Create and customize Microsoft Sentinel playbooks from templates
A playbook template is a prebuilt, tested, and ready-to-use automation workflow for Microsoft Sentinel that can be customized to meet your needs. Templates can also serve as a reference for best practices when developing playbooks from scratch, or as inspiration for new automation scenarios.
Playbook templates aren't active playbooks themselves, and you must create an editable copy for your needs.
Many playbook templates are developed by the Microsoft Sentinel community, independent software vendors (ISVs), and Microsoft's own experts, based on popular automation scenarios used by security operations centers around the world.
Important
Playbook templates are currently in PREVIEW. See the Supplemental Terms of Use for Microsoft Azure Previews for additional legal terms that apply to Azure features that are in beta, preview, or otherwise not yet released into general availability.
Microsoft Sentinel is generally available within Microsoft's unified security operations platform in the Microsoft Defender portal. For preview, Microsoft Sentinel is available in the Defender portal without Microsoft Defender XDR or an E5 license. For more information, see Microsoft Sentinel in the Microsoft Defender portal.
Prerequisites
To create and manage playbooks, you need access to Microsoft Sentinel with one of the following Azure roles:
- Logic App Contributor, to edit and manage logic apps
- Logic App operator, to read, enable, and disable logic apps
For more information, see Microsoft Sentinel playbook prerequisites.
We recommend that you read Azure Logic Apps for Microsoft Sentinel playbooks before creating your playbook.
Access playbook templates
Access playbook templates from the following sources:
| Location | Description |
|---|---|
| Microsoft Sentinel Automation page | The Playbook templates tab lists all installed playbooks. Create one or more active playbooks using the same template. When we publish a new version of a template, any active playbooks created from that template have an extra label added in the Active playbooks tab to indicate that an update is available. |
| Microsoft Sentinel Content hub page | Playbook templates are available as part of product solutions or standalone content installed from the Content hub. For more information, see: About Microsoft Sentinel content and solutions Discover and manage Microsoft Sentinel out-of-the-box content |
| GitHub | The Microsoft Sentinel GitHub repository contains many other playbook templates. Select Deploy to Azure to deploy a template to your Azure subscription. |
Technically, a playbook template is an Azure Resource Manager (ARM) template, which consists of several resources: an Azure Logic Apps workflow and API connections for each connection involved.
This article focuses on deploying a playbook template from the Playbook templates tab under Automation.
Explore playbook templates
For Microsoft Sentinel in the Azure portal, select the Content management > Content hub page. For Microsoft Sentinel in the Defender portal, select Microsoft Sentinel > Content management > Content hub.
On the Content hub page, select Content type to filter for Playbook. This filtered view lists all the solutions and standalone content that include one or more playbook templates. Install the solution or standalone content to get the template.
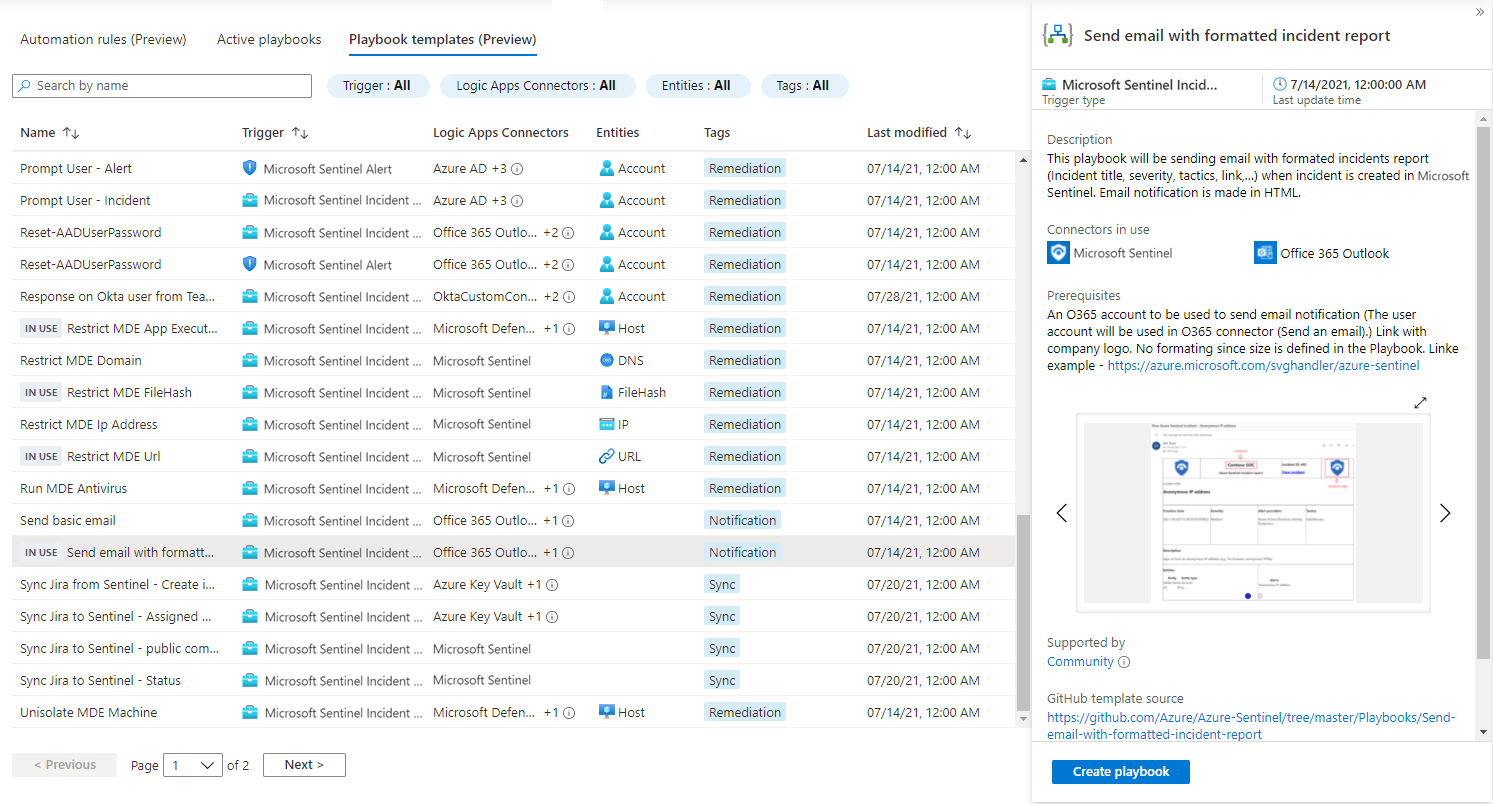
Then, select Configuration > Automation > Playbook templates tab to view the installed templates. For example:
To find a playbook template that fits your requirements, filter the list by the following criteria:
| Filter | Description |
|---|---|
| Trigger | Filter by how the playbook is triggered, including incidents, alerts, or entities. For more information, see Supported Microsoft Sentinel triggers. |
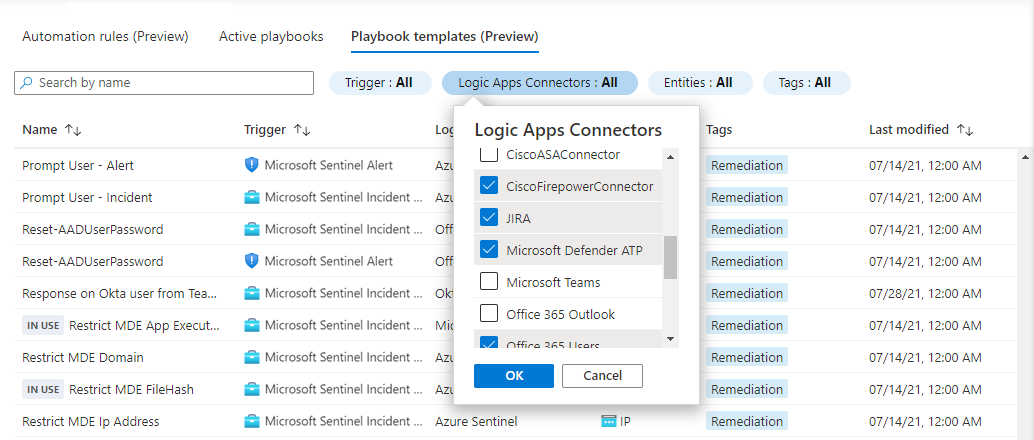
| Logic Apps connectors | Filter by the external services the playbooks interact with. During the deployment process, each connector needs to assume an identity to authenticate to the external service. |
| Entities | Filter by the entity types that the playbook expects to find in the incident. For example, a playbook that tells a firewall to block an IP address expects to to find IP addresses in the incident. Such incidents might be created by a Brute Force attack analytics rule. |
| Tags | Filter by the labels applied to the playbook, relating the playbook to a specific scenario, or indicating special characteristic. For example: - Enrichment - Playbooks that fetch information from another service to add context to an incident. This information is typically added as a comment to the incident or sent to the SOC. - Remediation - Playbooks that take an action on the affected entities to eliminate a potential threat. - Sync - Playbook that help to keep an external service, such as an incident management service, updated with the incident's properties. - Notification - Playbooks that send an email or message. - Response from Teams - Playbooks that allow analysts to take a manual action from Teams using interactive cards. |
For example:
Customize a playbook from a template
This procedure describes how to deploy playbook templates, and can be repeated to create multiple playbooks from the same template.
While most playbook templates can be used as they are, we recommend that you adjust them as needed to fit your playbook to your SOC needs.
On the Playbook templates tab, select a playbook to start from.
If the playbook has any prerequisites, make sure to follow the instructions. For example:
Some playbooks call other playbooks as actions. This second playbook is referred to as a nested playbook. In such a case, one of the prerequisites is to first deploy the nested playbook.
Some playbooks require deploying a custom Logic Apps connector or an Azure Function. In such cases, there's a Deploy to Azure link that takes you to the general ARM template deployment process.
Select Create playbook to open the playbook creation wizard based on the selected template. The wizard has four tabs:
Basics: Locate your new playbook, which is a Logic Apps resource, and give it a name. You can use the default. For example:
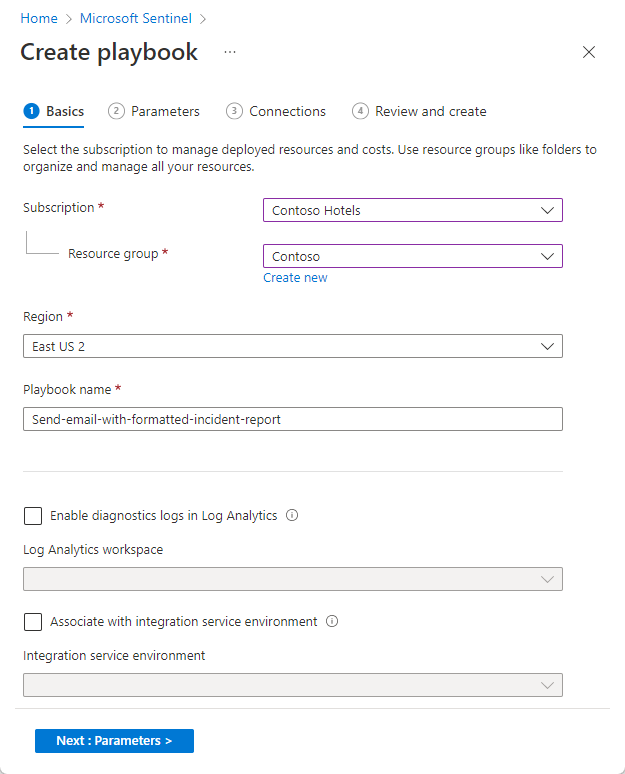
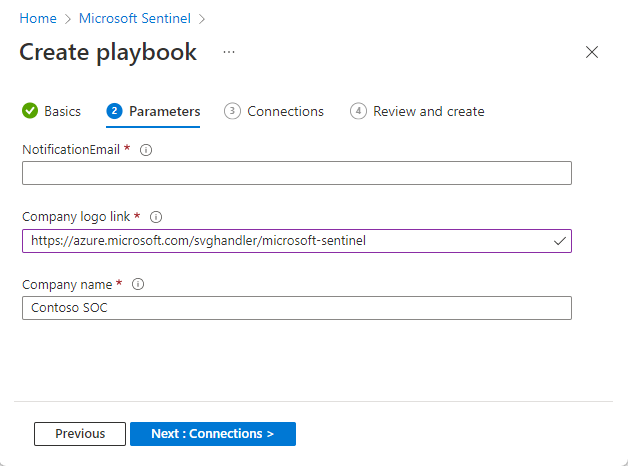
Parameters: Enter customer-specific values that the playbook uses. For example, if the playbook sends an email to the SOC, define the recipient address. If the playbook has a custom connector in use, it must be deployed in the same resource group, and you're prompted to enter its name in the Parameters tab.
The Parameters tab shows only if the playbook has parameters. For example:
Connections: Expand each action to see the existing connections you created for previous playbooks. You can choose to use existing connections, or create a new one. For example:
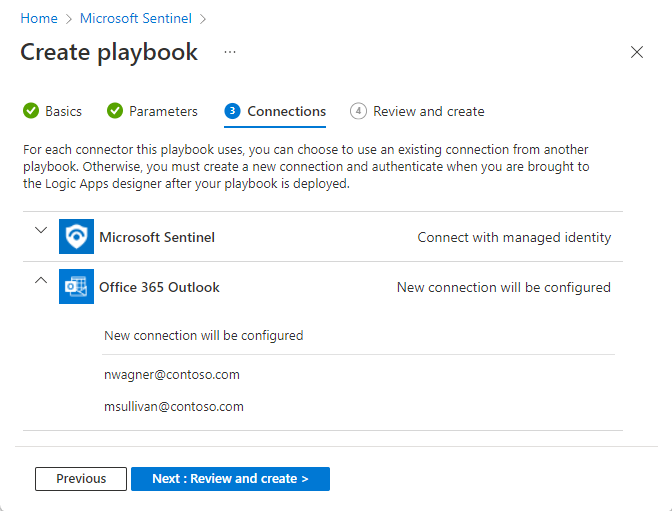
To create a new connection, select Create new connection after deployment. This option takes you to the Logic Apps designer after the deployment process is completed.
Custom connectors are listed by the custom connector name entered in the Parameters tab.
For connectors that support connecting with managed identity, such as Microsoft Sentinel, managed identity is the default connection method.
For more information, see Authenticate playbooks to Microsoft Sentinel.
Review and Create: View a summary of the process and await validation of your input before creating the playbook.
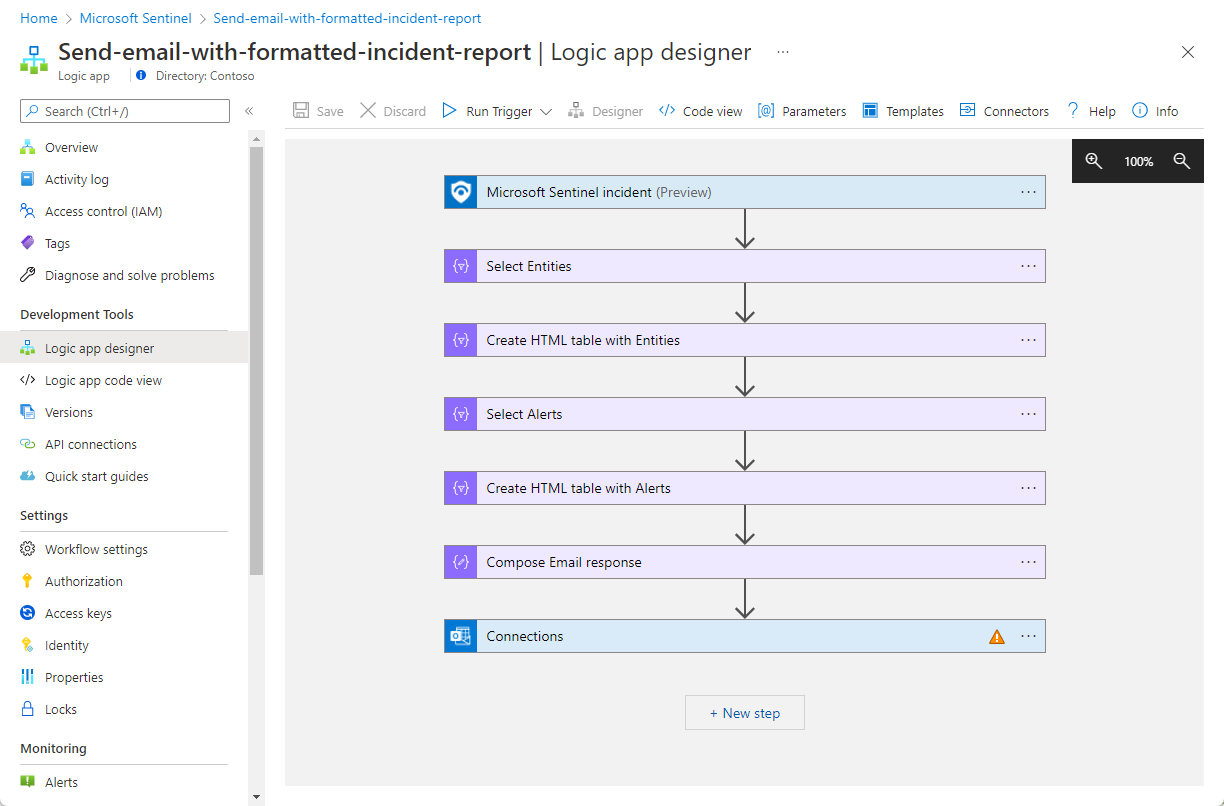
After following the steps in the playbook creation wizard to the end, you're taken to the new playbook's workflow design in the Logic Apps designer. For example:
For each connector you chose, create a new connection for after deployment:
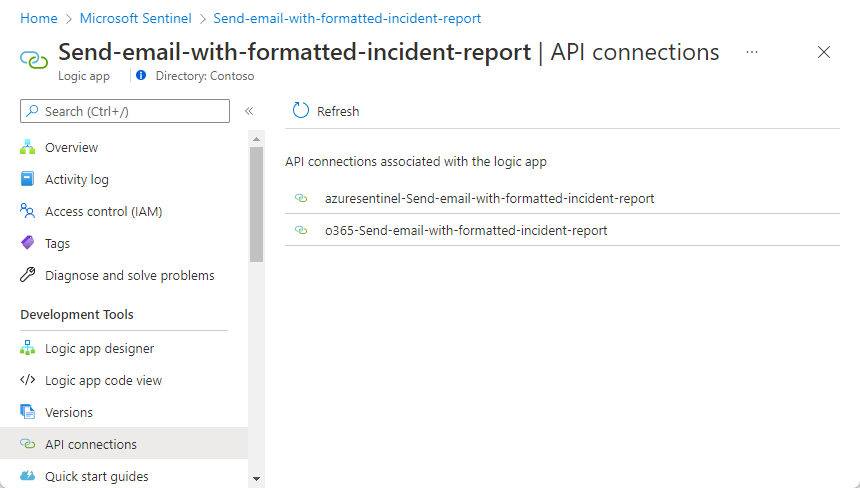
From the navigation menu, select API connections and then select the connection name. For example:
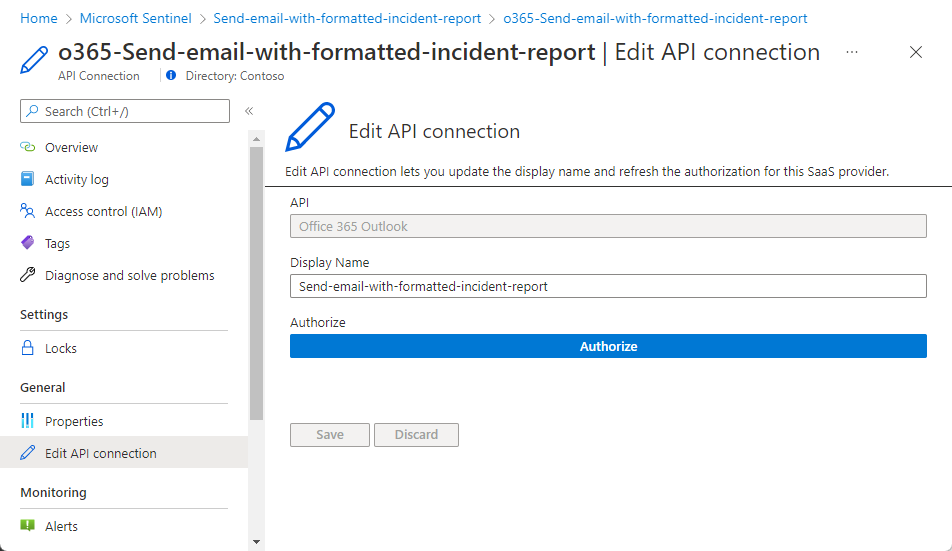
Select Edit API connection from the navigation menu.
Fill in the required parameters and select Save. For example:
Alternatively, create a new connection from within the relevant steps in the Logic Apps designer:
For each step that appears with an error sign, select it to expand and then select Add new.
Authenticate according to the relevant instructions. For more information, see Authenticate playbooks to Microsoft Sentinel.
If there are other steps using this same connector, expand their boxes. From the list of connections that appears, select the connection you just created.
If you have chosen to use a managed identity connection for Microsoft Sentinel, or for other supported connections, make sure to grant permissions to the new playbook on the Microsoft Sentinel workspace or on the relevant target resources for other connectors.
Save the playbook. The playbook appears in the Active Playbooks tab.
To run your playbook, set an automated response or run it manually. For more information, see Respond to threats with Microsoft Sentinel playbooks.
Report an issue in a playbook template
To report a bug or request an improvement for a playbook, select the Supported by link in the playbook's details pane. If this is a community-supported playbook, the link takes you to open a GitHub issue. Otherwise, you're directed to the supporter's page, with information about how to send your feedback.