Overview of Microsoft Defender for Endpoint Plan 1
Applies to
Microsoft Defender for Endpoint is an enterprise endpoint security platform designed to help organizations to prevent, detect, investigate, and respond to advanced threats. Defender for Endpoint is now available in two plans:
- Defender for Endpoint Plan 1, described in this article; and
- Defender for Endpoint Plan 2, generally available, and formerly known as Defender for Endpoint.
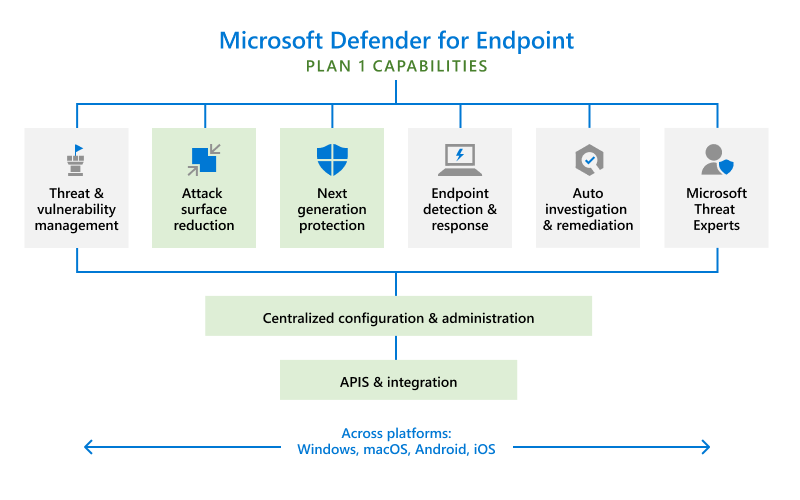
The green boxes in the following image depict what's included in Defender for Endpoint Plan 1:
Use this guide to:
- Get an overview of what's included in Defender for Endpoint Plan 1
- Learn how to set up and configure Defender for Endpoint Plan 1
- Get started using the Microsoft Defender portal, where you can view incidents and alerts, manage devices, and use reports about detected threats
- Get an overview of maintenance and operations
For minimum requirements for Microsoft Defender for Endpoint, see Microsoft Defender for Endpoint requirements.
Defender for Endpoint Plan 1 capabilities
Defender for Endpoint Plan 1 includes the following capabilities:
- Next-generation protection that includes industry-leading, robust antimalware and antivirus protection
- Manual response actions, such as sending a file to quarantine, that your security team can take on devices or files when threats are detected
- Attack surface reduction capabilities that harden devices, prevent zero-day attacks, and offer granular control over endpoint access and behaviors
- Centralized configuration and management with the Microsoft Defender portal and integration with Microsoft Intune
The following sections provide more details about these capabilities.
Next-generation protection
Next-generation protection includes robust antivirus and antimalware protection. With next-generation protection, you get:
- Behavior-based, heuristic, and real-time antivirus protection
- Cloud-delivered protection, which includes near-instant detection and blocking of new and emerging threats
- Dedicated protection and product updates, including updates related to Microsoft Defender Antivirus
To learn more, see Next-generation protection overview.
Manual response actions
Manual response actions are actions that your security team can take when threats are detected on endpoints or in files. Defender for Endpoint includes certain manual response actions that can be taken on a device that is detected as potentially compromised or has suspicious content. You can also run response actions on files that are detected as threats. The following table summarizes the manual response actions that are available in Defender for Endpoint Plan 1.
| File/Device | Action | Description |
|---|---|---|
| Device | Run antivirus scan | Starts an antivirus scan. If any threats are detected on the device, those threats are often addressed during an antivirus scan. |
| Device | Isolate device | Disconnects a device from your organization's network while retaining connectivity to Defender for Endpoint. This action enables you to monitor the device and take further action if needed. |
| File | Add an indicator to block or allow a file | Block indicators prevent portable executable files from being read, written, or executed on devices. Allow indicators prevent files from being blocked or remediated. |
To learn more, see the following articles:
Attack surface reduction
Your organization's attack surfaces are all the places where you're vulnerable to cyberattacks. With Defender for Endpoint Plan 1, you can reduce your attack surfaces by protecting the devices and applications that your organization uses. The attack surface reduction capabilities that are included in Defender for Endpoint Plan 1 are described in the following sections.
- Overview of Microsoft Defender for Endpoint Plan 1
To learn more about attack surface reduction capabilities in Defender for Endpoint, see Overview of attack surface reduction.
Attack surface reduction rules
Attack surface reduction rules target certain software behaviors that are considered risky. Such behaviors include:
- Launching executable files and scripts that attempt to download or run other files
- Running obfuscated or otherwise suspicious scripts
- Initiating behaviors that apps don't usually initiate during normal work
Legitimate business applications can exhibit such software behaviors; however, these behaviors are often considered risky because they are commonly abused by attackers through malware. Attack surface reduction rules can constrain risky behaviors and help keep your organization safe.
To learn more, see Use attack surface reduction rules to prevent malware infection.
Ransomware mitigation
With controlled folder access, you get ransomware mitigation. Controlled folder access allows only trusted apps to access protected folders on your endpoints. Apps are added to the trusted apps list based on their prevalence and reputation. Your security operations team can add or remove apps from the trusted apps list, too.
To learn more, see Protect important folders with controlled folder access.
Device control
Sometimes threats to your organization's devices come in the form of files on removable drives, such as USB drives. Defender for Endpoint includes capabilities to help prevent threats from unauthorized peripherals from compromising your devices. You can configure Defender for Endpoint to block or allow removable devices and files on removable devices.
To learn more, see Control USB devices and removable media.
Web protection
With web protection, you can protect your organization's devices from web threats and unwanted content. Web protection includes web threat protection and web content filtering.
- Web threat protection prevents access to phishing sites, malware vectors, exploit sites, untrusted or low-reputation sites, and sites that you explicitly block.
- Web content filtering prevents access to certain sites based on their category. Categories can include adult content, leisure sites, legal liability sites, and more.
To learn more, see web protection.
Network protection
With network protection, you can prevent your organization from accessing dangerous domains that might host phishing scams, exploits, and other malicious content on the Internet.
To learn more, see Protect your network.
Network firewall
With network firewall protection, you can set rules that determine which network traffic is permitted to flow to or from your organization's devices. With your network firewall and advanced security that you get with Defender for Endpoint, you can:
- Reduce the risk of network security threats
- Safeguard sensitive data and intellectual property
- Extend your security investment
To learn more, see Windows Defender Firewall with advanced security.
Application control
Application control protects your Windows endpoints by running only trusted applications and code in the system core (kernel). Your security team can define application control rules that consider an application's attributes, such as its codesigning certificates, reputation, launching process, and more. Application control is available in Windows 10 or later.
To learn more, see Application control for Windows.
Centralized management
Defender for Endpoint Plan 1 includes the Microsoft Defender portal, which enables your security team to view current information about detected threats, take appropriate actions to mitigate threats, and centrally manage your organization's threat protection settings.
To learn more, see Microsoft Defender portal overview.
Role-based access control
Using role-based access control (RBAC), your security administrator can create roles and groups to grant appropriate access to the Microsoft Defender portal (https://security.microsoft.com). With RBAC, you have fine-grained control over who can access the Defender for Cloud, and what they can see and do.
To learn more, see Manage portal access using role-based access control.
Important
Starting February 16, 2025, new Microsoft Defender for Endpoint customers will only have access to the Unified Role-Based Access Control (URBAC). Existing customers keep their current roles and permissions. For more information, see URBAC Unified Role-Based Access Control (URBAC) for Microsoft Defender for Endpoint
Reporting
The Microsoft Defender portal (https://security.microsoft.com) provides easy access to information about detected threats and actions to address those threats.
- The Home page includes cards to show at a glance which users or devices are at risk, how many threats were detected, and what alerts/incidents were created.
- The Incidents & alerts section lists any incidents that were created as a result of triggered alerts. Alerts and incidents are generated as threats are detected across devices.
- The Action center lists remediation actions that were taken. For example, if a file is sent to quarantine, or a URL is blocked, each action is listed in the Action center on the History tab.
- The Reports section includes reports that show threats detected and their status.
To learn more, see Get started with Microsoft Defender for Endpoint Plan 1.
APIs
With the Defender for Endpoint APIs, you can automate workflows and integrate with your organization's custom solutions.
To learn more, see Defender for Endpoint APIs.
- Microsoft Defender for Servers Plan 1 or Plan 2 (recommended for enterprise customers) as part of the Defender for Cloud offering. To learn more. see Overview of Microsoft Defender for Servers.
- Microsoft Defender for Endpoint Server (recommended for enterprise customers). To learn more, see Defender for Endpoint onboarding Windows Server.
- Microsoft Defender for Business servers (for small and medium-sized businesses who have Microsoft Defender for Business). To learn more, see How to get Microsoft Defender for Business servers.
See Microsoft licensing and product terms.
Next steps
- Set up and configure Defender for Endpoint Plan 1
- Get started with Defender for Endpoint Plan 1
- Manage Defender for Endpoint Plan 1
- Learn about exclusions for Microsoft Defender for Endpoint and Microsoft Defender Antivirus
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender for Endpoint Tech Community.