Optimize your security operations
Security operations center (SOC) teams look for ways to improve processes and outcomes and ensure you have the data needed to address risks without extra ingestion costs. SOC teams want to make sure that you have all the necessary data to act against risks, without paying for more data than needed. At the same time, SOC teams must also adjust security controls as threats and business priorities change, doing so quickly and efficiently to maximize your return on investment.
SOC optimizations are actionable recommendations that surface ways that you can optimize your security controls, gaining more value from Microsoft security services as time goes on. Recommendations help you reduce costs without affecting SOC needs or coverage, and can help you add security controls and data where needed. These optimizations are tailored to your environment and based on your current coverage and threat landscape.
Use SOC optimization recommendations to help you close coverage gaps against specific threats and tighten your ingestion rates against data that doesn't provide security value. SOC optimizations help you optimize your Microsoft Sentinel workspace, without having your SOC teams spend time on manual analysis and research.
Important
Microsoft Sentinel is generally available within Microsoft's unified security operations platform in the Microsoft Defender portal. For preview, Microsoft Sentinel is available in the Defender portal without Microsoft Defender XDR or an E5 license. For more information, see Microsoft Sentinel in the Microsoft Defender portal.
Watch the following video for an overview and demo of SOC optimization in the Microsoft Defender portal. If you just want a demo, jump to minute 8:14.
Prerequisites
SOC optimization uses standard Microsoft Sentinel roles and permissions. For more information, see Roles and permissions in Microsoft Sentinel.
To use SOC optimization in the Defender portal, onboard Microsoft Sentinel to the Defender portal. For more information, see Connect Microsoft Sentinel to the Microsoft Defender portal.
Access the SOC optimization page
Use one of the following tabs, depending on whether you're working in the Azure portal or Defender portal. When your workspace is onboarded for unified security operations, SOC optimizations include coverage from across Microsoft security services.
In Microsoft Sentinel in the Azure portal, under Threat management, select SOC optimization.
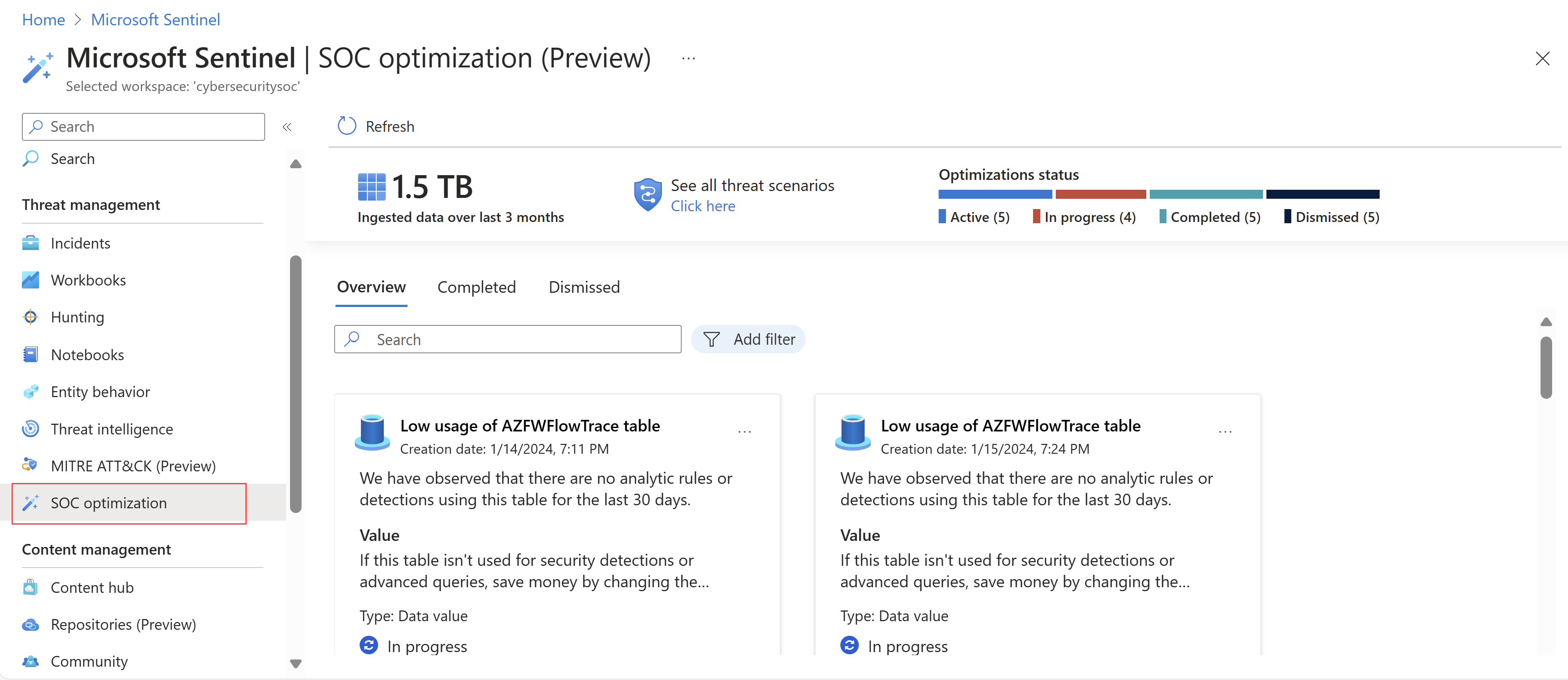
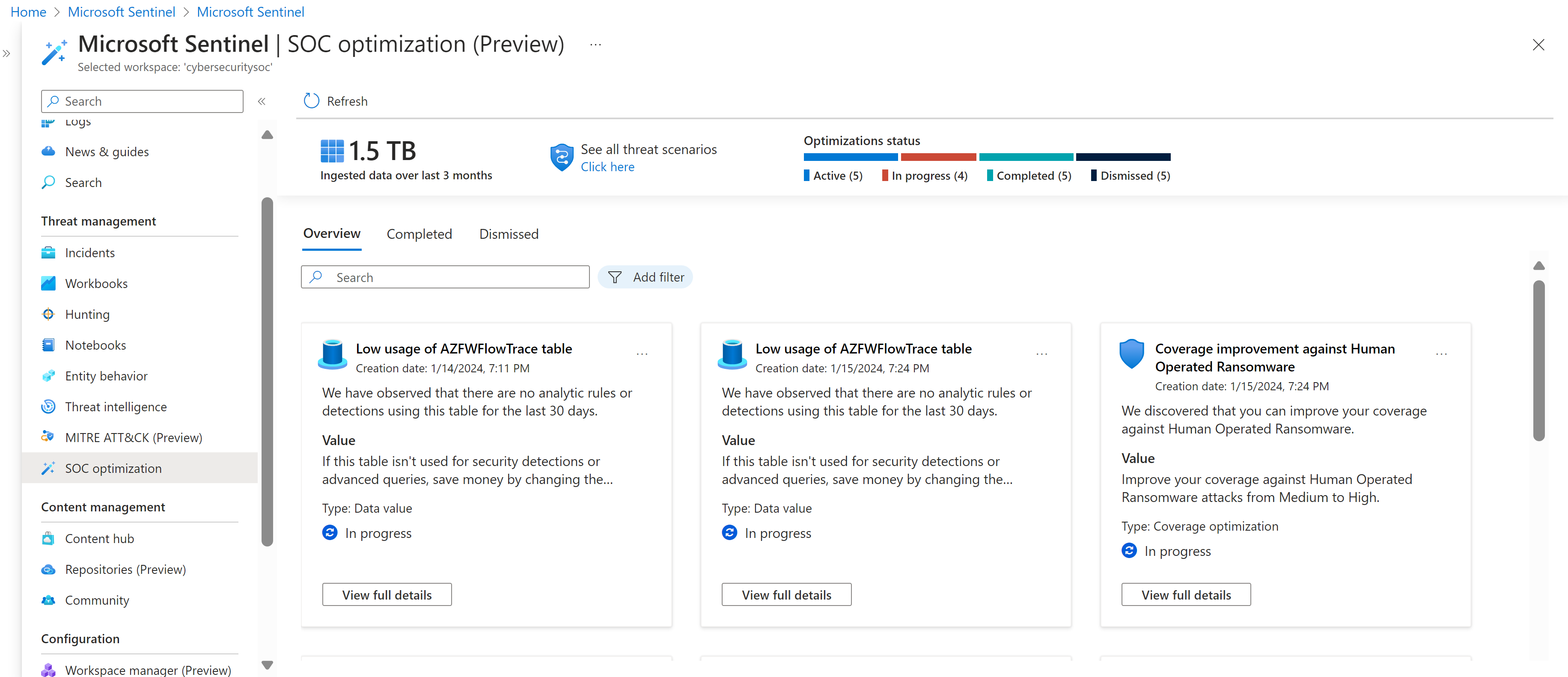
Understand SOC optimization overview metrics
Optimization metrics shown at the top of the Overview tab give you a high level understanding of how efficiently you're using your data, and will change over time as you implement recommendations.
Supported metrics at the top of the Overview tab include:
| Title | Description |
|---|---|
| Ingested data over the last 3 months | Shows the total data ingested in your workspace over the last three months. |
| Optimizations status | Shows the number of recommended optimizations that are currently active, completed, and dismissed. |
Select See all threat scenarios to view the full list of relevant threats, percentages of active and recommended analytics rules, and coverage levels.
View and manage optimization recommendations
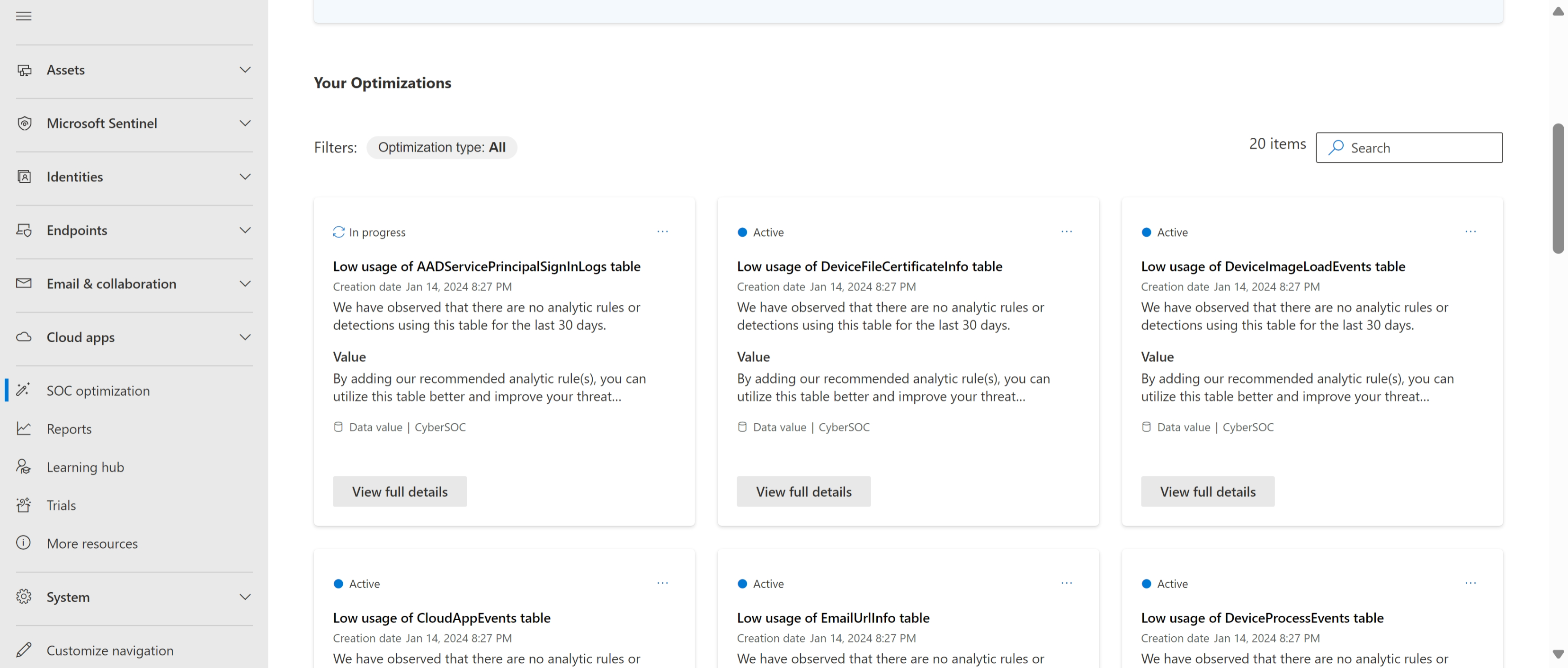
In the Azure portal, SOC optimization recommendations are listed on the SOC optimization > Overview tab.
For example:
SOC optimization recommendations are calculated every 24 hours. Each optimization card includes the status, title, the date it was created, a high-level description, and the workspace it applies to.
Filter optimizations
Filter the optimizations based on optimization type, or search for a specific optimization title using the search box on the side. Optimization types include:
Coverage: Includes threat-based recommendations for adding security controls to help close coverage gaps for various types of attacks.
Data value: Includes recommendations that suggest ways to improve your data usage for maximizing security value from ingested data, or suggest a better data plan for your organization.
View optimization details and take action
Select one of the following tabs, depending on the portal you're using:
In each optimization card, select View details to see a full description of the observation that led to the recommendation, and the value you see in your environment when that recommendation is implemented.
Scroll down to the bottom of the details pane for a link to where you can take the recommended actions. For example:
- If an optimization includes recommendations to add analytics rules, select Go to Content Hub.
- If an optimization includes recommendations to move a table to basic logs, select Change plan.
If you install an analytics rule template from the Content hub without the solution installed, only the installed template appears in the solution.
Install the full solution to see all available content items from the selected solution. For more information, see Discover and manage Microsoft Sentinel out-of-the-box content.
Manage optimizations
By default, optimization statuses are Active. Change their statuses as your teams progress through triaging and implementing recommendations.
Either select the options menu or select View details to take one of the following actions:
| Action | Description |
|---|---|
| Complete | Complete an optimization when you completed each recommended action. If a change in your environment is detected that makes the recommendation irrelevant, the optimization is automatically completed and moved to the Completed tab. For example, you might have an optimization related to a previously unused table. If your table is now used in a new analytics rule, the optimization recommendation is now irrelevant. In such cases, a banner shows in the Overview tab with the number of automatically completed optimizations since your last visit. |
| Mark as in progress / Mark as active | Mark an optimization as in progress or active to notify other team members that you're actively working on it. Use these two statuses flexibly, but consistently, as needed for your organization. |
| Dismiss | Dismiss an optimization if you're not planning to take the recommended action and no longer want to see it in the list. |
| Provide feedback | We invite you to share your thoughts on the recommended actions with the Microsoft team! When sharing your feedback, be careful not to share any confidential data. For more information, see Microsoft Privacy Statement. |
View completed and dismissed optimizations
If you marked a specific optimization as Completed or Dismissed, or if an optimization is automatically completed, it's listed on the Completed and Dismissed tabs, respectively.
From here, either select the options menu or select View full details to take one of the following actions:
Reactivate the optimization, sending it back to the Overview tab. Reactivated optimizations are recalculated to provide the most updated value and action. Recalculating these details can take up to an hour, so wait before checking the details and recommended actions again.
Reactivated optimizations might also move directly to the Completed tab if, after recalculating the details, they're found to be no longer relevant.
Provide further feedback to the Microsoft team. When sharing your feedback, be careful not to share any confidential data. For more information, see Microsoft Privacy Statement.
SOC optimization usage flow
This section provides a sample flow for using SOC optimizations, from either the Defender or Azure portal:
On the SOC optimization page, start by understanding the dashboard:
- Observe the top metrics for overall optimization status.
- Review optimization recommendations for data value and threat-based coverage.
Use the optimization recommendations to identify tables with low usage, indicating that they're not being used for detections. Select View full details to see the size and cost of unused data. Consider one of the following actions:
Add analytics rules to use the table for enhanced protection. To use this option, select Go to the Content Hub to view and configure specific out-of-the-box analytic rule templates that use the selected table. In the Content hub, you don't need to search for the relevant rule, as you're taken directly to the relevant rule.
If new analytic rules require extra log sources, consider ingesting them to improve threat coverage.
For more information, see Discover and manage Microsoft Sentinel out-of-the-box content and Detect threats out-of-the-box.
Change your commitment tier for cost savings. For more information, see Reduce costs for Microsoft Sentinel.
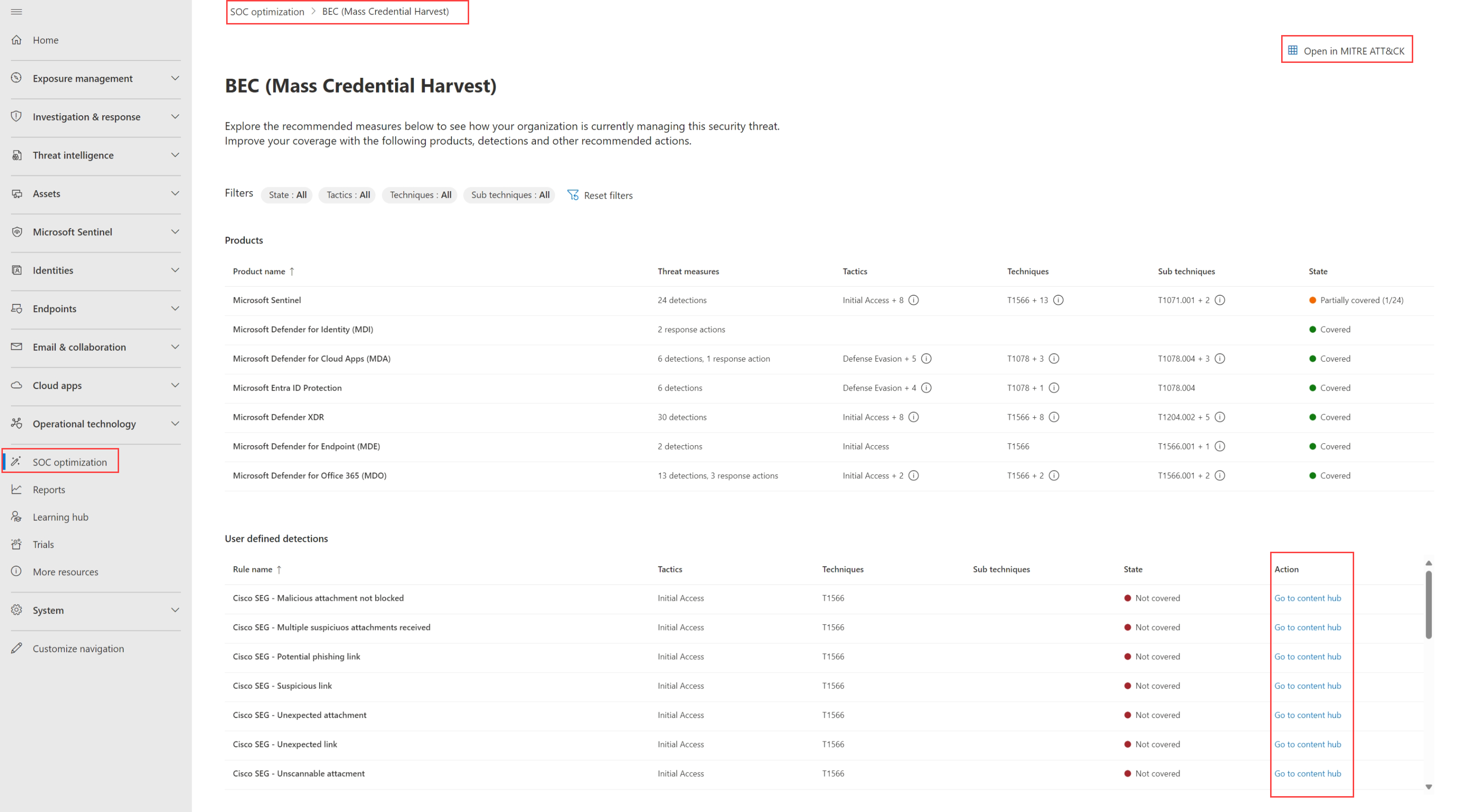
Use the optimization recommendations to improve coverage against specific threats. For example, for a human-operated ransomware optimization:
Select View full details to see the current coverage and suggested improvements.
Select View all MITRE ATT&CK technique improvement to drill down and analyze the relevant tactics and techniques, helping you understand the coverage gap.
Select Go to Content hub to view all recommended security content, filtered specifically for this optimization.
After configuring new rules or making changes, mark the recommendation as completed or let the system update automatically.