Get the public IP address and username for your main cluster from the Azure Stack Hub dashboard. To get this information:
- Sign in to the Azure Stack Hub portal at
https://portal.local.azurestack.external/. - Select All services > All resources. Find the master in your cluster resource group. The master is named
k8s-master-<sequence-of-numbers>.
- Sign in to the Azure Stack Hub portal at
Open the control plane node in the portal. Copy the Public IP address. Select Connect to get your user name in the Login using VM local account box. This is the same user name you set when you created your cluster. Use the public IP address rather than the private IP address listed in the connect blade.
Open an SSH client to connect to the main cluster. If you use Windows, you can use Putty to create the connection. You use the public IP address for the control plane node, the username, and add the private key you used when you created the cluster.
When the terminal connects, type
kubectlto open the Kubernetes command-line client.Run the following command:
kubectl cluster-infoFind the URL for the dashboard. For example:
https://k8-1258.local.cloudapp.azurestack.external/api/v1/namespaces/kube-system/services/https:kubernetes-dashboard:/proxyExtract the self-signed certificate and convert it to the PFX format. Run the following command:
sudo su openssl pkcs12 -export -out /etc/kubernetes/certs/client.pfx -inkey /etc/kubernetes/certs/client.key -in /etc/kubernetes/certs/client.crt -certfile /etc/kubernetes/certs/ca.crtGet the list of secrets in the kube-system namespace. Run the following command:
kubectl -n kube-system get secretsMake note of the kubernetes-dashboard-token-<XXXXX> value.
Get the token and save it. Update the
kubernetes-dashboard-token-<####>with the secret value from the previous step:kubectl -n kube-system describe secret kubernetes-dashboard-token-<####>| awk '$1=="token:"{print $2}'
Import the certificate
Open Filezilla and connect to the control plane node. You need the following information:
- Control plane node public IP
- Username
- Private secret
- Use SFTP - SSH File Transfer Protocol
Copy
/etc/kubernetes/certs/client.pfxand/etc/kubernetes/certs/ca.crtto your Azure Stack Hub management machine.Make a note of the file locations. Update the script with the locations, and then open PowerShell with an elevated prompt. Run the updated script:
Import-Certificate -Filepath "ca.crt" -CertStoreLocation cert:\LocalMachine\Root $pfxpwd = Get-Credential -UserName 'Enter password below' -Message 'Enter password below' Import-PfxCertificate -Filepath "client.pfx" -CertStoreLocation cert:\CurrentUser\My -Password $pfxpwd.Password
Open the Kubernetes dashboard
Disable the pop-up blocker on your web browser.
Point your browser to the URL noted when you ran the command
kubectl cluster-info; for example,https://azurestackdomainnamefork8sdashboard/api/v1/namespaces/kube-system/services/https:kubernetes-dashboard:/proxy.Select the client certificate.
Enter the token.
Reconnect to the bash command line on the control plane node and give permissions to
kubernetes-dashboard. Run the following command:kubectl create clusterrolebinding kubernetes-dashboard --clusterrole=cluster-admin --serviceaccount=kube-system:kubernetes-dashboardThe script gives
kubernetes-dashboardcloud administrator privileges. For more information, see For RBAC-enabled clusters.
You can now use the dashboard. For more information about the Kubernetes dashboard, see Kubernetes Web UI Dashboard.
Troubleshooting
Custom Virtual Networks
If you encounter connectivity issues accessing the Kubernetes dashboard after you deploy Kubernetes to a custom virtual network, ensure that target subnets are linked to the route table and network security group resources that were created by the AKS engine.
Make sure that the network security group rules allow communication between the control plane nodes and the Kubernetes dashboard pod IP. You can validate this permission by using the ping command from a control plane node.