Enable the Microsoft Defender Threat Intelligence data connector
Bring public, open-source and high-fidelity indicators of compromise (IOCs) generated by Microsoft Defender Threat Intelligence into your Microsoft Sentinel workspace with the Defender Threat Intelligence data connectors. With a simple one-click setup, use the threat intelligence from the standard and premium Defender Threat Intelligence data connectors to monitor, alert, and hunt.
Microsoft Sentinel is generally available within Microsoft's unified security operations platform in the Microsoft Defender portal. For preview, Microsoft Sentinel is available in the Defender portal without Microsoft Defender XDR or an E5 license. For more information, see Microsoft Sentinel in the Microsoft Defender portal.
For more information about the benefits of the standard and premium Defender Threat Intelligence data connectors, see Understand threat intelligence.
Prerequisites
- To install, update, and delete standalone content or solutions in the Content hub, you need the Microsoft Sentinel Contributor role at the resource group level.
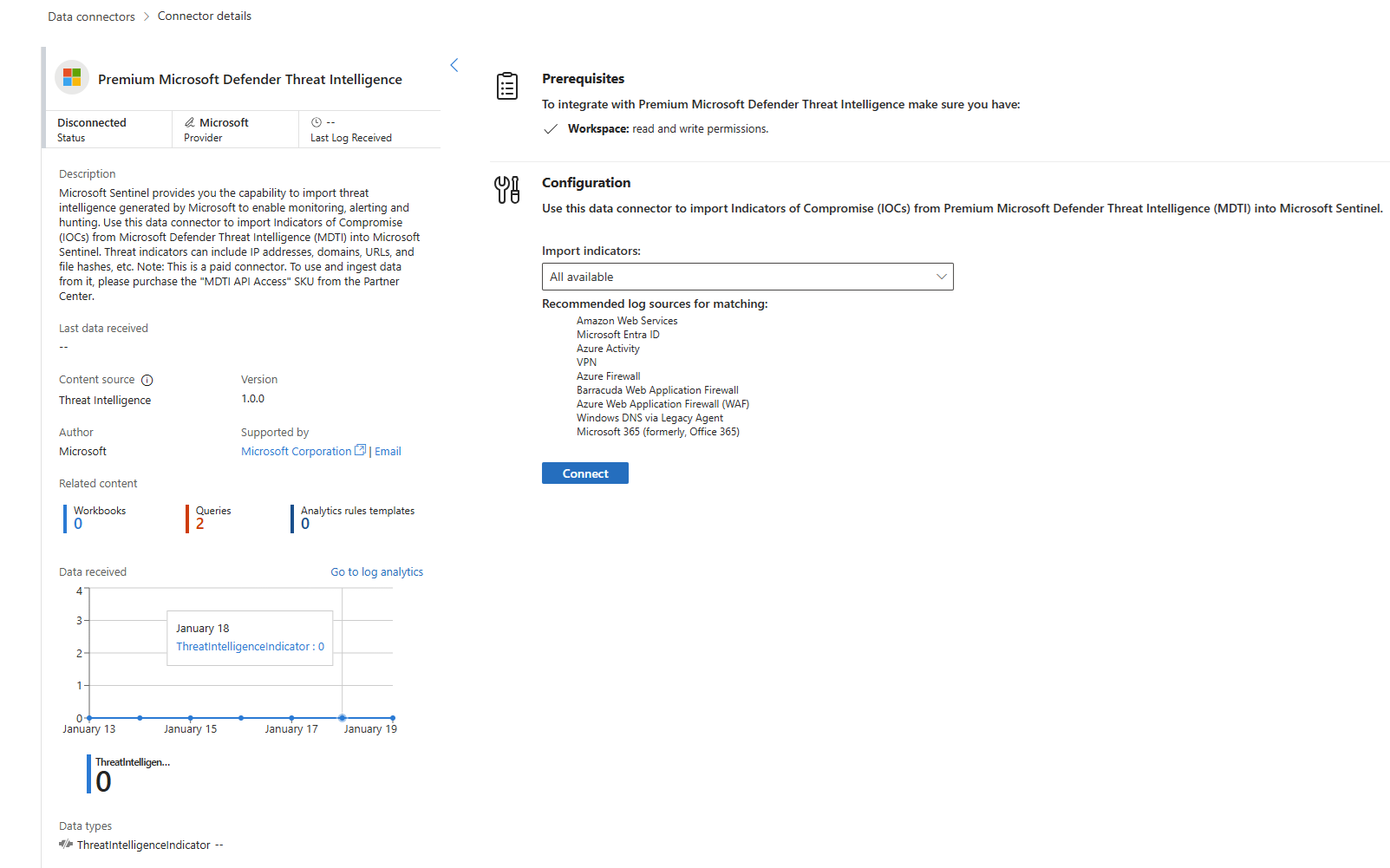
- To configure these data connectors, you must have read and write permissions to the Microsoft Sentinel workspace.
- To access threat intelligence from the premium version of the Defender Threat Intelligence data connector, contact sales to purchase the MDTI API Access SKU.
For more information on how to get a premium license and explore all the differences between the standard and premium versions, see Explore Defender Threat Intelligence licenses.
Install the threat intelligence solution in Microsoft Sentinel
To import threat intelligence into Microsoft Sentinel from standard and premium Defender Threat Intelligence, follow these steps:
For Microsoft Sentinel in the Azure portal, under Content management, select Content hub.
For Microsoft Sentinel in the Defender portal, select Microsoft Sentinel > Content management > Content hub.
Find and select the Threat Intelligence solution.
Select the
 Install/Update button.
Install/Update button.
For more information about how to manage the solution components, see Discover and deploy out-of-the-box content.
Enable the Defender Threat Intelligence data connector
For Microsoft Sentinel in the Azure portal, under Configuration, select Data connectors.
For Microsoft Sentinel in the Defender portal, select Microsoft Sentinel > Configuration > Data connectors.
Find and select either the standard or premium Defender Threat Intelligence data connector. Select Open connector page button.
Enable the feed by selecting Connect.
When Defender Threat Intelligence starts populating the Microsoft Sentinel workspace, the connector status displays Connected.
At this point, the ingested intelligence is now available for use in the TI map... analytics rules. For more information, see Use threat indicators in analytics rules.
Find the new intelligence in the management interface or directly in Logs by querying the ThreatIntelligenceIndicator table. For more information, see Work with threat intelligence.
Related content
In this article, you learned how to connect Microsoft Sentinel to the Microsoft threat intelligence feed with the Defender Threat Intelligence data connector. To learn more about Defender Threat Intelligence, see the following articles:
- Learn about What is Defender Threat Intelligence?.
- Get started with the Defender Threat Intelligence portal.
- Use Defender Threat Intelligence in analytics by using matching analytics to detect threats.