Azure App Service: Generating memory dumps on first chance exception using Procdump
In one of my older posts, I have explained on how we can generate memory dumps on first chance exceptions using Debug Diag . In certain scenarios where the users do not have permissions to install tools, users have to look for alternate options. For example, in Azure App Service, the users do not have permissions to install anything on the VM.
However, Azure App Service provides the KUDU console, using which the users can use a command line utility like procdump.exe to generate memory dumps. We can also use procdump to generate memory dumps on first chance exception using the below command:
procdump.exe -accepteula -ma -e 1 -f "<Exception Name>" <Process ID>
where, -ma Write a dump file with all process memory. The default dump format only includes thread and handle information -accepteula Use this switch to automatically accept the Sysinternals license agreement.
-e Write a dump when the process encounters an unhandled exception. Include the 1 to create dump on first chance exceptions.
-f Filter the first chance exceptions. Wildcards (*) are supported. To just display the names without dumping, use a blank ("") filter
Azure App Service instances include the sysinternals suite in the default image. They can be located here via the KUDU console: D:\devtools\sysinternals
The users may also download ProcDump from here and upload it a specific location such as D:\home\Dumps and use it.
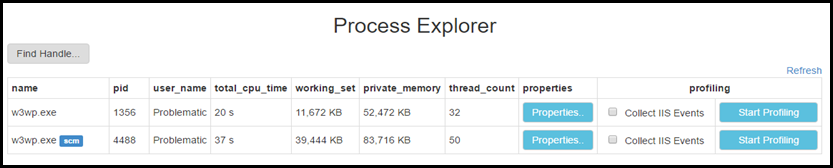
You would need to determine the process ID of the process against which procdump would be executed. You can determine that by navigating to the Process explorer in the KUDU console as shown below: (Note the PID of the w3wp process without the SCM tag)
Here is an example:
D:\home\Dumps>procdump.exe -accepteula -ma -e 1 -f "System.UnauthorizedAccessException" 7808
ProcDump v8.2 - Sysinternals process dump utilityCopyright (C) 2009-2016 Mark Russinovich and Andrew RichardsSysinternals - www.sysinternals.com
Process: w3wp.exe (7808)Process image: D:\Windows\SysWOW64\inetsrv\w3wp.exeCPU threshold: n/aPerformance counter: n/aCommit threshold: n/aThreshold seconds: n/aHung window check: DisabledLog debug strings: DisabledException monitor: First Chance+UnhandledException filter: [Includes] *System.UnauthorizedAccessException* [Excludes]Terminate monitor: DisabledCloning type: DisabledConcurrent limit: n/aAvoid outage: n/aNumber of dumps: 1Dump folder: D:\home\Dumps\Dump filename/mask: PROCESSNAME_YYMMDD_HHMMSSQueue to WER: DisabledKill after dump: Disabled
Press Ctrl-C to end monitoring without terminating the process.CLR Version: v4.0.30319 [10:02:46] Exception: E0434F4D.System.Exception ("There was a problem processing this request") [10:02:47] Exception: E0434F4D.System.UnauthorizedAccessException ("Access is denied.") [10:02:47] Dump 1 initiated: D:\home\Dumps\w3wp.exe_170426_100247.dmp [10:02:52] Dump 1 writing: Estimated dump file size is 306 MB. [10:03:16] Dump 1 complete: 306 MB written in 29.8 seconds[10:03:17] Dump count reached
HTH! ![]()