Configure data loss prevention policies for agents
With Copilot Studio, you can rapidly build and roll out high-value agents for your users that can connect with many data sources and services. Some of these sources and services might be external, non-Microsoft services, and might even include social networks, alongside connections to your organizational data.
Organizational data is the most important asset administrators are responsible for safeguarding. The ability to use that data in a protected way, while still connecting and interacting with other services and systems, is a cornerstone of data security.
Data loss prevention (DLP) policies let you govern how agents connect and interact with data and services, within and outside your organization. Administrators can configure Copilot Studio and Power Platform DLP policies in the Power Platform admin center.
Important
In early 2025, DLP policy enforcement for all tenants is set to Enabled by default, as announced in the message center alert MC973179: Copilot Studio - Upcoming updates to data loss prevention policy enforcement.
In January 2025:
- By default, enforcement for agents in all tenants is set to Soft-enabled (previously, enforcement was disabled by default):
- Existing agents that had DLP enforcement set to Disabled automatically change to Soft-enabled. New agents have DLP enforcement set to Soft-enabled by default, at creation.
- If a published agent has a DLP policy violation, users of the agent can continue to interact with the agent, however updates to the agent can't be published. The DLP policy violations must be resolved before the agent can be published.
- DLP policy violations are recorded for admins, and users and makers see DLP violation warnings. Users aren't blocked from using the agent.
- The PowerShell cmdlet can no longer be used to turn off enforcement.
Starting in February 2025:
- By default, enforcement for agents in all tenants will be set to Enabled – all published agents and updates to existing agents are subject to DLP policies that apply as defined in the tenant.
- The PowerShell cmdlet can no longer be used to turn enforcement on or off, and won't be supported after February 2025.
Learn about confirming enforcement in your tenant.
Prerequisites
- You should review concepts about DLP policies
- You must be a tenant admin or have the Environment Admin role
Copilot Studio connectors
Copilot Studio connectors can be classified within a DLP policy under the following data groups, which are presented in the Power Platform admin center when reviewing DLP policies:
- Business
- Non-business
- Blocked
You can use the connectors in DLP policies to protect your organization's data from any malicious or unintentional data exfiltration by your agent makers.
Important
Copilot Studio supports DLP policy enforcement in real time. Agent makers and users see error messages for any DLP policy violation.
In a DLP policy, the connectors must be in the same data group because data can't be shared among connectors that are in different groups.
You can configure DLP policies in the Power Platform admin center to block any of the following Copilot Studio connectors.
| Connector name | Use case |
|---|---|
| Application Insights in Copilot Studio | Block agent makers from connecting agents with Application Insights. |
| Chat without Microsoft Entra ID authentication in Copilot Studio | Block agent makers from publishing agents that aren't configured for authentication. Agent users must authenticate themselves to chat with the agent. For more information, see Data loss prevention example - Require user authentication in agents. |
| Direct Line channels in Copilot Studio | Block agent makers from enabling or using Direct Line channel. For example, the Demo website, Custom website, Mobile app, and other Direct Line channels would be blocked. |
| Facebook channel in Copilot Studio | Block agent makers from enabling or using the Facebook channel. |
| Knowledge source with SharePoint and OneDrive in Copilot Studio | Block agent makers from publishing agents configured with SharePoint as a knowledge source. Supports DLP connector endpoint filtering to allow or deny endpoints. |
| Knowledge source with documents in Copilot Studio | Block agent makers from publishing agents configured with documents as a knowledge source. |
| Knowledge source with public websites and data in Copilot Studio | Block agent makers from publishing agents configured with public websites as a knowledge source. Supports DLP connector endpoint filtering to allow or deny endpoints. |
| Microsoft Copilot Studio | Block agent makers from using event triggers in Copilot Studio agents. For more information, see Data loss prevention example - Block event triggers in agents. |
| Microsoft Teams channel in Copilot Studio | Block agent makers from enabling or using the Teams channel. |
| Omnichannel in Copilot Studio | Block agent makers from enabling or using the Omnichannel channel. |
| Skills with Copilot Studio | Block agent makers from using skills in Copilot Studio agents. For more information, see Data loss prevention example - Block skills in agents and Data loss prevention example - Block HTTP requests in agents. |
Example DLP policy configurations
To get started with Copilot Studio agent governance, review the following example scenarios:
- Data loss prevention example - Require user authentication in agents
- Data loss prevention example - Block SharePoint knowledge source in agents
- Data loss prevention example - Block Power Platform Connectors in agents
- Data loss prevention example - Block HTTP requests in agents
- Data loss prevention example - Block skills in agents
- Data loss prevention example - Block event triggers in agents
- Data loss prevention example - Block channels to disable agent publish
Use PowerShell to enable and administer DLP enforcement for agents in your organization
You can configure whether DLP policies should be applied to your agents with the PowerAppDlpErrorSettings and PowerVirtualAgentsDlpEnforcement PowerShell cmdlets.
You can:
- Confirm if DLP policies are enforced for agents in your tenant.
- Switch DLP policy enforcement to auditing mode (
-Mode SoftEnabled) so agent makers can see errors, but aren't prevented from performing actions that DLP policy enforcement would block. - Turn DLP enforcement on or off, to show DLP enforcement errors, and prevent agent makers from publishing DLP-affected agents or configuring DLP-related settings.
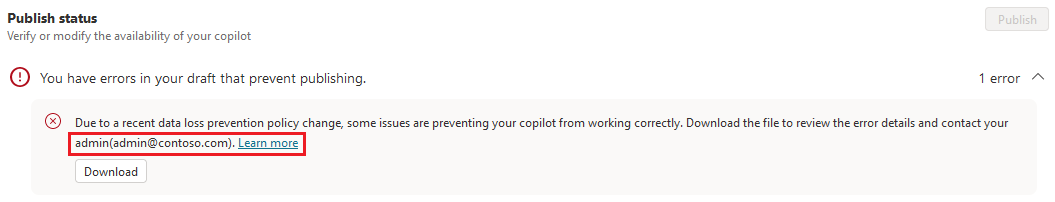
- Add and update the learn-more and contact email links that are shown to agent makers when Copilot Studio triggers a DLP policy violation.
Important
Before using the PowerShell cmdlets, or the example scripts shown here, ensure you install the following modules using PowerShell.
- Microsoft.PowerApps.Administration.PowerShell
- Microsoft.PowerApps.PowerShell -AllowClobber
You need to be a tenant admin to use the cmdlets.
Typically, you would use these cmdlets in accordance with a DLP rollout process, which might consist of the following steps, in order:
Add or update the learn-more and admin contact email links that are shown in DLP errors for agent makers.
Determine which (if any) agents currently have DLP policy enforcement enabled.
Use auditing mode so makers can see DLP errors in the Copilot Studio web and Teams apps.
Mitigate risk by contacting makers and informing them about the best course of action for their app or flow.
Turn on strict DLP policy enforcement for agents.
Important
Agent DLP policy enforcement exemption is no longer supported. Agents that were previously exempted from DLP enforcement will have their enforcement set to Soft-enabled in January 2025, and set to Enabled in February 2025.
Add and update the learn-more and admin contact email links
You can use the Set-PowerAppDlpErrorSettings PowerShell cmdlet to add an email address and a "Learn more" link to the DLP error messages.
To add the email address and learn-more link for the first time, run the following PowerShell script, replacing the values for the <email>, <URL>, and <tenant ID> parameters with your own.
$ContactDetails = [pscustomobject] @{
Enabled=$true
Email="<email>"
}
$ErrorMessageDetails = [pscustomobject] @{
Enabled=$true
Url="<URL>"
}
$ErrorSettingsObj = [pscustomobject] @{
ErrorMessageDetails=$ErrorMessageDetails
ContactDetails=$ContactDetails
}
New-PowerAppDlpErrorSettings -TenantId "<tenant ID>" -ErrorSettings $ErrorSettingsObj
To update an existing configuration, use the same PowerShell script, and replace New-PowerAppDlpErrorSettings with Set-PowerAppDlpErrorSettings.
Warning
These settings apply to all Power Platform apps within the specified tenant.
Configure DLP enforcement for agents
You can enable, disable, configure, and audit DLP enforcement within Copilot Studio with the PowerVirtualAgentsDlpEnforcement cmdlet.
In any of the following examples, replace (or declare) <tenant ID> with your tenant's ID.
You can scope to agents created after a certain date by replacing <date> with a date in the format MM-DD-YYYY. To remove the scope, delete the -OnlyForBotsCreatedAfter parameter and its value.
Confirm DLP policy enforcement for agents
By default, DLP policy enforcement for agents is set to auditing or "soft" mode.
Run the following PowerShell cmdlet to check the DLP policy enforcement status for a tenant.
Get-PowerVirtualAgentsDlpEnforcement -TenantId <tenant ID>
Note
If DLP isn't configured for Copilot Studio, the response from the cmdlet is empty.
Use auditing mode to see DLP errors in Copilot Studio
Run the following PowerShell script to enable DLP policies in auditing or "soft" mode. When this mode is active, agent makers can see DLP-related error messages when configuring agents in Copilot Studio, but it doesn't block them from performing DLP-related actions. However, makers can't publish agents while this mode is active.
Set-PowerVirtualAgentsDlpEnforcement -TenantId <tenant ID> -Mode SoftEnabled
To find agents that your organization's DLP policies might affect, you can:
Use the Power BI dashboard of the Center of Excellence (CoE) Starter Kit to get a list of agents in your organization. Go to the Copilot Studio overview page on the CoE Dashboard to see the agents and environment names in your organization.
Run a campaign with the agent makers in your organization to address DLP errors or updated DLP policies. You can download all agent DLP errors by selecting Details in the error notification banner and selecting Download from the error message details.
Turn on DLP enforcement for agents
Warning
Before turning on DLP policy enforcement, ensure you know which agents are likely to report errors to users due to DLP policy violations.
You can run the following PowerShell command to enforce DLP policies in Copilot Studio. Agent makers are prevented from performing actions that would violate DLP policies, and users see error messages for any violations.
Set-PowerVirtualAgentsDlpEnforcement -TenantId <tenant ID> -Mode Enabled -OnlyForBotsCreatedAfter <date>