Troubleshoot Azure Resource Manager service connections
Azure DevOps Services | Azure DevOps Server 2022 - Azure DevOps Server 2019
This article presents the common troubleshooting scenarios to help you resolve issues you might encounter when creating an Azure Resource Manager service connection. See Manage service connections to learn how to create, edit, and secure service connections.
What happens when you create an Azure Resource Manager service connection
If you don't have a service connection, you can create one as follows:
From within your project, select Project settings, and then select Service connections.
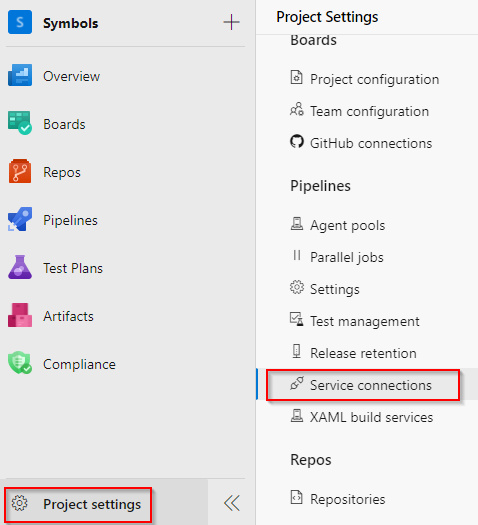
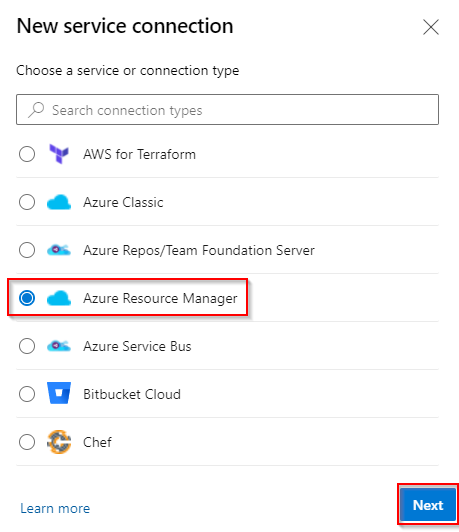
Select New service connection to add a new service connection, and then select Azure Resource Manager. Select Next when you're done.
Select App registration (automatic) as the Identity type and Workload identity federation as the credential.
Select Subscription, and then select your subscription from the drop-down list. Fill out the rest of the form and then select Save when you're done.
When you save your new Azure Resource Manager service connection, Azure DevOps does the following actions:
- Connects to the Microsoft Entra tenant for to the selected subscription.
- Creates an application in Microsoft Entra ID on behalf of the user.
- Assigns the application as a contributor to the selected subscription.
- Creates an Azure Resource Manager service connection using this application's details.
Note
To create service connections, you need to be assigned the Creator or Administrator role for the Endpoint Creator group in your project settings: Project settings > Service connections > More Actions > Security. Project Contributors are added to this group by default.
Troubleshooting scenarios
The following issues might occur when you create service connections:
- The user has only guest permission in the directory
- The user isn't authorized to add applications in the directory
- Failed to obtain an access token or a valid refresh token wasn't found
- Failed to assign Contributor role
- Subscription isn't listed when creating a service connection
- Some subscriptions are missing from the list of subscriptions
- Service principal's token expired
- Failed to obtain the JSON web token (JWT) by using the service principal client ID
- Azure subscription isn't passed from the previous task output
- What authentication mechanisms are supported? How do managed identities work?
The user has only guest permission in the directory
Sign in to the Azure portal using an administrator account. The account should be an owner or user account administrator
Select Microsoft Entra ID in the left navigation bar.
Ensure you're editing the appropriate directory corresponding to the user subscription. If not, select Switch directory and sign in using the appropriate credentials if necessary.
Select Users from the Manage section.
Select User settings.
Select Manage external collaboration settings from the External users section.
Change the Guest user permissions are limited option to No.
Alternatively, if you're prepared to give the user administrator-level permissions, you can make the user a member of an Administrator role. Do the following steps:
Warning
Assigning users to the Global Administrator role allows them to read and modify every administrative setting in your Microsoft Entra organization. As a best practice, assign this role to fewer than five people in your organization.
Sign in to the Azure portal using an administrator account. The account should be an owner or user account administrator.
Select Microsoft Entra ID from the left navigation pane.
Ensure you're editing the appropriate directory corresponding to the user subscription. If not, select Switch directory and sign in using the appropriate credentials if necessary.
Select Users from the Manage section.
Use the search box to search for the user you want to manage.
Select Directory role from the Manage section, and then change the role. Select Save when you're done.
It typically takes 15 to 20 minutes to apply the changes globally. The user then can try recreating the service connection.
The user isn't authorized to add applications in the directory
You must have permissions to add integrated applications in the directory. The directory administrator has permissions to change this setting.
Select Microsoft Entra ID in the left navigation pane.
Ensure you're editing the appropriate directory corresponding to the user subscription. If not, select Switch directory and sign in using the appropriate credentials if necessary.
Select Users, and then select User settings.
Under App registrations, and then change the Users can register applications option to Yes.
You can also create the service principal with an existing user who already has the required permissions in Microsoft Entra ID. For more information, see Create an Azure Resource Manager service connection with an existing service principal.
Failed to obtain an access token or a valid refresh token wasn't found
These errors typically occur when your session is expired. To resolve these issues:
- Sign out of Azure DevOps.
- Open an InPrivate or incognito browser window and navigate to Azure DevOps.
- Sign in using the appropriate credentials.
- Select your organization and your project.
- Create your service connection.
Failed to assign Contributor role
This error typically occurs when you don't have Write permission for the selected Azure subscription.
To resolve this issue, ask the subscription administrator to assign you the appropriate role in Microsoft Entra ID.
Subscription isn't listed when creating a service connection
Maximum of 50 Azure subscriptions listed in the various Azure subscription drop-down menus (billing, service connection, and so on): If you're setting up a service connection and you have more than 50 Azure subscriptions, some of your subscriptions aren't listed. In this scenario, complete the following steps:
- Create a new, native Microsoft Entra user in the Microsoft Entra instance of your Azure subscription.
- Set up the Microsoft Entra user so that it has the proper permissions to set up billing or create service connections. For more information, see Add a user who can set up billing for Azure DevOps.
- Add the Microsoft Entra user to the Azure DevOps org with a Stakeholder access level, and then add it to the Project Collection Administrators group (for billing), or ensure that the user has sufficient permissions in the Team Project to create service connections.
- Sign in to Azure DevOps with the new user credentials, and set up billing. You only see one Azure subscription in the list.
Old user token cached in Azure DevOps Services: If your Azure subscription isn't listed when you create an Azure Resource Manager (ARM) service connection, it might be due to an old user token cached in Azure DevOps Services. This scenario isn't immediately obvious as the list screen of Azure subscriptions doesn't display any errors or warning messages indicating that the user token is outdated. To resolve this issue, manually update the cached user token in Azure DevOps Services by doing the following steps:
- Sign out of Azure DevOps Services and sign back in. This action can refresh the user token.
- Clear your browser cache and cookies to ensure that any old tokens are removed.
- From the Azure DevOps portal, go to the service connections, and reauthorize the connection to Azure. This step prompts Azure DevOps to use a new token.
Some subscriptions are missing from the list of subscriptions
Change support account types settings: This issue can be fixed by changing the supported account types settings and defining who can use your application. Do the following steps:
Sign in to the Azure portal.
If you have access to multiple tenants, use the Directory + subscription filter in the top menu to select the tenant in which you want to register an application.
Select Microsoft Entra ID from the left pane.
Select App registrations.
Select your application from the list of registered applications.
Under Authentication, select Supported account types.
Under Supported account types, Who can use this application or access this API? select Accounts in any organizational directory.

Select Save when you're done.
Old user token cached in Azure DevOps Services: If your Azure subscription isn't listed when you create an Azure Resource Manager (ARM) service connection, it might be due to an old user token cached in Azure DevOps Services. This scenario isn't immediately obvious as the list screen of Azure subscriptions doesn't display any errors or warning messages indicating that the user token is outdated. To resolve this issue, manually update the cached user token in Azure DevOps Services by doing the following steps:
- Sign out of Azure DevOps Services and sign back in. This action can refresh the user token.
- Clear your browser cache and cookies to ensure that any old tokens are removed.
- From the Azure DevOps portal, go to the service connections, and reauthorize the connection to Azure. This step prompts Azure DevOps to use a new token.
Service principal's token expired
An issue that often arises with service principals or secrets that are automatically created is that the token expires and needs to be renewed. If you have an issue with refreshing the token, see Failed to obtain an access token or a valid refresh token wasn't found.
If your token expired, you could see one of the error messages:
AADSTS7000215: Invalid client secret is providedAADSTS7000222: The provided client secret keys for app '***' are expiredInvalid client id or client secret
To renew the access token for an automatically created service principal or secret:
Go to Project settings > Service connections, and then select the service connection you want to modify.
Select Edit in the upper-right corner, and the select Verify.
Select Save.
The token for your service principal or secret is now renewed for three more months.
Note
This operation is available even if the service principal's token has not expired. Make sure that the user performing the operation has proper permissions on the subscription and Microsoft Entra ID, because it will update the secret for the app registered for the service principal. For more information, see Create an Azure Resource Manager service connection using automated security and What happens when you create a Resource Manager service connection?
Failed to obtain the JWT by using the service principal client ID
This issue occurs when you try to verify a service connection that has an expired secret.
To resolve this issue:
Go to Project settings > Service connections, and then select the service connection you want to modify.
Select Edit in the upper-right corner, and then make any change to your service connection. The easiest and recommended change is to add a description.
Select Save to save the service connection.
Note
Select Save. Don't try to verify the service connection at this step.
Exit the service connection edit window, and then refresh the service connections page.
Select Edit in the upper-right corner, and now select Verify.
Select Save to save your service connection.
Azure subscription isn't passed from the previous task output
When you set your Azure subscription dynamically for your release pipeline and want to consume the output variable from a preceding task, you might encounter this issue.
To resolve the issue, ensure that the values are defined within the variables section of your pipeline. You can then pass this variable between your pipeline's tasks.
What authentication mechanisms are supported? How do managed identities work?
An Azure Resource Manager service connection can connect to an Azure subscription by using a Service Principal Authentication (SPA) or managed identity authentication.
The Azure Resource Manager service connection can connect to an Azure subscription, management group, or machine learning workspace using:
- App registration (recommended): You can authenticate the connection using a Workload identity federation or a secret.
- Managed identity: Managed identities for Azure resources provide Azure services with an automatically managed identity in Microsoft Entra ID. You can also use an agent-assigned managed identity.
To learn about managed identities for virtual machines, see Assigning roles.
Note
Managed identities aren't supported in Microsoft-hosted agents. In this scenario, you must set up a self-hosted agent on an Azure VM and configure a managed identity for that VM.