Implementación de una aplicación web Django de Python con PostgreSQL en Azure
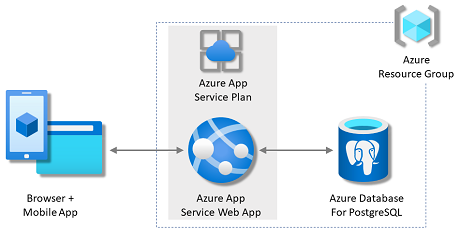
En este tutorial, implementará una aplicación web de Python controlada por datos (Django) en Azure App Service con el servicio de base de datos relacional Azure Database for PostgreSQL. Azure App Service admite Python en un entorno de servidor Linux. Si lo desea, consulte el tutorial de Flask o el tutorial de FastAPI en su lugar.
En este tutorial, aprenderá a:
- Cree una arquitectura de App Service, PostgreSQL y Redis Cache segura de manera predeterminada.
- Asegure los secretos de conexión utilizando una identidad administrada y referencias de Key Vault.
- Implemente una aplicación de muestra de Python en App Service desde un repositorio de GitHub.
- Acceda a las cadenas de conexión de App Service y a la configuración de la aplicación en el código de la aplicación.
- Realice actualizaciones y vuelva a implementar el código de la aplicación.
- Genere el esquema de la base de datos mediante la ejecución de migraciones de bases de datos.
- Transmitir registros de diagnóstico desde Azure.
- Administrar la aplicación en Azure Portal.
- Aprovisione la misma arquitectura e impleméntela usando Azure Developer CLI.
- Optimice su flujo de trabajo de desarrollo con GitHub Codespaces y GitHub Copilot.
Requisitos previos
- Una cuenta de Azure con una suscripción activa. Si no tiene una cuenta de Azure, puede crearla gratis.
- Una cuenta de GitHub. También puede obtener una gratis.
- Conocimientos de Python con el desarrollo de Django.
- (Opcional) Para probar GitHub Copilot, una cuenta de GitHub Copilot. Hay disponible una evaluación gratuita de 30 días.
- Una cuenta de Azure con una suscripción activa. Si no tiene una cuenta de Azure, puede crearla gratis.
- Azure Developer CLI instalado. Puede seguir los pasos con Azure Cloud Shell porque ya tiene instalado Azure Developer CLI.
- Conocimientos de Python con el desarrollo de Django.
- (Opcional) Para probar GitHub Copilot, una cuenta de GitHub Copilot. Hay disponible una evaluación gratuita de 30 días.
Ir al final
Si solo quiere ver la aplicación de ejemplo en este tutorial que se ejecuta en Azure, solo tiene que ejecutar los siguientes comandos en Azure Cloud Shell y seguir el aviso:
mkdir msdocs-django-postgresql-sample-app
cd msdocs-django-postgresql-sample-app
azd init --template msdocs-django-postgresql-sample-app
azd up
1. Ejecución del ejemplo
En primer lugar, configurará una aplicación controlada por datos de ejemplo como punto inicial. Para lograr mayor comodidad, el repositorio de ejemplo incluye una configuración de contenedor de desarrollo. El contenedor de desarrollo tiene todo lo que necesita para desarrollar una aplicación, incluida la base de datos, la caché y todas las variables de entorno necesarias para la aplicación de ejemplo. El contenedor de desarrollo puede ejecutarse en un codespace de GitHub, lo que significa que puede ejecutar el ejemplo en cualquier equipo con un explorador web.
Nota:
Si sigue este tutorial con su propia aplicación, examine la descripción del archivo requirements.txt en el archivo README.md para ver los paquetes que necesitará.
Paso 1: En una nueva ventana del navegador:
- Inicie sesión en su cuenta de GitHub.
- Vaya a https://github.com/Azure-Samples/msdocs-django-postgresql-sample-app/fork.
- Anule la selección de Copiar solo la rama principal. Quiere todas las ramas.
- Seleccione Crear bifurcación.
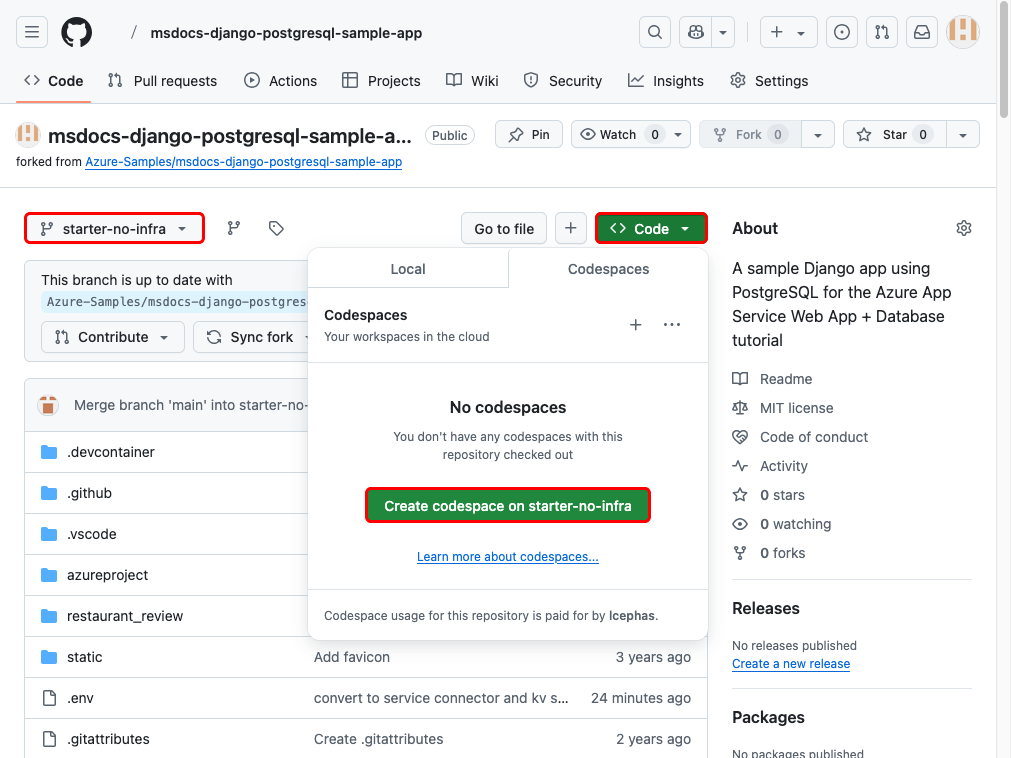
Paso 2: en la bifurcación de GitHub:
- Seleccione Principal>starter-no-infra para la rama de inicio. Esta rama contiene solo el proyecto de ejemplo y ninguna configuración ni archivo relacionados con Azure.
- Seleccione Código>Crear codespace on starter-no-infra.
El espacio de código tarda unos minutos en configurarse y se ejecuta
pip install -r requirements.txtpara el repositorio al final. Además, el archivo .env proporcionado ya contiene una variableSECRET_KEYficticia que Django debe ejecutar localmente.
Paso 3: En el terminal de codespace:
- Ejecute las migraciones de la base de datos con
python manage.py migrate. - Ejecute la aplicación con
python manage.py runserver. - Cuando vea la notificación
Your application running on port 8000 is available., seleccione Abrir en explorador. Debería ver la aplicación de ejemplo en una nueva pestaña del explorador. Para detener la aplicación, escribaCtrl+C.
Sugerencia
Puede preguntar a GitHub Copilot sobre este repositorio. Por ejemplo:
- @workspace ¿Qué hace este proyecto?
- @workspace ¿Qué hace la carpeta .devcontainer?
¿Tiene problemas? Consulte la sección Solución de problemas.
2. Creación de App Service, base de datos y caché
En este paso, creará los recursos de Azure. Los pasos que se usan en este tutorial crean un conjunto de recursos seguros de manera predeterminada que incluyen App Service, Azure Database for PostgreSQL y Azure Cache. En el proceso de creación, especifique lo siguiente:
- El Nombre de la aplicación web. Se usa como parte del nombre DNS de la aplicación en forma de
https://<app-name>-<hash>.<region>.azurewebsites.net. - La región para ejecutar la aplicación físicamente en el mundo. También se usa como parte del nombre DNS de la aplicación.
- La pila en tiempo de ejecución para la aplicación. Es donde se selecciona la versión de Python que se va a usar para la aplicación.
- El plan de hospedaje para la aplicación. Es el plan de tarifa que incluye el conjunto de características y la capacidad de escalado de la aplicación.
- El Grupo de recursos de la aplicación. Un grupo de recursos permite agrupar (en un contenedor lógico) todos los recursos de Azure necesarios para la aplicación.
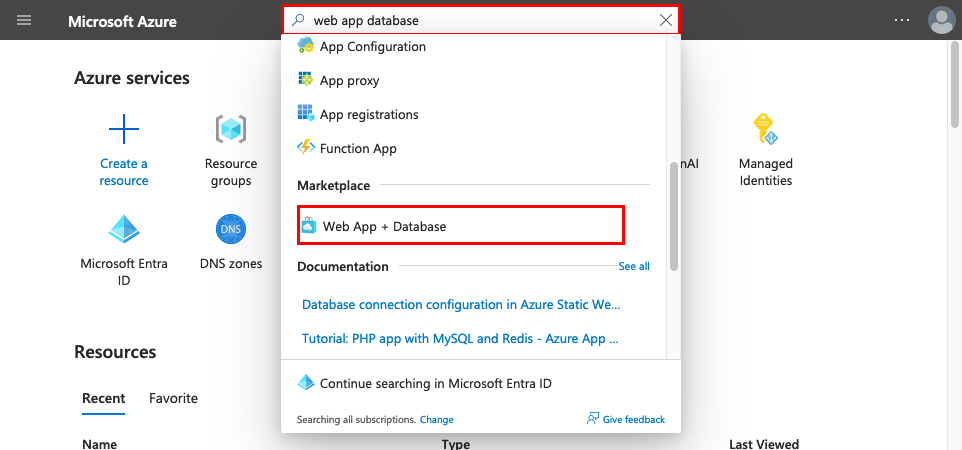
Inicie sesión en Azure Portal y siga estos pasos para crear los recursos de Azure App Service.
Paso 1: En el portal Azure:
- Escriba "base de datos de aplicación web" en la barra de búsqueda de la parte superior de Azure Portal.
- Seleccione el elemento denominado Aplicación web + base de datos en el encabezado Marketplace. También puede ir directamente al asistente de creación.
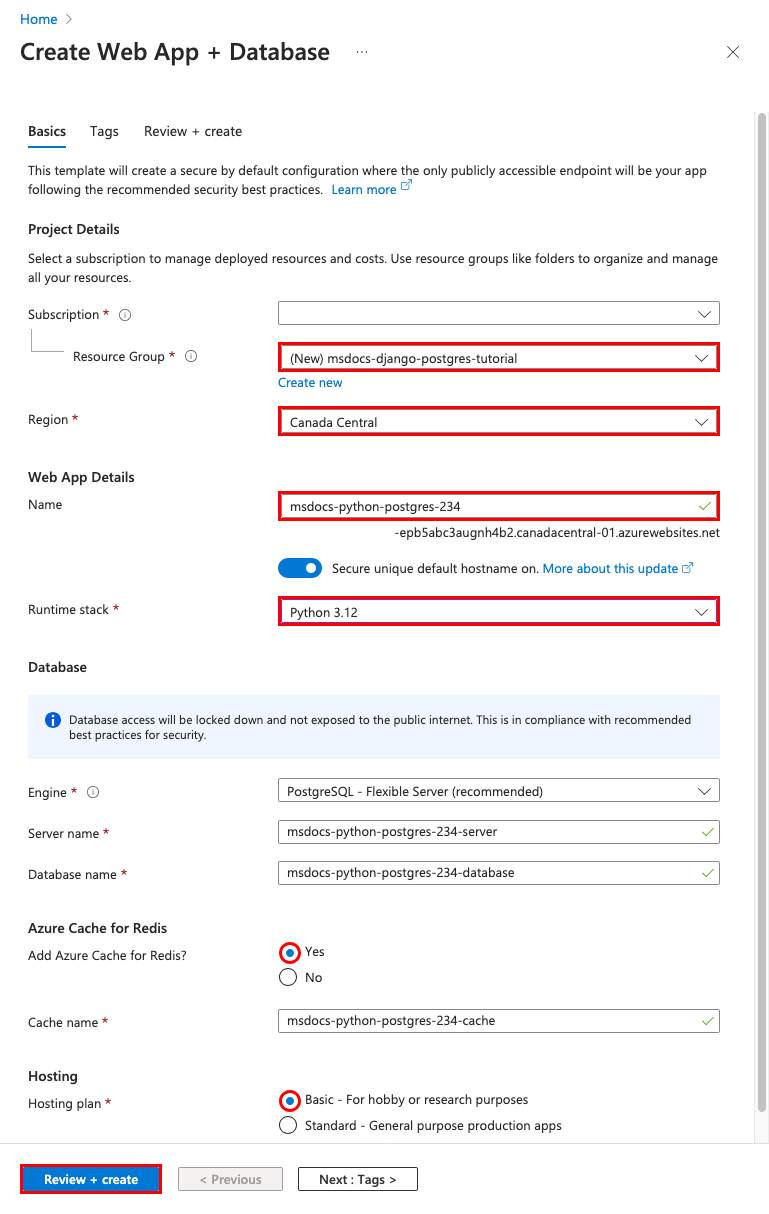
Paso 2: In the páginaCrear aplicación web + base de datos, rellene el formulario de la siguiente manera.
- Grupo de recursos: seleccione Crear nuevo y use un nombre de msdocs-quarkus-postgres-tutorial.
- Región: cualquier región de Azure cercana a usted.
- Nombre: msdocs-python-postgres-XYZ.
- Pila de runtime: Python 3.12.
- Base de datos: PostgreSQL: servidor flexible está seleccionado de manera predeterminada como motor de base de datos. El nombre del servidor y el nombre de la base de datos también se establecen de manera predeterminada en los valores adecuados.
- ¿Agregar Azure Cache for Redis?: sí.
- Plan de hospedaje: Básico. Cuando esté listo, puede escalar verticalmente a un plan de tarifa de producción.
- Seleccione Revisar + crear.
- Una vez completada la validación, seleccione Crear.
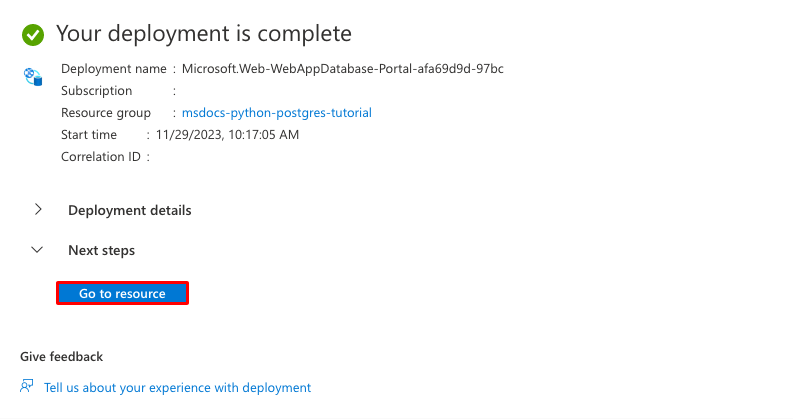
Step 3:La implementación tarda unos minutos en completarse. Una vez completada la implementación, seleccione el botón Ir al recurso. Se le dirigirá directamente a la aplicación App Service, pero se crean los siguientes recursos:
- Grupo de recursos: contenedor para todos los recursos creados.
- Plan de App Service: define los recursos de proceso de App Service. Se crea un plan de Linux en el nivel Básico.
- App Service: representa su aplicación y se ejecuta en el plan de App Service.
- Red virtual: se integra con la aplicación App Service y aísla el tráfico de back-end.
- Punto de conexión privado: punto de conexión de acceso para Redis Cache en la red virtual.
- Interfaces de red: representa direcciones IP privadas, una para cada uno de los puntos de conexión privados.
- Servidor flexible de Azure Database for PostgreSQL: accesible solo desde dentro de la red virtual. Una base de datos y un usuario se crean automáticamente en el servidor.
- Azure Cache for Redis: accesible solo desde detrás de su punto de conexión privado.
- Zonas DNS privadas: habilitar la resolución DNS del servidor de base de datos y Redis Cache en la red virtual.
3. Protección de los secretos de conexión y adición de SECRET_KEY
El Asistente para la creación generó automáticamente las variables de conectividad como valores de configuración de la aplicación. Sin embargo, el procedimiento recomendado de seguridad es mantener completamente los secretos fuera de App Service. Moverá los secretos a un almacén de claves y cambiará la configuración de la aplicación a referencias de Key Vault con la ayuda de Service Connectors.
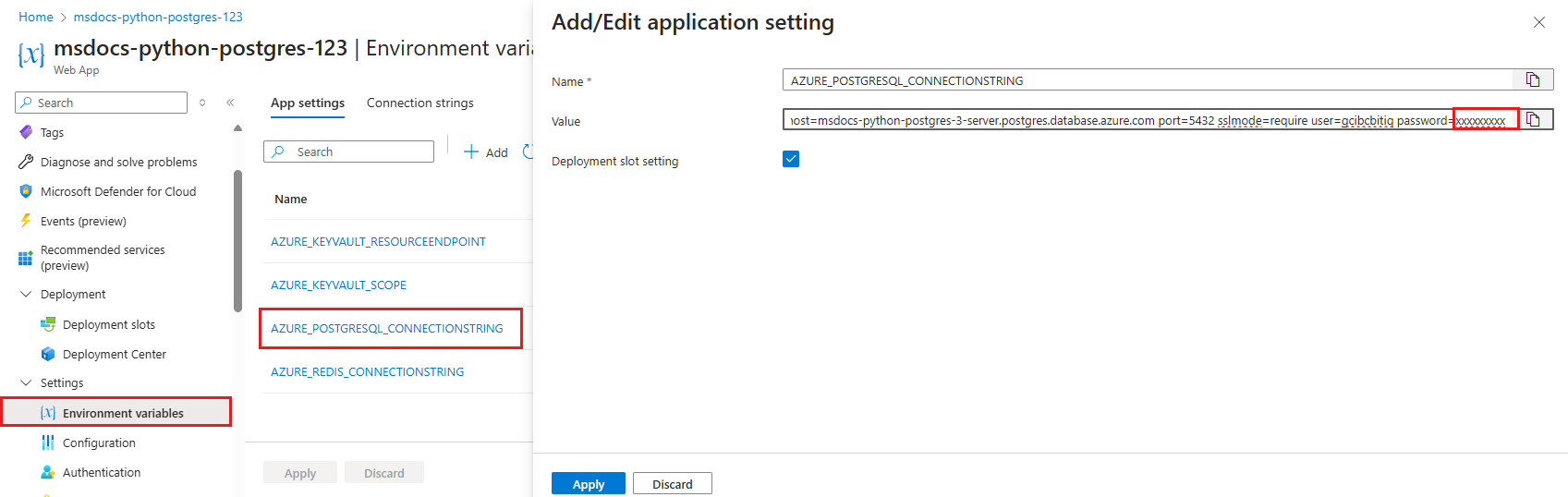
Paso 1: Recuperación de la cadena de conexión existente
- En el menú de la izquierda de la página App Service, seleccione Configuración > Variables de entorno.
- Seleccione AZURE_POSTGRESQL_CONNECTIONSTRING.
- En Agregar o editar configuración de aplicación, en el campo Valor, busque la parte password= al final de la cadena.
- Copie la cadena de contraseña después de password= para usarla más adelante.
Esta configuración de la aplicación le permite conectarse a la base de datos de Postgres y a Redis Cache protegida detrás de puntos de conexión privados. Sin embargo, el secreto se guarda directamente en la aplicación de App Service, que no es lo mejor. Cambiará esto. Además, agregará una configuración
SECRET_KEY, que es necesaria para la aplicación Django.
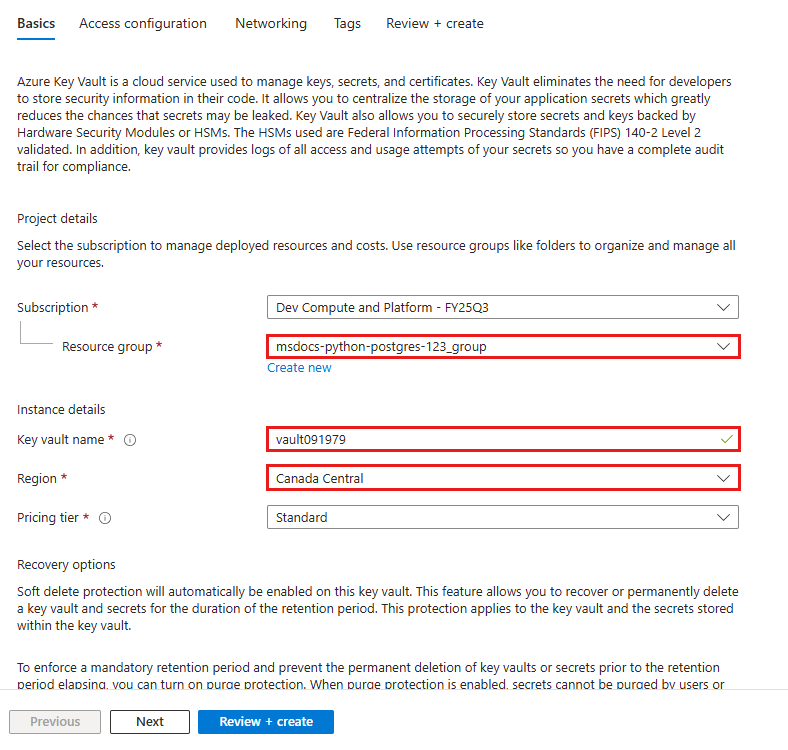
Paso 2: Creación de un almacén de claves para la administración segura de secretos
- En la barra de búsqueda superior, escriba "almacén de claves" y, a continuación, seleccione Marketplace>Key Vault.
- En Grupo de recursos, seleccione msdocs-python-postgres-tutorial.
- En Nombre del almacén de claves, escriba un nombre que consta de solo letras y números.
- En Región, establézcalo en la misma ubicación que el grupo de recursos.
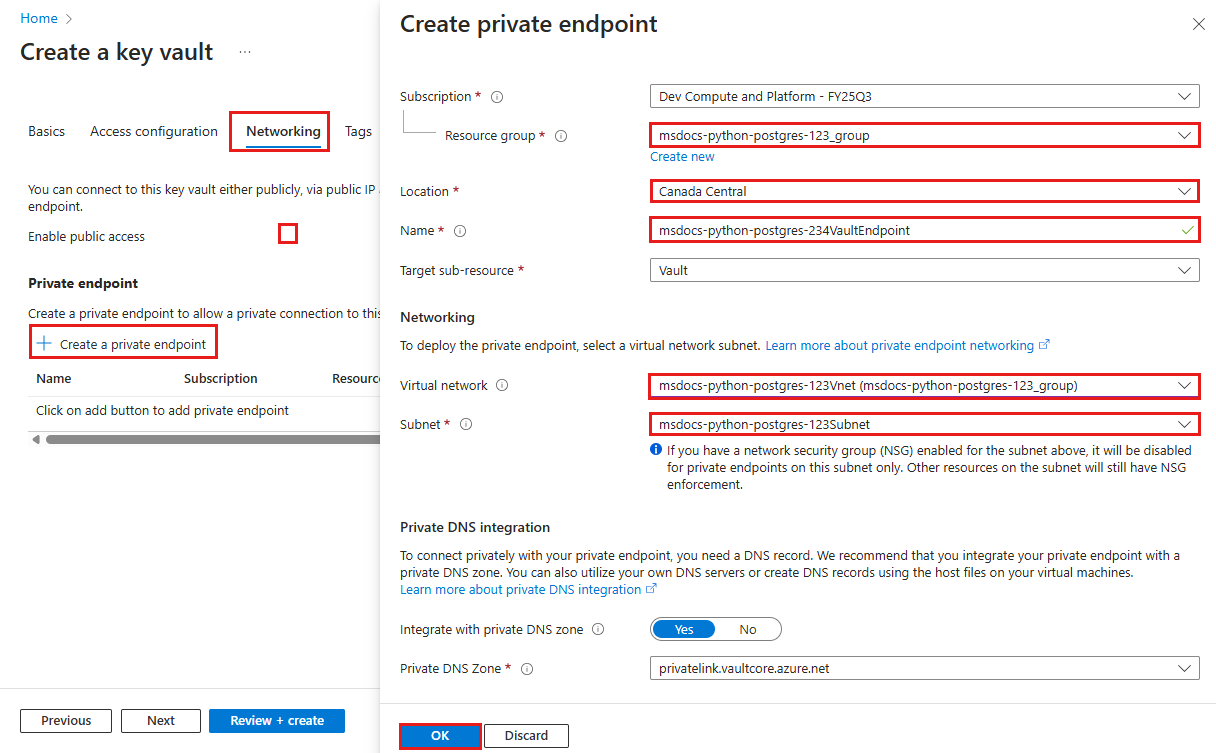
Paso 3: Protección del almacén de claves con un punto de conexión privado
- Seleccione la pestaña Redes.
- Anule la selección de Habilitar acceso público.
- Seleccione Crear un punto de conexión privado.
- En Grupo de recursos, seleccione msdocs-python-postgres-tutorial.
- En el cuadro de diálogo, en Ubicación, seleccione la misma ubicación que la aplicación de App Service.
- En Nombre, escriba msdocs-python-postgres-XYZVaultEndpoint.
- En Red virtual, seleccione msdocs-python-postgres-XYZVnet.
- En Subred, msdocs-python-postgres-XYZSubnet.
- Seleccione Aceptar.
- Seleccione Revisar y crear y, luego, Crear. Espere a que finalice la implementación del almacén de claves. Debería ver "La implementación está completa".
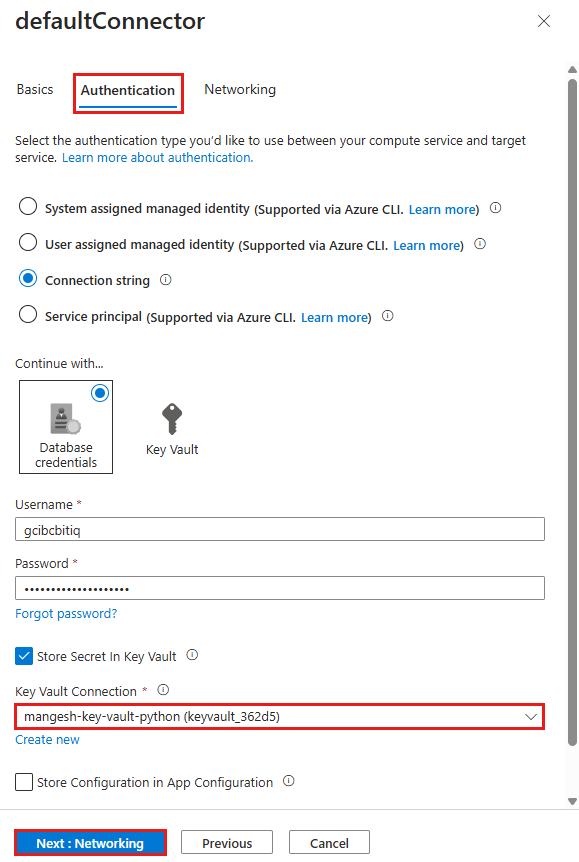
Paso 4: Configuración del conector de PostgreSQL
- En la barra de búsqueda superior, escriba msdocs-python-postgres y, a continuación, seleccione el recurso de App Service denominado msdocs-python-postgres-XYZ.
- En la página App Service, en el menú de la izquierda, seleccione Configuración > Conector de servicio. Ya hay dos conectores, que el asistente para la creación de aplicaciones ha creado automáticamente.
- Active la casilla situada junto al conector de PostgreSQL y seleccione Editar.
- En Tipo de cliente, seleccione Django. El tipo de cliente Django del conector del servicio PostgreSQL proporciona variables de base de datos en configuraciones independientes en lugar de una cadena de conexión. Las variables independientes son más fáciles de usar en la configuración de la base de datos de Django.
- Seleccione la pestaña Autenticación.
- En Contraseña, pegue la contraseña que copió anteriormente.
- Seleccione Almacenar secreto en Key Vault.
- En Conexión de Key Vault, seleccione Crear nuevo. Se abre un cuadro de diálogo Crear conexión encima del cuadro de diálogo de edición.
Paso 5: Establecimiento de la conexión de Key Vault
- En el cuadro de diálogo Crear conexión para la conexión de Key Vault, en Key Vault, seleccione el almacén de claves que ha creado antes.
- Seleccione Revisar + crear.
- Cuando se complete la validación, seleccione Crear.
Paso 6: Finalización de la configuración del conector de PostgreSQL
- Vuelve al cuadro de diálogo de edición de defaultConnector. En la pestaña Autenticación, espere a que se cree el conector del almacén de claves. Cuando haya terminado, la lista desplegable Conexión de Key Vault la selecciona automáticamente.
- Seleccione Siguiente: Redes.
- Seleccione Guardar. Espere hasta que aparezca la Actualización correcta notificación.
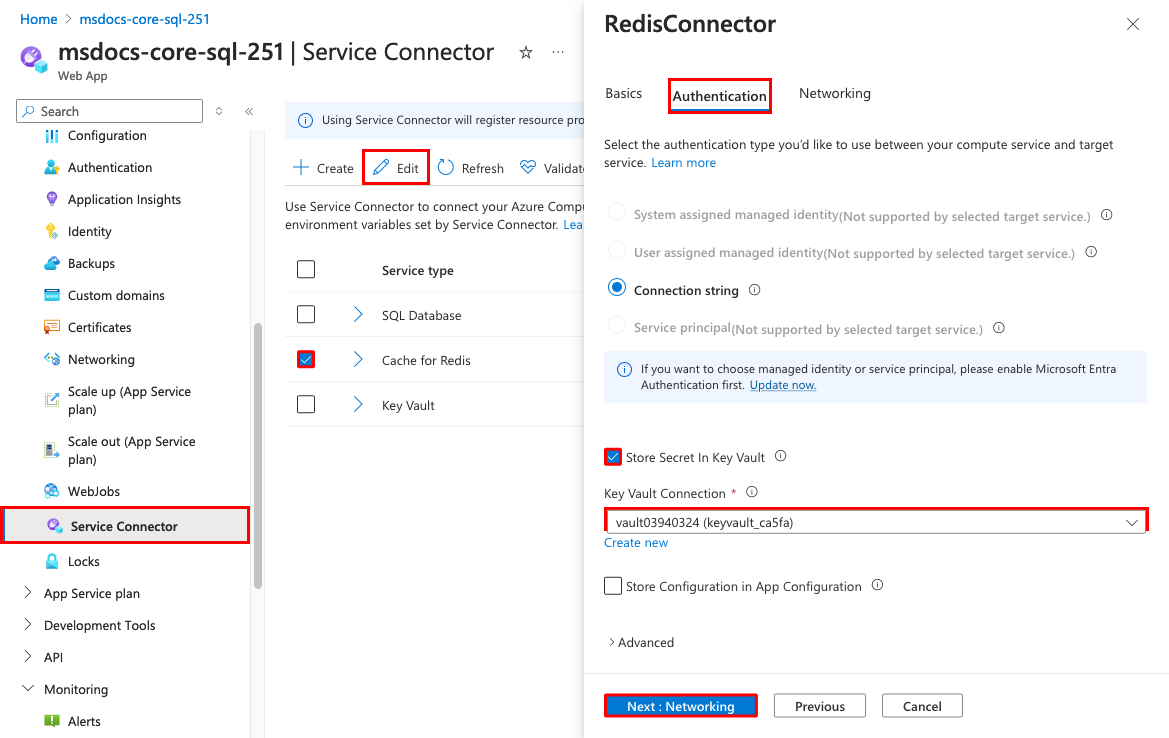
Paso 7: Configuración del conector de Redis para usar secretos de Key Vault
- En la página Conectores de servicio, active la casilla situada junto al conector de Cache for Redis y, a continuación, seleccione Editar.
- Seleccione la pestaña Autenticación.
- Seleccione Almacenar secreto en Key Vault.
- En Conexión de Key Vault, seleccione el almacén de claves que creó.
- Seleccione Siguiente: Redes.
- Seleccione Configurar reglas de firewall para habilitar el acceso al servicio de destino. El Asistente para la creación de aplicaciones ya ha protegido la base de datos SQL con un punto de conexión privado.
- Seleccione Guardar. Espere hasta que aparezca la Actualización correcta notificación.
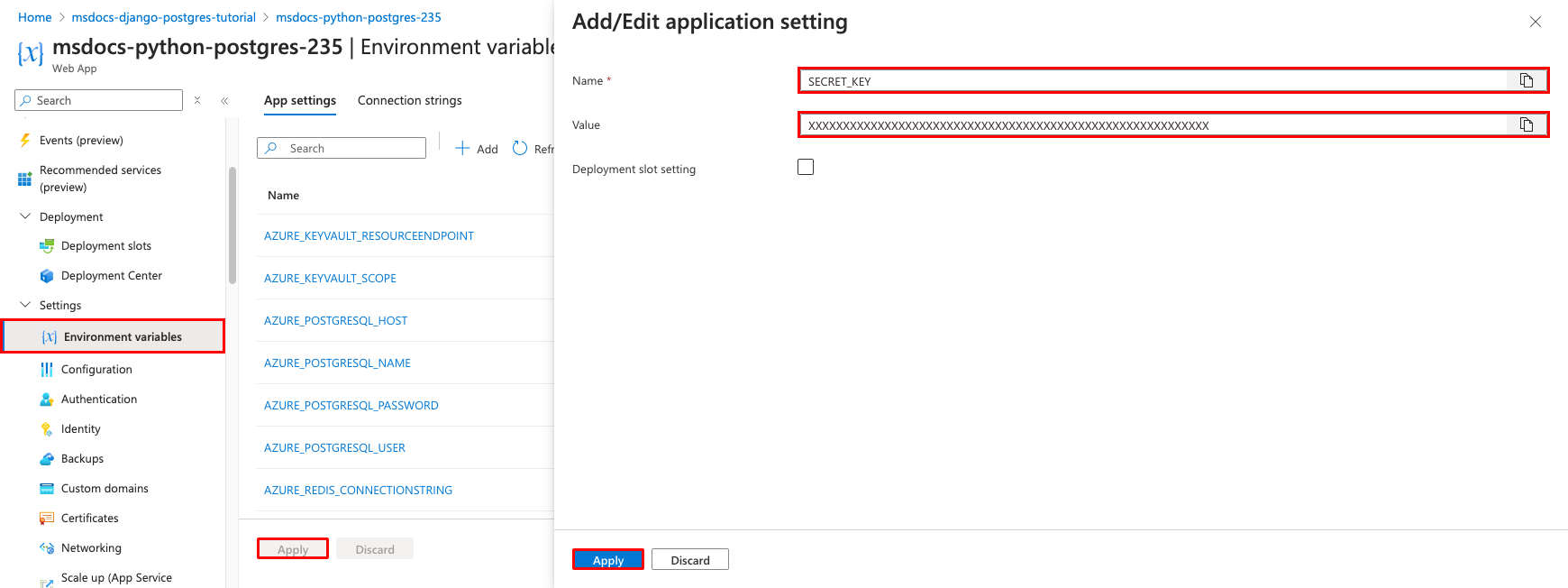
Paso 8: Comprobar la integración de Key Vault
- En el menú de la izquierda, vuelva a seleccionar Configuración > Variables de entorno.
- Junto a AZURE_POSTGRESQL_PASSWORD, seleccione Mostrar valor. El valor debe ser
@Microsoft.KeyVault(...), lo que significa que es un referencia del almacén de claves porque el secreto ahora se administra en el almacén de claves. - Para comprobar la cadena de conexión de Redis, seleccione Mostrar valor junto a AZURE_REDIS_CONNECTIONSTRING.
Paso 9: La aplicación de ejemplo lee la variable de entorno SECRET_KEY para establecer la configuración de SECRET_KEY necesaria. Se crea como una configuración de aplicación en este paso.
- En la pestaña Configuración de la aplicación, seleccione + Agregar.
- Establezca Nombre en SECRET_KEY.
- Establezca Valor en una cadena aleatoria larga.
- Haga clic en Aplicar, luego en Aplicar una vez más y, a continuación, en Confirmar.
En resumen, el proceso para proteger los secretos de conexión implicados:
- Recuperar los secretos de conexión de las variables de entorno de la aplicación de App Service.
- Creación de un almacén de claves.
- Creación de una conexión de Key Vault con la identidad administrada asignada por el sistema.
- Actualización de los conectores de servicio para almacenar los secretos en el almacén de claves.
Nota:
Lo ideal es que la configuración de la aplicación SECRET_KEY se configure también como una referencia del almacén de claves, que es un proceso de varios pasos. Para obtener más información, consulte ¿Cómo cambio la configuración de la aplicación de SECRET_KEY a una referencia de Key Vault?
¿Tiene problemas? Consulte la sección Solución de problemas.
4. Implantación del código de ejemplo
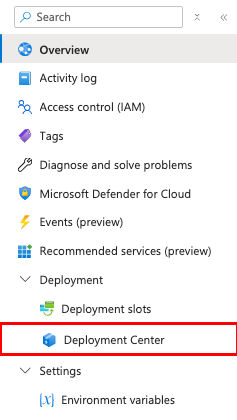
En este paso, configurará la implementación de GitHub mediante Acciones de GitHub. Es solo una de las muchas maneras de implementar en App Service, pero también una excelente manera de disponer de integración continua en el proceso de implementación. De forma predeterminada, cada uno de los repositorios git push de GitHub inicia la acción de compilación e implementación.
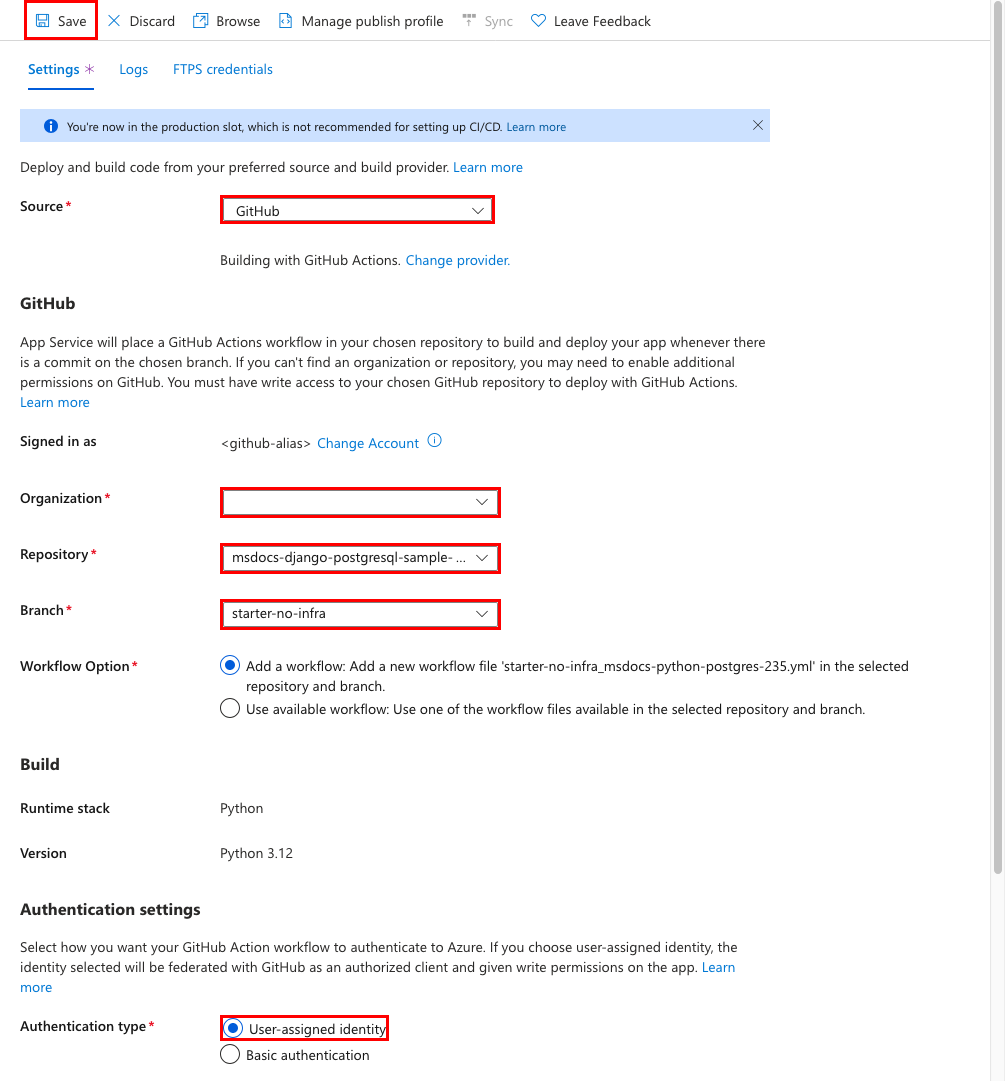
Paso 1: En el menú de la izquierda, seleccione Implementación>Centro de implementación.
Paso 2: En la página Centro de implementación:
- En Origen, seleccione GitHub. De forma predeterminada, Acciones de GitHub está seleccionado como proveedor de compilación.
- Inicie sesión en su cuenta de GitHub y siga las indicaciones para autorizar a Azure.
- En Organización, seleccione su cuenta.
- En Repositorio, seleccione msdocs-django-postgresql-sample-app.
- En Rama, seleccione starter-no-infra. Esta es la misma rama en la que ha trabajado con la aplicación de ejemplo, sin archivos ni configuraciones relacionados con Azure.
- En Tipo de autenticación, seleccione Identidad asignada por el usuario.
- En el menú superior, elija Guardar.
App Service confirma un archivo de flujo de trabajo en el repositorio de GitHub escogido, en el directorio
.github/workflows. De manera predeterminada, el centro de implementación crea una identidad asignada por el usuario para que el flujo de trabajo se autentique mediante Microsoft Entra (autenticación OIDC). Para obtener opciones de autenticación alternativas, consulte Implementación en App Service mediante Acciones de GitHub.
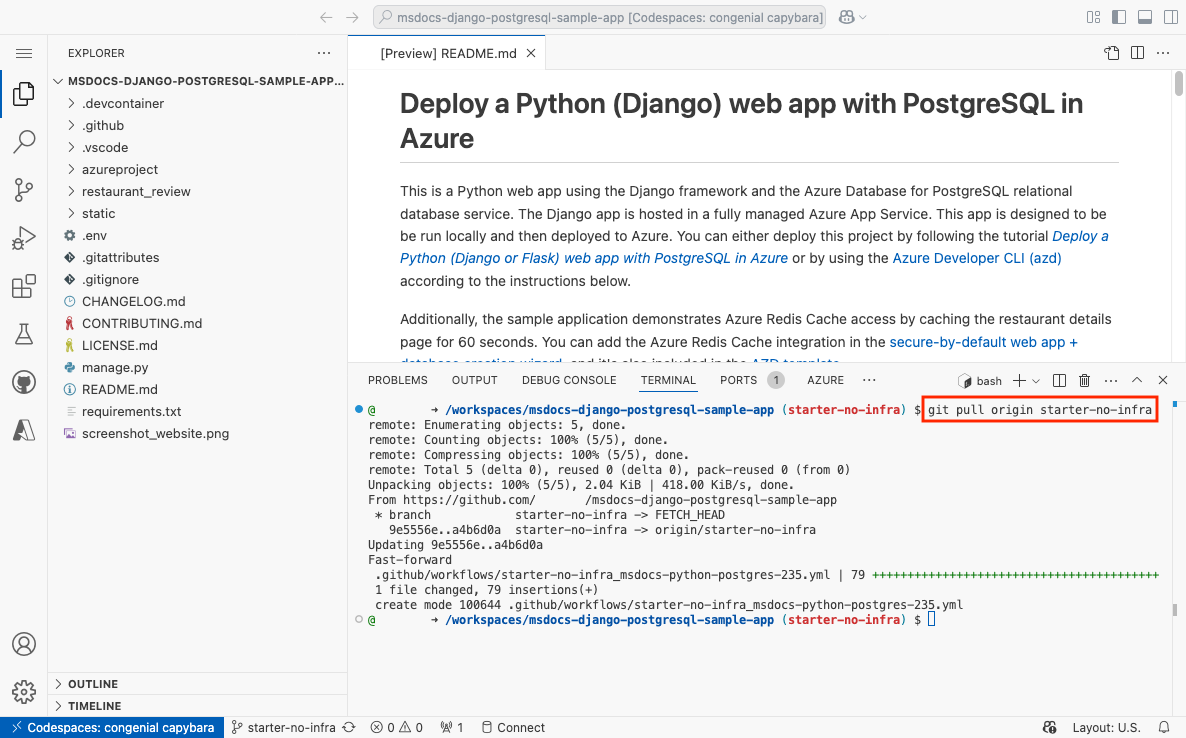
Paso 3: De nuevo en el codespace de GitHub de la bifurcación de ejemplo, ejecute git pull origin starter-no-infra.
Esto extrae el archivo de flujo de trabajo recién confirmado en el codespace.
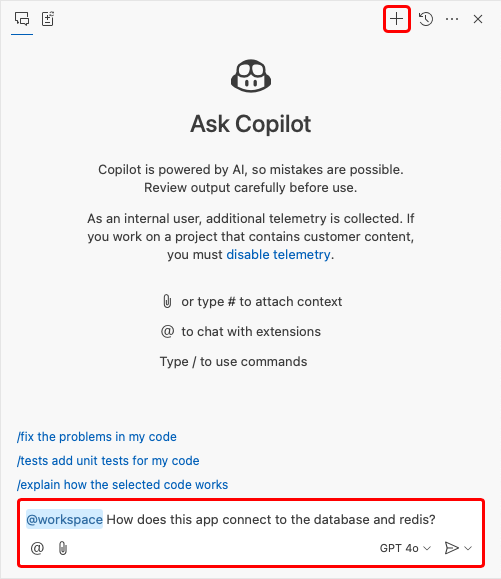
Paso 4 (Opción 1: con GitHub Copilot):
- Inicie una nueva sesión de chat al seleccionar la vista Chat y, después, seleccionar +.
- Pregunte: "@workspace ¿Cómo se conecta la aplicación a la base de datos y a Redis?". Copilot puede darle una explicación sobre cómo se configuran las opciones en azureproject/development.py y azureproject/production.py.
- Pregunte: "@workspace En modo de producción, mi aplicación se ejecuta en una aplicación web de App Service, que usa Azure Service Connector para conectarse a un servidor flexible de PostgreSQL mediante el tipo de cliente Django. ¿Cuáles son los nombres de las variables de entorno que necesito usar?" Copilot puede proporcionarle una sugerencia de código similar a la de los pasos de la Opción 2: sin GitHub Copilot que se indican a continuación e incluso indicarle que realice el cambio en el archivo azureproject/production.py.
- Abra azureproject/production.py en el explorador y agregue la sugerencia de código.
- Pregunte: "@workspace Mi aplicación App Service también usa Azure Service Connector para conectarse a una instancia de Cache for Redis mediante el tipo de cliente Django. ¿Cuáles son los nombres de las variables de entorno que necesito usar?*" Copilot puede proporcionar una sugerencia de código similar a la de los pasos de la Opción 2: sin GitHub Copilot que se indican a continuación e incluso indicarle que realice el cambio en el archivo azureproject/production.py.
- Agregue la sugerencia de código. GitHub Copilot no proporciona la misma respuesta cada vez y no siempre esta es correcta. Es posible que tenga que formular más preguntas para ajustar su respuesta. Para obtener sugerencias, consulte ¿Qué puedo hacer con GitHub Copilot en mi espacio de código?.
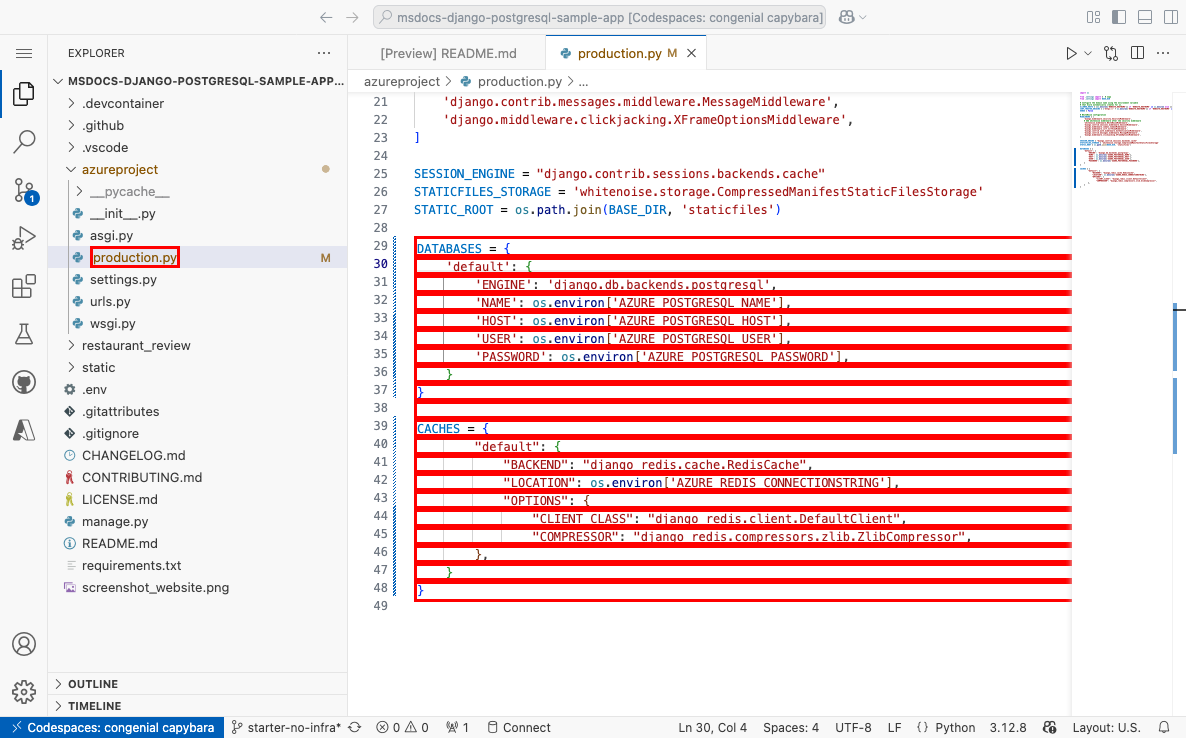
Paso 4 (Opción 2: sin GitHub Copilot):
- Abra Program.cs en el explorador.
- Busque el código comentado (líneas 29-48) y quite la marca de comentario.
Esto crea conexiones de PostgreSQL y Redis mediante
AZURE_POSTGRESQL_USER,AZURE_POSTGRESQL_PASSWORD,AZURE_POSTGRESQL_HOST,AZURE_POSTGRESQL_NAMEyAZURE_REDIS_CONNECTIONSTRING.
Paso 5:
- Seleccione la extensión Control de código fuente.
- En el cuadro de texto, escriba un mensaje de confirmación, por ejemplo,
Configure Azure database and cache connectons. O bien, seleccione y deje que GitHub Copilot genere un mensaje de confirmación de manera automática.
y deje que GitHub Copilot genere un mensaje de confirmación de manera automática. - Seleccione Confirmar y, a continuación, confirme con Sí.
- Seleccione Sincronización de cambios 1 y confirme con Aceptar.
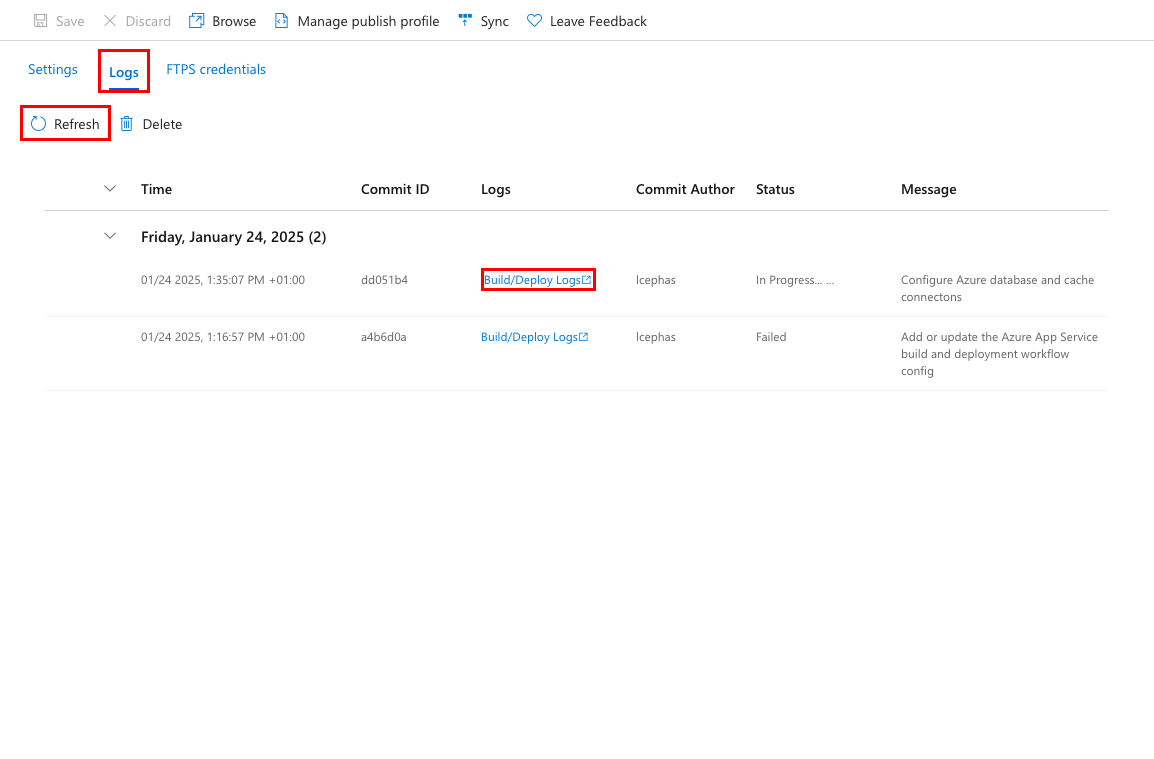
Paso 6: De vuelta en la página Centro de implementación en Azure Portal:
- Seleccione la pestaña Registros y, a continuación, seleccione Actualizar para ver la nueva ejecución de implementación.
- En el elemento de registro de la ejecución de implementación, seleccione la entrada Registros de compilación/implementación con la marca de tiempo más reciente.
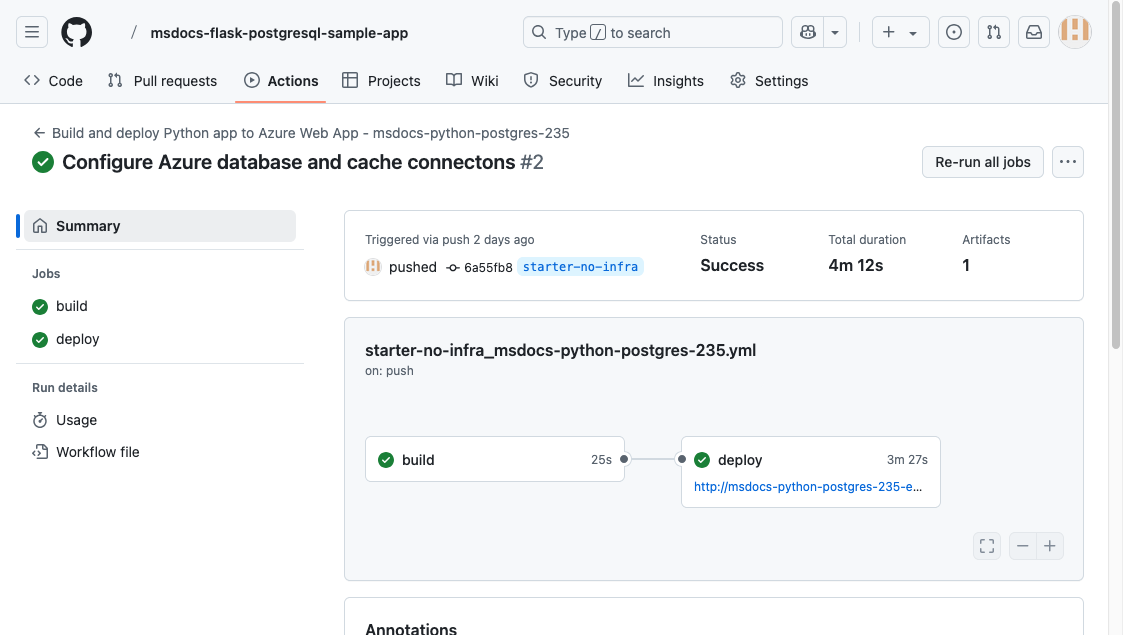
Paso 7: Se le llevará al repositorio de GitHub, donde ve que la acción de GitHub se está ejecutando. El archivo de flujo de trabajo define dos fases independientes: compilación e implementación. Espere a que la ejecución de GitHub muestre el estado Correcto. Tardará unos 5 minutos.
¿Tiene problemas? Consulte la Guía de solución de problemas.
5. Generar esquema de base de datos
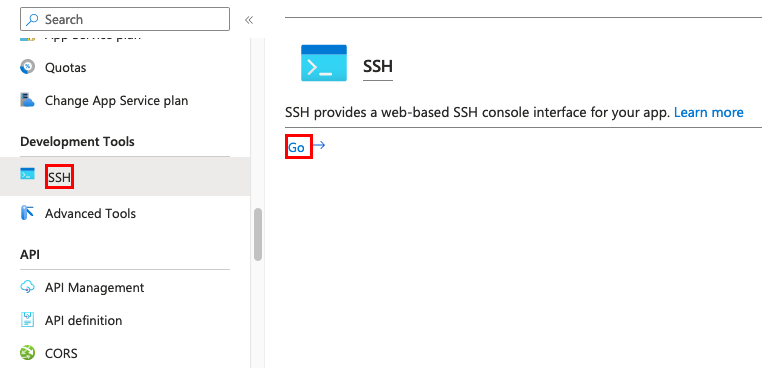
Con la base de datos PostgreSQL protegida por la red virtual, la manera más fácil de ejecutar migraciones de base de datos de Django es mediante una sesión SSH con el contenedor de Linux en App Service.
Paso 1: De vuelta en la página App Service, en el menú de la izquierda,
- Seleccione Herramientas de desarrollo>SSH.
- Seleccione Ir.
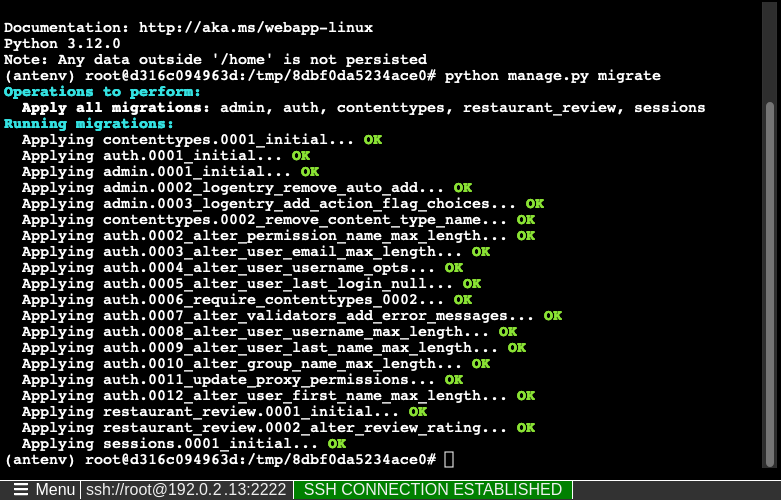
Paso 2: En la sesión SSH, ejecute python manage.py migrate. Si se realiza correctamente, App Service se conecta a la base de datos.
Sugerencia
En la sesión SSH, solo los cambios en los archivos de /home pueden persistir más allá de los reinicios de la aplicación. Los cambios efectuados fuera de /home no se conservan. La sesión SSH es útil para ejecutar comandos python manage.py comunes, como la creación de usuarios con python manage.py createsuperuser. Para obtener más información, consulte la documentación de django django-admin y manage.py. Use la cuenta de superusuario para acceder a la parte /admin del sitio web.
¿Tiene problemas? Consulte la sección Solución de problemas.
6. Navegación hasta la aplicación
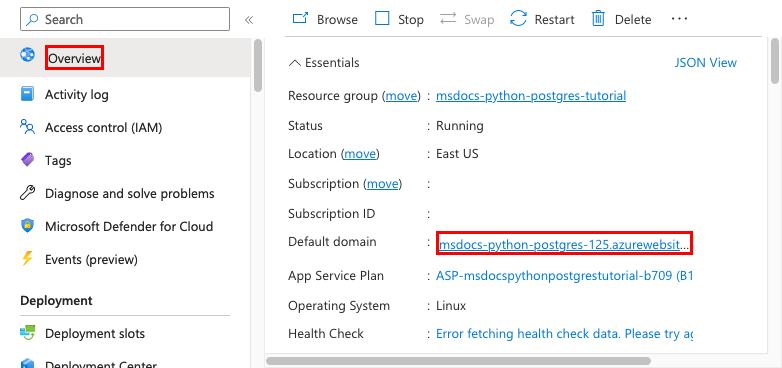
Paso 1. En la página App Service:
- En el menú de la izquierda, seleccione Información general.
- Seleccione la dirección URL de la aplicación.
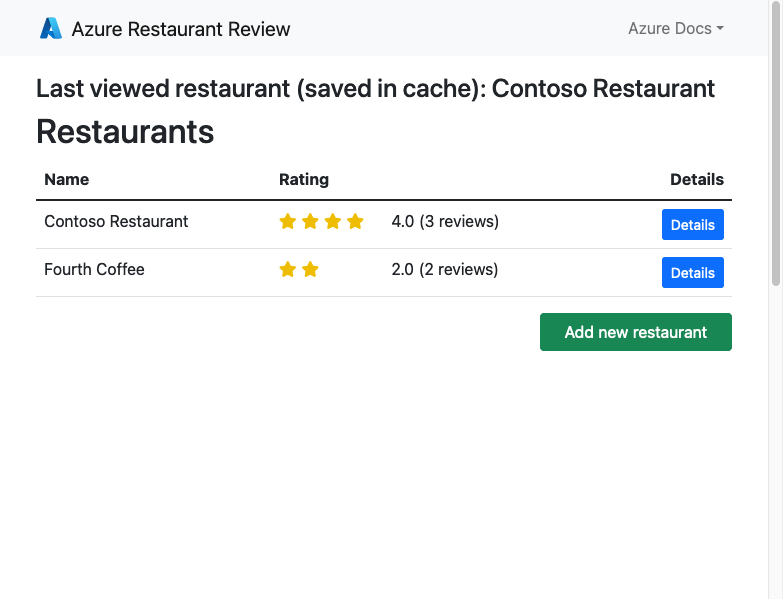
Paso 2: agregue algunos restaurantes a la lista. Enhorabuena, ya está ejecutando una aplicación web en Azure App Service, con conectividad protegida a Azure Database for PostgreSQL.
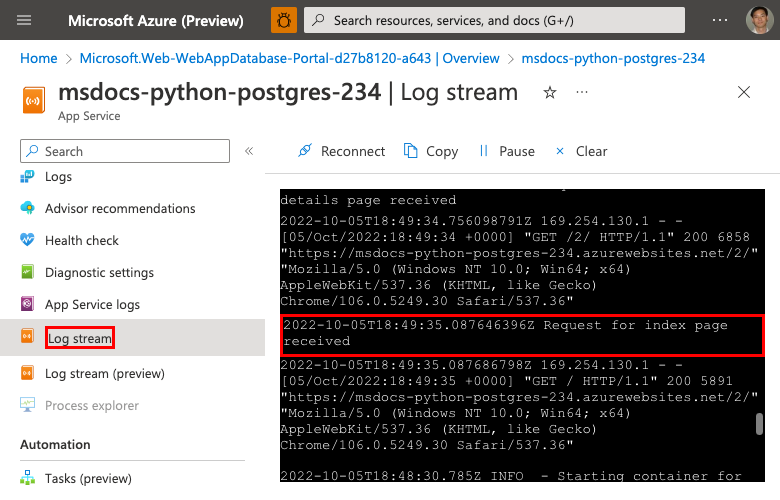
7. Transmisión de registros de diagnóstico
Azure App Service captura todos los registros de consola para ayudarle a diagnosticar problemas con la aplicación. La aplicación de ejemplo incluye instrucciones print() para demostrar esta funcionalidad, como se muestra a continuación.
def index(request):
print('Request for index page received')
restaurants = Restaurant.objects.annotate(avg_rating=Avg('review__rating')).annotate(review_count=Count('review'))
lastViewedRestaurant = request.session.get("lastViewedRestaurant", False)
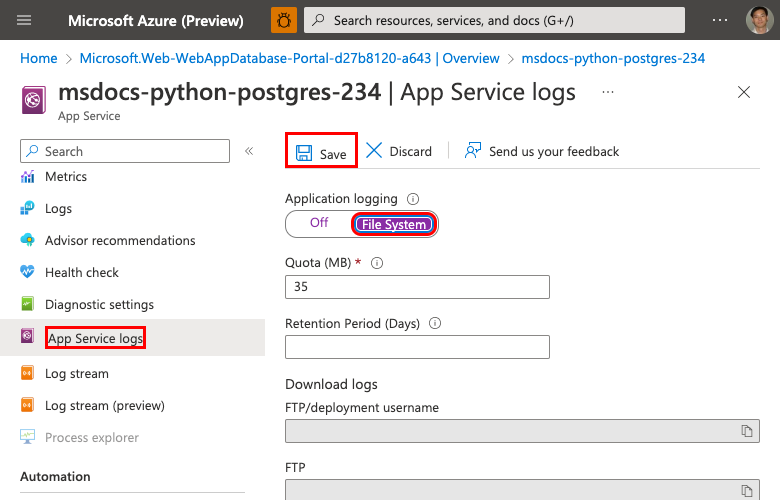
Paso 1. En la página App Service:
- En el menú de la izquierda, seleccione Supervisión>Registros de App Service.
- En Registro de aplicaciones, seleccione Sistema de archivos.
- En el menú superior, elija Guardar.
Paso 2: En el menú de la izquierda, seleccione Flujo de registro. Verá los registros de la aplicación, incluidos los registros de plataforma y los registros de dentro del contenedor.
Obtenga más información sobre cómo iniciar sesión en aplicaciones de Python en la serie sobre cómo configurar Azure Monitor para la aplicación Python.
8. Limpieza de recursos
Cuando acabe, puede eliminar todos los recursos de la suscripción de Azure mediante la eliminación del grupo de recursos.
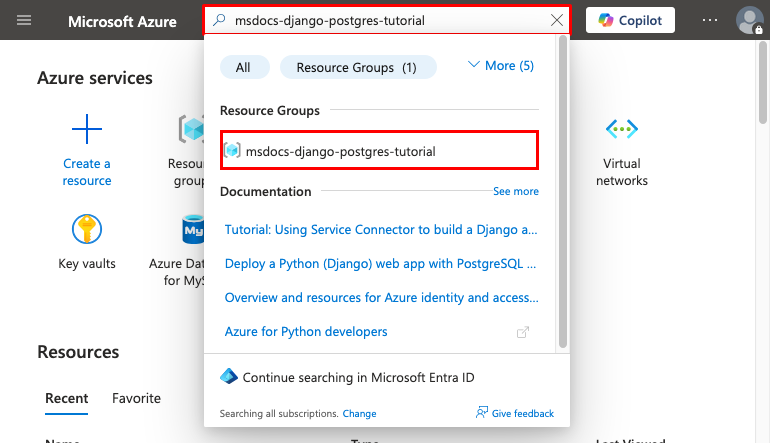
Paso 1:En la barra de búsqueda de la parte superior de Azure Portal:
- Escriba el nombre del grupo de recursos.
- Seleccione el grupo de recursos.
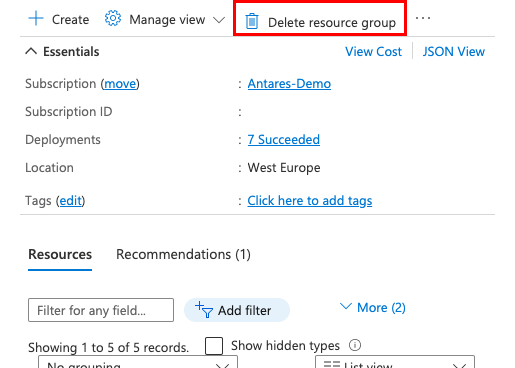
Paso 2: En la página del grupo de recursos, seleccione Borrar grupo de recursos.
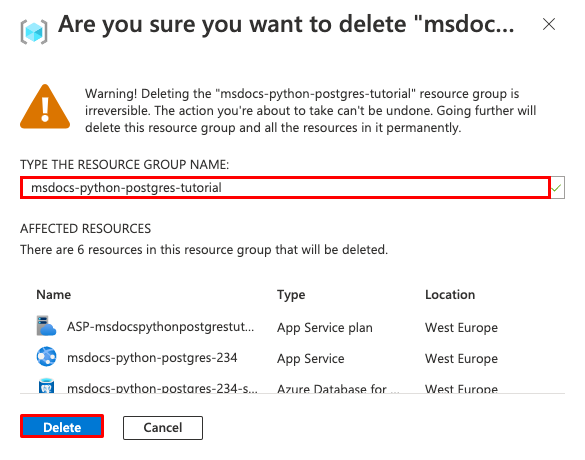
Paso 3:
- Escriba el nombre del grupo de recursos para confirmar la eliminación.
- Seleccione Eliminar.
2. Creación de recursos de Azure e implementación de una aplicación de ejemplo
En este paso, creará los recursos de Azure e implementará una aplicación de ejemplo en App Service en Linux. Los pasos que se usan en este tutorial crean un conjunto de recursos seguros de manera predeterminada que incluyen App Service, Azure Database for PostgreSQL y Azure Cache for Redis.
El contenedor de desarrollo ya tiene Azure Developer CLI (AZD).
Desde la raíz del repositorio, ejecute
azd init.azd init --template python-app-service-postgresql-infraCuando se le solicite, proporcione las siguientes respuestas:
Pregunta Respuesta El directorio actual no está vacío. ¿Desea inicializar un proyecto aquí en "<su directorio>"? Y ¿Qué quiere hacer con estos archivos? Mantener mis archivos existentes sin cambios Escribir un nuevo nombre de entorno Escriba un nombre único. La plantilla de AZD usa este nombre como parte del nombre DNS de la aplicación web en Azure ( <app-name>-<hash>.azurewebsites.net). Se permiten caracteres alfanuméricos y guiones.Inicie sesión en Azure mediante la ejecución del comando
azd auth loginy siga la solicitud:azd auth loginCree los recursos de Azure necesarios con el comando
azd provision. Siga la solicitud para seleccionar la suscripción y la ubicación deseadas para los recursos de Azure.azd provisionEl comando
azd provisiontarda unos 15 minutos en completarse (la Redis Cache tarda más tiempo). Más adelante, modificará el código para trabajar con App Service e implementará los cambios conazd deploy. Mientras se ejecuta, el comando proporciona mensajes sobre el proceso de aprovisionamiento e implementación, incluido un vínculo a la implementación en Azure.Esta plantilla de AZD contiene archivos (azure.yaml y el directorio infra) que generarán una arquitectura segura de manera predeterminada con los siguientes recursos de Azure:
- Grupo de recursos: contenedor para todos los recursos creados.
- Plan de App Service: define los recursos de proceso de App Service. Se crea un plan de Linux en el nivel Básico.
- App Service: representa su aplicación y se ejecuta en el plan de App Service.
- Red virtual: se integra con la aplicación App Service y aísla el tráfico de back-end.
- Puntos de conexión privados: acceda a puntos de conexión para el almacén de claves y Redis Cache en la red virtual.
- Interfaces de red: representa direcciones IP privadas, una para cada uno de los puntos de conexión privados.
- Servidor flexible de Azure Database for PostgreSQL: accesible solo desde dentro de la red virtual. Una base de datos y un usuario se crean automáticamente en el servidor.
- Zona DNS privada: habilita la resolución DNS del servidor PostgreSQL en la red virtual.
- Área de trabajo de Log Analytics: actúa como contenedor de destino para que su aplicación envíe sus registros, donde también puede consultar los registros.
- Azure Cache for Redis: accesible solo desde detrás de su punto de conexión privado.
- Almacén de claves: accesible solo desde detrás de su punto de conexión privado. Se usa para administrar secretos para la aplicación de App Service.
Una vez que el comando termina de crear recursos e implementar el código de la aplicación la primera vez, la aplicación de ejemplo implementada aún no funciona porque debe realizar pequeños cambios para conectarse a la base de datos en Azure.
¿Tiene problemas? Consulte la sección Solución de problemas.
3. Uso de la cadena de conexión de base de datos
La plantilla de AZD que usa ya ha generado las variables de conectividad como valores de la aplicación y las envía al terminal para mayor comodidad. La configuración de la aplicación es una forma de mantener los secretos de conexión fuera del repositorio de código.
En la salida de AZD, busque los valores
AZURE_POSTGRESQL_USER,AZURE_POSTGRESQL_PASSWORD,AZURE_POSTGRESQL_HOST,AZURE_POSTGRESQL_NAMEyAZURE_REDIS_CONNECTIONSTRING. Para mantener los secretos seguros, solo se muestran los nombres de configuración. Tienen este aspecto en la salida de AZD:App Service app has the following connection settings: - AZURE_POSTGRESQL_NAME - AZURE_POSTGRESQL_HOST - AZURE_POSTGRESQL_USER - AZURE_POSTGRESQL_PASSWORD - AZURE_REDIS_CONNECTIONSTRING - AZURE_KEYVAULT_RESOURCEENDPOINT - AZURE_KEYVAULT_SCOPEPara mayor comodidad, la plantilla de AZD muestra el vínculo directo a la página de configuración de la aplicación. Busque el vínculo y ábralo en una nueva pestaña del explorador.
¿Tiene problemas? Consulte la sección Solución de problemas.
4. Modificación del código de ejemplo y reimplementación
En el espacio de código de GitHub, inicie una nueva sesión de chat; para ello, seleccione la vista Chat y, a continuación, seleccione +.
Pregunte: "@workspace ¿Cómo se conecta la aplicación a la base de datos?". Copilot puede proporcionar una explicación sobre cómo se configuran las opciones de conexión en azureproject/development.py y azureproject/production.py.
Pregunte: "@workspace En modo de producción, mi aplicación se ejecuta en una aplicación web de App Service, que usa Azure Service Connector para conectarse a un servidor flexible de PostgreSQL mediante el tipo de cliente Django. ¿Cuáles son los nombres de las variables de entorno que necesito usar?" Copilot puede proporcionarle una sugerencia de código similar a la de los pasos de la Opción 2: sin GitHub Copilot que se indican a continuación e incluso indicarle que realice el cambio en el archivo azureproject/production.py.
Abra azureproject/production.py en el explorador y agregue la sugerencia de código.
GitHub Copilot no proporciona la misma respuesta cada vez y no siempre esta es correcta. Es posible que tenga que formular más preguntas para ajustar su respuesta. Para obtener sugerencias, consulte ¿Qué puedo hacer con GitHub Copilot en mi espacio de código?.
En el terminal, ejecute
azd deploy.azd deploy
¿Tiene problemas? Consulte la sección Solución de problemas.
5. Generar esquema de base de datos
Con la base de datos PostgreSQL protegida por la red virtual, la manera más fácil de ejecutar migraciones de base de datos de Django es mediante una sesión SSH con el contenedor de Linux en App Service.
En la salida de AZD, busque la dirección URL de la sesión SSH y vaya a ella en el explorador. Se parece a esto en la salida:
Open SSH session to App Service container at: https://<app-name>.scm.azurewebsites.net/webssh/host
En la sesión SSH, ejecute
python manage.py migrate. Si se realiza correctamente, App Service se conecta a la base de datos.Nota:
Cuando la aplicación se reinicie, solo persisten los cambios realizados en los archivos ubicados en
/home. Los cambios efectuados fuera de/homeno se conservan.
¿Tiene problemas? Consulte la sección Solución de problemas.
6. Navegación hasta la aplicación
En la salida de AZD, busque la dirección URL de la aplicación y vaya a ella en el explorador. La dirección URL tiene este aspecto en la salida de AZD:
Deploying services (azd deploy) (✓) Done: Deploying service web - Endpoint: https://<app-name>.azurewebsites.net/
Agregue algunos restaurantes a la lista.
Enhorabuena, ya está ejecutando una aplicación web en Azure App Service, con conectividad protegida a Azure Database for PostgreSQL.
¿Tiene problemas? Consulte la sección Solución de problemas.
7. Transmisión de registros de diagnóstico
Azure App Service puede capturar registros de consola para ayudarle a diagnosticar problemas con la aplicación. Para mayor comodidad, la plantilla de AZD ya ha habilitado el registro en el sistema de archivos local y está enviando los registros a un área de trabajo de Log Analytics.
La aplicación de ejemplo incluye instrucciones print() para demostrar esta funcionalidad, como se muestra en el siguiente fragmento de código.
def index(request):
print('Request for index page received')
restaurants = Restaurant.objects.annotate(avg_rating=Avg('review__rating')).annotate(review_count=Count('review'))
lastViewedRestaurant = request.session.get("lastViewedRestaurant", False)
En la salida de AZD, busque el vínculo para transmitir registros de App Service y vaya a él en el explorador. El vínculo tiene este aspecto en la salida de AZD:
Stream App Service logs at: https://portal.azure.com/#@/resource/subscriptions/<subscription-guid>/resourceGroups/<group-name>/providers/Microsoft.Web/sites/<app-name>/logStream
Obtenga más información sobre cómo iniciar sesión en aplicaciones de Python en la serie sobre cómo configurar Azure Monitor para la aplicación Python.
¿Tiene problemas? Consulte la sección Solución de problemas.
8. Limpieza de recursos
Para eliminar todos los recursos de Azure en el entorno de implementación actual, ejecute azd down y siga las indicaciones.
azd down
Solución de problemas
A continuación se indican los problemas que pueden surgir al intentar trabajar con este tutorial y los pasos para resolverlos.
No puedo conectarme a la sesión de SSH
Si no puede conectarse a la sesión SSH, significa que no se pudo iniciar la propia aplicación. Compruebe los registros de diagnóstico para obtener más información. Por ejemplo, si ve un error como KeyError: 'AZURE_POSTGRESQL_HOST', puede significar que falta la variable de entorno (es posible que haya quitado el valor de configuración de la aplicación).
Recibo un error al ejecutar migraciones de base de datos
Si encuentra algún error relacionado con la conexión a la base de datos, compruebe si se han cambiado o eliminado los valores de configuración de la aplicación (AZURE_POSTGRESQL_USER, AZURE_POSTGRESQL_PASSWORD, AZURE_POSTGRESQL_HOST y AZURE_POSTGRESQL_NAME). Sin esa cadena de conexión, el comando de migración no se puede comunicar con la base de datos.
Preguntas más frecuentes
- ¿Cuánto cuesta esta configuración?
- ¿Cómo me conecto al servidor de PostgreSQL protegido tras la red virtual con otras herramientas?
- ¿Cómo funciona el desarrollo de aplicaciones locales con Acciones de GitHub?
- ¿Cómo está configurado el ejemplo de Django para ejecutarse en Azure App Service?
- ¿Cómo cambio la configuración de la aplicación SECRET_KEY a una referencia de Key Vault?
- ¿Cómo se depuran los errores durante la implementación de Acciones de GitHub?
- No tengo permisos para crear una identidad asignada por el usuario
- ¿Qué puedo hacer con GitHub Copilot en mi codespace?
- ¿Cuánto cuesta esta configuración?
- ¿Cómo me conecto al servidor de PostgreSQL protegido tras la red virtual con otras herramientas?
- ¿Cómo funciona el desarrollo de aplicaciones locales con Acciones de GitHub?
- ¿Cómo está configurado el ejemplo de Django para ejecutarse en Azure App Service?
- ¿Cómo se depuran los errores durante la implementación de Acciones de GitHub?
- No tengo permisos para crear una identidad asignada por el usuario
- ¿Qué puedo hacer con GitHub Copilot en mi codespace?
¿Cuánto cuesta esta configuración?
Los precios por los recursos creados son los siguientes:
- El plan de App Service se crea en el nivel Básico y puede escalar o reducirse verticalmente. Consulte Precios de App Service.
- PostgreSQL, servidor flexible se crea en el nivel ampliable más bajo (Standard_B1ms), con el tamaño de almacenamiento mínimo, que se puede escalar o reducir verticalmente. Consulte los precios de Azure Database for PostgreSQL.
- La red virtual no incurre en cargo alguno, a menos que se configure alguna funcionalidad extra, como, por ejemplo, el emparejamiento. Vea Precios de Azure Virtual Network.
- La zona DNS privada conlleva un pequeño cargo. Vea Precios de Azure DNS.
¿Cómo me conecto al servidor de PostgreSQL protegido tras la red virtual con otras herramientas?
- Para tener un acceso básico desde una herramienta de línea de comandos, puede ejecutar
psqldesde el terminal de SSH de la aplicación. - Para conectarse desde una herramienta de escritorio, la máquina debe estar en la red virtual. Por ejemplo, podría ser una máquina virtual de Azure conectada a una de las subredes, o una máquina de una red local que tenga una conexión VPN de sitio a sitio a la red virtual de Azure.
- También puede integrar Azure Cloud Shell en la red virtual.
¿Cómo funciona el desarrollo de aplicaciones locales con Acciones de GitHub?
Tomando como ejemplo el archivo de flujo de trabajo generado automáticamente de App Service: cada git push inicia una nueva ejecución de compilación e implementación. Desde un clon local del repositorio de GitHub, realiza las actualizaciones deseadas y las inserta en GitHub. Por ejemplo:
git add .
git commit -m "<some-message>"
git push origin main
¿Cómo está configurado el ejemplo de Django para ejecutarse en Azure App Service?
La aplicación de ejemplo de Django configura los valores en el archivo azureproject/production.py para que se pueda ejecutar en Azure App Service. Estos cambios son comunes a la implementación de Django en producción y no son específicos de App Service.
Django valida el encabezado HTTP_HOST en las solicitudes entrantes. El código de ejemplo usa la variable de entorno
WEBSITE_HOSTNAMEen App Service para agregar el nombre de dominio de la aplicación al valor de ALLOWED_HOSTS de Django.# Configure the domain name using the environment variable # that Azure automatically creates for us. ALLOWED_HOSTS = [os.environ['WEBSITE_HOSTNAME']] if 'WEBSITE_HOSTNAME' in os.environ else []Django no admite servir archivos estáticos en producción. En este tutorial se usa WhiteNoise para permitir servir los archivos. El paquete WhiteNoise ya se instaló con requirements.txt y su middleware se ha agregado a la lista.
# WhiteNoise configuration MIDDLEWARE = [ 'django.middleware.security.SecurityMiddleware', # Add whitenoise middleware after the security middleware 'whitenoise.middleware.WhiteNoiseMiddleware',Los valores del archivo estático se configuran según la documentación de Django.
SESSION_ENGINE = "django.contrib.sessions.backends.cache" STATICFILES_STORAGE = 'whitenoise.storage.CompressedManifestStaticFilesStorage'
Para obtener más información, consulte Configuración de producción para aplicaciones de Django.
¿Cómo cambio la configuración de la aplicación SECRET_KEY a una referencia de Key Vault?
En los pasos anteriores del portal, puede cambiar SECRET_KEY a una referencia de Key Vault mediante la ejecución de los siguientes comandos de la CLI de Azure en Cloud Shell:
# Change the following variables to match your environment
SUBSCRIPTION_ID=<subscription-id>
RESOURCE_GROUP=<resource-group-name>
KEY_VAULT_NAME=<key-vault-name>
APP_SERVICE_NAME=<app-name>
SECRET_NAME=djangoSecretKey
# Set the subscription ID
az account set --subscription $SUBSCRIPTION_ID
# Assign 'Key Vault Secrets Officer' role to your user at the scope of the key vault
az role assignment create \
--assignee $(az ad signed-in-user show --query id -o tsv) \
--role $(az role definition list --name "Key Vault Secrets Officer" --query "[].id" -o tsv) \
--scope $(az keyvault show --name $KEY_VAULT_NAME --resource-group $RESOURCE_GROUP --query id --output tsv)
# Add the secret to the key vault
az keyvault secret set \
--vault-name $KEY_VAULT_NAME \
--name $SECRET_NAME \
--value $(python -c 'import secrets; print(secrets.token_hex())')
# Add Key Vault reference to the App Service configuration
az webapp config appsettings set \
--resource-group $RESOURCE_GROUP \
--name $APP_SERVICE_NAME \
--settings "SECRET_KEY=@Microsoft.KeyVault(SecretUri=https://$KEY_VAULT_NAME.vault.azure.net/secrets/$SECRET_NAME)"
También puede hacer lo mismo en el portal. Para más información, vea:
¿Cómo se depuran los errores durante la implementación de Acciones de GitHub?
Si se produce un error en un paso en el archivo de flujo de trabajo de GitHub generado automáticamente, intente modificar el comando con errores para generar una salida más detallada. Por ejemplo, puede obtener más resultados del comando python agregando la opción -d. Confirme e inserte los cambios para desencadenar otra implementación en App Service.
No tengo permisos para crear una identidad asignada por el usuario
Consulte Configuración de la implementación de Acciones de GitHub desde el centro de implementación.
¿Qué puedo hacer con GitHub Copilot en mi codespace?
Es posible que haya observado que la vista de chat de GitHub Copilot ya estaba allí cuando creó el codespace. Para mayor comodidad, incluimos la extensión de chat de GitHub Copilot en la definición del contenedor (consulte .devcontainer/devcontainer.json). Sin embargo, necesita una cuenta de GitHub Copilot (versión de prueba gratuita de 30 días disponible).
Algunas sugerencias para usted al hablar con GitHub Copilot:
- En una sola sesión de chat, las preguntas y respuestas se basan entre sí y puede ajustar sus preguntas para ajustar la respuesta que obtenga.
- De forma predeterminada, GitHub Copilot no tiene acceso a ningún archivo del repositorio. Para formular preguntas sobre un archivo, abra primero el archivo en el editor.
- Para permitir que GitHub Copilot tenga acceso a todos los archivos del repositorio al preparar sus respuestas, comience la pregunta con
@workspace. Para obtener más información, vea Use the @workspace agent. - En la sesión de chat, GitHub Copilot puede sugerir cambios y (con
@workspace) incluso donde realizar los cambios, pero no se permite realizar los cambios automáticamente. Es necesario agregar los cambios sugeridos y probarlos.
Pasos siguientes
Pase al tutorial siguiente para aprender a proteger la aplicación con un dominio personalizado y un certificado.
Obtenga información sobre cómo App Service ejecuta una aplicación de Python: