Enterprise Security in DeployR 8.0.5
DeployR Enterprise Security Model:
DeployR Enterprise is designed to deliver analytics solutions at scale to whomever needs it: inside or outside the enterprise. It also guarantees secure delivery of your analytics via DeployR web services. These secure web services integrate seamlessly with existing enterprise security solutions: Single Sign-On, LDAP, Active Directory, PAM, and Basic Authentication, can enforce access privileges already defined by your IT department for existing enterprise users and also have the capability to safely support anonymous users when needed.
Key Security Considerations in Enterprise setting:
- SSL/TLS
In all production environments, it is strongly recommended that SSL/HTTPS be enabled so that client applications can make API calls that connect over HTTPS. Use the following guide to Enable TLS/SSL protocols in DeployR.
- LDAP and LDAPS
The standard protocol for reading data from and writing data to Active Directory (AD) domain controllers (DCs) is LDAP. AD LDAP traffic is unsecured by default, which makes it possible to use network-monitoring software to view the LDAP traffic between clients and DCs. You can make LDAP traffic confidential and secure by using Secure Sockets Layer (SSL) / Transport Layer Security (TLS) technology. This combination is referred to as LDAP over SSL -- or LDAPS. To ensure that no one else can read the traffic, SSL/TLS establishes an encrypted tunnel between an LDAP client and a DC.
Reasons for enabling LDAPS include:
- Organizational security policies typically require that all client/server communication is encrypted.
- Applications use simple BIND to transport credentials and authenticate against a DC. As simple BIND exposes the users’ credentials in clear text, using SSL/TLS to encrypt the authentication session is strongly recommended.
- Use of proxy binding or password change over LDAP, which requires LDAPS. (Bind to an AD LDS Instance Through a Proxy Object)
- Applications that integrate with LDAP servers (such as Active Directory or Active Directory Domain Controllers) might require encrypted LDAP communications.
LDAPS Authentication Workflow in DeployR:
[caption id="attachment_185" align="alignnone" width="855"]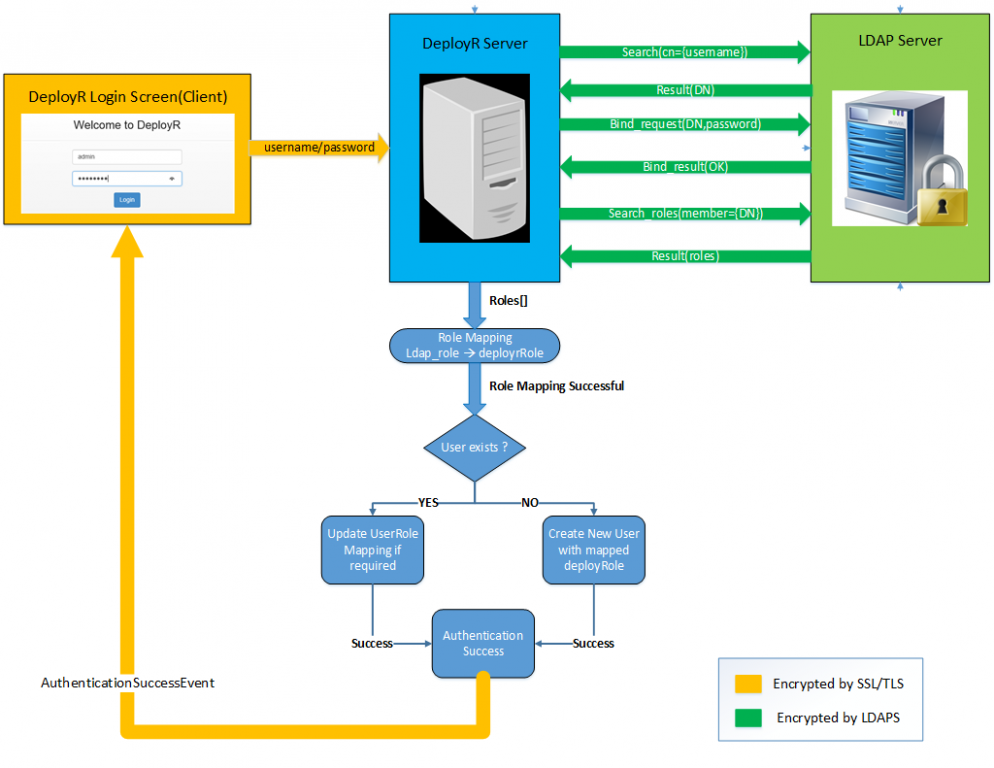 LDAPS Authentication Workflow[/caption]
LDAPS Authentication Workflow[/caption]
By default, the LDAP security provider is disabled. To enable LDAP authentication support, you must update the relevant properties in your DeployR external configuration file. The values you assign to these properties should match the configuration of your LDAP Directory Information Tree (DIT).
- For LDAP, set
grails.plugin.springsecurity.ldap.context.serverto the LDAP server URL, such as'ldap://localhost:389/'. - For LDAPS, set
grails.plugin.springsecurity.ldap.context.serverto the LDAP-S server URL, such as'ldaps://localhost:636/'.
/*
* DeployR LDAP Authentication Configuration Properties
*
* To enable LDAP authentication uncomment the following properties and
* set grails.plugin.springsecurity.ldap.active=true and
* provide property values matching your LDAP DIT:
*/
grails.plugin.springsecurity.ldap.active=false
/*
grails.plugin.springsecurity.ldap.context.managerDn = 'dc=example,dc=com'
grails.plugin.springsecurity.ldap.context.managerPassword = 'secret'
// LDAP
// grails.plugin.springsecurity.ldap.context.server = 'ldap://localhost:389/'
// LDAPS
grails.plugin.springsecurity.ldap.context.server = 'ldaps://localhost:636/'
grails.plugin.springsecurity.ldap.context.anonymousReadOnly = true
grails.plugin.springsecurity.ldap.search.base = 'ou=people,dc=example,dc=com'
grails.plugin.springsecurity.ldap.search.searchSubtree = true
grails.plugin.springsecurity.ldap.authorities.groupSearchFilter = 'member={0}'
grails.plugin.springsecurity.ldap.authorities.retrieveGroupRoles = true
grails.plugin.springsecurity.ldap.authorities.groupSearchBase = 'ou=group,dc=example,dc=com'
grails.plugin.springsecurity.ldap.authorities.defaultRole = "ROLE_BASIC_USER"
// Optionally, specify LDAP password encryption algorithm: MD5, SHA-256
// grails.plugin.springsecurity.password.algorithm = 'xxx'
// deployr.security.ldap.user.properties.map
// Allows you to map LDAP user property names to DeployR user property names:
deployr.security.ldap.user.properties.map = ['displayName':'cn',
'email':'mail',
'uid' : 'uidNumber',
'gid' : 'gidNumber']
// deployr.security.ldap.roles.map property
// Allows you to map between LDAP group names to DeployR role names.
// NOTE, while LDAP group names can be defined on the LDAP server using
// any mix of upper and lower case, such as finance, Finance or FINANCE,
// the LDAP group names that appear in the map must have ROLE_ appended
// and be capitialized. For example, an LDAP group named "finance" should
// appear in the map as ROLE_FINANCE. DeployR role names must
// begin with ROLE_ and must always be upper case.
deployr.security.ldap.roles.map = ['ROLE_FINANCE':'ROLE_BASIC_USER',
'ROLE_ENGINEERING':'ROLE_POWER_USER']
*/
For more information, see the complete list of LDAP configuration properties.