Send Azure Monitor Activity log data
The Azure Monitor Activity Log is a platform log that provides insight into subscription-level events. The Activity Log includes information like when a resource is modified or a virtual machine is started. You can view the Activity Log in the Azure portal or retrieve entries with PowerShell and the Azure CLI. This article provides information on how to view the Activity Log and send it to different destinations.
Create a diagnostic setting to send the Activity Log to one or more of these locations:
- Log Analytics workspace for more complex querying and alerting
- Azure Event Hubs to forwarding logs outside of Azure.
- Azure Storage for cheaper, long-term archiving.
For details on how to create a diagnostic setting, see Create diagnostic settings to send platform logs and metrics to different destinations.
Tip
Send Activity Logs to a Log Analytics workspace for the following benefits:
- Sending logs to a Log Analytics workspace is free of charge for the default retention period.
- Send logs to a Log Analytics workspace for longer retention of up to 12 years.
- Logs exported to a Log Analytics workspace can be shown in Power BI
- Insights are provided for Activity Logs exported to Log Analytics.
Note
- Entries in the Activity Log are system generated and can't be changed or deleted.
- Entries in the Activity Log are representing control plane changes like a virtual machine restart, any non related entries should be written into Azure Resource Logs
- Entries in the Activity Log are typically a result of changes (create, update or delete operations) or an action having been initiated. Operations focused on reading details of a resource are not typically captured.
Send to Log Analytics workspace
Send the activity log to a Log Analytics workspace to enable the Azure Monitor Logs feature, where you:
- Correlate activity log data with other monitoring data collected by Azure Monitor.
- Consolidate log entries from multiple Azure subscriptions and tenants into one location for analysis together.
- Use log queries to perform complex analysis and gain deep insights on activity log entries.
- Use log search alerts with Activity entries for more complex alerting logic.
- Store activity log entries for longer than the activity log retention period.
- Incur no data ingestion or retention charges for activity log data stored in a Log Analytics workspace.
- The default retention period in Log Analytics is 90 days
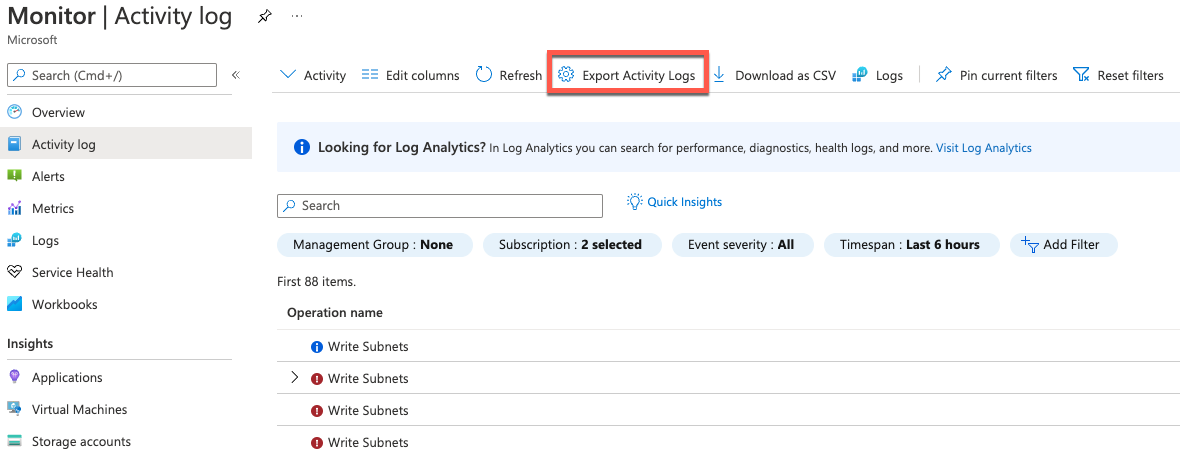
Select Export Activity Logs to send the activity log to a Log Analytics workspace.
You can send the activity log from any single subscription to up to five workspaces.
Activity log data in a Log Analytics workspace is stored in a table called AzureActivity that you can retrieve with a log query in Log Analytics. The structure of this table varies depending on the category of the log entry. For a description of the table properties, see the Azure Monitor data reference.
For example, to view a count of activity log records for each category, use the following query:
AzureActivity
| summarize count() by CategoryValue
To retrieve all records in the administrative category, use the following query:
AzureActivity
| where CategoryValue == "Administrative"
Important
In some scenarios, it's possible that values in fields of AzureActivity might have different casings from otherwise equivalent values. Take care when querying data in AzureActivity to use case-insensitive operators for string comparisons, or use a scalar function to force a field to a uniform casing before any comparisons. For example, use the tolower() function on a field to force it to always be lowercase or the =~ operator when performing a string comparison.
Send to Azure Event Hubs
Send the activity log to Azure Event Hubs to send entries outside of Azure, for example, to a third-party SIEM or other log analytics solutions. Activity log events from event hubs are consumed in JSON format with a records element that contains the records in each payload. The schema depends on the category and is described in Azure activity log event schema.
The following sample output data is from event hubs for an activity log:
{
"records": [
{
"time": "2019-01-21T22:14:26.9792776Z",
"resourceId": "/subscriptions/s1/resourceGroups/MSSupportGroup/providers/microsoft.support/supporttickets/115012112305841",
"operationName": "microsoft.support/supporttickets/write",
"category": "Write",
"resultType": "Success",
"resultSignature": "Succeeded.Created",
"durationMs": 2826,
"callerIpAddress": "111.111.111.11",
"correlationId": "aaaa0000-bb11-2222-33cc-444444dddddd",
"identity": {
"authorization": {
"scope": "/subscriptions/s1/resourceGroups/MSSupportGroup/providers/microsoft.support/supporttickets/115012112305841",
"action": "microsoft.support/supporttickets/write",
"evidence": {
"role": "Subscription Admin"
}
},
"claims": {
"aud": "https://management.core.windows.net/",
"iss": "https://sts.windows.net/72f988bf-86f1-41af-91ab-2d7cd011db47/",
"iat": "1421876371",
"nbf": "1421876371",
"exp": "1421880271",
"ver": "1.0",
"http://schemas.microsoft.com/identity/claims/tenantid": "ffffffff-eeee-dddd-cccc-bbbbbbbbbbb0",
"http://schemas.microsoft.com/claims/authnmethodsreferences": "pwd",
"http://schemas.microsoft.com/identity/claims/objectidentifier": "2468adf0-8211-44e3-95xq-85137af64708",
"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn": "admin@contoso.com",
"puid": "20030000801A118C",
"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifier": "9vckmEGF7zDKk1YzIY8k0t1_EAPaXoeHyPRn6f413zM",
"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/givenname": "John",
"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/surname": "Smith",
"name": "John Smith",
"groups": "cacfe77c-e058-4712-83qw-f9b08849fd60,7f71d11d-4c41-4b23-99d2-d32ce7aa621c,31522864-0578-4ea0-9gdc-e66cc564d18c",
"http://schemas.xmlsoap.org/ws/2005/05/identity/claims/name": " admin@contoso.com",
"appid": "00001111-aaaa-2222-bbbb-3333cccc4444",
"appidacr": "2",
"http://schemas.microsoft.com/identity/claims/scope": "user_impersonation",
"http://schemas.microsoft.com/claims/authnclassreference": "1"
}
},
"level": "Information",
"location": "global",
"properties": {
"statusCode": "Created",
"serviceRequestId": "50d5cddb-8ca0-47ad-9b80-6cde2207f97c"
}
}
]
}
Send to Azure Storage
Send the activity log to an Azure Storage account if you want to retain your log data longer than 90 days for audit, static analysis, or back up. If you're required to retain your events for 90 days or less, you don't need to set up archival to a storage account. Activity log events are retained in the Azure platform for 90 days.
When you send the activity log to Azure, a storage container is created in the storage account as soon as an event occurs. The blobs in the container use the following naming convention:
insights-activity-logs/resourceId=/SUBSCRIPTIONS/{subscription ID}/y={four-digit numeric year}/m={two-digit numeric month}/d={two-digit numeric day}/h={two-digit 24-hour clock hour}/m=00/PT1H.json
For example, a particular blob might have a name similar to:
insights-activity-logs/resourceId=/SUBSCRIPTIONS/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/y=2020/m=06/d=08/h=18/m=00/PT1H.json
Each PT1H.json blob contains a JSON object with events from log files that were received during the hour specified in the blob URL. During the present hour, events are appended to the PT1H.json file as they're received, regardless of when they were generated. The minute value in the URL, m=00 is always 00 as blobs are created on a per hour basis.
Each event is stored in the PT1H.json file with the following format. This format uses a common top-level schema but is otherwise unique for each category, as described in Activity log schema.
{ "time": "2020-06-12T13:07:46.766Z", "resourceId": "/SUBSCRIPTIONS/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/RESOURCEGROUPS/MY-RESOURCE-GROUP/PROVIDERS/MICROSOFT.COMPUTE/VIRTUALMACHINES/MV-VM-01", "correlationId": "bbbb1111-cc22-3333-44dd-555555eeeeee", "operationName": "Microsoft.Resourcehealth/healthevent/Updated/action", "level": "Information", "resultType": "Updated", "category": "ResourceHealth", "properties": {"eventCategory":"ResourceHealth","eventProperties":{"title":"This virtual machine is starting as requested by an authorized user or process. It will be online shortly.","details":"VirtualMachineStartInitiatedByControlPlane","currentHealthStatus":"Unknown","previousHealthStatus":"Unknown","type":"Downtime","cause":"UserInitiated"}}}
Other methods to retrieve activity log events
You can also access activity log events by using the following methods:
- Use the Get-AzLog cmdlet to retrieve the activity log from PowerShell. See Azure Monitor PowerShell samples.
- Use az monitor activity-log to retrieve the activity log from the CLI. See Azure Monitor CLI samples.
- Use the Azure Monitor REST API to retrieve the activity log from a REST client.
Legacy collection methods
Note
- Azure Activity logs solution was used to forward Activity Logs to Azure Log Analytics. This solution is being retired on the 15th of Sept 2026 and will be automatically converted to Diagnostic settings.
If you're collecting activity logs using the legacy collection method, we recommend you export activity logs to your Log Analytics workspace and disable the legacy collection using the Data Sources - Delete API as follows:
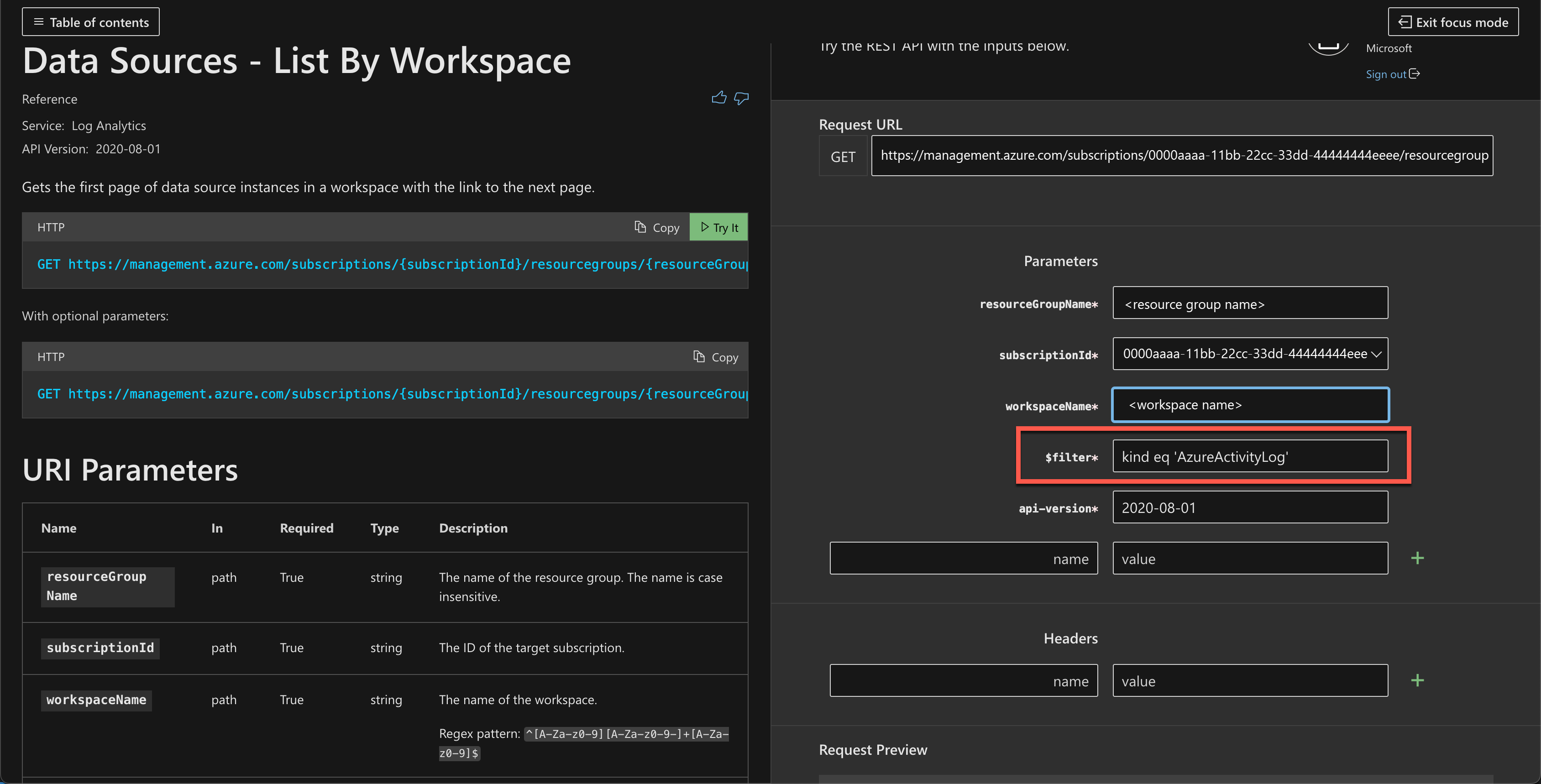
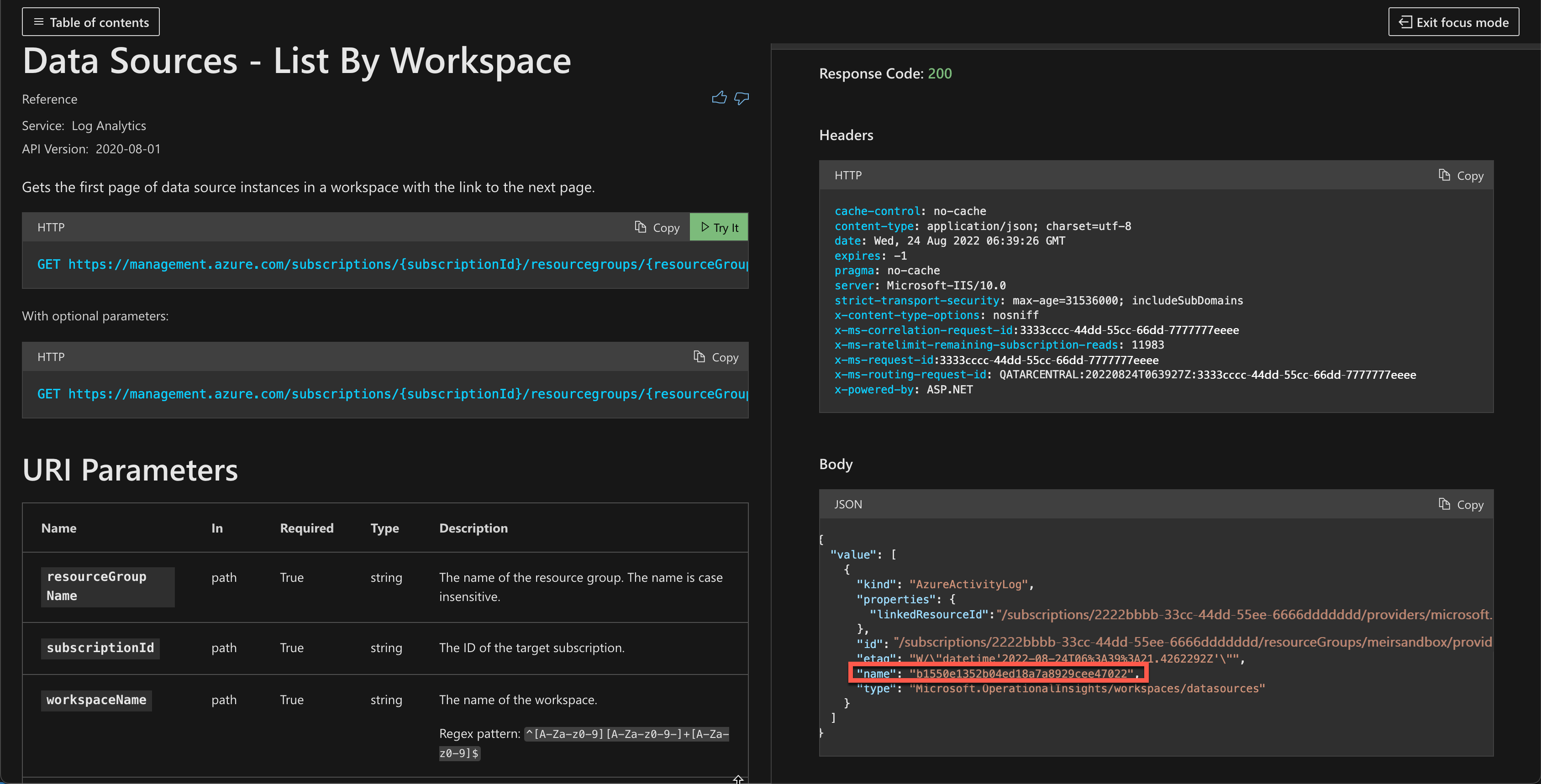
List all data sources connected to the workspace using the Data Sources - List By Workspace API and filter for activity logs by setting
kind eq 'AzureActivityLog'.Copy the name of the connection you want to disable from the API response.
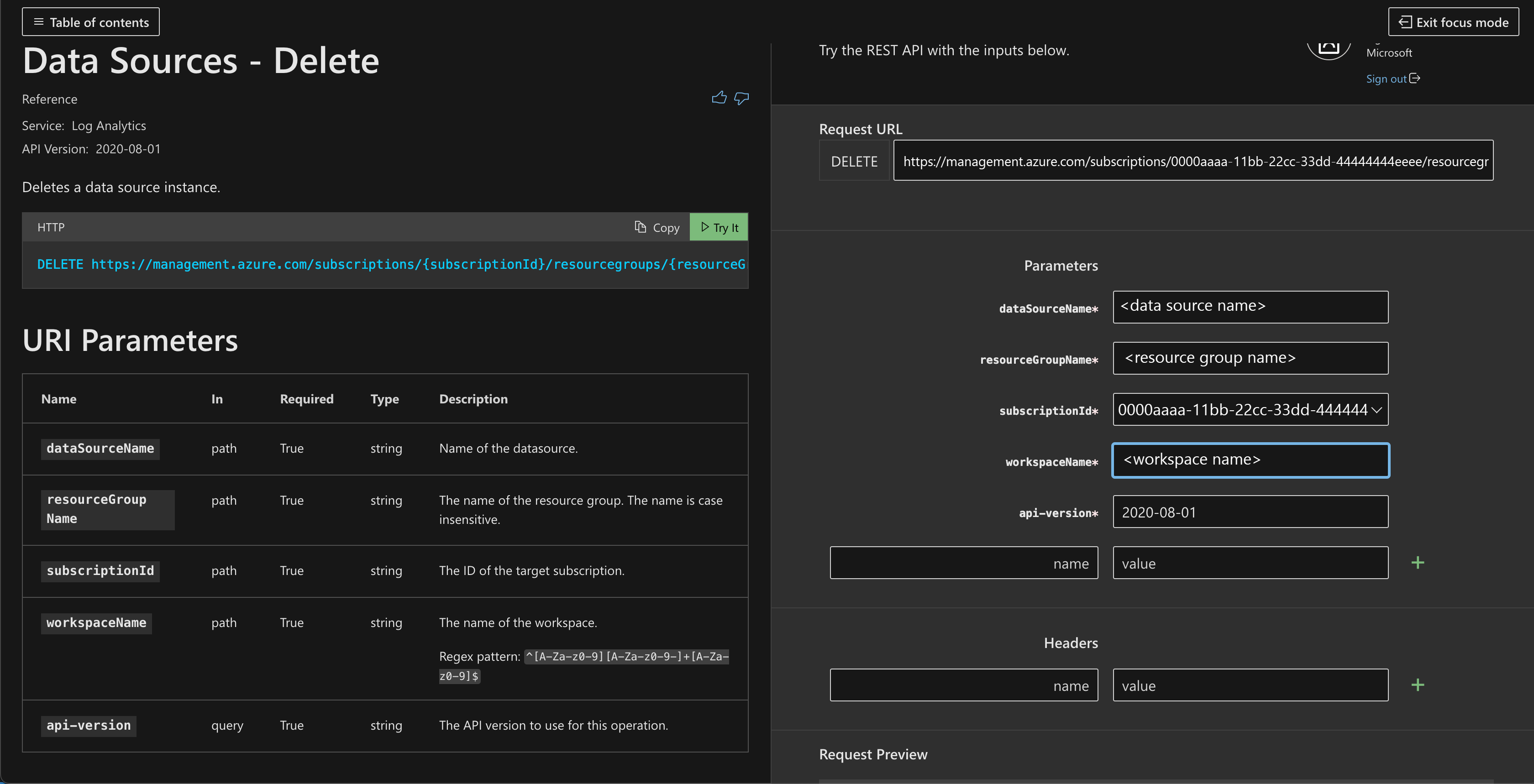
Use the Data Sources - Delete API to stop collecting activity logs for the specific resource.
Managing legacy Log Profiles - retiring
Note
- Logs Profiles was used to forward Activity Logs to storage accounts and Event Hubs. This method is being retired on the 15th of Sept 2026.
- If you are using this method, transition to Diagnostic Settings before 15th of Sept 2025, when we will stop allowing new creates of Log Profiles.
Log profiles are the legacy method for sending the activity log to storage or event hubs. If you're using this method, transition to Diagnostic Settings, which provide better functionality and consistency with resource logs.
If a log profile already exists, you first must remove the existing log profile, and then create a new one.
Use
Get-AzLogProfileto identify if a log profile exists. If a log profile exists, note theNameproperty.Use
Remove-AzLogProfileto remove the log profile by using the value from theNameproperty.# For example, if the log profile name is 'default' Remove-AzLogProfile -Name "default"Use
Add-AzLogProfileto create a new log profile:Add-AzLogProfile -Name my_log_profile -StorageAccountId /subscriptions/s1/resourceGroups/myrg1/providers/Microsoft.Storage/storageAccounts/my_storage -serviceBusRuleId /subscriptions/s1/resourceGroups/Default-ServiceBus-EastUS/providers/Microsoft.ServiceBus/namespaces/mytestSB/authorizationrules/RootManageSharedAccessKey -Location global,westus,eastus -RetentionInDays 90 -Category Write,Delete,ActionProperty Required Description Name Yes Name of your log profile. StorageAccountId No Resource ID of the storage account where the activity log should be saved. serviceBusRuleId No Service Bus Rule ID for the Service Bus namespace where you want to have event hubs created. This string has the format {service bus resource ID}/authorizationrules/{key name}.Location Yes Comma-separated list of regions for which you want to collect activity log events. RetentionInDays Yes Number of days for which events should be retained in the storage account, from 1 through 365. A value of zero stores the logs indefinitely. Category No Comma-separated list of event categories to be collected. Possible values are Write, Delete, and Action.
Example script
This sample PowerShell script creates a log profile that writes the activity log to both a storage account and an event hub.
# Settings needed for the new log profile
$logProfileName = "default"
$locations = (Get-AzLocation).Location
$locations += "global"
$subscriptionId = "<your Azure subscription Id>"
$resourceGroupName = "<resource group name your Event Hub belongs to>"
$eventHubNamespace = "<Event Hub namespace>"
$storageAccountName = "<Storage Account name>"
# Build the service bus rule Id from the settings above
$serviceBusRuleId = "/subscriptions/$subscriptionId/resourceGroups/$resourceGroupName/providers/Microsoft.EventHub/namespaces/$eventHubNamespace/authorizationrules/RootManageSharedAccessKey"
# Build the Storage Account Id from the settings above
$storageAccountId = "/subscriptions/$subscriptionId/resourceGroups/$resourceGroupName/providers/Microsoft.Storage/storageAccounts/$storageAccountName"
Add-AzLogProfile -Name $logProfileName -Location $locations -StorageAccountId $storageAccountId -ServiceBusRuleId $serviceBusRuleId
Data structure changes
The Export activity logs experience sends the same data as the legacy method used to send the activity log with some changes to the structure of the AzureActivity table.
The columns in the following table are deprecated in the updated schema. They still exist in AzureActivity, but they have no data. The replacements for these columns aren't new, but they contain the same data as the deprecated column. They're in a different format, so you might need to modify log queries that use them.
| Activity log JSON | Log Analytics column name (older deprecated) |
New Log Analytics column name | Notes |
|---|---|---|---|
| category | Category | CategoryValue | |
| status Values are success, start, accept, failure |
ActivityStatus Values same as JSON |
ActivityStatusValue Values change to succeeded, started, accepted, failed |
The valid values change as shown. |
| subStatus | ActivitySubstatus | ActivitySubstatusValue | |
| operationName | OperationName | OperationNameValue | REST API localizes the operation name value. Log Analytics UI always shows English. |
| resourceProviderName | ResourceProvider | ResourceProviderValue |
Important
In some cases, the values in these columns might be all uppercase. If you have a query that includes these columns, use the =~ operator to do a case-insensitive comparison.
The following columns have been added to AzureActivity in the updated schema:
- Authorization_d
- Claims_d
- Properties_d
Next steps
Learn more about: