Scan file servers, network shares, and SharePoint with Azure Information Protection Scanner
With GDPR just around the corner (May 2018), organizations are heads down identifying data, creating compliance processes, and hiring additional resources to lead the compliance and reporting required by GDPR.
In a previous post I reviewed GDPR as well as the technologies and services Microsoft offers to assist with discovery, managing, protecting, and reporting on data.
For this post I’ll expand on the topic of scanning file servers and SharePoint servers using a the Azure Information Protection Scanner or AIP Scanner.
Scanning SharePoint Server and File Shares
Azure Information Protection includes a scanning tool called the Azure Information Protection scanner or AIP scanner. The AIP scanner is used to comb through file shares and SharePoint and identity and/or classify + protect data.
The scanner runs as a service on Windows Server and lets you discover, classify, and protect files on the following data stores:
Local folders on the Windows Server computer that runs the scanner.
UNC paths for network shares that use the Common Internet File System (CIFS) protocol.
Sites and libraries for SharePoint Server 2016 and SharePoint Server 2013.
Source: https://docs.microsoft.com/en-us/information-protection/deploy-use/deploy-aip-scanner
Once the AIP scanner is deployed, use it to report on information you’re looking for and when discovery is complete, run the AIP scanner and apply classification with or without protection across those files.
The classification labels and encryption policies come from the Azure Information Protection service in Azure. Labels may be defined with or without encryption. At a minimum I recommend all information at least be classified. To learn more about creating classification labels using Azure Information Protection please visit: https://docs.microsoft.com/en-us/information-protection/understand-explore/what-is-information-protection
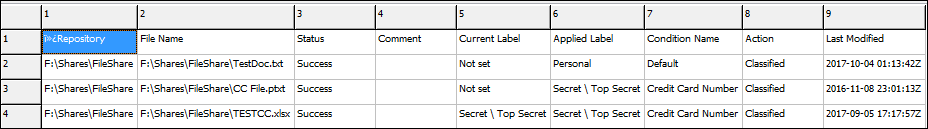
I won’t go through the details of installation process as it’s clearly documented in the link I provide below. However, the output below is from a scan I completed using the AIP scanner against a few sample files. The AIP scanner will look for specific information based on the AIP policies that are configured (e.g. credit card info, passport numbers, etc.).
For more information about the Azure Information Protection scanner please visit: /en-us/information-protection/deploy-use/deploy-aip-scanner
Automation
To help with automating the AIP Scanner process I created a script to walk through each option. Feel free to utilize, however keep in mind when new AIP scanner versions are released you may need to update the script to accommodate new features. I also make no guarantees so use at your own risk.
#AIP Scanner Script
#Created by Courtenay Bernier
$AIPScannerLogFiles = $env:LOCALAPPDATA + '\Microsoft\MSIP\Scanner\Reports'
#AIP scanner config
Write-Host ""
Write-Host 'AIP scanner configuration'
Write-Host ""
$ScanMode = Read-Host -Prompt 'ScanMode: Enforce | Discover'
$Type = Read-Host -Prompt 'ScanType: Incremental | Full'
$ReportLevel = Read-Host -Prompt 'ReportLevel: Off | Debug | Info | Error'
$Schedule = Read-Host -Prompt 'Scanner Runtime Schedule: OneTime | Continuous | Never'
$JustificationMessage = Read-Host -Prompt 'JustificationMessage: Free Text or leave blank'
Write-Host "The AIPScannerConfiguration options selected are: '$ScanMode', '$Type', $ReportLevel, $Schedule, $JustificationMessage"
Set-AIPScannerConfiguration -ScanMode $ScanMode -Type $Type -ReportLevel $ReportLevel -Schedule $Schedule -JustificationMessage $JustificationMessage
Write-Host ""
Write-Host 'This is the AIP Scanner Configuration set:'
Get-AIPScannerConfiguration
#AIP scanner repository
Write-Host ""
Write-Host 'AIP scanner repository'
Write-Host ""
$OverrideLabel = Read-Host -Prompt 'OverrideLabel: On | Off'
$SetDefaultlabel = Read-Host -Prompt 'SetDefaultLabel: UsePolicyDefault | On | Off'
$PreserveFileDetails = Read-Host -Prompt 'PreserveFileDetails: On | Off'
$DefaultOwner = Read-Host -Prompt 'Specify the default owner by: email address or leave blank'
do {$DLID = Read-Host -Prompt 'Add a default label ID by GUID? Yes or No' }
until ('yes','no' -contains $DLID)
if ($DLID -eq 'yes')
{
$DefaultLabelID = Read-Host -Prompt 'specify the label GUID found in the AIP label policy'
}
elseif ($DLID -eq 'no')
{
Write-Host ""
write-host "No default label ID was added"
Write-Host ""
}
#add file location
$Path = Read-Host -Prompt 'Fileshare or SPS Path: e.g. F:\Shares\FileShare or \\network\path or https://sp2013/Shared Documents'
Add-AIPScannerRepository $Path
Write-Host ""
#ask to add for more file locations
do {$answer = Read-Host -Prompt 'Would you like to add another file location? Yes or No'
if ($answer -eq 'yes')
{
$Path = Read-Host -Prompt 'Fileshare or SPS Path: e.g. F:\Shares\FileShare or \\network\path or https://sp2013/Shared Documents'
#add file location
Add-AIPScannerRepository $Path
Write-Host ""
}
else
{
Write-Host ""
write-host "No additional paths were added"
Write-Host ""
Write-Host "To remove repositories: use Remove-AIPScannerRepository share/sps path"
Write-Host ""
Get-AIPScannerRepository
Write-Host ""
}
}
Until ($answer -eq 'no')
#set AIP scanner repository
Write-Host ""
Write-Host 'Setting scanner repository config:'
Set-AIPScannerRepository -OverrideLabel $OverrideLabel -PreserveFileDetails $PreserveFileDetails -DefaultOwner $DefaultOwner -Path $Path -DefaultLabelId $DefaultLabelID -SetDefaultLabel $SetDefaultLabel
#show file location(s)
Get-AIPScannerRepository
Write-Host ""
#start AIP scanner service or abort
do {$answer = Read-Host -Prompt 'Are you ready to start the AIP Scanner Service? Yes or No' }
until ('yes','no' -contains $answer)
if ($answer -eq 'yes')
{
write-host "Starting AIP Scanner Service for ($ScanMode)"
start-Service 'Azure Information Protection Scanner'
Write-Host ""
#Show last AIP events
Write-Host "waiting for eventlogs to populate"
Start-Sleep -s 15
Get-EventLog -Newest 4 -LogName 'Azure Information Protection' | Format-List -Property *
Write-Host ""
#Open Scanner Report Folder
explorer $AIPScannerLogFiles
Write-Host ""
}
elseif ($answer -eq 'no')
{
Write-Host ""
write-host "Canceling AIP Scan"
Write-Host ""
Write-Host "To remove repositories: use Remove-AIPScannerRepository share/sps path"
Write-Host ""
}