Monitor and revoke personal access tokens
To authenticate to the Azure Databricks REST API, a user can create a personal access token (PAT) and use it in their REST API request. A user can also create a service principal and use it with a personal access token to call Azure Databricks REST APIs in their CI/CD tools and automation. This article explains how Azure Databricks admins can manage personal access tokens in their workspace. To create a personal access token, see Azure Databricks personal access token authentication.
Use OAuth instead of personal access tokens
Databricks recommends you use OAuth access tokens instead of PATs for greater security and convenience. Databricks continues to support PATs, but due to their greater security risk, it is suggested that you audit your account’s current PAT usage, and migrate your users and service principals to OAuth access tokens. To create an OAuth access token (instead of a PAT) to use with a service principal in automation, see Authorize unattended access to Azure Databricks resources with a service principal using OAuth.
Databricks recommends you minimize your personal access token exposure with the following steps:
- Set a short lifetime for all new tokens created in your workspaces. The lifetime should be less than 90 days. By default, the maximum lifetime for all new tokens is 730 days (two years).
- Work with your Azure Databricks workspace administrators and users to switch to those tokens with shorter lifetimes.
- Revoke all long-lived tokens to reduce the risk of these older tokens getting misused over time. Databricks automatically revokes all PATs for your Azure Databricks workspaces when the token hasn’t been used in 90 or more days.
Requirements
You must be an admin to manage personal access tokens.
Azure Databricks account admins can monitor and revoke personal access tokens in across the account.
Azure Databricks workspace admins can do the following:
- Disable personal access tokens for a workspace.
- Control which non-admin users can create tokens and use tokens.
- Set a maximum lifetime for new tokens.
- Monitor and revoke tokens in their workspace.
Managing personal access tokens in your workspace requires the Premium plan.
Monitor and revoke personal access tokens in the account
Important
This feature is in Private Preview. To join this preview, contact your Azure Databricks account team.
Account admins can monitor and revoke personal access tokens from the account console. The queries to monitor tokens run only when an account admin uses the token report page.
To join this preview, first contact your Azure Databricks account team.
As an account admin, log in to the account console.
In the sidebar, click Previews.
Use toggles
 to enable Access Token Report.
to enable Access Token Report.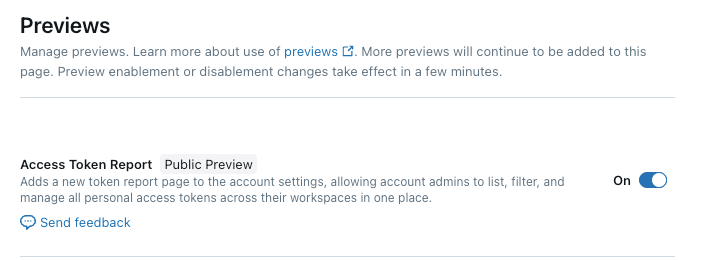
In the sidebar, click Settings and Token report.
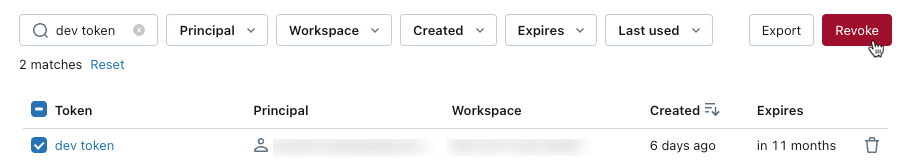
You can filter by the token owner, workspace, created date, expiration date, and date the token was last used. Use the buttons on the top of the report to filter for access tokens for inactive principals or access tokens with no expiration date.
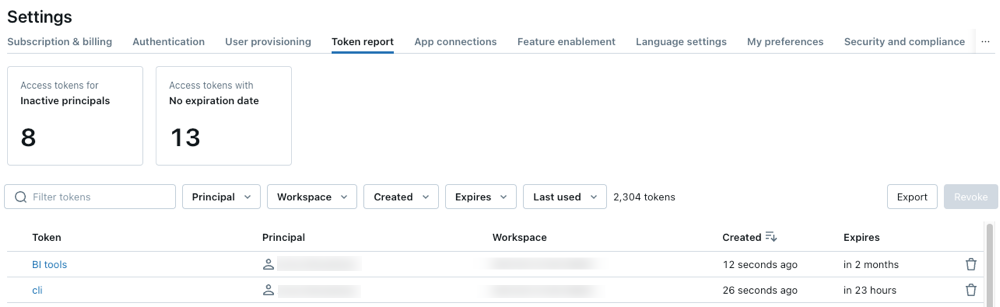
To export a report to a CSV, click Export.
To revoke a token, select a token and click Revoke.
Enable or disable personal access token authentication for the workspace
Personal access token authentication is enabled by default for all Azure Databricks workspaces that were created in 2018 or later. You can change this setting in the workspace settings page.
When personal access tokens are disabled for a workspace, personal access tokens cannot be used to authenticate to Azure Databricks and workspace users and service principals cannot create new tokens. No tokens are deleted when you disable personal access token authentication for a workspace. If tokens are re-enabled later, any non-expired tokens are available for use.
If you want to disable token access for a subset of users, you can keep personal access token authentication enabled for the workspace and set fine-grained permissions for users and groups. See Control who can create and use personal access tokens.
Warning
Partner Connect and partner integrations require personal access tokens to be enabled on a workspace.
To disable the ability to create and use personal access tokens for the workspace:
Go to the settings page.
Click the Advanced tab.
Click the Personal Access Tokens toggle.
Click Confirm.
This change may take a few seconds to take effect.
You can also use the Workspace configuration API to disable personal access tokens for the workspace.
Control who can create and use personal access tokens
Workspace admins can set permissions on personal access tokens to control which users, service principals, and groups can create and use tokens. For details on how to configure personal access token permissions, see Manage personal access token permissions.
Set maximum lifetime of new personal access tokens
By default, the maximum lifetime of new tokens is 730 days (two years). You can set a shorter maximum token lifetime in your workspace using the Databricks CLI or the Workspace configuration API. This limit applies only to new tokens.
Set maxTokenLifetimeDays to the maximum token lifetime of new tokens in days, as an integer. For example:
Databricks CLI
databricks workspace-conf set-status --json '{
"maxTokenLifetimeDays": "90"
}'
Workspace configuration API
curl -n -X PATCH "https://<databricks-instance>/api/2.0/workspace-conf" \
-d '{
"maxTokenLifetimeDays": "90"
}'
If you set the maxTokenLifetimeDays to zero, new tokens can be created with a lifetime up to 730 days (two years).
To use the Databricks Terraform provider to manage the maximum lifetime for new tokens in a workspace, see databricks_workspace_conf Resource.
Monitor and revoke tokens in your workspace
This section describes how workspace admins can use the Databricks CLI to manage existing tokens in the workspace. You can also use the Token Management API. Databricks automatically revokes personal access tokens that haven’t been used in 90 or more days.
Get tokens for the workspace
To get the workspace’s tokens:
Python
from databricks.sdk import WorkspaceClient
w = WorkspaceClient()
spark.createDataFrame([token.as_dict() for token in w.token_management.list()]).createOrReplaceTempView('tokens')
display(spark.sql('select * from tokens order by creation_time'))
Bash
# Filter results by a user by using the `created-by-id` (to filter by the user ID) or `created-by-username` flags.
databricks token-management list
Delete (revoke) a token
To delete a token, replace TOKEN_ID with the id of the token to delete:
databricks token-management delete TOKEN_ID