Vysvětlení a zkoumání cest laterálního pohybu (LVP) s využitím Microsoft Defender for Identity
Laterální pohyb je, když útočník použije k získání přístupu k citlivým účtům v celé síti jiné účty. Laterální pohyb používají útočníci k identifikaci a získání přístupu k citlivým účtům a počítačům ve vaší síti, které sdílejí uložené přihlašovací údaje v účtech, skupinách a počítačích. Jakmile útočník provede úspěšné laterální kroky směrem k vašim klíčovým cílům, může také využít výhod a získat přístup k vašim řadičům domény. K útokům s laterálním pohybem se používá mnoho metod popsaných v tématu výstrahy zabezpečení Microsoft Defender for Identity.
Klíčovou součástí přehledů zabezpečení Microsoft Defender for Identity jsou cesty laterálního pohybu nebo LMP. LVP defenderu for Identity jsou vizuální příručky, které vám pomůžou rychle pochopit a přesně identifikovat, jak se útočníci můžou laterálně pohybovat ve vaší síti. Účelem laterálních přesunů v rámci řetězce útoků kyberútoků je, aby útočníci získali a ohrozili vaše citlivé účty pomocí účtů, které nejsou citlivé. Ohrožení zabezpečení citlivých účtů je dostane o další krok blíž k jejich konečnému cíli, dominanci v doméně. Pokud chcete zabránit tomu, aby tyto útoky byly úspěšné, poskytují místně přístupní partneři Defenderu for Identity k vašim nejzranitelnějším a citlivým účtům snadno interpretovatelnými a přímo vizuálními pokyny. LMP pomáhají tato rizika zmírnit a v budoucnu jim předcházet a uzavřít přístup útočníka předtím, než dosáhne dominantního postavení v doméně.
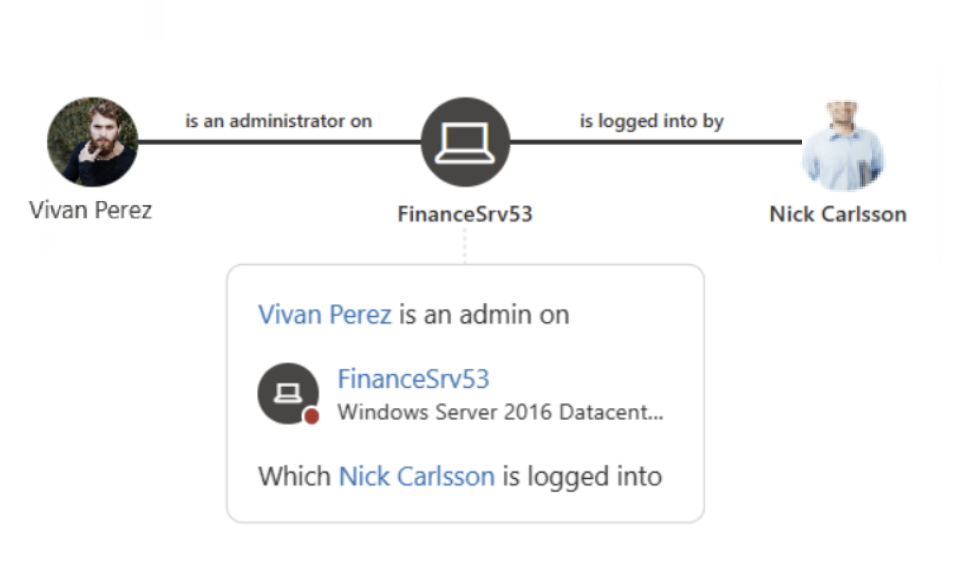
Příklady:
K útokům na laterální pohyb se obvykle používá celá řada různých technik. Mezi nejoblíbenější metody, které útočníci používají, patří krádež přihlašovacích údajů a Pass the Ticket. V obou metodách používají útočníci vaše účty, které nejsou citlivé, k laterálním přesunům tím, že využívají necitlivá zařízení, která sdílejí uložené přihlašovací údaje v účtech, skupinách a počítačích s citlivými účty.
Podívejte se na následující video, ve které se dozvíte více o omezení cest laterálního pohybu pomocí Defenderu for Identity:
Kde najdu LMP defenderu for Identity?
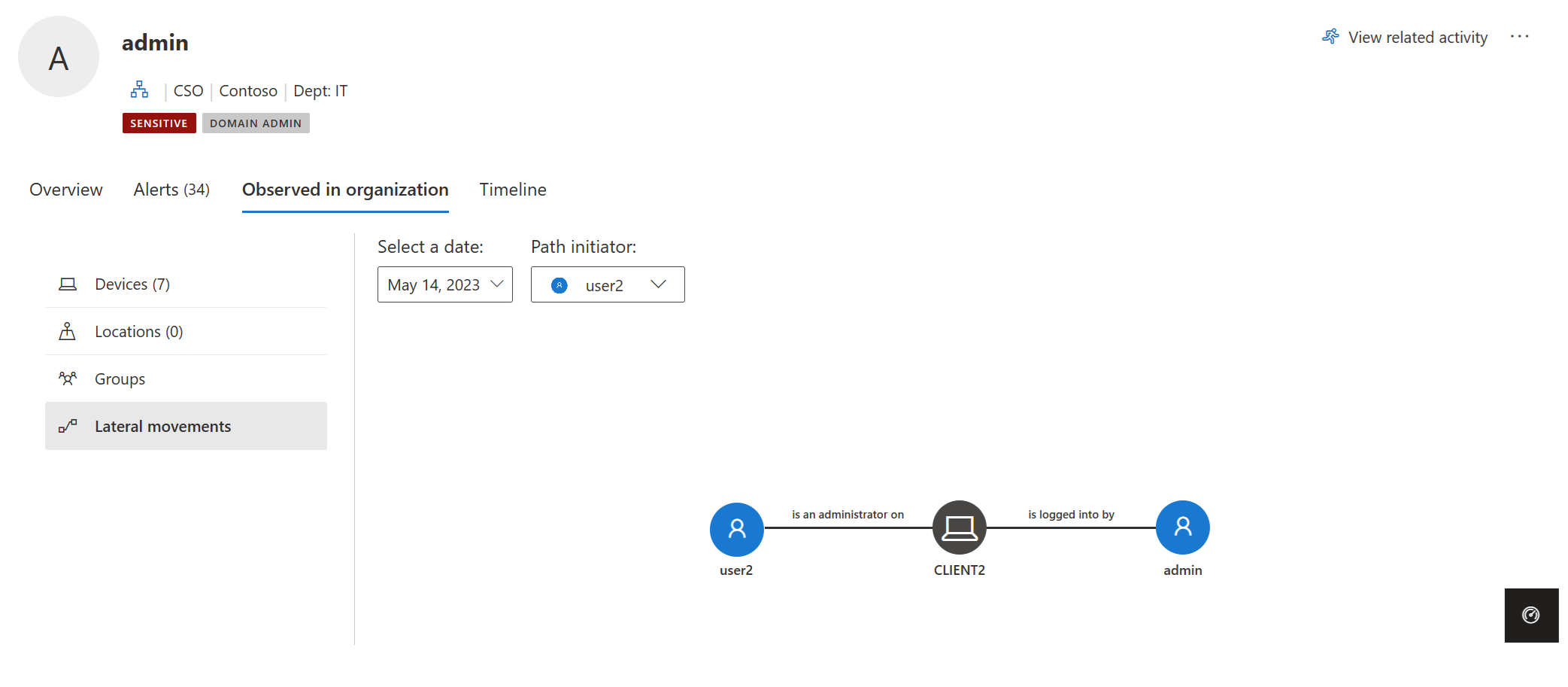
Každá identita, kterou Defender for Identity zjistí, že je v LMP, má na kartě Pozorované v organizaci informace o cestách laterálního pohybu. Například:
LMP pro každou entitu poskytuje různé informace v závislosti na citlivosti entity:
- Citliví uživatelé – zobrazí se potenciální LMP(y) vedoucí k tomuto uživateli.
- Zobrazí se necitliví uživatelé a počítače – potenciální LMP,se které entita týká.
Při každém výběru karty se v Defenderu for Identity zobrazí naposledy zjištěný LMP. Každý potenciální LMP se uloží po dobu 48 hodin po zjištění. K dispozici je historie LMP. Zobrazte starší LMP, které byly zjištěny v minulosti, výběrem možnosti Vybrat datum. Výběrem možnosti Iniciátor cesty můžete také vybrat jiného uživatele, který inicioval LMP.
Zjišťování LMP s využitím rozšířeného proaktivního vyhledávání
Pokud chcete proaktivně zjišťovat aktivity cesty laterálního pohybu, můžete spustit rozšířený dotaz proaktivního vyhledávání.
Tady je příklad takového dotazu:
Pokyny ke spouštění pokročilých dotazů proaktivního vyhledávání najdete v tématu Proaktivní vyhledávání hrozeb pomocí rozšířeného proaktivního vyhledávání v Microsoft Defender XDR.
Entity související s LMP
LMP teď může přímo pomoct s procesem vyšetřování. Seznamy důkazů výstrah zabezpečení defenderu for Identity poskytují související entity, které jsou součástí každé potenciální cesty laterálního pohybu. Seznamy důkazů přímo pomáhají týmu reakce na zabezpečení zvýšit nebo snížit důležitost výstrahy zabezpečení a/nebo vyšetřování souvisejících entit. Pokud je například vydáno upozornění Pass the Ticket, zdrojový počítač, ohrožený uživatel a cílový počítač, ze kterých byl odcizený lístek použit, jsou součástí potenciální cesty laterálního pohybu vedoucí k citlivému uživateli. Díky existenci zjištěného LMP je prošetření výstrahy a sledování podezřelého uživatele ještě důležitější, aby se zabránilo nežádoucímu člověku v dalších laterálních přesunech. V sadě LMP jsou k dispozici sledovatelné důkazy, které vám usnadní a urychlí zabránění útočníkům v pohybu ve vaší síti.
Posouzení zabezpečení cest lateral Movement
Microsoft Defender for Identity průběžně monitoruje vaše prostředí, aby identifikovala citlivé účty s nejrizičími cestami laterálního pohybu, které vystavují bezpečnostní riziko, a sestavy těchto účtů, které vám pomůžou při správě prostředí. Cesty se považují za rizikové, pokud mají tři nebo více necitlivých účtů, které můžou vystavit citlivý účet krádeži přihlašovacích údajů ze strany zlými úmysly. Pokud chcete zjistit, které z vašich citlivých účtů mají rizikové cesty laterálního pohybu, projděte si posouzení zabezpečení nejrizičích cest laterálního pohybu (LMP ). Na základě doporučení můžete entitu ze skupiny odebrat nebo odebrat oprávnění místního správce pro entitu ze zadaného zařízení.
Další informace najdete v tématu Posouzení zabezpečení: Nejrizičí cesty laterálního pohybu (LMP).
Osvědčené postupy pro prevenci
Přehledy zabezpečení nejsou nikdy pozdě na to, aby se zabránilo dalšímu útoku a nápravě škod. Z tohoto důvodu nabízí zkoumání útoku i ve fázi dominance domény jiný, ale důležitý příklad. Při vyšetřování výstrahy zabezpečení, jako je vzdálené spuštění kódu, obvykle může dojít k ohrožení zabezpečení řadiče domény, pokud je výstraha skutečně pozitivní. LMP ale informují o tom, kde útočník získal oprávnění a jakou cestu použil k vaší síti. Při použití tohoto způsobu můžou LMP také nabídnout klíčové přehledy o tom, jak nápravu provést.
Nejlepší způsob, jak zabránit vystavení laterálnímu pohybu ve vaší organizaci, je zajistit, aby citliví uživatelé používali přihlašovací údaje správce pouze při přihlašování k počítačům s posílenými oprávněními. V příkladu zkontrolujte, jestli správce v cestě skutečně potřebuje přístup ke sdílenému počítači. Pokud potřebujete přístup, ujistěte se, že se ke sdílenému počítači přihlašují pomocí jiného uživatelského jména a hesla, než jsou přihlašovací údaje správce.
Ověřte, že vaši uživatelé nemají zbytečná oprávnění správce. V tomto příkladu zkontrolujte, jestli všichni ve sdílené skupině skutečně vyžadují práva správce na vystavených počítačích.
Ujistěte se, že uživatelé mají přístup jenom k nezbytným prostředkům. V tomto příkladu Ron Harper výrazně rozšiřuje expozici Nicka Cowleyho. Je nutné, aby byl Ron Harper zahrnut do skupiny? Existují podskupiny, které by se daly vytvořit, aby se minimalizovalo vystavení laterálnímu pohybu?
Tip
Pokud se pro entitu za posledních 48 hodin nezjistí žádná aktivita potenciální cesty laterálního pohybu, zvolte Vybrat datum a zkontrolujte předchozí potenciální cesty laterálního pohybu.
Důležité
Pokyny k nastavení klientů a serverů tak, aby služba Defender for Identity umožňovala provádění operací SAM-R potřebných pro detekci cest laterálního pohybu, najdete v tématu Konfigurace Microsoft Defender for Identity pro vzdálená volání SAM.
Prozkoumání cest laterálního pohybu
Existuje několik způsobů, jak použít a prozkoumat LMP. Na portálu Microsoft Defender vyhledejte podle entity a pak prozkoumejte cestu nebo aktivitu.
Na portálu vyhledejte uživatele. V části Pozorované v organizaci (na kartách Přehled i Pozorování ) můžete zjistit, jestli je uživatel zjištěn v potenciálním LMP.
Pokud se uživatel zjistí, vyberte kartu Pozorované v organizaci a zvolte Cesty laterálního pohybu.
Zobrazený graf poskytuje mapu možných cest k citlivému uživateli během 48hodinového časového období. Pomocí možnosti Vybrat datum zobrazte graf předchozích detekcí cesty laterálního pohybu pro entitu.
Projděte si graf a podívejte se, co se můžete dozvědět o odhalení přihlašovacích údajů citlivého uživatele. Například v cestě postupujte podle šipek Přihlášeni a podívejte se, kde se Nick přihlásil pomocí svých privilegovaných přihlašovacích údajů. V tomto případě byly na zobrazeném počítači uloženy Citlivé přihlašovací údaje Nicka. Teď si všimněte, kteří další uživatelé se přihlásili k počítačům, které vytvořily největší ohrožení a ohrožení zabezpečení. V tomto příkladu má Elizabeth Kingová možnost přistupovat k přihlašovacím údajům uživatele z tohoto prostředku.