Security baselines assessment
Applies to:
- Microsoft Defender Vulnerability Management
- Microsoft Defender XDR
- Microsoft Defender for Servers Plan 2
Note
To use this feature you'll require Microsoft Defender Vulnerability Management Standalone or if you're already a Microsoft Defender for Endpoint Plan 2 customer, the Defender Vulnerability Management add-on.
Instead of running never-ending compliance scans, security baselines assessment helps you to continuously and effortlessly monitor your organization's security baselines compliance and identify changes in real time.
A security baseline profile is a customized profile that you can create to assess and monitor endpoints in your organization against industry security benchmarks. When you create a security baseline profile, you're creating a template that consists of multiple device configuration settings and a base benchmark to compare against.
Security baselines provide support for Center for Internet Security (CIS) benchmarks for Windows 10, Windows 11, and Windows Server 2008 R2 and above, as well as Security Technical Implementation Guides (STIG) benchmarks for Windows 10 and Windows Server 2019.
Note
The benchmarks currently only support Group Policy Object (GPO) configurations and not Microsoft Configuration Manager (Intune).
Tip
Did you know you can try all the features in Microsoft Defender Vulnerability Management for free? Find out how to sign up for a free trial.
Note
Security baseline assessment is not supported when DFSS (Dynamic Fair Share Scheduling) is enabled on Windows Server 2012 R2.
Get started with security baselines assessment
Go to Vulnerability management > Baselines assessment in the Microsoft Defender portal.
Select the Profiles tab at the top, then select the Create profile button.
Enter a name and description for your security baselines profile and select Next.
On the Baseline profile scope page set the profile settings such as software, base benchmark (CIS or STIG), and the compliance level and select Next.
Select the configurations you want to include in the profile.
Note
Some configurations might not be included in the baseline assessment due to manual checking requirement or the configurations are unsupported. These configurations are marked as needing Manual check in the list and these will not be automatically assessed for compliance.
Select Customize if you want to change the threshold configuration value for your organization.
Select Next to choose the device groups and device tags you want to include in the baseline profile. The profile will be automatically applied to devices added to these groups in the future.
Select Next to review the profile.
Select Submit to create your profile.
On the final page, select View profile page to see the assessment results.
Tip
You can create multiple profiles for the same operating system with various customizations.
When you customize a configuration an icon will appear beside it to indicate that it has been customized and is no longer using the recommended value. Select the reset button to revert to the recommended value.
Useful icons to be aware of:
 - This configuration has been customized before. When creating a new profile if you select Customize, you'll see the available variations you can choose from.
- This configuration has been customized before. When creating a new profile if you select Customize, you'll see the available variations you can choose from.
 - This configuration has been customized and is not using the default value.
- This configuration has been customized and is not using the default value.
Security baselines assessment overview
On the security baselines assessment overview page you can view device compliance, profile compliance, top failing devices and top misconfigured devices.
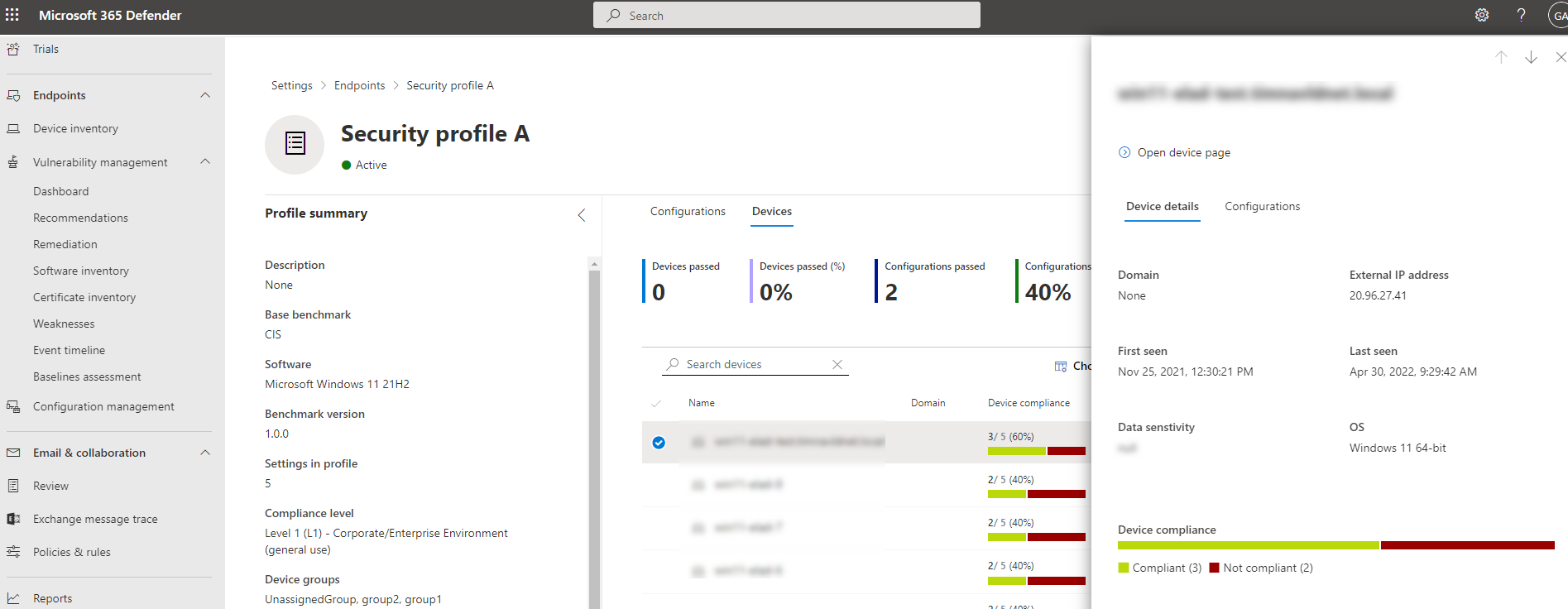
Review security baseline profile assessment results
In the Profiles page, select any of your profiles to open a flyout with additional information.
Select Open profile page. The profile page contains two tabs Configurations and Devices.
View by configuration
In the Configurations tab, you can review the list of configurations and assess their reported compliance state.
By selecting a configuration in the list, you'll see a flyout with details for the policy setting, including the recommended value (the expected value range for a device to be considered compliant) and the source used to determine the current device settings.
The Devices tab shows a list of all applicable devices and their compliance state against this specific configuration. For each device, you can use the current value detected to see why it's compliant or non compliant.
View by device
In the main Devices tab, you can review the list of devices and assess their reported compliance state.
By selecting a device in the list, you'll see a flyout with additional details.
Select the Configuration tab to view the compliance of this specific device against all the profile configurations.
At the top of the device side panel, select Open device page to go to the device page in the device inventory. The device page displays the Baseline compliance tab that provides granular visibility into the compliance of the device.
By selecting a configuration in the list, you'll see a flyout with compliance details for the policy setting on this device.
Create and manage exceptions
You may have cases where you don't want to assess specific configurations on certain devices. For example, a device could be under third party control or it could have an alternate mitigation already in place. In these situations, you can add exceptions to exclude the assessment of specific configurations on a device.
Devices included in exceptions won't be assessed for the specified configurations in the baseline profiles. This means it won't affect an organization's metrics and score, and it can help provide organizations with a clearer view of their compliance.
To view exceptions:
- Go to Vulnerability management > Baselines assessment in the Microsoft Defender portal.
- Select the Exceptions tab at the top
To add a new exception:
On the Exceptions tab select the Create button.
Fill in the requested details, including the justification reason, and duration.
Select Next.
On the Configuration scope page choose the software, base benchmark, and the compliance level and select Next.
Select the configurations you want to add to the exception.
Select Next to choose the devices you want to include in the exception. The exception will be automatically applied to devices.
Select Next to review the exception.
Select Submit to create your exception.
On the final page, select View all exceptions to return to the exceptions page.
In the Exceptions page, select any of your exceptions to open a flyout pane where you can see the status, edit or delete your exception:
Use advanced hunting
You can run advanced hunting queries on the following tables to gain visibility on security baselines in your organization:
- DeviceBaselineComplianceProfiles: provides details on created profiles.
- DeviceBaselineComplianceAssessment: device compliance related information.
- DeviceBaselineComplianceAssessmentKB: general settings for CIS and STIG benchmarks (not related to any device).
Known issues with data collection
We are aware of known issues affecting data collection in certain versions of the CIS, STIG, and Microsoft benchmarks. The issues might cause inaccurate or incomplete results when running tests in these versions. These issues are being actively worked on and will be resolved in future updates.
We recommend to exclude the affected tests from the benchmark profile while running the assessment to avoid the impact of these issues.
If your benchmark version is not listed below and you're experiencing issues, please contact Microsoft Support to help us investigate further and assist you with a resolution.
The following CIS, Microsoft, and STIG benchmarks are affected:
CIS
- CIS 17.1.1
- CIS 17.2.1
- CIS 17.3.1 to 17.3.2
- CIS 17.5.1 to 17.5.6
- CIS 17.6.1 to 17.6.4
- CIS 17.7.1 to 17.7.5
- CIS 17.8.1
- CIS 17.9.1 to 17.9.5
CIS Checks Additions
- CIS 2.3.7.3 to 2.3.7.5
- CIS 2.3.10.1
- CIS 1.1.5
Microsoft Checks
- Microsoft 2.1
- Microsoft 2.10
- Microsoft 2.12 to 2.30
- Microsoft 2.33 to 2.37
- Microsoft 2.40 to 2.50
- Microsoft 3.55
- Microsoft 3.57
- Microsoft 3.60
- Microsoft 3.72
Microsoft Certificate Store Checks for Windows and Windows Server
- MCS 1.1 for Windows 10 1909 (Temporary) 1.1.5
- MCS 2.0 for Windows 10 1909 (Temporary) 1.1.5
- MCS 1.1 for Windows 10 20H2 (Temporary) 1.1.5
- MCS 2.0 for Windows 10 20H2 (Temporary) 1.1.5
- MCS 2.0 for Windows 10 v21H2 1.1.5
- MCS 2.0 for Windows 10 v22H2 1.1.5
- MCS 2.0 for Windows 11 1.1.5
- MCS 2.0 for Windows 11 23H2 1.1.5
- MCS 2.0 for Windows Server 2022 1.1.5
- MCS 2.0 for Windows Server 2022 Domain Controller 1.1.5
- MCS 2.0 for Windows Server 2019 1.1.5
- MCS 2.0 for Windows Server 2019 Domain Controller 1.1.5
- MCS 2.0 for Windows Server 2016 1.1.5
- MCS 2.0 for Windows Server 2016 Domain Controller 1.1.5
- MCS 2.0 for Windows Server 2012_R2 1.1.5
- MCS 1.1 for Windows Server 2008_R2 (Temporary) 1.1.5
- MCS 2.0 for Windows Server 2022 Domain Controller 2.3.10.1
- MCS 2.0 for Windows Server 2019 Domain Controller 2.3.10.1
- MCS 2.0 for Windows Server 2016 Domain Controller 2.3.10.1
STIG List
- STIG SV-205678r569188
- STIG SV-220746r569187
- STIG SV-220754r569187
- STIG SV-220757r569187
- STIG SV-220760r569187
- STIG SV-220767r569187
- STIG SV-220768r569187
- STIG SV-220768r851975
- STIG SV-220775r569187
- STIG SV-220775r851978
- STIG SV-220786r569187
- STIG SV-220769r569187
- STIG SV-225273r569185
- STIG SV-225281r569185
- STIG SV-225284r569185
- STIG SV-225287r569185
- STIG SV-225292r569185
- STIG SV-225294r569185
- STIG SV-225294r852189
- STIG SV-225295r569185
- STIG SV-225302r569185
- STIG SV-225302r852194
- STIG SV-226092r569184
- STIG SV-226092r794343
- STIG SV-226099r569184
- STIG SV-226099r794279
- STIG SV-226102r569184
- STIG SV-226102r794335
- STIG SV-226107r569184
- STIG SV-226107r794336
- STIG SV-226110r569184
- STIG SV-226110r794366
- STIG SV-226117r569184
- STIG SV-226117r794356
- STIG SV-226117r852079
- STIG SV-226109r569184
- STIG SV-226109r794353
- STIG SV-226109r852074
- STIG SV-226063r569184
- STIG SV-226063r794292
- STIG SV-254271r848629
- STIG SV-224873r569186