Microsoft Defender for Cloud overview
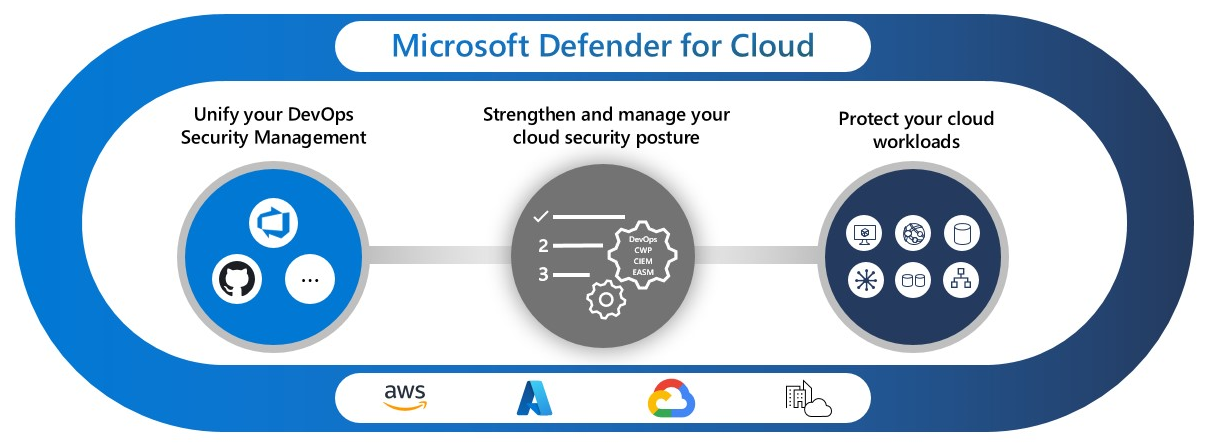
Microsoft Defender for Cloud is a cloud-native application protection platform (CNAPP) that includes security measures and practices designed to protect cloud-based applications from various cyber threats and vulnerabilities. Defender for Cloud includes:
- A development security operations (DevSecOps) solution that unifies security management at the code level across multicloud and multi-pipeline environments
- A cloud security posture management (CSPM) solution that identifies actions to prevent breaches
- A cloud workload protection platform (CWPP) with protections for servers, containers, storage, databases, and other workloads
Note
For Defender for Cloud pricing information, see the pricing page.
The Microsoft 365 Defender portal helps security teams investigate attacks on cloud resources, devices, and identities. Microsoft 365 Defender provides an overview of attacks, including suspicious and malicious events in cloud environments. Microsoft 365 Defender achieves this by correlating all alerts and incidents, including cloud alerts and incidents.
Learn more about the integration between Microsoft Defender for Cloud and Microsoft Defender XDR.
Secure cloud applications
Defender for Cloud helps you incorporate good security practices early in the software development process, or DevSecOps. You can protect your code management environments and code pipelines, and get insights into your development environment security posture from a single location. Defender for Cloud enables security teams to manage DevOps security across multi-pipeline environments.
Today's applications require security awareness at the code, infrastructure, and runtime levels to ensure that deployed applications are hardened against attacks.
| Capability | What problem does it solve? | Get started | Defender plan |
|---|---|---|---|
| Code pipeline insights | Empowers security teams with the ability to protect applications and resources from code to cloud across multi-pipeline environments, including GitHub, Azure DevOps, and GitLab. DevOps security findings, such as Infrastructure as Code (IaC) misconfigurations and exposed secrets, can then be correlated with other contextual cloud security insights to prioritize remediation in code. | Connect Azure DevOps, GitHub, and GitLab repositories to Defender for Cloud | Foundational CSPM (Free) and Defender CSPM |
Improve your security posture
The security of your cloud and on-premises resources relies on proper configuration and deployment. Defenders for Cloud recommendations identify steps to secure your environment.
Defender for Cloud includes free Foundational CSPM capabilities. Enable advanced CSPM capabilities with the Defender CSPM plan.
| Capability | What problem does it solve? | Get started | Defender plan |
|---|---|---|---|
| Centralized policy management | Define the security conditions that you want to maintain across your environment. The policy translates to recommendations that identify resource configurations that violate your security policy. The Microsoft cloud security benchmark is a built-in standard that applies security principles with detailed technical implementation guidance for Azure and other cloud providers (such as Amazon Web Services (AWS) and Google Cloud Platform (GCP). | Customize a security policy | Foundational CSPM (Free) |
| Secure score | Summarize your security posture based on the security recommendations. As you remediate recommendations, your secure score improves. | Track your secure score | Foundational CSPM (Free) |
| Multicloud coverage | Connect to your multicloud environments with agentless methods for CSPM insight and CWP protection. | Connect your Amazon AWS and Google GCP cloud resources to Defender for Cloud | Foundational CSPM (Free) |
| Cloud Security Posture Management (CSPM) | Use the dashboard to see weaknesses in your security posture. | Enable CSPM tools | Foundational CSPM (Free) |
| Advanced Cloud Security Posture Management | Get advanced tools to identify weaknesses in your security posture, including: - Governance to drive actions to improve your security posture - Regulatory compliance to verify compliance with security standards - Cloud security explorer to build a comprehensive view of your environment |
Enable CSPM tools | Defender CSPM |
| Data Security Posture Management | Data security posture management automatically discovers datastores containing sensitive data, and helps reduce risk of data breaches. | Enable data security posture management | Defender CSPM or Defender for Storage |
| Attack path analysis | Model traffic on your network to identify potential risks before you implement changes to your environment. | Build queries to analyze paths | Defender CSPM |
| Cloud Security Explorer | A map of your cloud environment that lets you build queries to find security risks. | Build queries to find security risks | Defender CSPM |
| Security governance | Drive security improvements through your organization by assigning tasks to resource owners and tracking progress in aligning your security state with your security policy. | Define governance rules | Defender CSPM |
| Microsoft Entra Permissions Management | Provide comprehensive visibility and control over permissions for any identity and any resource in Azure, AWS, and GCP. | Review your Permission Creep Index (CPI) | Defender CSPM |
Protect cloud workloads
Proactive security principles require implementing security practices to protect your workloads from threats. Cloud workload protections (CWP) provide workload-specific recommendations to guide you to the right security controls to protect your workloads.
When your environment is threatened, security alerts immediately indicate the nature and severity of the threat so you can plan your response. After identifying a threat in your environment, respond quickly to limit the risk to your resources.
| Capability | What problem does it solve? | Get started | Defender plan |
|---|---|---|---|
| Protect cloud servers | Provide server protections through Microsoft Defender for Endpoint or extended protection with just-in-time network access, file integrity monitoring, vulnerability assessment, and more. | Secure your multicloud and on-premises servers | Defender for Servers |
| Identify threats to your storage resources | Detect unusual and potentially harmful attempts to access or exploit your storage accounts using advanced threat detection capabilities and Microsoft Threat Intelligence data to provide contextual security alerts. | Protect your cloud storage resources | Defender for Storage |
| Protect cloud databases | Protect your entire database estate with attack detection and threat response for the most popular database types in Azure to protect the database engines and data types, according to their attack surface and security risks. | Deploy specialized protections for cloud and on-premises databases | - Defender for Azure SQL Databases - Defender for SQL servers on machines - Defender for Open-source relational databases - Defender for Azure Cosmos DB |
| Protect containers | Secure your containers so you can improve, monitor, and maintain the security of your clusters, containers, and their applications with environment hardening, vulnerability assessments, and run-time protection. | Find security risks in your containers | Defender for Containers |
| Infrastructure service insights | Diagnose weaknesses in your application infrastructure that can leave your environment susceptible to attack. | - Identify attacks targeting applications running over App Service - Detect attempts to exploit Key Vault accounts - Get alerted on suspicious Resource Manager operations - Expose anomalous Domain Name System (DNS) activities |
- Defender for App Service - Defender for Key Vault - Defender for Resource Manager - Defender for DNS |
| Security alerts | Get informed of real-time events that threaten the security of your environment. Alerts are categorized and assigned severity levels to indicate proper responses. | Manage security alerts | Any workload protection Defender plan |
| Security incidents | Identify attack patterns by correlating alerts and integrate with Security Information and Event Management (SIEM), Security Orchestration, Automation, and Response (SOAR), and IT classic deployment model solutions to respond to threats and reduce risk to your resources. | Export alerts to SIEM, SOAR, or ITSM systems | Any workload protection Defender plan |
Important
As of August 1 2023, customers with an existing subscription to Defender for DNS can continue to use the service, but new subscribers will receive alerts about suspicious DNS activity as part of Defender for Servers P2.
Learn More
For more information about Defender for Cloud and how it works, see:
- A step-by-step walkthrough of Defender for Cloud
- An interview about Defender for Cloud with an expert in cybersecurity in Lessons Learned from the Field
- Microsoft Defender for Cloud - Use cases
- Microsoft Defender for Cloud PoC Series - Microsoft Defender for Containers
- Learn how Microsoft Defender for Cloud provides data security