Data encryption for Azure Database for MySQL - Flexible Server by using the Azure portal
This tutorial shows you how to set up and manage data encryption for Azure Database for MySQL Flexible Server.
In this tutorial, you learn how to:
Set data encryption for Azure Database for MySQL Flexible Server.
Configure data encryption for restoration.
Configure data encryption for replica servers.
Note
Azure key vault access configuration now supports two types of permission models - Azure role-based access control and Vault access policy. The tutorial describes configuring data encryption for Azure Database for MySQL Flexible Server using Vault access policy. However, you can choose to use Azure RBAC as permission model to grant access to Azure Key Vault. To do so, you need any built-in or custom role that has below three permissions and assign it through "role assignments" using Access control (IAM) tab in the keyvault: a) KeyVault/vaults/keys/wrap/action b) KeyVault/vaults/keys/unwrap/action c) KeyVault/vaults/keys/read. For Azure key vault managed HSM, you will also need to assign the "Managed HSM Crypto Service Encryption User" role assignment in RBAC.
Prerequisites
An Azure account with an active subscription.
If you don't have an Azure subscription, create an Azure free account before you begin.
Note
With an Azure free account, you can now try Azure Database for MySQL Flexible Server for free for 12 months. For more information, see Use an Azure free account to try Azure Database for MySQL - Flexible Server for free.
Set the proper permissions for key operations
In Key Vault, select Access policies, and then select Create.
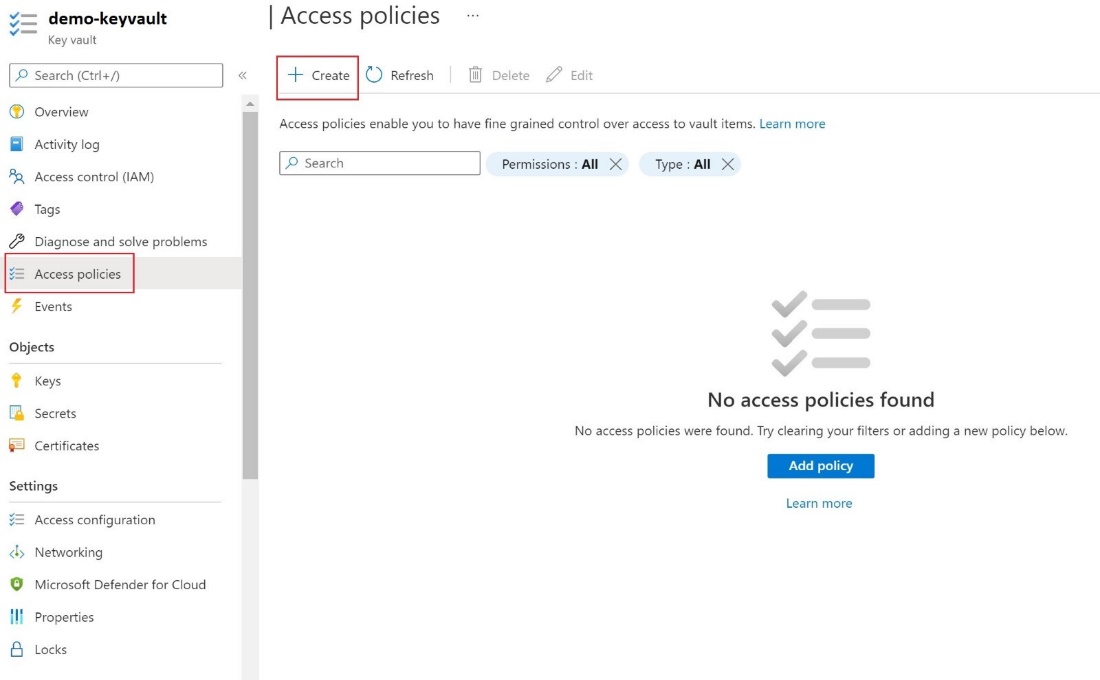
On the Permissions tab, select the following Key permissions - Get , List , Wrap Key , Unwrap Key.
On the Principal tab, select the User-assigned Managed Identity.
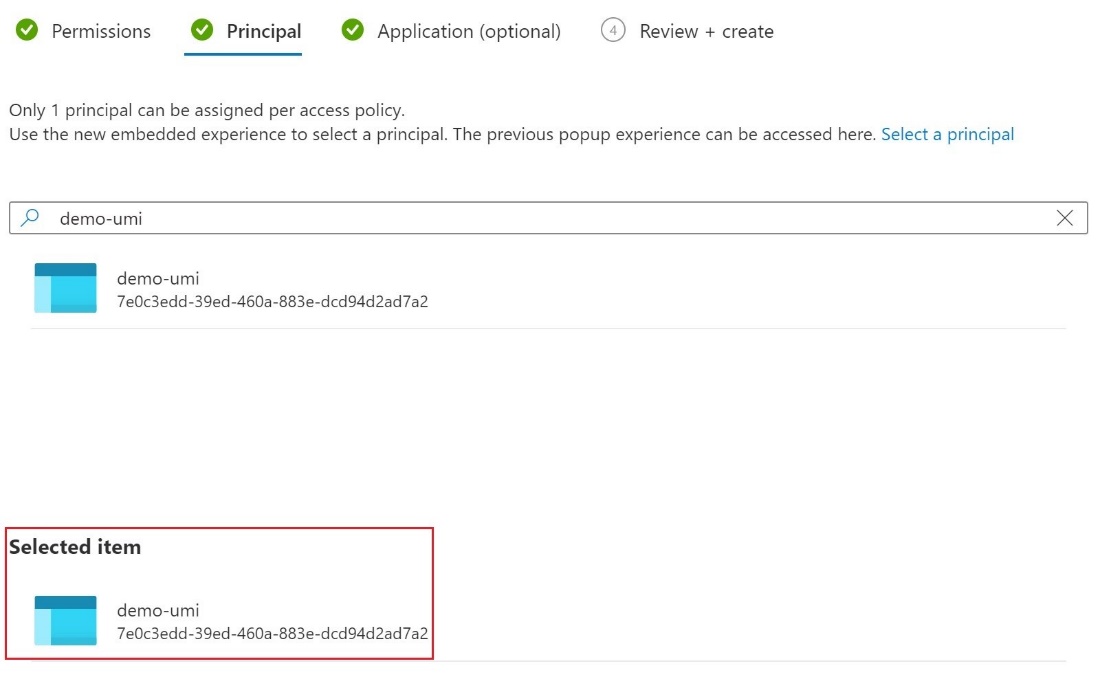
Select Create.
Configure customer managed key
To set up the customer managed key, perform the following steps.
In the portal, navigate to your Azure Database for MySQL Flexible Server instance, and then, under Security , select Data encryption.
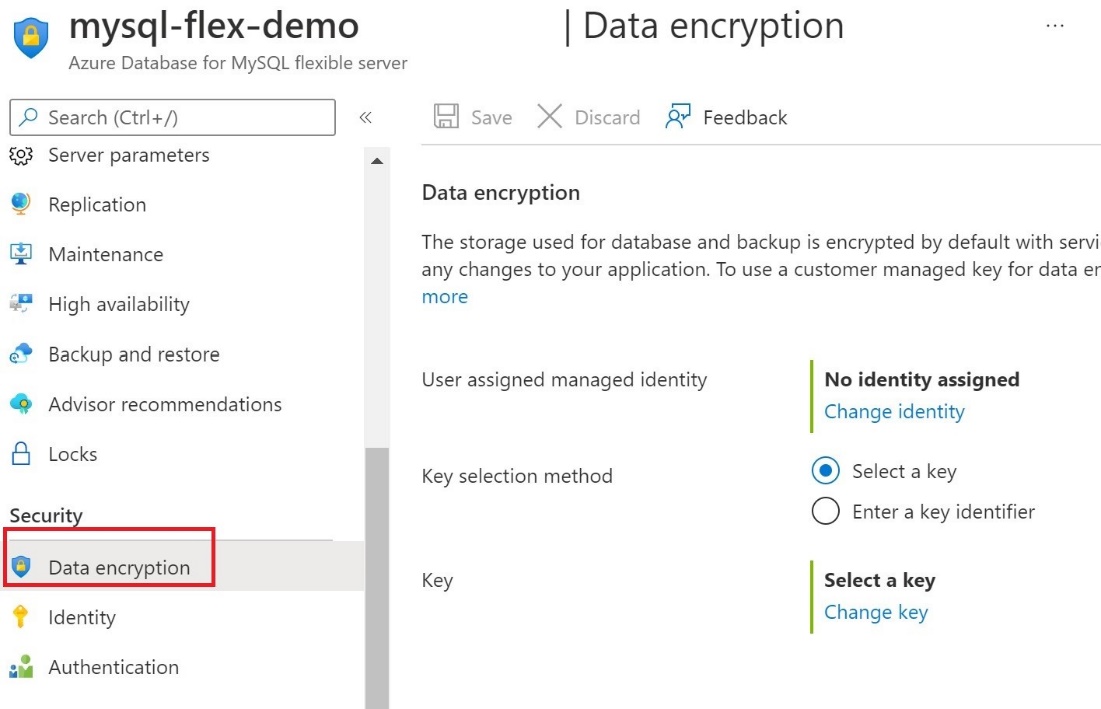
On the Data encryption page, under No identity assigned , select Change identity ,
In the Select user assigned* managed identity dialog box, select the demo-umi identity, and then select Add**.
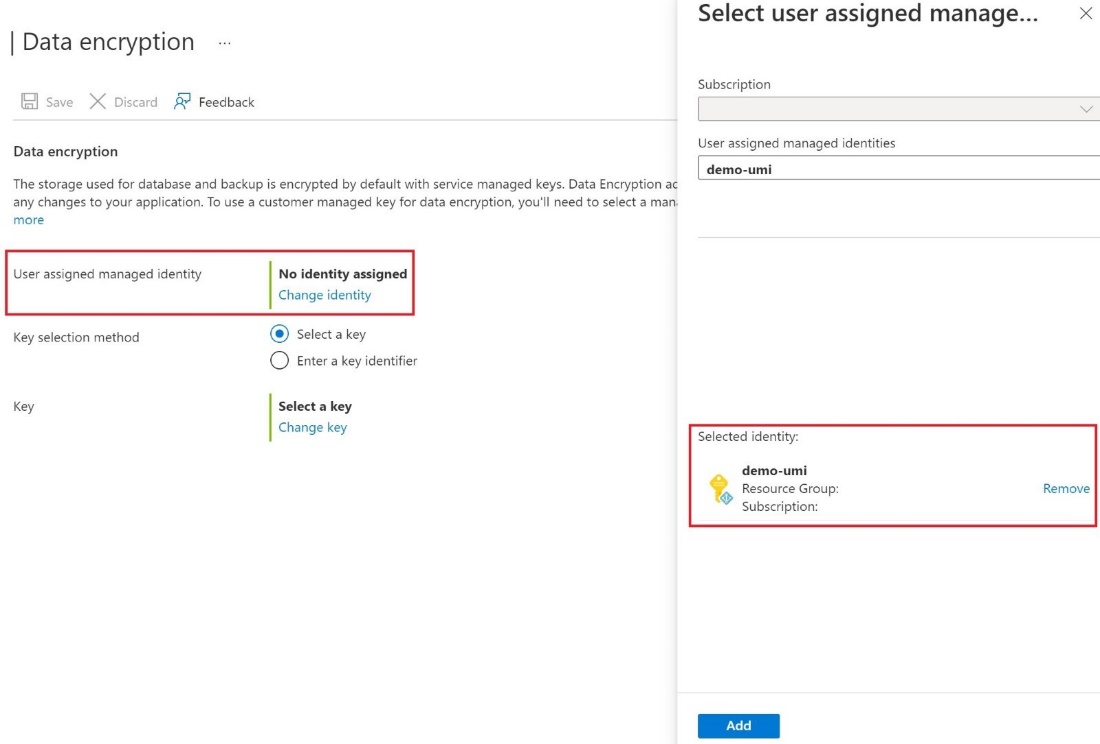
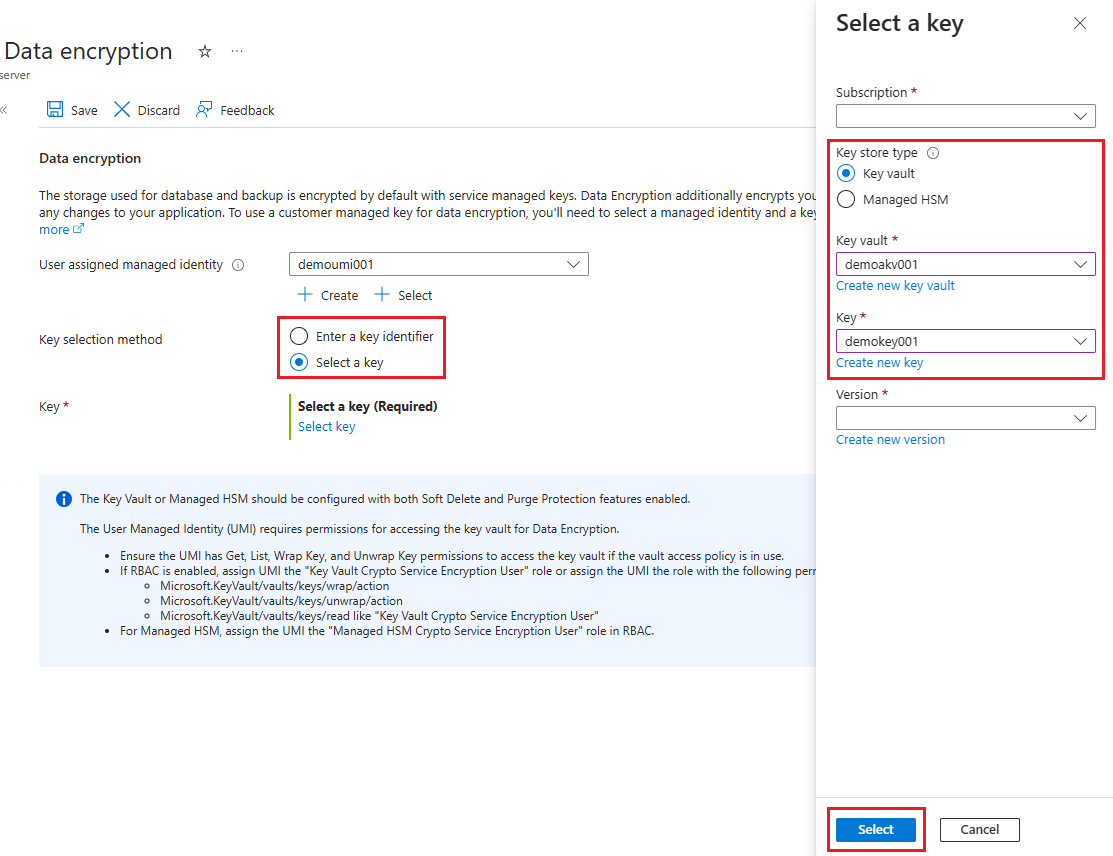
To the right of Key selection method , either Select a key and specify a key vault and key pair, or select Enter a key identifier.
Select Save.
Use Data encryption for restore
To use data encryption as part of a restore operation, perform the following steps.
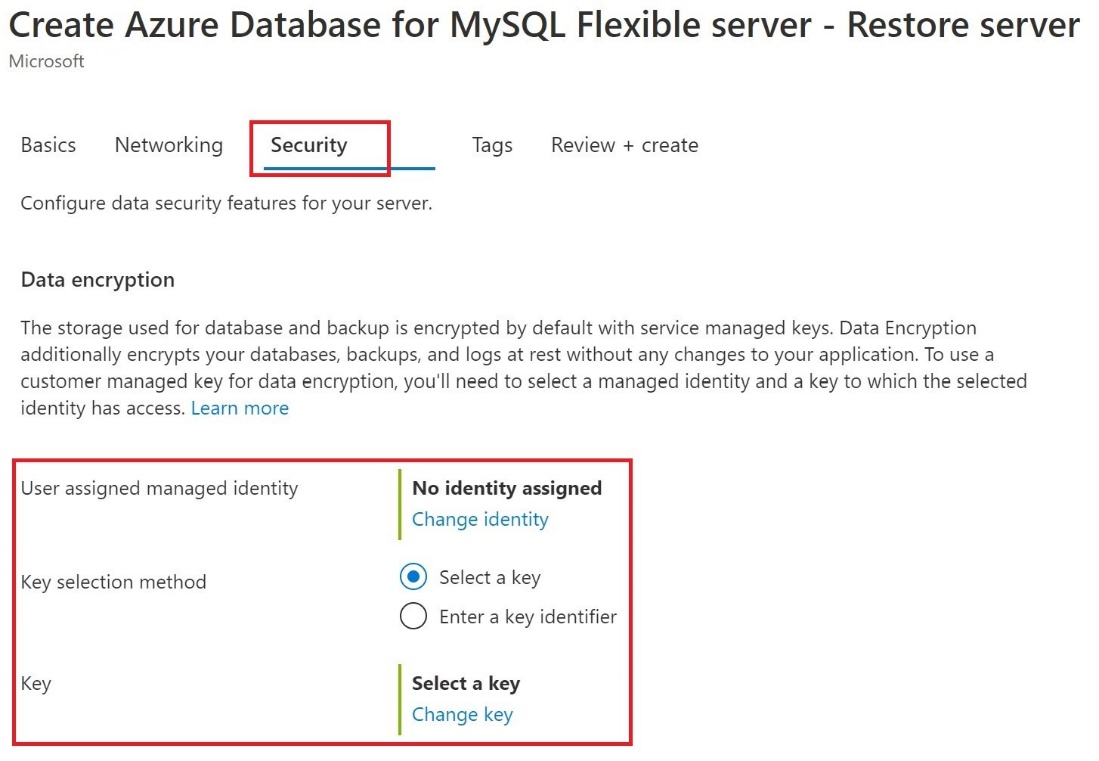
In the Azure portal, on the navigate Overview page for your server, select Restore.
On the Security tab, you specify the identity and the key.
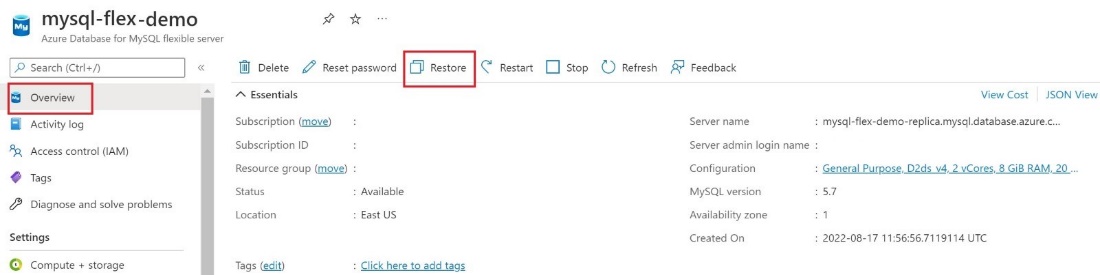
Select Change identity and select the User assigned managed identity and select Add To select the Key , you can either select a key vault and key pair or enter a key identifier
Use Data encryption for replica servers
After your Azure Database for MySQL Flexible Server instance is encrypted with a customer's managed key stored in Key Vault, any newly created copy of the server is also encrypted.
To configuration replication, under Settings , select Replication , and then select Add replica.
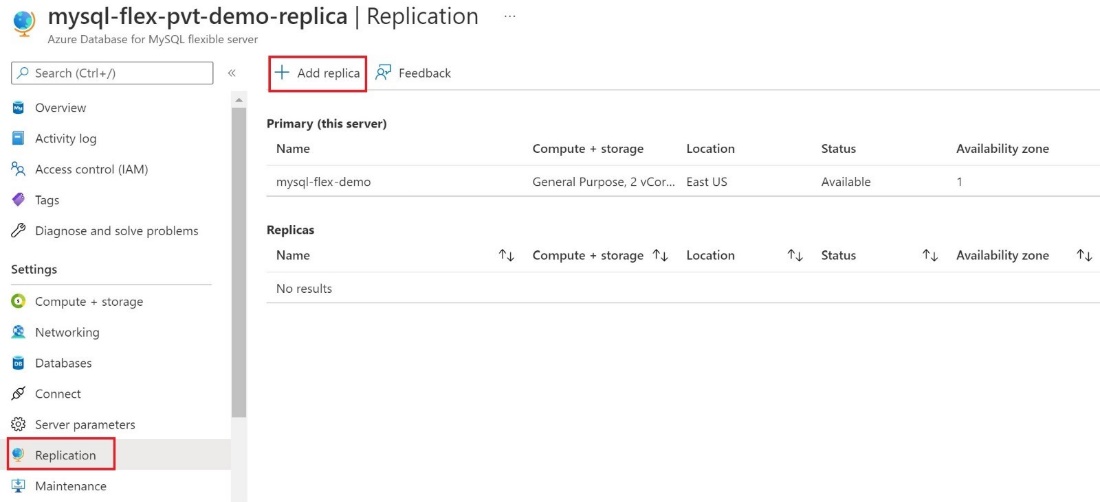
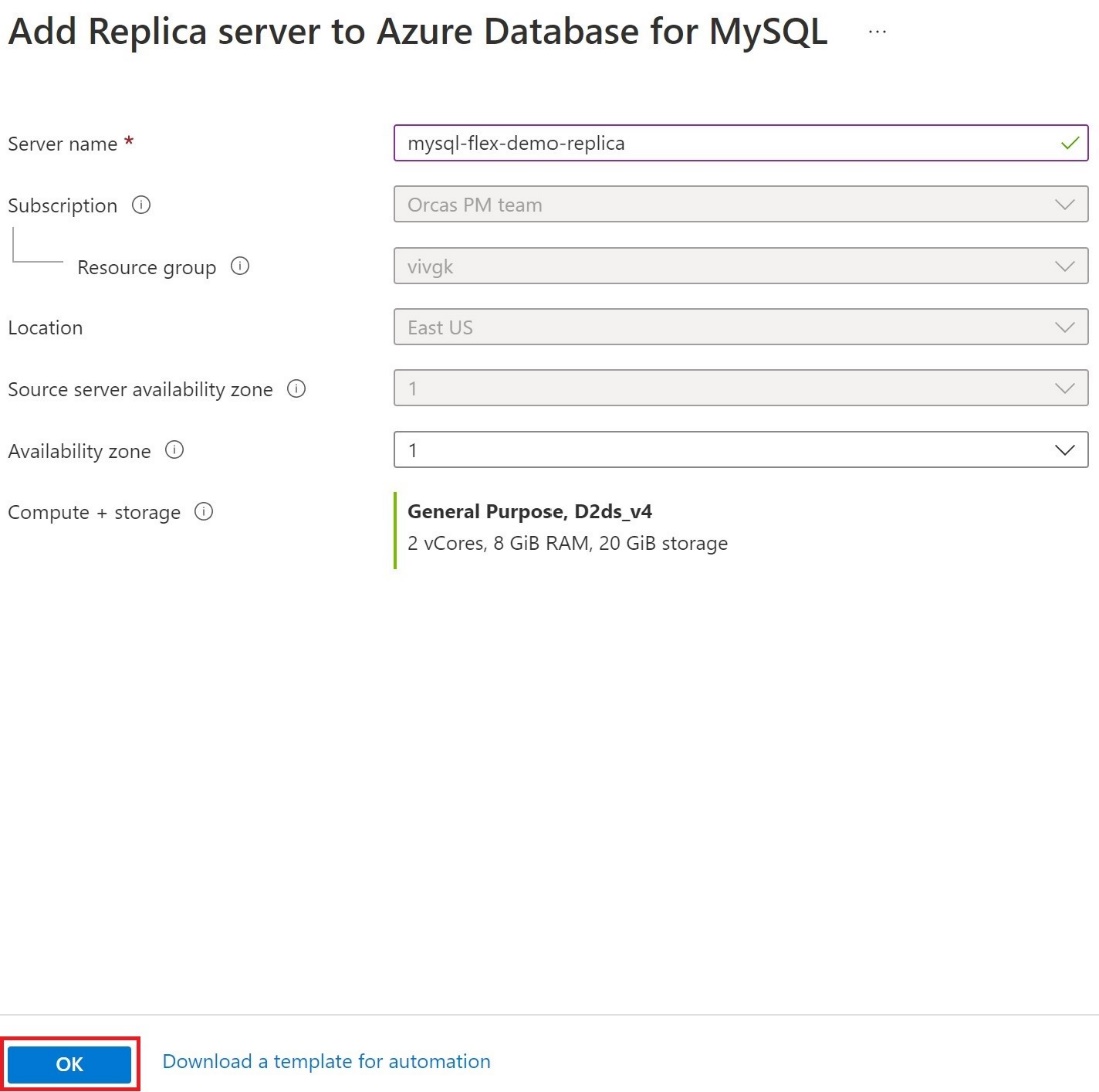
In the Add Replica server to Azure Database for MySQL dialog box, select the appropriate Compute + storage option, and then select OK.
Important
When trying to encrypt Azure Database for MySQL Flexible Server with a customer managed key that already has a replica(s), we recommend configuring the replica(s) as well by adding the managed identity and key.