Manage NSG flow logs using Azure Policy
Important
On September 30, 2027, network security group (NSG) flow logs will be retired. As part of this retirement, you'll no longer be able to create new NSG flow logs starting June 30, 2025. We recommend migrating to virtual network flow logs, which overcome the limitations of NSG flow logs. After the retirement date, traffic analytics enabled with NSG flow logs will no longer be supported, and existing NSG flow logs resources in your subscriptions will be deleted. However, NSG flow logs records won't be deleted and will continue to follow their respective retention policies. For more information, see the official announcement.
Azure Policy helps you enforce organizational standards and assess compliance at scale. Common use cases for Azure Policy include implementing governance for resource consistency, regulatory compliance, security, cost, and management. To learn more about Azure policy, see What is Azure Policy? and Quickstart: Create a policy assignment to identify non-compliant resources.
In this article, you learn how to use two built-in policies to manage your setup of network security group (NSG) flow logs. The first policy flags any network security group that doesn't have flow logs enabled. The second policy automatically deploys NSG flow logs that don't have flow logs enabled.
Audit network security groups using a built-in policy
The Flow logs should be configured for every network security group policy audits all existing network security groups in a scope by checking all Azure Resource Manager objects of type Microsoft.Network/networkSecurityGroups. This policy then checks for linked flow logs via the flow logs property of the network security group, and it flags any network security group that doesn't have flow logs enabled.
To audit your flow logs using the built-in policy, follow these steps:
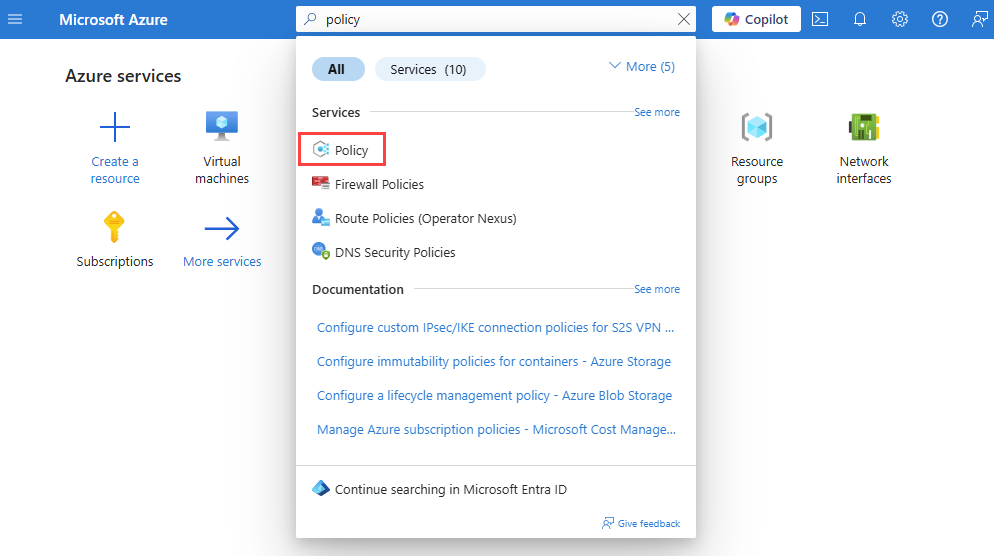
Sign in to the Azure portal.
In the search box at the top of the portal, enter policy. Select Policy from the search results.
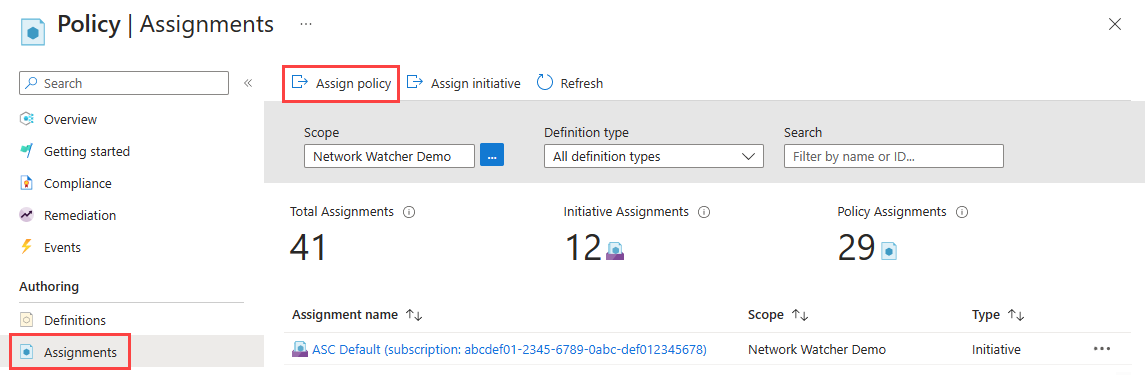
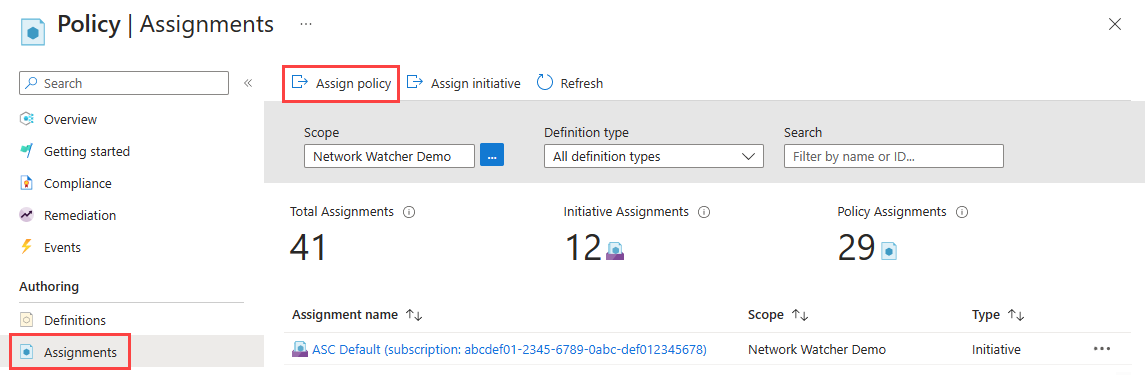
Select Assignments, and then select Assign policy.
Select the ellipsis (...) next to Scope to choose your Azure subscription that has the network security groups that you want the policy to audit. You can also choose the resource group that has the network security groups. After you make your selections, choose the Select button.
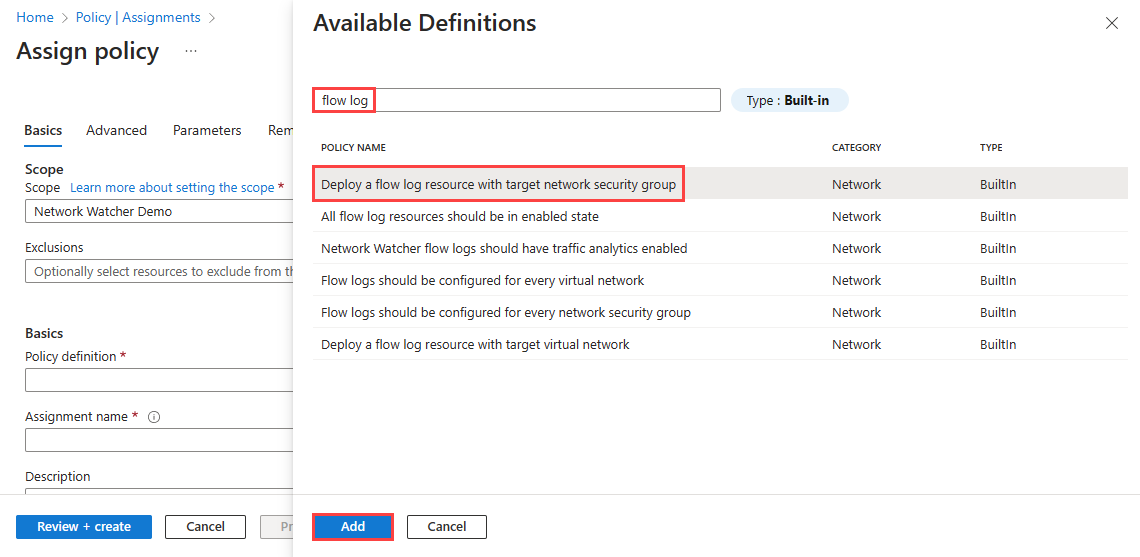
Select the ellipsis (...) next to Policy definition to choose the built-in policy that you want to assign. Enter flow log in the search box, and then select the Built-in filter. From the search results, select Flow logs should be configured for every network security group, and then select Add.
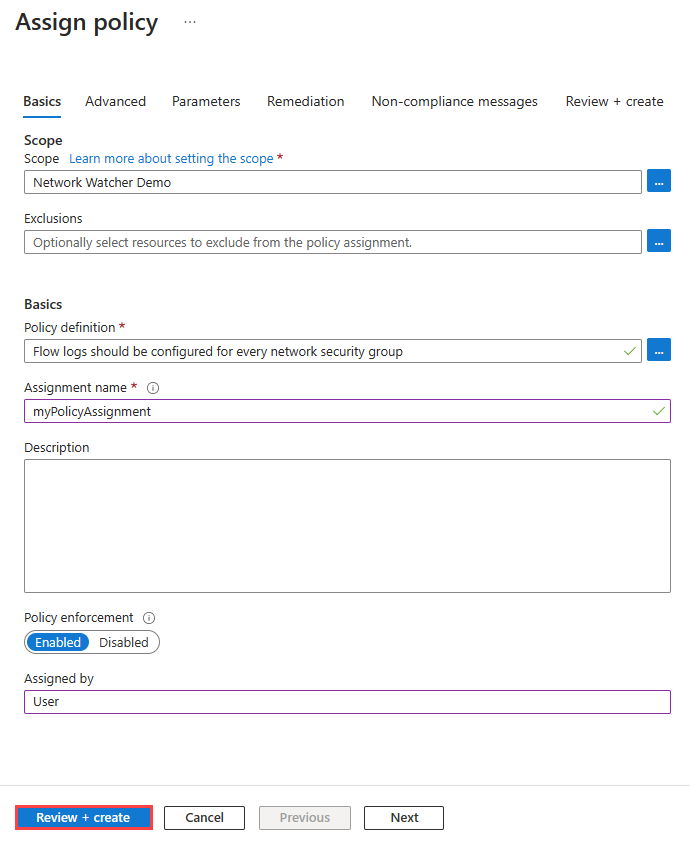
Enter a name in Assignment name, and enter your name in Assigned by.
This policy doesn't require any parameters. It also doesn't contain any role definitions, so you don't need to create role assignments for the managed identity on the Remediation tab.
Select Review + create, and then select Create.
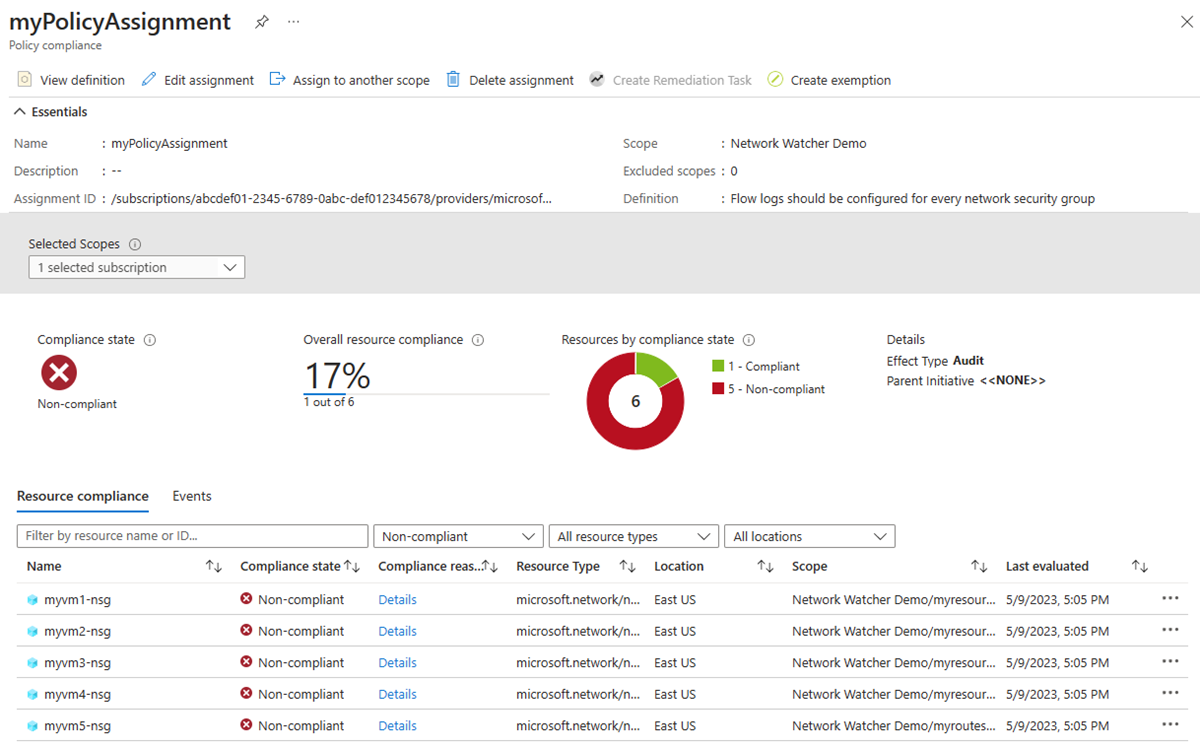
Select Compliance. Search for the name of your assignment, and then select it.
Select Resource compliance to get a list of all non-compliant network security groups.
Deploy and configure NSG flow logs using a built-in policy
The Deploy a flow log resource with target network security group policy checks all existing network security groups in a scope by checking all Azure Resource Manager objects of type Microsoft.Network/networkSecurityGroups. It then checks for linked flow logs via the flow logs property of the network security group. If the property doesn't exist, the policy deploys a flow log.
To assign the deployIfNotExists policy:
Sign in to the Azure portal.
In the search box at the top of the portal, enter policy. Select Policy from the search results.
Select Assignments, and then select Assign policy.
Select the ellipsis (...) next to Scope to choose your Azure subscription that has the network security groups that you want the policy to audit. You can also choose the resource group that has the network security groups. After you make your selections, choose the Select button.
Select the ellipsis (...) next to Policy definition to choose the built-in policy that you want to assign. Enter flow log in the search box, and then select the Built-in filter. From the search results, select Deploy a flow log resource with target network security group, and then select Add.
Enter a name in Assignment name, and enter your name in Assigned by.
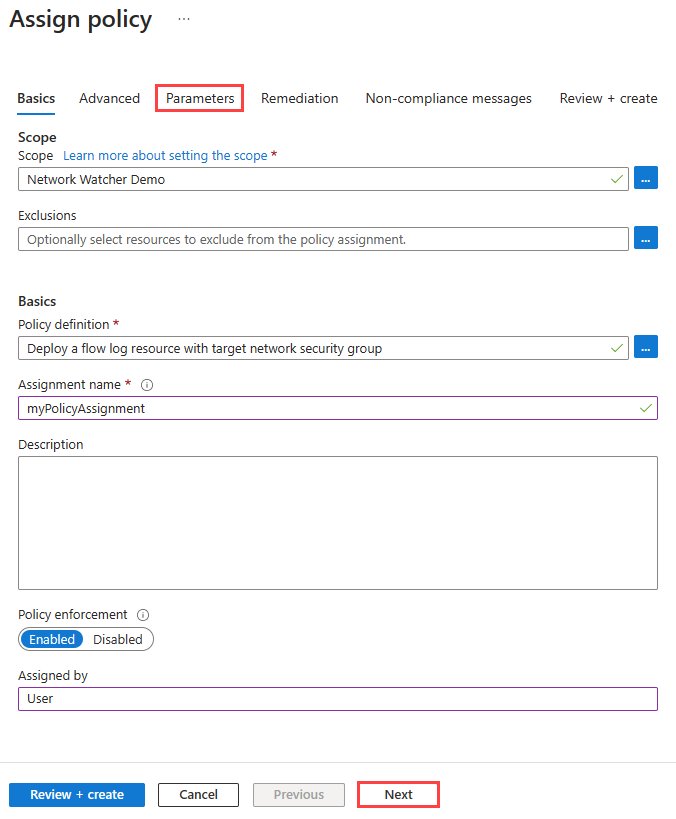
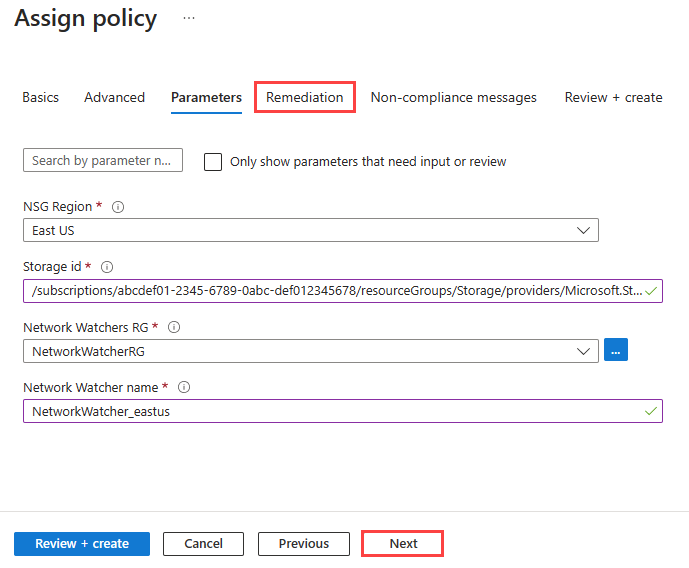
Select Next button twice, or select the Parameters tab. Then enter or select the following values:
Setting Value NSG Region Select the region of your network security group that you're targeting with the policy. Storage id Enter the full resource ID of the storage account. The storage account must be in the same region as the network security group. The format of storage resource ID is /subscriptions/<SubscriptionID>/resourceGroups/<ResourceGroupName>/providers/Microsoft.Storage/storageAccounts/<StorageAccountName>.Network Watchers RG Select the resource group of your Azure Network Watcher instance. Network Watcher name Enter the name of your Network Watcher instance. Select Next or the Remediation tab. Enter or select the following values:
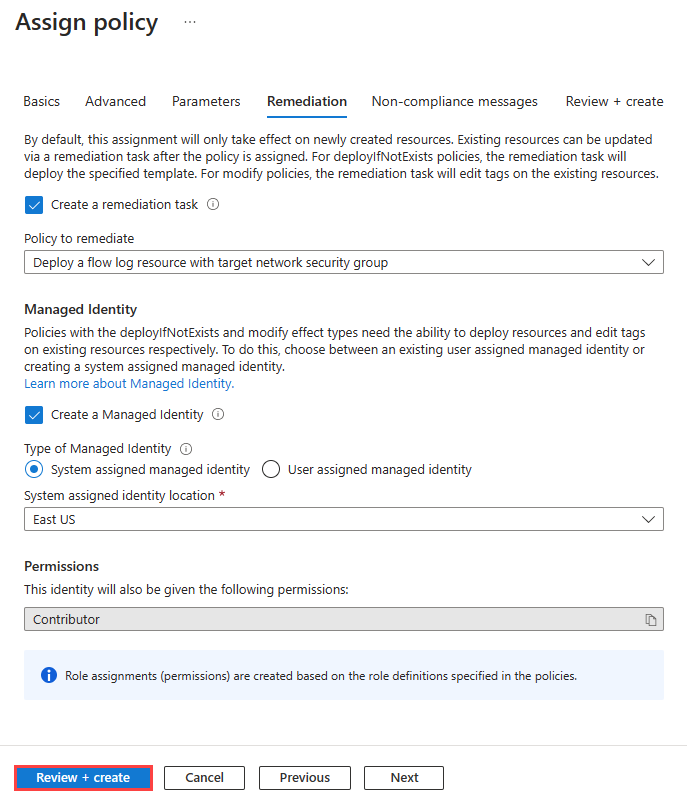
Setting Value Create a remediation task Select the checkbox if you want the policy to affect existing resources. Create a Managed Identity Select the checkbox. Type of Managed Identity Select the type of managed identity that you want to use. System assigned identity location Select the region of your system assigned identity. Scope Select the scope of your user-assigned identity. Existing user assigned identities Select your user-assigned identity. Note
You need Contributor or Owner permission to use this policy.
Select Review + create, and then select Create.
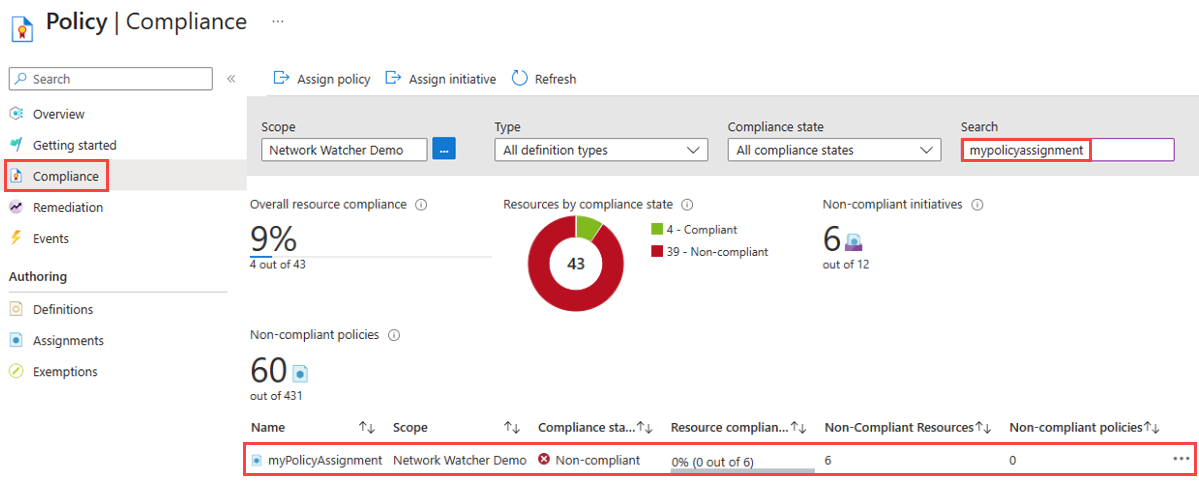
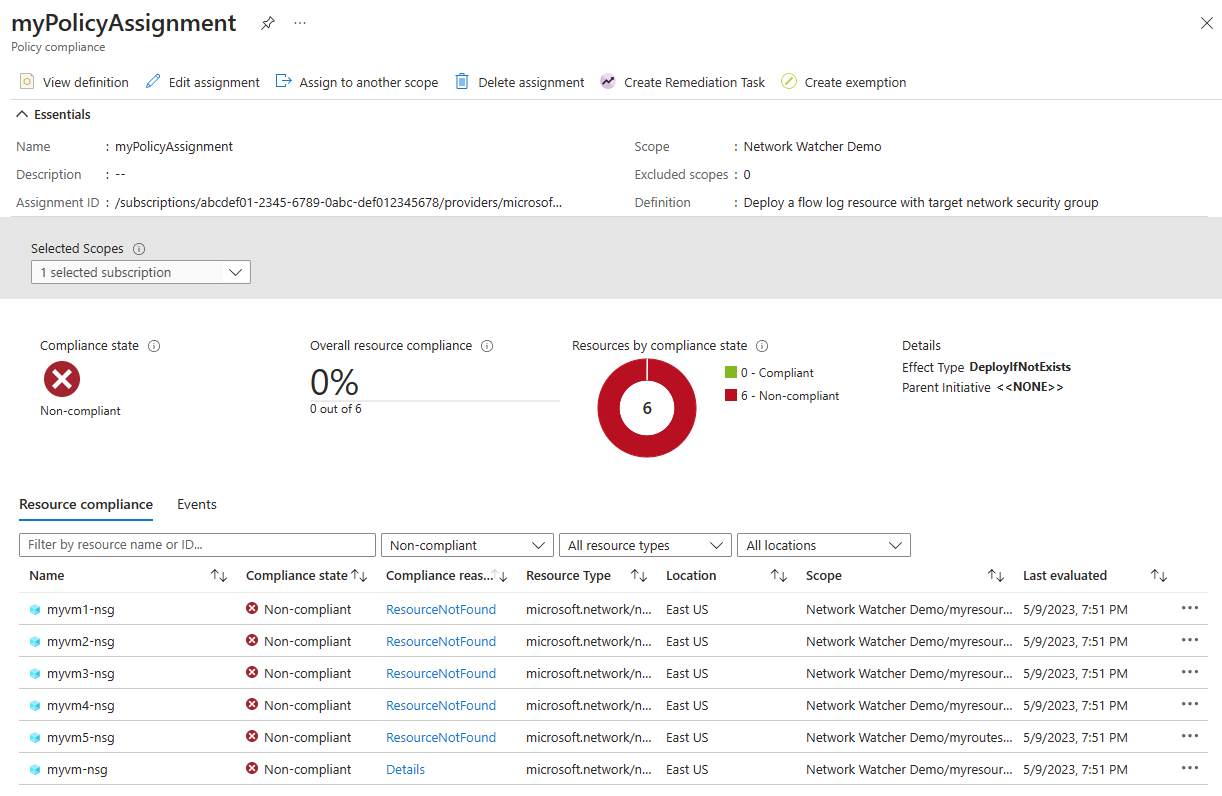
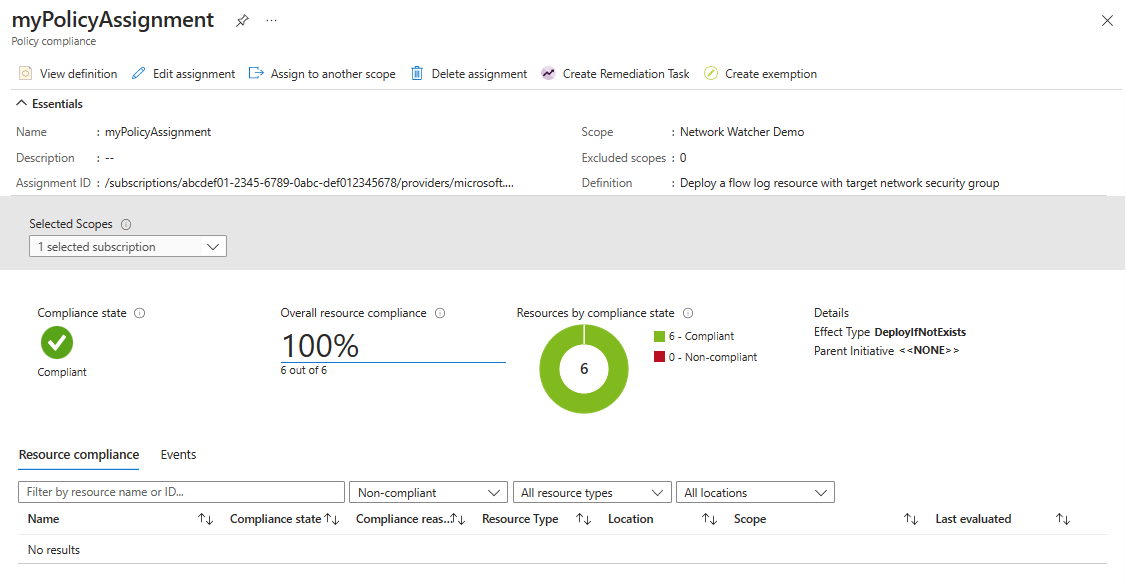
Select Compliance. Search for the name of your assignment, and then select it.
Select Resource compliance to get a list of all non-compliant network security groups.
Leave the policy runs to evaluate and deploy flow logs for all non-compliant network security groups. Then select Resource compliance again to check the status of network security groups (you don't see noncompliant network security groups if the policy completed its remediation).
Related content
- To learn more about NSG flow logs, see Flow logs for network security groups.
- To learn about using built-in policies with traffic analytics, see Manage traffic analytics using Azure Policy.
- To learn how to use an Azure Resource Manager (ARM) template to deploy flow logs and traffic analytics, see Configure NSG flow logs using an Azure Resource Manager template.